Author Archives: Blargh
Author Archives: Blargh
I found a security bug in GNU cpio and thought I’d write down the story of that. It’s not the most interesting bug in the world, but it may still be an interesting story to some.
The whole thing started with me looking at the manpage
-H, --format=FORMAT
Use given archive FORMAT. Valid formats are (the number in
parentheses gives maximum size for individual archive member):
bin The obsolete binary format. (2147483647 bytes)
odc The old (POSIX.1) portable format. (8589934591 bytes)
newc The new (SVR4) portable format, which supports file
systems having more than 65536 i-nodes. (4294967295 bytes)
crc The new (SVR4) portable format with a checksum added.
tar The old tar format. (8589934591 bytes)
ustar The POSIX.1 tar format. Also recognizes GNU tar archives, which are
similar but not identical. (8589934591 bytes)
hpbin The obsolete binary format used by HPUX's cpio (which stores device
files differently).
hpodc The portable format used by HPUX's cpio (which stores device files
differently).
What’s wrong with this picture? Those are some very odd size
limits. 2GiB and 4GiB I understand, as it’s 32bit signed and unsigned
int. But tar having a max size of 8GiB? 33 bits? That Continue reading
I’ve used OpenBSD on and off since 2.1. More back then than in the last 10 years or so though, so I thought I’d try it again.
What triggered this was me finding a silly bug in GNU cpio that has existed with a “FIXME” comment since at least 1994. I checked OpenBSD to see if it had a related bug, but as expected no it was just fine.
I don’t quite remember why I stopped using OpenBSD for servers, but I do remember filesystem corruption on “unexpected power disconnections” (even with softdep turned on), which I’ve never really seen on Linux.
That and that fewer things “just worked” than with Linux, which matters more when I installed more random things than I do now. I’ve become a lot more minimalist. Probably due to less spare time. Life is better when you don’t run things like PHP (not that OpenBSD doesn’t support PHP, just an example) or your own email server with various antispam tooling, and other things.
This is all experience from running OpenBSD on a server. On my next laptop I intend to try running OpenBSD on the dektop, and will see if that more ad-hoc environment Continue reading
TCP_MD5 (RFC 2385) is something that doesn’t come up often. There’s a couple fo reasons for that, good and bad.
I used it with tlssh, but this should explain why I didn’t enable it by default.
In short it’s a TCP option that adds an MD5-based signature to every TCP packet. It signs the source and destination IP address, and the ports, and the payload. That way the data is both authenticated and integrity protected.
When an endpoint enables TCP MD5, all unsigned packets (including SYN packets) are silently dropped. For a signed connection it’s not even possible for an eavesdropper to reset the connection, since the RST would need to be signed.
It’s used by the BGP protocol to set a password on the connection, instead of sending the password in the handshake. If the password doesn’t match the TCP connection doesn’t even establish.
But outside of BGP it’s essentially not used, which is a shame. If we could enable it for any TCP service it’d add a preshared key and completely replace the silly port knocking. It probably couldn’t replace user passwords, but it could add a layer and greatly reduce attack surface much Continue reading
What is the point of amateur radio? To learn about radio, propagation, the electromagnetic spectrum in general. To understand how it works, and maybe even build or modify your own equipment. The license, after all, is the only legal way to use the electromagnetic spectrum at interesting power levels.
In order to learn we must be able to inspect; To tinker, or at the very least have access to a specification we can build from.
Some amateur radio operators seem to complain that people don’t build their own radios anymore. That they just buy a box and antenna and are now consumers. This is not what I’m talking about here. First, you know in principle how your radio works. And you could build one that could replace it. Would it be as good as a modern fancy rig? Of course not. It wouldn’t be as good, but you could build one, and you could use it just as well as the bought one.
And if you learn enough, and tweak enough with the rig and antenna system, you could build something better for your particular environment.
When I first learned that D-Star used a proprietary voice codec I couldn’t understand Continue reading
JT65 is a slow protocol for propagation reports. In short it takes 60 seconds to send 13 characters. Then you wait 60 seconds for a reply, and repeat.
The 60 seconds are actually 1 second silence, 46.872 second of signal, then another 12.128 seconds of silence, allowing for clock drifts and for a human to choose the reply.
The mode is this slow in order to add a lot of redundancy and to make it easier for the receiver to dig out a signal way below the noise floor. It was originally meant for making contacts by bouncing signals off the moon, which has a path loss of ~250dB. Someone even managed a JT65 moonbounce on 10 Watts using JT65 with gear you and I could buy/build!. That’s the power of a low energy light bulb!
I wanted to do propagation experiments with SDR, with low power in various frequency bands, but couldn’t find a GNURadio module for JT65. So I made one.
The JT65 specification is very well written, except for the parts it says “the code is the specification”. Which would normally be fine, but the code is in Fortran and Fortran is terrible.
JT65A is Continue reading
The Go standard library is generally great, but some parts have replacements that are just plain better and remove frustrations that you may have not even realised were frustrations. Here are my recommendations for every Go program.
I wouldn’t recommend that anyone use the standard library version of these for any purpose, since better alternatives exist.
This list may expand in the future.
The standard router is fine, but very low level. Here’s some of the features that makes it vital.
With the standard router you have to manually check that the method is
what you expect it to be, and if the same endpoint has both GET and
POST then you have to route that yourself. With gorilla/mux it’s as simple as:
r := mux.NewRouter()
get := r.Method("GET").Subrouter()
post := r.Method("POST").Subrouter()
get.HandleFunc("/", handleRoot)
get.HandleFunc("/items", handleListItems)
post.HandleFunc("/items", handleUploadItem)
You can also assert that headers are in place, for example to check
X-Requested-With because some API endpoints should not be allowed in
cross-domain XHR requests. Adding it to the router instead of manual
checks simplifies code and reduces risk of forgetting to add the
check.
With Continue reading
My interest in SDR got me into Amateur Radio. One reason was that so that I could transmit on non-ISM bands and with more power. Turns out the 2.3GHz band available to Amateur Radio operators is much quieter than the 2.4GHz band where WiFi, bluetooth, microwave ovens, drones, cordless phones and everything else lives. Shocker, I know.
Amateur radio doesn’t just have voice and morse code, there’s also digital modes.
A popular mode is FT8. It’s only used to exchange signal reports, so there’s no chatting. It’s in fact often practically unattended.
It’s a good way to check the quality of your radio setup, and the radio propagation properties that depend on how grumpy the ionosphere is at the moment.
If you transmit, even if you nobody replies, you’ll be able to see on PSKReporter who heard you, which is useful.
Because propagation should be pretty much symmetric, receiving a strong signal should mean that two-way communication is possible with the station. Though FT8 is a slow mode that will get through where others won’t, so a weak FT8 signal means that any voice communication is very unlikely to get through.
Unfortunately unlike WSPR the standard FT8 Continue reading
Short post this time.
If you on Linux set up your Yubikey in smartcard mode then you can use that Yubikey without any setup at all on Windows.
Just open
PuttyWincrypt, put
in the host to log in to, and under Connection > SSH > Auth set
Private key file for authentication to cert://*, then click
Open.
It’ll ask for the PIN, you’ll have to touch the Yubikey when it’s blinking, and you’re in.
I’ve blogged before about how the new integrity-checking filesystem in Windows, ReFS, doesn’t actually have integrity checking turned on by default. It’s pretty silly that for a modern filesystem meant to compete with ZFS and BtrFS, to have the main 21st century feature turned off by default. But it’s not quite ridiculous. Not yet.
Now it turns out that scrubbing is only supported on Windows Server
I used to say that Windows 10 is the best Windows ever, and that Microsoft kinda won my trust back. But what the hell?
I contacted Microsoft support over chat, who first suggested I do a system restore (sigh). But after I insisted that they please confirm that it’s supposed to work confirmed that no that only ships with Windows Server.
It’s not even clear from their pricing if I need the $882 Standard Edition or the $6,155 Datacenter Edition. Either one is way too much for such a standard feature.
What the hell, Microsoft? All I want is a checksumming file system. Either provide it, or don’t. Don’t give me a checksumming filesystem that can’t be Continue reading
For every day that passes I like bitcoin less. It’s bad for the world.
I have ranted about this many times, and it’s time I consolidate these rants into a blog post.
We’ll see with time if this rant ages poorly or not.
These would be good things:
Bitcoin today is pretty much only good for two things:
If you’re not doing one of those, then don’t use Bitcoin.
If you are an online store then sure, accept Bitcoin. There’s moral problems with supporting Bitcoin (see rest of post), but as long as you immediately convert to fiat currency when you receive payment it’s fine for you. There are even companies out there that’ll guarantee an exchange rate so that you never have to get into the business of currency.
You may say that Bitcoin can be used to get money out of China, or into Brazil, or to enable shopping of “things that should not be called ‘drugs’ anyway”, but you have to admit that no matter what you think Continue reading
The recent bug in WPA2 has a worst case outcome that is the same as using a wifi without a password: People can sniff, maybe inject… it’s not great but you connect to open wifi at Starbucks anyway, and you’re fine with that because you visit sites with HTTPS and SSH. Eventually your client will get a fix too, so the whole thing is pretty “meh”.
But there’s a reason I call it “WPA2 bug” and I call the recent issue with Infineon key generation “the Infineon disaster”. It’s much bigger. It seems like the whole of Estonia needs to re-issue ID cards, and several years worth of PC-, smartcard-, Yubikey, and other production have been generating bad keys. And these keys will stick around.
From now until forever when you generate, use, or accept RSA keys you have to check for these weak keys. I assume OpenSSH will if it hasn’t already.
But then what? It’s not like servers can just reject these keys, or it’ll lock people out. And it’s not clear that an adversary even has your public key for SSH. And you can’t crack the key if you don’t have the public half. Maybe a Continue reading
In this post I’ll describe some experiences I had with the Internet in China, and what it means for people making websites in the west in order to reach expats, visitors, and anyone else in China. So this should be useful information even if you don’t care about China as a market at all.
This blog post may be updated, as I have more thoughts on Internet in China.
My subjective experience is that “Internet in China” is an oxymoron. How exactly is there “Internet” without Google, Facebook, and Twitter? When attaching an Android phone to a WiFi in China it even says “Wi-Fi has no Internet access”.
OK, that’s not entirely serious. Especially since I’m obviously not aware of what the Chinese language Internet looks like, not speaking or reading Chinese. Baidu looks like it largely provides the services Google does (search, maps, …), but they’re pretty much not translated. The Baidu Map app seems fine, but is almost useless if you don’t speak Chinese. The one thing it’s good for is that unlike Google Maps (if you can even get to it. see below) it actually shows you a correct location within China.
But more importantly it’s not Continue reading
I made a tool to check if your TPM chip is bad. Well, it extracts the SRK public key and you can then use marcan’s tool to easily check if the key is good or bad.
Example use:
$ g++ -o check-srk -std=gnu++11 check-srk.cc -ltspi -lssl -lcrypto 2>&1 && ./check-srk
Size: 2048
Outputting modulus…
8490234823904890234823904823904890238490238490238490238490[…]893428490823904231
$ wget https://gist.githubusercontent.com/marcan/fc87aa78085c2b6f979aefc73fdc381f/raw/526bc2f2249a2e3f5d4450c7c412e0dbf57b2288/roca_test.py
[…]
$ python roca_test.py 8490234823904890234823904823904890238490238490238490238490[…]893428490823904231
Vuln!
(use -s if you have an SRK PIN)
If the SRK is weak then not only are very likely anything else you generated in the TPM weak, but also anything generated outside the TPM and imported is crackable, since your blobs are encrypted using this crackable SRK key.
Because of the Infineon Disaster of 2017 lots of TPM and Yubikey keys have to be regenerated.
I have previously blogged about how to create these keys inside the yubikey, so here’s just the short version of how to redo it by generating the key in software and importing it into the yubikey.
When it appears to stall, that’s when it’s waiting for a touch.
openssl genrsa -out key.pem 2048
openssl rsa -in key.pem -outform PEM -pubout -out public.pem
yubico-piv-tool -s 9a -a import-key --touch-policy=always -i key.pem
yubico-piv-tool -a verify-pin -a selfsign-certificate -s 9a -S '/CN=my SSH key/' -i public.pem -o cert.pem
yubico-piv-tool -a import-certificate -s 9a -i cert.pem
rm key.pem public.pem cert.pem
ssh-keygen -D /usr/lib/x86_64-linux-gnu/opensc-pkcs11.so -e
Delete all mentions of previous key. It’s good to have a disaster plan ahead of time if keys need to be replaced, but if you don’t have one:
~/.ssh/authorized_keys)Because of the Infineon Disaster of 2017 lots of TPM and Yubikey keys have to be regenerated.
I have previously blogged about how to create these keys inside the yubikey, so here’s just the short version of how to redo it by generating the key in software and importing it into the yubikey.
When it appears to stall, that’s when it’s waiting for a touch.
openssl genrsa -out key.pem 2048
openssl rsa -in key.pem -outform PEM -pubout -out public.pem
yubico-piv-tool -s 9a -a import-key --touch-policy=always -i key.pem
yubico-piv-tool -a verify-pin -a selfsign-certificate -s 9a -S '/CN=my SSH key/' -i public.pem -o cert.pem
yubico-piv-tool -a import-certificate -s 9a -i cert.pem
rm key.pem public.pem cert.pem
ssh-keygen -D /usr/lib/x86_64-linux-gnu/opensc-pkcs11.so -e
Delete all mentions of previous key. It’s good to have a disaster plan ahead of time if keys need to be replaced, but if you don’t have one:
~/.ssh/authorized_keys)I really don’t like the trend of filesystem authors to only care about filesystem integrity by default. How about having seat belt for your data integrity by default and let people turn it off if they want to compromise correctness for performance?
What I didn’t know is that ReFS integrity is not on by default. Only metadata integrity.
It’s also not visible or changeable in the UI (which is why I assumed they’d done the right thing), which is strange to me, this being Windows. No, you have to drop down into Microsoft’s crappy CLI.
PS E:\> Get-Item '*' | Get-FileIntegrity
FileName Enabled Enforced
-------- ------- --------
E:\SomeDirectory False True
E:\SomeOtherDirectory False True
E:\SomeFile.txt False True
[...]
Fuck you, Microsoft.
Of course Get-Item doesn’t do recursion. Why would it? That would
make sense.
PS E:\> Get-Children -Recurse 'E:\SomeDirectory' | Get-FileIntegrity
FileName Enabled Enforced
-------- ------- --------
E:\SomeDirectory\foo.txt False True
[...]
Both commands are needed. The first command sets the new default for the root directory, and the second adds checksums to all existing files and directories.
PS E:\> Continue readingTwo interesting things I saw when listening to the output from my microwave:
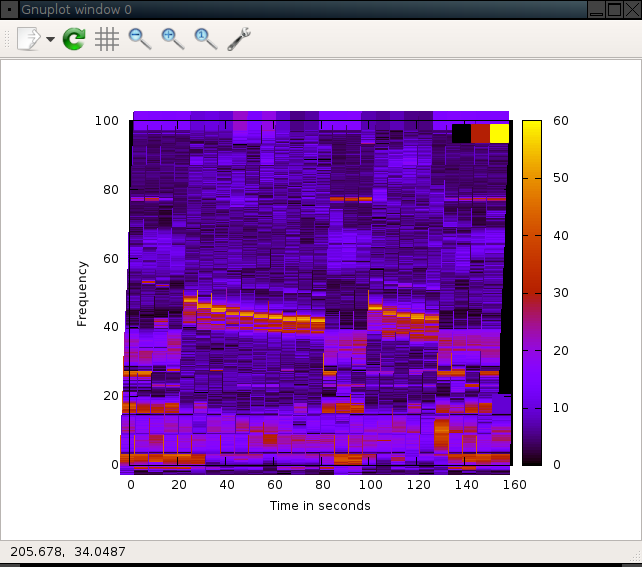
Separate measurement some rooms away.
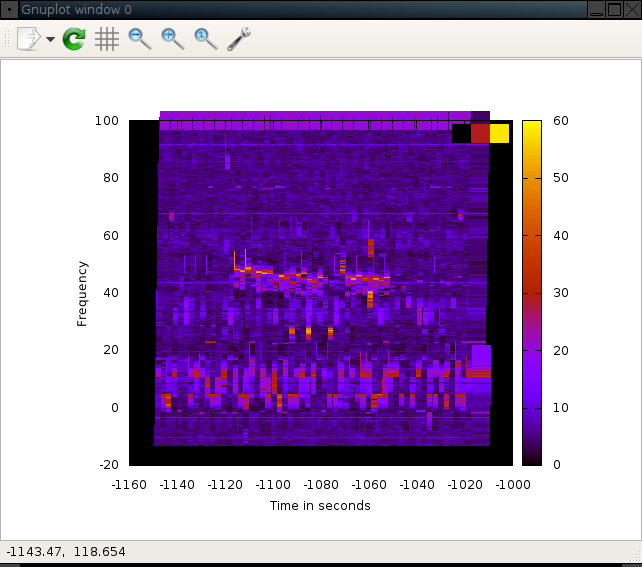
# Edit usrp_spectrum_sense.py so that it prints time.time() instead of datetime.now()
./usrp_spectrum_sense.py --dwell-delay=0.1 -A RX2 -s 8000000 --real-time 2.4e9 2.5e9 > near-microwave.txt
# Edit near-microwave to remove the stupid verbose messages from the top.
cat > microwave.plot << EOF
set view map
set size ratio .9
set object 1 rect from graph 0, graph 0 to graph 1, graph 1 back
set object 1 rect fc rgb "black" fillstyle solid 1.0
set xlabel 'Time in seconds'
set ylabel 'Frequency'
set zlabel 'dB'
set terminal epslatex color
set output "near-microwave.eps"
splot 'near-microwave.txt' using ($1-1496693552.11):((($5/1000-2400000)/1000)):4 with points pointtype 5 pointsize 3 palette linewidth 30 title 'Signal'
EOF
gnuplot microwave.plot
convert near-microwave.{eps,png}
I can’t have GNUPlot output PNG directly because it hangs.
The magic value 1496693552.11 is the first timestamp in the file.
Something I’ve been playing with lately is software defined radio with GNURadio. I’m not good at it yet, but I’ve managed to decode the signals from a couple of things.
This is my step-by-step for how I decoded data from a boiler thermostat. I’m not saying it’s the best way, or even a good way. But it’s what got me there.
Often this is written on the device itself. Other times it’s in the manual. If not, then more research is needed, such as by trying to find the manufacturer on fcc.gov or similar.
In this case it was easy. The manual said “868 MHz”, which is in the SRD860 band.
When I poked at the controls of the thermostat, saying “please make the room 25 degrees”, the thermostat must send this data to the boiler. I could hear the boiler start up and shut down, so there must be something sent between me pressing the buttons and I heard the results.
I started by centering around 868.5 Mhz with 1Msps. The minimum for the RTL-SDR is 900ksps, so even if you wanted to see less than 1MHz you need Continue reading
Let’s say you have some TCP connections to your local system that you
want to kill. You could kill the process that handles the connection,
but that may also kill other connections, so that’s not great. You
could also put in a firewall rule that will cause the connection to be
reset. But that won’t work on a connection that’s idle (also if one
side is initiator then using this method the other side would not tear
down its side of the connection). There’s
tcpkill, but it needs to
sniff the network to find the TCP sequence numbers, and again that
won’t work for an idle connection.
Ideally for these long-running connections TCP keepalive would be enabled. But sometimes it’s not. (e.g. it’s not on by default for gRPC TCP connections, and they certainly can be long-running and idle).
You could also do this by attaching a debugger and calling
shutdown(2) on the sockets, but having the daemon calling unexpected
syscalls thus getting into an unexpected state doesn’t really make for
a stable system. Also attaching a debugger hangs the daemon while
you’re attached to it.
This post documents how to do this on a Debian system.
I managed to get an SSH client working using an SSH pubkey protected by a TPM.
This is not needed, since TPM operations only need well known SRK PIN, not owner PIN, to do useful stuff. I only document it here in case you want to do it. Microsoft recommends against it.
Set OSManagedAuthLevel to 4
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\TPM\OSManagedAuthLevel 2 -> 4
Reboot.
Clear TPM
Run tpm.msc and choose “Clear TPM”. The machine will reboot
and ask you to press F12 or something for physical proof of
presence to clear it.
Set owner password from within tpm.msc
Create key
tpmvscmgr.exe create /name "myhostnamehere VSC" /pin prompt /adminkey random /generate
PIN must be at least 8 characters.
Create CSR
Create a new text file req.inf:
[NewRequest]
Subject = "CN=myhostnamehere"
Keylength = 2048
Exportable = FALSE
UserProtected = TRUE
MachineKeySet = FALSE
ProviderName = "Microsoft Base Smart Card Crypto Provider"
ProviderType = 1
RequestType = PKCS10
KeyUsage = 0x80
certreq -new -f req.inf myhostname.csr
If you get any errors, just reboot and try again with the command that failed.
Get the CSR signed by any Continue reading