Author Archives: Ivan Pepelnjak
Author Archives: Ivan Pepelnjak
Would you like to start a tech blog but don’t know how to do it? Ethan Banks put together a phenomenal how-to guide in his Developing Content & Gathering Research For Your Tech Blog article.
Oh, and please use Hugo (or similar) and use walled gardens like LinkedIn solely to post summaries and links to your content. You want to be in control and retain ownership of your work, right?
Last week, I had the privilege of discussing Disaster Recovery Myths at the DEEP Conference. I also took the opportunity to attend several other presentations covering topics such as eBPF, open-source supply pipelines, tips for bug bounty hunters, and SSE.
TL&DR: I loved the experience ;)
In the previous blog posts, we explored three fundamental EVPN designs: we don’t need EVPN, IBGP EVPN AF over IGP-advertised loopbacks (the way EVPN was designed to be used) and EBGP-only EVPN (running the EVPN AF in parallel with the IPv4 AF).
Now we’re entering Wonderland: the somewhat unusual1 things vendors do to make their existing stuff work while also pretending to look cool2. We’ll start with EBGP-over-EBGP, and to understand why someone would want to do something like that, we have to go back to the basics.
Similarly to how it handles VRFs, netlab automatically creates VLANs on a lab device if the device uses them on any access- or trunk link or if the VLAN is mentioned in the node vlans dictionary.
If the VLAN is an IRB VLAN (which can be modified globally or per node with the VLAN mode parameter), netlab also creates the VLAN (or SVI, or BVI) interface. But how do you specify the parameters of the VLAN interface?

I had a Disaster Recovery Myths and Reality talk at the DEEP conference yesterday. The presentation is already online, but unfortunately, not everyone made it to Zadar (your loss, but I get it).
To counteract that, I made the first part of the Designing Active-Active and Disaster Recovery Data Centers webinar public. Hope you’ll like it.
Now and then, someone asks how netlab deals with reboots (or power failures or crashes) of the server it’s running on.
TL&DR: It doesn’t. However…
netlab is a CLI command that acts as an umbrella orchestration layer for Vagrant and Containerlab. It does not run as a cron job, init script, or service and thus cannot be invoked when a server is booted.
Long long time ago1, in an ancient town far far away2, an old-school networking Jeddi3 was driving us toward a convent4 where we had an SDN workshop5. While we were stuck in the morning traffic jam, an enthusiastic engineer sitting beside me wanted to know my opinion about per-prefix and per-VRF MPLS/VPN label allocation.
At that time, I had lived in a comfortable Cisco IOS bubble for way too long, so my answer was along the lines of “Say what???” Nicola Modena6 quickly expanded my horizons, and I said, “Gee, I have to write a blog post about that!” As you can see, it took me over a decade.
From a very high-level perspective, OSPF and IS-IS are quite similar. Both were created in the Stone Age of networking, and both differentiate between multi-access LAN segments and point-to-point serial interfaces. Unfortunately, that approach no longer works in the Ethernet Everywhere world where most of the point-to-point links look like LAN segments, so we always have to change the default settings to make an IGP work better.
That’s what you’ll do in today’s lab exercise, which also explains the behind-the-scenes differences between point-to-point and multi-access links and the intricate world of three-way handshake.

I never know what to expect when I’m invited to speak at a regional (or in-country) Network Operator Group (NOG) meeting. Sometimes, it turns out to be a large conference (PLNOG and ITNOG come to mind); other times, it’s just a few people gathered around free donuts and coffee1. Last week’s Croatian NOG (NOG.HR) meeting was in the Goldilocks zone between the extremes: plenty of interested networking engineers, but not large enough to be overpowering.
Also, it was such a nice experience ;)

Michele Chubirka (currently at Google) kindly allowed me to make her PCI DSS for Networking Engineers webinar public (available without registration or login).
The webinar covers an older version of PCI DSS (version 3.0; the current version is 4.0.1), but as fundamentals never change, you might still find it useful.
Now that we know a bit more about addresses in a networking stack (read the whole series) and why CLNP uses node addresses while TCP/IP uses interface addresses, let’s see how they solve common addressing problems like finding adjacent nodes.
Let’s start with the elephant in the room: how do you know whether you can reach a host you want to communicate with directly? In the following diagram, how does A know whether B is sitting next to it?
Dmytro Shypovalov wrote a great series of detailed posts on Egress Peer Engineering:
Have fun!
In previous BGP policy lab exercises, we covered several mechanisms you can use to ensure your autonomous system is not leaking transit routes (because bad things happen when you do, particularly when your upstream ISP is clueless).
As you probably know by now, there’s always more than one way to get something done with BGP. Today, we’ll explore how you can use the NO_EXPORT community to filter transit routes.
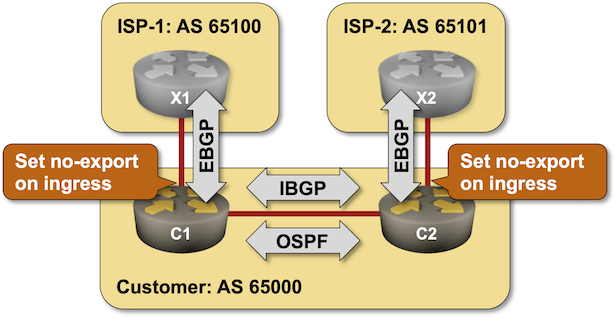
Click here to start the lab in your browser using GitHub Codespaces (or set up your own lab infrastructure). After starting the lab environment, change the directory to policy/d-no-export and execute netlab up.
A while ago, Eric Chou invited me to a friendly chat in his Network Automation Nerds podcast.
The episode was published a few days ago; I hope you’ll enjoy listening to it.
In the first exercise in the IS-IS labs series, you configured IS-IS routing for IPv4. Before moving on to more complex topics, let’s explore the data structures IS-IS created to represent your network.

In the previous blog posts, we explored the simplest possible IBGP-based EVPN design and made it scalable with BGP route reflectors.
Now, imagine someone persuaded you that EBGP is better than any IGP (OSPF or IS-IS) when building a data center fabric. You’re running EBGP sessions between the leaf- and the spine switches and exchanging IPv4 and IPv6 prefixes over those EBGP sessions. Can you use the same EBGP sessions for EVPN?
TL&DR: It depends™.
netlab release 1.9.1 brings packet capture capabilities and numerous routing features:
We also added support for Cisco IOSv layer-2 image. You’ll find more details in the release notes.
I spent a few days in a beautiful place with suboptimal Internet connectivity. The only thing I could do whenever I got bored (without waiting for the Internet gnomes to hand-carry the packets across the mountain passes) was to fix the BGP labs on a Ubuntu VM running on my MacBook Air (hint: it all works).
Big things first. I added validation to these labs:
After publishing the EVPN L3VPN lab-building instructions, I published a deep dive into EVPN and data-plane data structures. You might have missed it, as it was published in mid-August.
In the first exercise in the IS-IS labs series, you’ll configure IS-IS routing for IPv4. The basic configuration is trivial, but you’ll also have to tweak the defaults that most vendors got wrong (we’ll discuss why those defaults are wrong in the next lab exercises).

I also tried to make the IS-IS labs more than just lab exercises. Each exercise includes a bit of background information or IS-IS theory; this one describes generic OSI addresses (NSAPs) and router addresses (NETs).