Coming to SD-WAN: The Build vs. Buy Decision
Earlier this month, I attended Networking Field Day 13, where we heard from VeloCloud on their SD-WAN solution. Their presentation and case study got me thinking about how most businesses will consume SD-WAN and where business customers may fall on the “Buy” vs. “Build” spectrum.
At the outset of the NFD13 presentation, VeloCloud CEO Sanjay Uppal recapped some stats: VeloCloud has been around for just about 4 years, and at this point has around 600 enterprise customers and is deployed to about 50,000 sites. If VeloCloud was a product line from an encumbent networking vendor with stats like that, they would be declaring it as a very successful mainstream product. I point this out as I think it demonstrates that SD-WAN solutions and vendors are moving out of “startup” mode and into a mainstream solution.

One of the things that has set VeloCloud apart from many of their competitors since their inception has been their focus on building a true multi-tenant solution from the beginning, as well as their choice to partner with service providers to provide a solution for managed SD-WAN. Strong API capabilties and flexible zero-touch provisioning features support this as well. This is what really caught my attention Continue reading
NFD13 Forecast – Cloudy With a Chance of Software
Well, this week is a week of firsts — or at least, firsts in a while. It’s my first time actually posting something new on the blog in a while, and it will also be my first Tech Field Day event in a while.
I’m honored to have been invited back to NFD13, happening on Thursday, 11/17 and Friday, 11/18. I’m very excited to be joining the TFD team for another event! The delegate panel includes some of the most experienced and well respected names in the networking industry (myself excluded, obviously), and the sponsor list is really quite exciting. I’m looking forward to seeing some old friends, and making some new ones along the way.
I really like when NFD events have a mix of focuses (foci?). It keeps the conversation varied and interesting for both the delegates and the audience. For NFD 13, I see several big themes for the sponsor list:
Data Center Fabric/Automation/Orchestration
Network Testing/Modeling/Audit/Management
Software Defined WAN
Note: I could be mis-classifying a couple of Continue reading
Performing Ping Sweeps with IOS TclSh
Creating Uplink Port-Channels in UCS Manager
Setup:
Procedure:
interface port-channel5 description To ucs6248-a switchport mode trunk switchport trunk allowed vlan 1-50 spanning-tree port type edge trunk vpc 5 ! interface Ethernet1/5 description To ucs6248-a switchport mode trunk switchport trunk allowed vlan 1-50 channel-group 5 mode active no shutdown ! interface Ethernet1/6 description To ucs6248-a switchport mode trunk Continue reading
ASA File Operation Tips
Delete from the active, upload to the Continue reading
Thoughts on Building Tools versus “Programming”
A couple weeks ago at Networking Field Day 9, Brocade presented with their usual A-list of networking gurus. One of the presenters was Jon Hudson, a very engaging, visionary speaker. His talk, shown below, was about the state of network programmability.
During the conversation (which is well worth watching), discussion turned to the question of “will network engineers become programmers?” posed by John Herbert of MovingPackets.net. Jon Hudson’s response elicited applause from the room. He said:
“The trouble I have with that statement is, most network engineers I know, like myself, we know how how to code. We went to school for it, and we chose not to.” – Jon Hudson
The conversation went on to discuss the value of programmability for the sake of consistency in the management and configuration of large-scale network fabrics (which I don’t think anyone would really debate as a “Good Thing”), but Jon’s quote about being a programmer and some of the sidebar that flowed from it created a fair bit of activity in the Twitter stream. Following the presentation, my attention was called to a mailing list on which a question was asked about networking engineerings being “given a Continue reading
The Buzz About NetBeez
NFD8 Recap: Nuage Networks – One to Watch
Last fall, I attended the Tech Field Day NFD8 event, and one of the presenting companies was Nuage Networks. This was actually the second time I’d seen Nuage present at an NFD event, the first one being NFD6 a year earlier. Upon my return from NFD8, I did a short write-up of each presenting sponsor for my coworkers at H.A. Storage Systems to keep them informed. The following is my recap of Nuage Networks after their presentation in which I explain why I think Nuage is really on-target with their SDN solution and is definitely a solution to keep an eye on.
In the Data Center, No One Can Hear You Lose Your Hearing
Working for a data center-focused reseller/integrator like H.A. Storage Systems, I spend my fair share of time in various data center environments. I have, for years, elected to use some sort of hearing protection when in these facilities. I have constantly been amazed, though, at how few other workers in data centers do the same.
Honestly, I’m not sure why most people I see in data center facilities don’t use hearing protection. Perhaps they think they’ll only be on the data center floor for a few minutes. We all know it never goes like that! Perhaps they think it makes it too hard to hear co-workers. Personally, I find it easier to communicate with someone when I have ear protection on. Maybe workers think it’s not loud enough for ear protection to be necessary. Unfortunately, this isn’t true in most cases.
Can You Hear Me Now?
As an example, I was recently down at the Sungard Availability Services colo facility in Philadelphia. It’s one of the largest colos in the immediate area with 230,000 square feet of raised floor. I was in there all day long with one of my customers, for two days while we traced out Continue reading
Normalizing ACLs to Support Automated Changes
R1(config)#do sh access-list NAT Extended IP access list NAT 14 deny ip 10.10.1.48 0.0.0.7 10.0.0.0 0.255.255.255 20 deny ip 10.11.1.48 0.0.0.7 10.0.0.0 0.255.255.255 25 permit ip 10.10.1.48 0.0.0.7 192.168.0.0 0.0.255.255 30 permit ip 10.10.1.48 0. Continue reading
Managing the Network as a Fabric — About Time!
Earlier this September, I attended the Tech Field Day Networking Field Day 8 event. Over the course of three days, we saw presentations from many very interesting vendors including a mix of startups and established market leaders. One trend that really stuck out to me more this time around than at any previous NFD event was a nearly ubiquitous emphasis on data center network fabric management. In other words, truly managing an entire data center network (or at least a sub-block of it) as a single unit.
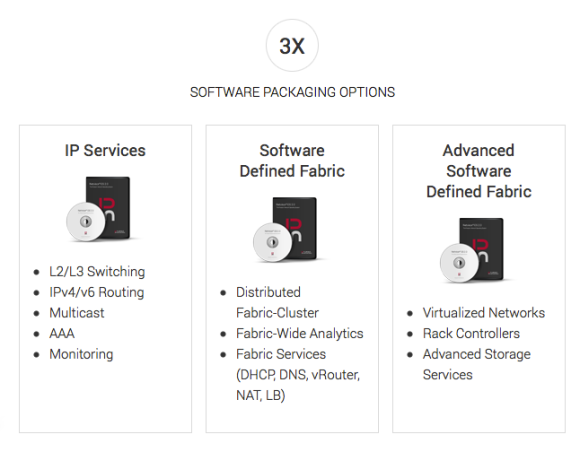
Just of the NFD8 presenters who were providing this option, we had Cisco with their ACI model (but it stands to reason that even the now-well-established FEX model has very similar capabilities), Big Switch Networks with their Big Cloud Fabric, Pluribus Networks’ Netvisor Software Defined Fabric, and Nuage Networks Virtual Services Platform. Each of these products has unique value propositions, so I’m not suggesting they’re all the same but rather pointing out that this concept of fabric-level management is clearly at the forefront of most, if not all, leading-edge data center solutions at this point. The concept has been building for a couple years, and other vendors are also pursuing this model Continue reading
Cisco Live – The Minimalist Packing List
Cisco Live 2014 is right around the corner! It’s almost time to start packing. The other day, Keith Miller (@packetologist), a first-time Cisco Live attendee, asked me on Twitter:
@BobMcCouch Since you are the king of being prepared, what is your travel pack consisting of to CLUS?
— Keith Miller (@packetologist) May 11, 2014
I have a bit of a reputation among some of my consulting clients as being ready for just about anything. Normally, that means my laptop bag weighs about 50 lbs. But for Cisco Live, I choose to travel light. I’ve seen people in the airport on the way to, and from, the event with a LOT of stuff. Sure, some folks are presenters or carrying company stuff but for the rest, you probably just have too much stuff.
Why choose to travel as light as possible? Here are just a few reasons:
- Airline bag check fees
- Airlines are great at losing/abusing your stuff once its out of your hands
- Due to #1, everyone is always fighting for room in the overhead bins and you end up checking your “carry on” anyway
- If you land early, you have to check your 3 tons of bags, or else Continue reading
Using EEM to Remotely Change a WAN IP – Part 2
In my last EEM post I provided a simple means to change an IP address and default route of a Cisco router using a script that makes the change without requiring interactive user input. This is helpful if you are remotely changing a device’s WAN/Internet IP and waiting for some on-site hands to move a cable over to a new ISP or WAN SP connection. That first script, however, would make the change and then exit. What would happen if the new Internet connection had a problem, or the on-site help couldn’t move the cable for some reason? Proper testing and preparation should help you avoid most of those issues but you just never know.
One way to deal with this possibility is to issue a “reload in 10” before kicking off the EEM change script. If the change can’t be completed, the router will reboot back to its previous configuration. That’s fine, but I like to avoid a full reboot whenever possible, and “reload in” has always been a rather clunky rollback mechanism.
Another idea mentioned by Jody Lemoine in the comments of the last post, is taking advantage of the newer configuration archive and rollback features. While my Continue reading
Using EEM to Remotely Change a WAN IP – Part 1
- Have out-of-band access using a 3G/4G/LTE-connected terminal server (I wrote about one of these before)
- Use a remote app like GetConsole so the remote hands can get me console access out of band using their smart phone
- Use something with a proper commit/rollback mechanism like a Juniper device
- Dial-up modem to the AUX port!
Dell Aims for the Clouds with Z9500 Spine
While at Networking Field Day 7, we got a small preview of a new switch Dell Networking has just announced, the Z9500. At some point I’ll have another post coming discussing more of Dell’s presentation at NFD7, but I wanted to briefly talk about this new product and what it brings to the table for Dell.
Taking a New Approach to Cisco Live 2014
It’s getting to be that time of year again when geeks across North America (and beyond) start getting excited for Cisco Live! The buzz is starting a bit early this year, but that’s because Cisco Live is about a month earlier this year (May 18-22) than it has been in recent years.
Introduction
@Rob_Coote @blakekrone @scottm32768 @networkingnerd @BobMcCouch @fryguy_pa This is the backpack, no Dora this time pic.twitter.com/ZJ504qJ66P
— Kathleen Mudge (@KathleenMudge) March 20, 2014
@Rob_Coote @blakekrone @scottm32768 @networkingnerd @BobMcCouch @fryguy_pa My pics aren’t doing it justice. It’s cool pic.twitter.com/J2ZI8OgQzl
— Kathleen Mudge (@KathleenMudge) March 20, 2014
Plans Continue reading
Weighing AWS VPN Options
Option 1
Build the VPNs off the Internet routers themselves. Route AWS traffic in to the corporate network through the firewall. In an ideal world, you’d probably dedicate some routers for this purpose, but I’ve never had anyone do that. We’re talking about a LAN-to-LAN VPN, here; one doesn’t commonly deploy totally dedicated infrastructure for each new Continue reading
Server Brawn + Switch Brains = Infrastructure Fabric
Last week I attended Networking Field Day 7, and was introduced to Pluribus Networks. Pluribus is taking an interesting approach to building the data center fabric, by combining high-performance data center top-of-rack (ToR) switching with powerful server internals in a platform they’ve dubbed the Freedom Server-Switch.
Faking an ASA as a DNS Forwarder
I came across a good tip the other day that was very helpful during a small site firewall migration. Here’s the back story:
I was migrating a small single-site customer that had, up to this point, been using a FIOS-provided consumer-type router/firewall/access point to some Cisco gear including an ASA firewall for better firewall/VPN capabilities. This is fairly common with small businesses that start out with essentially consumer-style connectivity and finally begin to grow to a point of needing business-grade capabilities. My preparation went fine, and when the time came I swapped the ASA firewall in place of the FIOS-provided one. Then everything broke.
I had meticulously prepared the ASA to take over immediately from the old FIOS router, even going so far as to spoof the FIOS router’s MAC address on the ASA’s inside interface for now so as not to disrupt the 60-or-so clients that were all on the single attached internal subnet while their ARP caches timed out since we were doing the install and cut-over during working hours. I had set up a DHCP scope on the ASA as well, which instructed clients to use some public DNS resolvers as this small business has, so far, Continue reading
Goodbye Snowpocalypse, Hello Networking Field Day 7!
I’m excited to rub elbows and network with the exceptional delegate list. I have met nearly all of this event’s delegates before and I respect the expertise and experience of every single participant. I feel I have learned so much and made so many valuable connections through TFD events and I’m grateful to Gestalt IT and the TFD community for another opportunity to participate.