Author Archives: Laura Ferguson
Author Archives: Laura Ferguson
Why accountability, not capability, is the real bottleneck for enterprise agentic AI, and what security leaders need to do about it before regulators force the issue.
Every enterprise is building AI agents. Marketing has one summarizing campaign performance. Engineering has one triaging incidents. Customer support has one resolving tickets. Finance has one processing invoices. And increasingly, those agents are talking to each other: calling tools, accessing databases, delegating tasks across complex multi-hop chains.
But here’s the question nobody wants to hear at 3 a.m. when something goes wrong: who authorized that action, what policy permitted it, and what’s the full chain of events?
For most enterprises, the honest answer is: nobody knows. That’s not a governance problem — it’s an AI agent accountability crisis.
The data paints a stark picture. McKinsey research found that 80% of organizations have already encountered risky behavior from AI agents. These actions were unintended, unauthorized, or outside acceptable guardrails. Yet only about one-third of organizations report meaningful governance maturity. Gartner predicts that over 40% of agentic AI projects will be canceled by the end of 2027 due to escalating costs, unclear business value, or inadequate risk controls.
This Continue reading
Welcome to the Calico monthly roundup: July edition! From open source news to live events, we have exciting updates to share—let’s get into it!
Exclusive: Cloud and container security leaders round table and dinner
An exclusive, invite-only round table and dinner designed specifically for cloud and container security leaders. This intimate gathering will discuss today’s most pressing issues facing cloud and container security. |
Your Guide to Observability
This guide explains what observability is and shows you how to use Calico’s observability tools. With these tools, you can find and troubleshoot issues with workload communications, performance, and operations in a Kubernetes cluster. |
Customer case study: Playtech
Calico seamlessly integrated with Amazon EKS GitOps model to enhance Playtech’s application security. Read the case study to learn more. |
Calico Live stream: Mitigating RCE zero-day attacks with Calico security policies – This live session on July 31, 2024 will examine the capabilities of Calico security policies to mitigate RCE attacks in a cloud-native environment. You can watch the live session on YouTube or LinkedIn.
Calico enhancements
Welcome to the Calico monthly roundup: June edition! From open source news to live events, we have exciting updates to share—let’s get into it!
S&P Global 451 Market Insight: Tigera Provides Most Comprehensive CNAPP
Learn how Tigera differentiates itself from competitors by focusing on runtime security, aligning with the rapidly growing market category and how it is one of the strong players in this segment. |
Your Guide to Observability
This guide explains what observability is and shows you how to use Calico’s observability tools. With these tools, you can find and troubleshoot issues with workload communications, performance, and operations in a Kubernetes cluster.Read case study. |
Customer case study: eHealth
Calico helped eHealth gain visibility and implement zero-trust security controls on Amazon EKS. Read the case study to learn more. |
Kubernetes network policies: 4 pain points and how to address them – Learn about the challenges of implementing Kubernetes network policies and how to simplify their management and enhance security using Calico. Read blog post.
The power of Kubevirt and Calico – Unlock the combined power of Kubevirt and Calico for your Kubernetes environments. Learn how to streamline VM management, Continue reading
Welcome to the Calico monthly roundup: May edition! From open source news to live events, we have exciting updates to share—let’s get into it!
What’s new in Calico
Discover the latest enhancements in Calico for Spring 2024, featuring new security capabilities, improved visualization tools, and an advanced workload-centric WAF to streamline and secure your Kubernetes operations. |
Customer case study: NuraLogix
AI-driven healthtech company, NuraLogix, improves security and compliance on Amazon EKS using Calico Cloud. |
Join us at CloudNative SecurityCon 2024 in Seattle We’re gearing up for CloudNative SecurityCon 2024, on June 26 and 27 in Seattle. Be sure to swing by our booth and learn about exciting container networking updates. Plus, pick up some cool new Calico swag! Stay tuned for details. We’re gearing up for CloudNative SecurityCon 2024, on June 26 and 27 in Seattle. Be sure to swing by our booth and learn about exciting container networking updates. Plus, pick up some cool new Calico swag! Stay tuned for details.
|

S&P Global 451 Market Insight: Tigera Provides Most Comprehensive CNAPP Learn how Tigera differentiates itself from competitors by focusing on runtime security, aligning with the rapidly growing market category and how it is one of the strong players in this segment. |
What’s new in 3.28 – Explore the new features in Calico 3.28, including a Grafana dashboard for Typha performance monitoring, Continue reading
Last week we had the pleasure of attending KubeCon + CloudNativeCon EU in Paris, France. It was a fantastic event where we once again had the opportunity to engage in meaningful conversations about Kubernetes, container security, and the latest developments in the open source ecosystem. We also hosted CalicoCon 2024, a co-located event, to talk about our favorite subject: Calico! Let’s take a look at some of the highlights from the conference.
A large group of KubeCon attendees joined us on March 19th for a full-day event to explore the trends, strategies, and technologies making waves in the Kubernetes networking, security, and observability world. The day included a keynote on Project Calico’s past, present, and future, plus multiple presentations and workshops delivered by Calico engineers that provided a deep dive into topics such as eBPF, Windows HNS, multi-cluster mesh, best practices for network policies, scale, performance, encryption, and compliance.



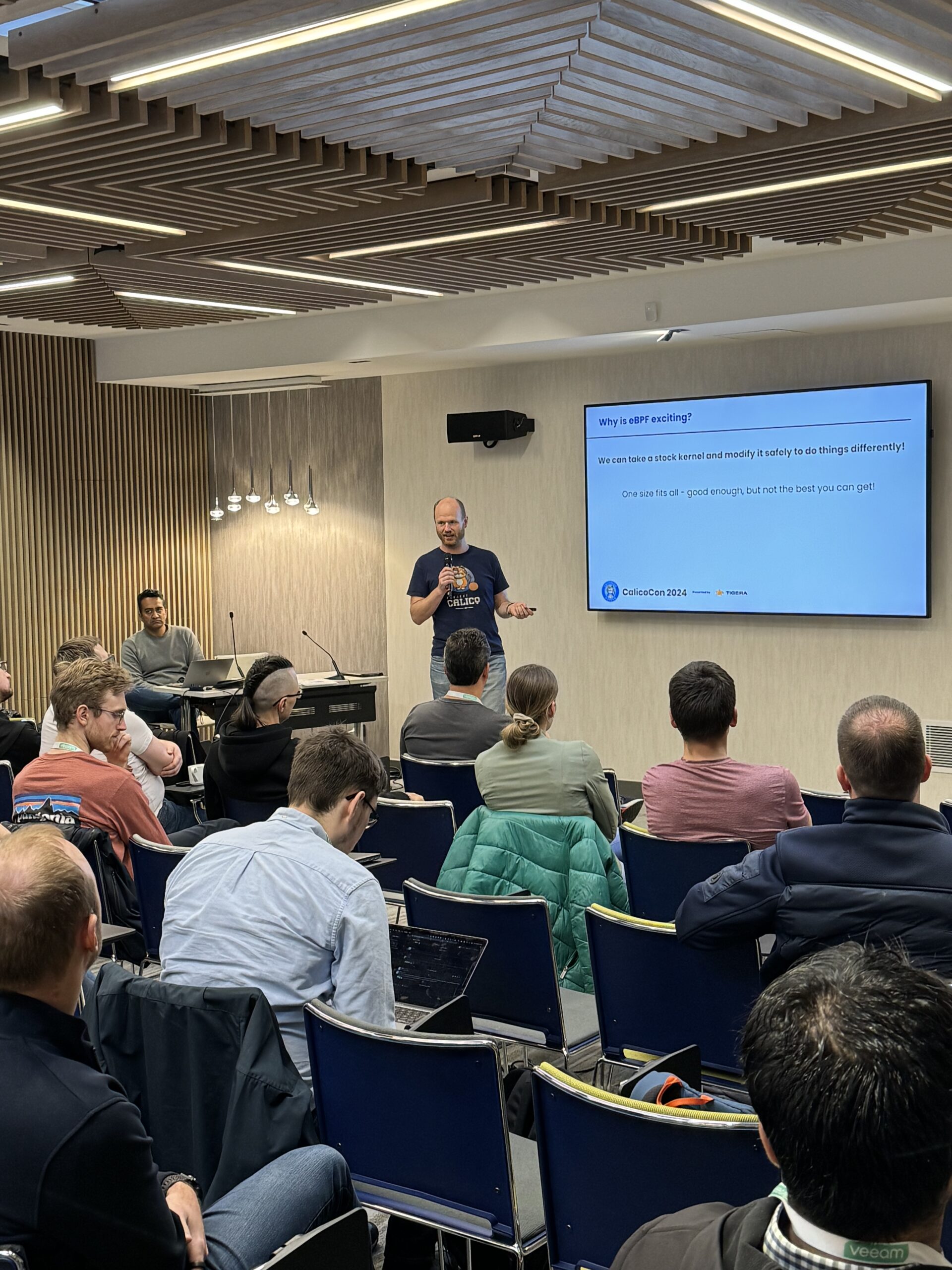
A good time was had by all in attendance, and two lucky winners of our raffles each took home a pair of AirPods! The day ended with happy hour and networking, where attendees had a chance to meet other Calico users as well as the engineers and leadership Continue reading
Welcome to the Calico monthly roundup: January edition! From open source news to live events, we have exciting updates to share—let’s get into it!
| Join us at CalicoCon 2024 in Paris We are thrilled to announce that CalicoCon 2024 will be held on March 19 in Paris as a KubeCon + CloudNativeCon Europe 2024 co-located event. Join us for an immersive event focused on the latest trends, strategies, and technologies in Kubernetes networking, security, and observability. Limited spots are available, so register now to secure your spot. |
Customer case study: NuraLogix
AI-driven healthtech company, NuraLogix, improves security and compliance on Amazon EKS using Calico Cloud. |
Tigera has achieved AWS Security Competency status!
Tigera has gained a new AWS Security Competency, which we’re proud to add to our already existing AWS Containers Software Competency. Read about the addition of our newest security competency. |
Securely connect EKS workloads to approved SaaS with Calico Egress Gateway Learn how Calico Egress Gateway for AWS Elastic IP provides a valuable tool to bolster an organization’s defenses and ensure secure and dependable connections to trusted SaaS platforms. |
*NEW* GitHub Discussion forum – Looking for Continue reading
As 2023 comes to a close, we’re happy to report that we’ve had a successful year full of powerful product advancements and notable third-party recognition.
With these new enhancements, Calico is the industry’s most complete solution for securing and observing Kubernetes environments.
Calico Open Source users represent a robust sample of IT professionals from across industries and use cases. We polled these users to better understand their needs and compiled the insights into Continue reading
Welcome to the Calico monthly roundup: December edition! From open source news to live events, we have exciting updates to share—let’s get into it!
Tigera has achieved AWS Security Competency status!
Tigera has gained a new AWS Security Competency, which we’re proud to add to our already existing AWS Containers Software Competency. Read about the addition of our newest security competency. |
Find your Cluster Security Score
Calico Cloud is releasing new capabilities for security posture management called Security Scoring and Recommended Actions. Start measuring and tracking your security posture. |
Customer case study: Leader-bet
Calico provides container security and compliance for online gaming giant, Leader-bet. Read our case study to learn more. |
 Comparing NGFW container firewalls with Calico container firewall Comparing NGFW container firewalls with Calico container firewall
Learn how to establish robust firewall policies with just code or a single click for advanced threat protection using behavior-based learning and IDS/IPS integrated with the firewall. |
Calico v3.27 is out  and there are a lot of new features, updates, and improvements that are packed into this release. Here is a breakdown of the most important changes:
and there are a lot of new features, updates, and improvements that are packed into this release. Here is a breakdown of the most important changes:
Welcome to the Calico monthly roundup: November edition! From open source news to live events, we have exciting updates to share—let’s get into it!
Find your Cluster Security Score
Calico Cloud is releasing new capabilities for security posture management called Security Scoring and Recommended Actions. Start measuring and tracking your security posture. |
Customer case study: Boundless Software
Calico Cloud enabled SOC 2 compliance for Boundless Software while also drastically reducing onboarding times for the company’s customers. Read our case study to find out how. |
 Secure Kubernetes traffic with Calico Egress gateway Secure Kubernetes traffic with Calico Egress gateway
Discover how egress gateways enable users to assign meaningful network identity to selected traffic so that this information can be further used by traditional tools to enforce granular policies to traffic based on identity or bandwidth. |
We’re happy to announce that Tigera recently achieved Amazon Web Services (AWS) Security Competency status. This designation recognizes the security capabilities of Tigera’s Calico Cloud platform in helping customers secure their AWS workloads and achieve their cloud security goals.
To receive the designation, AWS Partners must possess deep AWS expertise and deliver solutions seamlessly on AWS. After evaluating Calico Cloud’s security capabilities, including vulnerability management, container- and network-based threat detection, observability and security policy lifecycle, AWS found it surpassed the competency requirements.

This is the second AWS competency Tigera has achieved and we’re proud to add this new competency to our existing AWS Containers Software Competency. Our team is dedicated to helping companies achieve their Kubernetes and container security goals by combining our technology with the range of powerful security tools AWS provides.
Read the full press release for more details or visit us on the AWS Marketplace.
The post Tigera has achieved AWS Security Competency status! appeared first on Tigera.
Thanks to everyone who joined us in Chicago this month at KubeCon + CloudNativeCon NA 2023. We had a chance to have many meaningful conversations about Kubernetes and container security, the latest in the open source ecosystem, and of course—Calico! Here are some highlights from the conference.
We had a ton of visitors at our booth this year and were happy to catch up with old friends as well as meet new ones. Tech problems for business needs, such as how to provide fixed IPs to workloads for communication outside of the Kubernetes cluster instead of architectural debates about the underlying dataplane, was a popular topic of discussion. Another was runtime security at the workload level (default-deny/zero trust). The issue of visibility into workload communication at scale overlaid with effective security policies also came up often. We were all too happy to show how Calico can help!

Those who joined us for our private cruise party enjoyed a guided architecture tour of the spectacular Chicago lakefront. The evening went swimmingly and offered our guests a chance to unwind and network while enjoying great food and an open bar, against a backdrop of glittering skyscrapers.


Welcome to the Calico monthly roundup: October edition! From open source news to live events, we have exciting updates to share—let’s get into it!
Join us at KubeCon + CloudNativeCon North America 2023
We’re gearing up for KubeCon + CloudNativeCon 2023 in Chicago. Join us at booth #G13 for exciting Kubernetes security updates and pick up some cool new Calico swag! |
Customer case study: eHealth
Calico provides visibility and zero-trust security controls for eHealth on Amazon EKS. Read our new case study to find out how. |
|
Learn why a traditional firewall architecture doesn’t work for modern cloud-native applications and results in a huge resource drain in a production environment. |
The State of Calico Open Source: Usage & Adoption Report 2023 Get insights into Calico’s adoption across container and Kubernetes environments, in terms of platforms, data planes, and policies. |
Welcome to the Calico monthly roundup: September edition! From open source news to live events, we have exciting updates to share—let’s get into it!
|
Discover how you can automate security, ensure consistency, and tightly align security with development practices in a microservices environment. |
The State of Calico Open Source: Usage & Adoption Report 2023 Get insights into Calico’s adoption across container and Kubernetes environments, in terms of platforms, data planes, and policies. |
Welcome to the Calico monthly roundup: August edition! From open source news to live events, we have exciting updates to share—let’s get into it!
*NEW* The State of Calico Open Source: Usage & Adoption Report 2023 Get insights into Calico’s adoption across container and Kubernetes environments, in terms of platforms, data planes, and policies. |

Customer case study: HanseMerkur Using Calico, HanseMerkur was able to reduce infrastructure overhead and achieve organizational compliance. Read our new case study to find out how. |
We are excited to announce the publication of our 2023 State of Calico Open Source, Usage & Adoption report! The report compiles survey results from more than 1,200 Calico Open Source users from around the world, who are actively using Calico in their container and Kubernetes environments. It sheds light on how they are using Calico across various environments, while also highlighting different aspects of Calico’s adoption in terms of platforms, data planes, and policies.
The report shows that Calico continues to be a pivotal part of the container and Kubernetes ecosystem, finding large-scale adoption across major Kubernetes platforms.
Welcome to the Calico monthly roundup: July edition! From open source news to live events, we have exciting updates to share—let’s get into it!
Customer case study: Upwork Using Calico, Upwork was able to enforce zero-trust security for its newly migrated containerized applications on Amazon EKS. Read our new case study to find out how. |
Container security – Self-paced workshop This self-paced tutorial is designed to help you prevent, detect, and stop breaches in containers and Kubernetes. Learn how to secure all aspects of your containerized applications—all at your own pace! |
The challenges companies face regarding private and professional data protection are more important today than ever. In the modern enterprise, cloud computing and the use of cloud-native architectures enable unmatched performance, flexibility, velocity, and innovation. However, as digitalization pushes applications and services to the cloud, cyber criminals’ intrusion techniques have become increasingly sophisticated. To stay current with advancing technologies, doubling or tripling security measures is a must.
To understand the critical need for advanced cybersecurity measures, we turned to an expert in the industry, Ratan Tipirneni, President and CEO of Tigera – a company providing active, zero-trust-based security for cloud-native applications running on containers and Kubernetes.
Q: How did the idea of Tigera originate? What has your journey been like so far?
It was over six years ago that Tigera created Project Calico, an open-source container networking and security project.
As containers and Kubernetes adoption grew and organizations started using Kubernetes at scale, Tigera recognized the industry’s need for more advanced security and observability. Tigera has since grown from the Project Calico open-source project to a container security innovator that now supports many Fortune 100 companies across the globe.
Tigera’s continued success comes from listening to customers’ needs, understanding Continue reading
Welcome to the Calico monthly roundup: June edition! From open source news to live events, we have exciting updates to share—let’s get into it!

Customer case study: Box Using Calico, Box achieved zero-trust security and policy automation at scale in a multi-cluster environment. Read our new case study to find out how. |
Is your container environment compliant with NIST guidelines? This assessment helps you compare your current security posture against the NIST Cybersecurity Framework and assess your readiness to detect and protect against cyberattacks. |
During RSA Conference 2023, Utpal Bhatt sat down with SiliconANGLE & theCUBE host, John Furrier, to talk cloud-native security. Watch the full interview below.
Here’s a sneak peak of what’s inside…
“Cloud-native applications have fundamentally changed how security gets done. There are a lot of challenges that cloud-native applications bring to the table, given their large attack surface. You have attack vectors in your coding, CI/CD pipeline, deployment, and runtime. And I think that’s what organizations are realizing, that hey, this is fundamentally a different kind of architecture and we need to look at it differently.” —Utpal Bhatt, CMO at Tigera
“Cloud-native applications have fundamentally changed how security gets done. And there are a lot of challenges that cloud-native applications bring to the table, which is what organizations are realizing. If you think about organizations moving into the cloud, the majority have traditionally done a lift and shift. But now they’re recognizing that in order to get the economics right, they need to start developing cloud-native technologies, which are highly distributed, ephemeral, and transient. So all your standard security tools just really don’t work in that environment because you have a really large Continue reading
We are proud to announce that we have won the 2022 Microsoft OSS on Azure Partner of the Year award! The Microsoft Partner of the Year Awards recognize Microsoft partners that have developed and delivered outstanding Microsoft-based applications, services, and devices during the past year. Awards were classified in various categories, with honorees chosen from a set of more than 3,900 submitted nominations from more than 100 countries worldwide. Tigera was recognized for providing outstanding solutions and services for open source on Azure.
Since June 2021, Tigera and Microsoft Azure together provide users with active build, deploy, and runtime security with full-stack observability for securing, monitoring, and troubleshooting containers on Azure and AKS. Tigera works closely with Microsoft to offer networking, security, and observability for containerized workloads running in Microsoft Azure.
We are very proud to be recognized as Microsoft’s Partner of the Year for OSS on Azure as it re-affirms the reach and pervasiveness of Tigera’s Calico Open Source solution for container networking and security on Azure and AKS. As enterprises standardize across Microsoft Azure, customers require a resource-efficient and scalable networking and security solution that protects the workloads in a hybrid environment extending from the cloud (Azure and Continue reading