Site Maintenance
I am performing some site maintenance in conjunction with a move to a new VPS server. (Thank you Hetzner (some irony may be involved)).
Hopefully everything should be reachable, but some minor UI tweaks may occur.
Thanks for understanding.
/Kim
TFDx – Forward Networks
Forward Networks was one of the top presenters at TFDx at Cisco Live 2019 in Barcelona in my opinion.
I really didn’t know much about what they were all about before we had the presentation. One thing I did notice was that they were really organized, even handing out agendas before beginning the presentation. Also, we were told that their engineering department in San Jose were staying up late to watch the Live Stream! Talk about dedication.
So what does Forward Networks provide? – Very deep visibility into your network is the answer. This solution is by far the most comprehensive i have seen. But allow me to perform a breakdown of what im talking about.
These are the components of the solution:
- Retrieval of both device configuration as well as device state. The later being far more important than just a configuration dump.
- Common data modeling. A variant of Openconfig is used for this part.
- Mathematical calculation and graphing based upen the data modeling.
- Impressive GUI containing multiple “applications”.
- Open API’s and a query engine.
So let me go into detail and explain the relevance of each.
Retrieval of information:
There are basically 2 different kinds of information that Continue reading
Time to say goodbye to Barcelona
As im sitting here in the hotel, waiting to leave for the airport, the only thing on my mind is: Wow.. what an amazing week this has been.
I have met so many old friends and made a bunch of new ones. All of the Tech Field Day delegates and staff are so bright and friendly that its hard to put into words. We have debated, discussed, thought out loud, shrugged our shoulders and laughed hard.
If you are not already following these guys on twitter, you really should go ahead and push that follow button. Here they are: @al_rasheed @TechFieldDay @ioshints @networkautobahn @darkkavenger @bockcay @OrhanErgunCCDE
In the coming weeks I will put together my final impressions of both the Cisco Live event and the entire Tech Field Day Extra event. Also to come is an analysis of some of the presentations we were fortunate enough to receive.
A big shoutout to Ben Gage (@BenTGage) and Tom Hollingsworth (@NetworkingNerd) for inviting me to this amazing event! Thank you guys!
Time to leave for the airport. Take care!
/Kim
The post Time to say goodbye to Barcelona appeared first on Packet-Forwarding.net.
Thoughts before CLEUR 2019
In just 3 days time I will be leaving for Cisco Live 2019 in Barcelona. Im thinking about what sort of event it will be and what to expect in term of announcements.
Especially one thought keeps reappearing and thats the thought of the transformation of Cisco. It is no longer a company with a future in just selling hardware. It itself has been disrupted by the emergence of “everything software” and merchant silicon.
The issues and consequences of merchant silicon has been discussed in many places, so I won’t mention them in this post, other than saying it has in some way forced Cisco’s hands in going down the route of being a software and services company.
Especially the software component will be huge this year. If you need proof of this, just look at the very large following as well as events from the Cisco DevNet community. But is this transformation smooth sailing from here? — I think not.
Traditionally Cisco’s reputation in the industry when it comes to software has been very flaky, to say the least. Something a lot of engineers hope will change in the coming years.
That being said, I think a lot of Continue reading
Tech Field Day @ CiscoLive Europe 2019
I am honoured to have been selected as a delegate for Tech Field Day during Cisco Live Europe 2019 in Barcelona!
Cisco Live Europe will take place from the 27th of January until Friday 1st.
I am really looking forward to this opportunity. There are some really great names among the list of delegates that I hope to be interacting with quite a lot, both during and after the event.
I am still to receive the official list of presenters, so I can’t tell you just who all the presenters will be, but im sure the Tech Field Day crew will release that information shortly.
When possible, I will be blogging about the presenters for sure. Also, during the event I will be posting to twitter so stay tuned.
A big thank you to Ben and Tom from Tech Field Day for extending an invitation! I can’t wait!
Until then, take care!
https://techfieldday.com/event/cleur19/
The post Tech Field Day @ CiscoLive Europe 2019 appeared first on .
Cisco Champion 2019
Small update.
I was fortunate enough to be selected as a Cisco Champion for 2019. Looking forward to alot of good information and cooperation from the program! 
Practical OTV
Practical OTV
————-
This post is all about OTV (Overlay Transport Virtualization) on the CSR1000v.
I wanted to create the post because there are alot of acronyms and terminology involved.
A secondary objective was to have a “real” multicast network in the middle, as the examples I have seen around the web, have used a direct P2P network for the DCI.
Instead, I wanted to have full multicast running in the SP core in order to gain a full understanding of the packet forwarding and encapsulation.
First off, lets talk about the topology I will be using:
Datacenters:
————
We have 2 Datacenters, one represented by Site 1 and the other by Site 2.
In the middle, we have what is in all respects a SP provider network. In your environment, this may or may not be your own transport network.
In site 1, CSR-1 is our “server”, basically all thats configured on it is an IP address (192.168.100.1/24) on its G1 interface.
SW-9 is our L2 switch, which is configured with 2 VLAN’s (Vlan 100 (SERVER-VLAN) and Vlan 900 (SITE-VLAN)). The port (e0/0) going to CSR-1 is configured as an access-port in Vlan 100.
The ports Continue reading
Useful links for Observium + Rancid
I recently decided that i would like to utilize Observium as well as rancid for configuration backups on my home network. To that effect, the following links really helped me out getting it all setup correctly:
https://docs.observium.org/rancid/
http://packetsandpings.blogspot.com/2013/05/installing-and-configuring-rancid.html
https://layer77.net/2016/08/10/upgrading-from-rancid-2-3-8-to-3-4-1/
Let me know if you run into anything i might help out with.
/Kim
A quote from an Ex-Googler
I really like this paragraph, because almost everyone wants to imitate google. Why? well, the answer to that questions seems to be what everyone is missing!
Google’s solutions were built for scale that basically doesn’t exist outside of a maybe a handful of companies with a trillion dollar valuation. It’s foolish to assume that their solutions are better. They’re just more scalable. But they are actually very feature-poor. There’s a tradeoff there. We should not be imitating what Google did without thinking about why they did it. Sometimes the “whys” will apply to us, sometimes they won’t
The quote comes from Cloud Field Day 4, from Ben Sigelman of LightStep.
Thanks to Tom over at networkingnerd.net for the entire post!
/Kim
Complicated Vs. Complexity
I am currently reading Team of Teams, an excellent book!
In it, it highlights an interesting fact that I think is very relevant for the networking world and that is the difference between something that is complicated versus something that is complex.
There is a distinct difference in that something complicated can be broken down into its building blocks and analysed with a high degree of certainty. Think of a car engine for example. It is a very complicated piece of machinery for sure, but it is not complex, since you can divide its functionality down into components. On the other hand think of something like a virus and how it evolves. This is a complex organism that you you can’t be certain that will evolve in a predetermined fashion.
So im thinking, the way we build networks today, are we building them to be “just” complicated or are they really complex in nature instead? – The answer to this question determines how we need to manage our infrastructure!
Just some food for thought!
/Kim
JNCIA-Junos
I recently completed the entry level Juniper certification. I thought it would be a good idea to study for something other than the mighty Cisco, so Juniper’s JNCIA-Junos seemed like a good choice.
It was a very fair exam I can highly recommend.
Next up is AWS Solution Architect Associate. Need to get some cloud skills as thats where everything is going right? 
VxLAN on the CSR1Kv
By now, VxLAN is becoming the standard way of tunneling in the Datacenter.
Using VxLAN, i will show how to use the CSR1Kv to extend your Datacenter L2 reach between sites as well.
First off, what is VxLAN?
It stands for Virtual Extensible LAN. Basically you have a way of decoupling your vlan’s into a new scheme.
You basically map your VLAN into a VNI (Virtual Network Identifier), which in essence makes your VLAN numbering scheme locally significant.
Also, since the numbering for VNI’s is a 24 bit identifier, you have alot more flexibility than just the regular 4096 definable VLAN’s. (12 Bits .1q tags)
Each endpoint that does the encapsulation/decapsulation is called a VTEP (VxLAN Tunnel EndPoint). In our example this would be CSR3 and CSR5.
After the VxLAN header, the packet is further encapsulated into a UDP packet and forwarded across the network. This is a great solution as it doesnt impose any technical restrictions on the core of the network. Only the VTEPs needs to understand VxLAN (and probably have hardware acceleration for it as well).
Since we wont be using BGP EVPN, we will rely solely on multicasting in the network to establish who is the Continue reading
ISIS Authentication types (packet captures)
In this post i would like to highlight a couple of “features” of ISIS.
More specifically the authentication mechanism used and how it looks in the data plane.
I will do this by configuring a couple of routers and configure the 2 authentication types available. I will then look at packet captures taken from the link between them and illustrate how its used by the ISIS process.
The 2 types of Authentication are link-level authentication of the Hello messages used to establish an adjacency and the second type is the authentication used to authenticate the LSP’s (Link State Packet) themselves.
First off, here is the extremely simple topology, but its all thats required for this purpose:
Simple, right? 2 routers with 1 link between them on Gig1. They are both running ISIS level-2-only mode, which means they will only try and establish a L2 adjacency with their neighbors. Each router has a loopback interface, which is also advertised into ISIS.
First off, lets look at the relevant configuration of CSR-02 for the Link-level authentication:
key chain MY-CHAIN key 1 key-string WIPPIE ! interface GigabitEthernet1 ip address 10.1.2.2 255.255.255.0 ip router isis 1 negotiation auto no Continue reading
Progress update – 10/07-2017
Hello folks,
Im currently going through the INE DC videos and learning a lot about fabrics and how they work along with a fair bit of UCS information on top of that!
Im spending an average of 2.5 hours on weekdays for study and a bit more in the weekends when time permits.
I still have no firm commitment to the CCIE DC track, but at some point I need to commit to it and really get behind it. One of these days 
I mentioned it to the wife-to-be a couple of days ago and while she didn’t applaud the idea, at least she wasn’t firmly against it, which is always something I guess! Its very important for me to have my family behind me in these endeavours!
Im still a bit concerned about the lack of rack rentals for DCv2 from INE, which is something I need to have in place before I order a bootcamp or more training materials from them. As people know by now, I really do my best learning in front of the “system”, trying out what works and what doesn’t.
Now to spin up a few N9K’s in the lab and play around Continue reading
New Lab Server & random updates
New Server:
So I just completed a purchase off eBay for a new server for my lab purposes.
For a while now I’ve been limited to 32Gb of memory on my old ESXi server, which is really more like 20Gb when my regular servers have had their share. Running a combination of different types of devices, each taking at least 4Gb of memory, doesn’t leave much room for larger labs.
I decided to go with a “real” server this time around. So I got an older Cisco UCS C200 M2 server with 2 x Xeon 5570 processors and an additional 96 Gb ram (on top of the 24 it came with). That stil leaves room for a bit of memory upgrades in the future (it supports a total of 192Gb) (had a budget on this one, so couldn’t go crazy).
Work:
Work has been crazy lately. 2 of my Team members just resigned so a lot of workload has to be shifted until we find suitable replacements. That means I’ve been working 65+ hour work weeks for a while now. Something that I dont find even remotely amusing to be honest. But I’ve been reassured that everything is being done Continue reading
Onto the next one…
Yesterday I passed the CCNA-W exam. Now onto the next partner certification I need to do before summer.
Its called 500-452 ENCWE – Enterprise Networks Core and WAN Essentials and a large part of it involves iWAN, which im not too familiar with.
To that effect I have ordered the official Cisco Press iWAN book and downloaded all the presentations I could find on iWAN from CiscoLive365. That should keep me busy for the foreseeable future 
I will hopefully be doing some labs on iWAN and will post any findings I have here. It should be fun!
Im still debating whether or not I will goto CLUS this year. Whats really pulling me over there is the people I rarely get to meet. I need to make up my mind soon though.
Take care!
/Kim
So whats next?
I’ve had a little time readjusting after my exam and I’ve given some thought on what to keep me busy next.
Basically I have 3 projects to keep me busy for the next foreseeable future.
1) CCNA-Wireless
My boss came to me a week ago and tasked me with this. He was very humble about it, which was amusing. I will be allocated some time from my normal work projects to study for the exam, which is really helpful. Fortunally some of my CCDE study friends are also going for this exam, so I wont be going down the road alone on this one either.
Im actually quite positive about this as its a technology area I have not really paid much attention to and its very different in what im used to. A shakeup is good every now and then 
2) The IOS-XR Specialist exam
This is one I have been looking quite forward to for some time. Its basically an exam about all things IOS-XR and the platforms that supports it. I tried studying for this before I decided to go down the CCDE path, so it will be nice to pick back up.
3) Work on improving Continue reading
CCDE – A different Journey
Wednesday the 22nd of February, in a testing center in the middle of London, my journey towards achieving the CCDE certification, finally ended in me passing this beast of an exam.
This learning journey was a very different one than either of my CCIE’s. Whereas going for the CCIE meant spending countless hours at the command-line, the CCDE meant spending all of those hours reading and discussing use cases for technologies. It also meant stepping my toes into the business side, picking up the “Why?” behind selecting a specific technology.
It all started a few years ago when my friend Daniel (lostintransit.se) and I started going back and forth on how to approach this thing. We decided we should team up and share notes, discuss technologies and generally use each other as a sparring partner.
At that point I had already decided, that this was going to be a marathon for me, because I could at the time, not allocate as much time each day for study, as I had been for the CCIE’s. Fast forward a good amount of time and I had finally passed the written part of the exam and was ready to Continue reading
A look at Auto-Tunnel Mesh Groups
In this post I would like to give a demonstration of using the Auto-Tunnel Mesh group feature.
As you may know, manual MPLS-TE tunnels are first and foremost unidirectional, meaning that if you do them between two PE nodes, you have to do a tunnel in each direction with the local PE node being the headend.
Now imagine if your network had 10 PE routers and you wanted to do a full mesh between them, this can become pretty burdensome and error-prone.
Thankfully there’s a method to avoid doing this manual configuration and instead rely on your IGP to signal its willingness to become part of a TE “Mesh”. Thats what the Auto-Tunnel Mesh Group feature is all about!
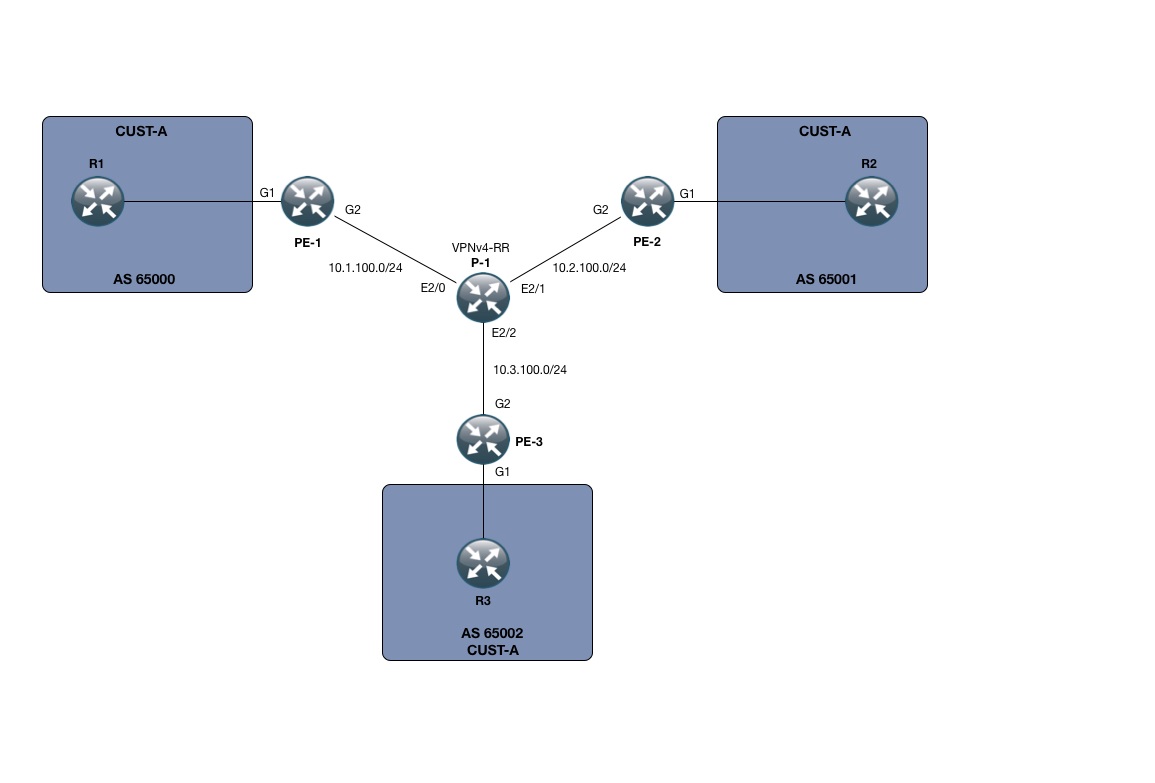
In my small SP setup, I only have 3 PE devices, namely PE-1, PE-2 and PE-3. I also only have one P node, called P-1.
However small this setup is, its enough to demonstrate the power of the Auto-Tunnel mesh functionality.
Beyond that, I have setup a small MPLS L3 VPN service for customer CUST-A, which has a presence on all 3 PE nodes. The VPNv4 address-family is using a RR which for this purpose is P-1.
We are running OSPF Continue reading
Happy New Year
Hi Everyone,
I wish you all a Happy New Year!
Currently im very busy studying for my 2nd attempt at the CCDE Practical exam.
I have it booked for the next slot, which is February 22nd in London.
Thankfully there are more and more material available for the CCDE than just a year ago. One of my primary sources are the study group which I have mentioned before, which Daniel (lostintransit.se) and I started way back.
Im also going through the INE scenarios as well as LiveLessons available through a Safari subscription. Those are really good and I highly recommend them.
One of the primary things im practicing at the moment is picking up business requirements from a given scenario. This is quite hard as im at heart an implementation-focused guy. But its good to learn something new and very useful.
If you are not following it just yet, I can highly recommend the “Unleashing CCDE” site on Cisco Learning Network (https://learningnetwork.cisco.com/blogs/unleashing-ccde). There are alot of good posts there on how to pick up these “soft” skills.
I will keep the blog updated with my study progress through February and we’ll see what happens February 22nd 
Take Care.
/Kim