VoidZero is joining Cloudflare
VoidZero, the company behind Vite, Vitest, Rolldown, Oxc, and Vite+, is joining Cloudflare. As part of this change, all team members of VoidZero are joining Cloudflare, too.
Before saying anything else, we want to make the most important thing clear: Vite, Vitest, Rolldown, Oxc, and Vite+ will stay open source, vendor-agnostic, and community-driven. Nothing about that changes.
Cloudflare's mission is to help build a better Internet. And a better Internet is an open Internet. Developers need choice, frameworks need a neutral foundation, and applications need to be portable. It is not reasonable to expect the entire web ecosystem to build around a single vendor. The most important tools and frameworks are portable by design.
Vite is one of the few foundational tools that the whole JavaScript ecosystem agrees on. It earned that position by being fast, excellent, portable, and vendor-neutral. One of the best ways Cloudflare can help build a better Internet is by investing in that foundational open source toolchain. A toolchain that makes the Internet better for everyone, not just people who use Cloudflare or choose to host with us.
Over the last few years we've invested heavily in making Cloudflare the best Continue reading
TP-Link Archer A1800 TX20U Plus on Raspberry
Do you need better Wi-Fi for your Raspberry Pi 3 Model B? The built-in Wi-Fi […]
The post TP-Link Archer A1800 TX20U Plus on Raspberry first appeared on Brezular's Blog.
Using netlab to Argue with Vendor TAC
A happy netlab user sent me an unexpected use case: they successfully used its multi-vendor capabilities to argue with a vendor TAC. Here’s the gist of the story (edited/anonymized for obvious reasons):
Multi-Layer Policy for Securing AI Agents
As part of our work at Tigera building products that create secure runtime environments for enterprise agents at scale in the real world, one small part of this puzzle I think about a lot is policy, and runtime enforcement of policy, and how to create a comprehensive secure runtime, configured from one place. The more companies we talk to trying to lock down and secure these platforms at runtime, the more I believe AI Agent security needs policy in multiple places, not just one (e.g., not just at the gateway layer), and ideally expressed in the same policy language.
At the L7 gateway layer, every agent call is observable: who is calling, what they are calling, what attributes both sides carry, what the requested action is. This is where you decide whether an agent should be permitted to talk to a particular MCP server, invoke a particular tool, delegate to another agent, or call a particular LLM. The atoms of policy here are identity, action, resource, and context.
At the agent runtime layer, or kernel layer in a container, what the agent does inside its own runtime is observable: syscalls, file access, library loads, network connections that bypass Continue reading
Enforcing the First AS in BGP AS_PATHs
Some recent route hijacks reported by Spamhaus captured our attention. In many of these hijack attempts, an apparent bad actor took advantage of unused autonomous system numbers, or ASNs. Notably in these hijacks, the actor appears to be creating fake AS_PATHs toward destinations, misdirecting traffic down an unexpected path.
By creating forged AS_PATHs, the hijacker is attempting to lead traffic somewhere it isn’t normally meant to go while also trying to conceal their identity. A hijacker could strip enough information away from a network path that they could pretend to be the origin of a Border Gateway Protocol (BGP) prefix themselves. Attackers can use this hijacked route to intercept traffic and for other nefarious purposes.
There is a simple solution for these cases: basic verification that a BGP peer autonomous system (AS) always includes their network as the “First AS” in an advertised route. To get a sense of how well these safeguards are implemented, we stress-tested several major networks and researched their BGP implementations. Read on to see what we learned.
The idea that an actor is creating fake AS_PATHs is supported when we take a closer look at implausible AS Continue reading
EVPN Centralized Routing with Arista EOS
A month ago, I described ARP issues in EVPN centralized routing design, and Naveen Kumar Devaraj was kind enough to add some Arista EOS implementation details. Today, let’s explore what EVPN routes Arista EOS generates in that scenario. We’ll use a very simple lab topology with a spine switch acting as a router. The leaf switches are layer-2 switches.
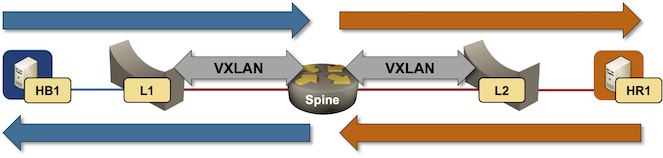
Packet forwarding in centralized routing design
What’s new in Calico: Spring 2026 Release
Kubernetes has come a long way since its debut in 2014. It’s gone from running a couple of containerized microservices to orchestrating fleets of production workloads spanning everything from AI agents to full scale VMs running in pods. As Kubernetes adoption grows, and its use cases stretch to cover more ground, managing its increasingly complex networking and security landscape demands operational maturity and a platform that supports it.
The Spring 2026 release of Calico provides that support in two key areas:
Unified operations across Kubernetes pods and VMs
- KubeVirt Live Migration in Bridge Mode allows you to migrate VM workloads with IPs preserved, minimal packet loss, and fast route convergence. VMs can move between nodes for planned maintenance, load balancing and to support high availability without interrupting network connectivity.
- Egress Gateway Layer 2 Advertisements (Enterprise exclusive) lets pod traffic egress with IPs from the host’s own subnet so workloads get a stable identity the rest of your network already recognizes eliminating the need for BGP Peering to advertise Egress Gateway IPs.
- Policy recommendations for VMs and hosts (Enterprise exclusive) automates and scales policy authoring for Calico-managed workloads running outside of your Kubernetes clusters.
- OpenStack Live Migration Improvements lets you migrate Continue reading
Worth Reading: Building the Tools I Wished I Had
Tony Mattke built several networking-focused CLI tools and released them on GitHub. You might find them useful.
How we reduced core unit boot time from hours to minutes
Cloudflare's core is the centralized data centers that run our control plane, billing, and analytics — distinct from the globally distributed edge that handles user traffic. Core servers are bare metal, and when issues happen during reboot, the consequences can cascade fast.
Their boot sequence is orchestrated by UEFI, the modern firmware standard that initializes hardware and hands off control to the operating system. Small quirks in that handoff can have outsized consequences.
After a routine firmware update, some of our core servers were taking four hours to come back online, rather than just minutes as they did before. What should have been a one-day fleet-wide rollout was stretching into multi-day slogs. New nodes faced the full timeout gauntlet on their very first boot. Maintenance windows ballooned. Engineering teams had to babysit upgrades that should have run unattended.
The behavior we saw was brought to light when we were bringing nodes online that had been powered off for an extended period. These nodes’ firmware was out of date and required multiple updates to resolve. Combine this with recent updates to the boot protocols used by servers in some of our locations, and boot times on the affected Continue reading
SR-MPLS over Unnumbered Interfaces
After the simple SR-MPLS demo and the dual-stack SR-MPLS setup, it was time for the next obvious question: Does SR-MPLS work over unnumbered IPv4 interfaces1, assuming the implementation of the underlying routing protocol supports them? Of course it does; let’s go through the details, using the same topology I used throughout the Segment Routing workshop @ ITNOG10.

DNS Delegation
A presentation, by ISC's Ondřej Surý, at RIPE 92 was on the topic of DNS provisioning, looking at how to strike a balance between resilience and efficiency in the provisioning of nameservers of DNS zones and the performance of DNS resolvers. lets dive into this topic!HN829: EVPN/VXLAN Vs. TradCore
Drew and Ethan sit down with Tony Bourke to determine whether TradCore or EVPN VXLAN is right for your network. Tony is a seasoned instructor in automation, network design, and more. They explore the key factors for choosing a design, including scale and redundancy, operational complexity, and workload mobility. AdSpot Sponsor: Auvik Sponsor Auvik Network... Read more »Hedge 307: bgproutes.io
If you advertise routes into the default free zone (or global Internet), you might struggle with seeing and understanding what they look like “on the other side.” While there are many manual tools to help operators with this process, bgproutes.io gives you visibility in the global routing table through interfaces like BMP. Listen to this episode of the Hedge to learn more.
You can find bgprotues.io here.
download