Cloudflare Peering Portal – Beta

It can be a big deal for Internet users when Cloudflare rolls into town. After our recent Mongolia launch, we received lots of feedback from happy customers that all of a sudden, Internet performance noticeably improved.
As a result, it's not a surprising that we regularly receive requests from all over the world to either peer with our network, or to host a node. However, potential partners are always keen to know just how much traffic will be served over that link. What performance benefits can end-users expect? How much upstream traffic will the ISP save? What new bandwidth will they have available for traffic management?
Starting today, ISPs and hosting providers can request a login to the Cloudflare Peering Portal to find the answers to these questions. After validating ownership of your ASN, the Cloudflare network team will provide a login to the newly launched Peering Portal - Beta. You can find more information at: cloudflare.com/partners/peering-portal/
What problem does peering solve?
If you're new to the core infrastructure of the Internet, the best way to understand peering is to frame the problems it solves:
- Bandwidth costs money
- Internet users don't like slow websites
- Network operators have limited Continue reading
Encrypt that SNI: Firefox edition
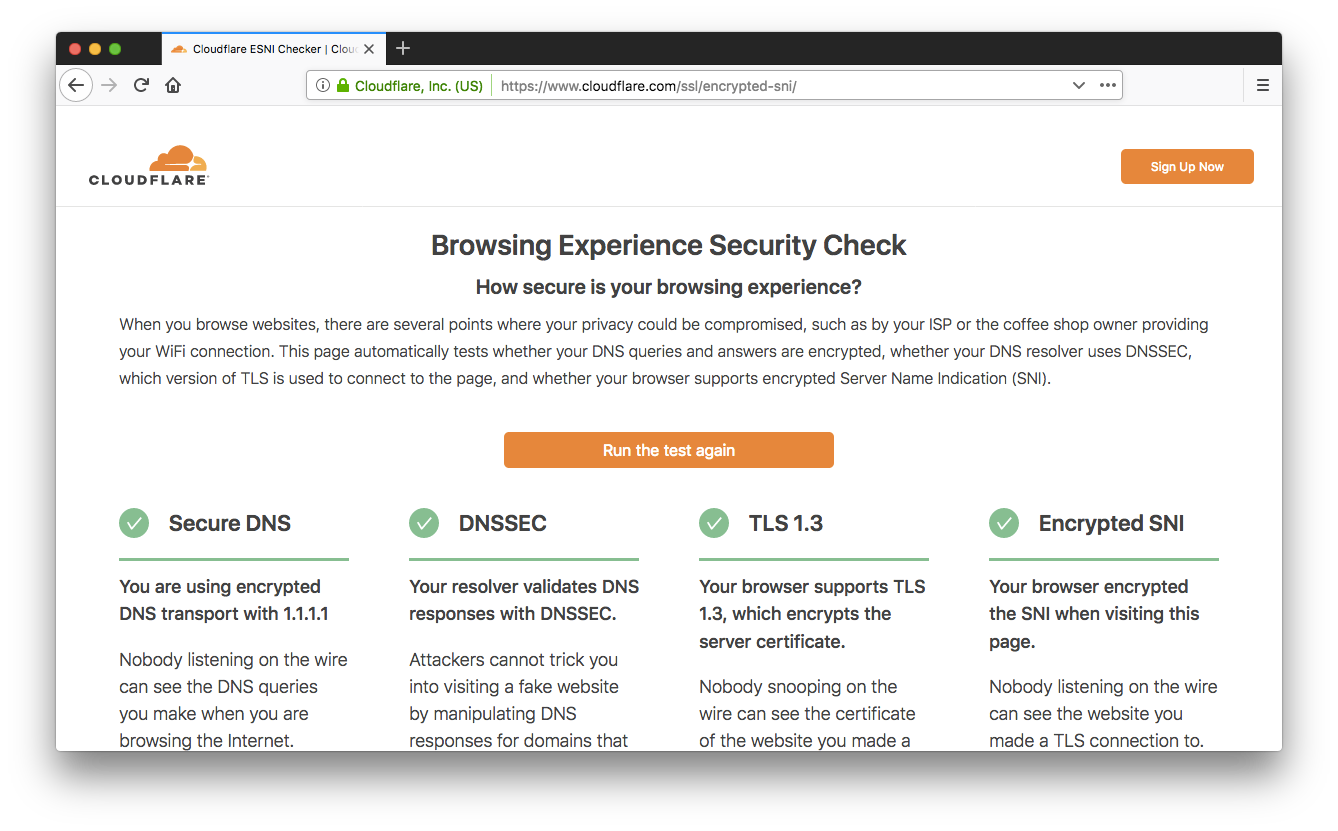
A couple of weeks ago we announced support for the encrypted Server Name Indication (SNI) TLS extension (ESNI for short). As promised, our friends at Mozilla landed support for ESNI in Firefox Nightly, so you can now browse Cloudflare websites without leaking the plaintext SNI TLS extension to on-path observers (ISPs, coffee-shop owners, firewalls, …). Today we'll show you how to enable it and how to get full marks on our Browsing Experience Security Check.

Here comes the night
The first step is to download and install the very latest Firefox Nightly build, or, if you have Nightly already installed, make sure it’s up to date.
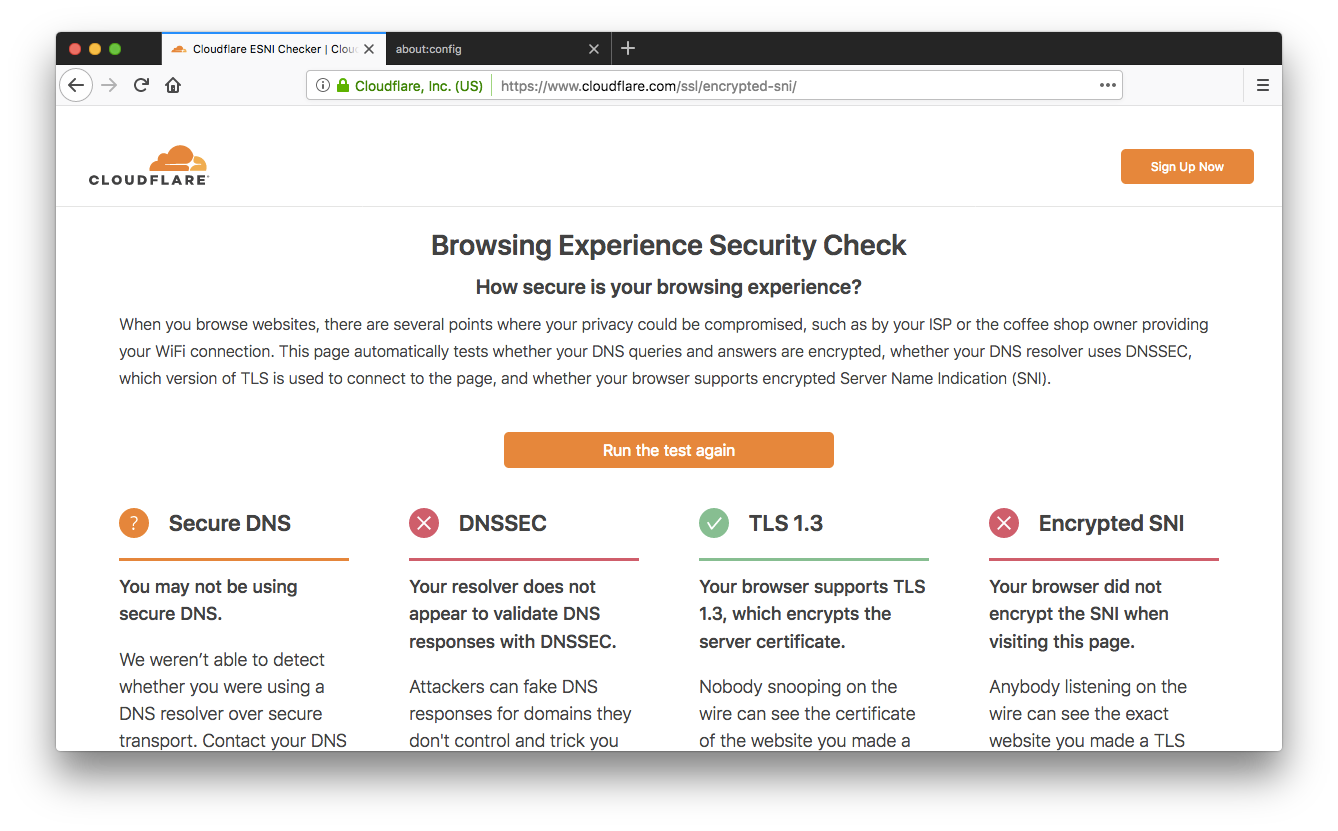
When we announced our support for ESNI we also created a test page you can point your browser to https://encryptedsni.com which checks whether your browser / DNS configuration is providing a more secure browsing experience by using secure DNS transport, DNSSEC validation, TLS 1.3 & ESNI itself when it connects to our test page. Before you make any changes to your Firefox configuration, you might well see a result something like this:
So, room for improvement! Next, head to the about:config page and look for the network.security.esni.enabled Continue reading
Warum ich Cloudflare helfe in Deutschland, Österreich und der Schweiz zu wachsen
Warum Cloudflare ?
Ich übernehme bei Cloudflare die Verantwortung für die DACH Region (Deutschland, Austria & Switzerland-CH), um das Geschäft von Cloudflare in Deutschland, Österreich und der Schweiz zu erweitern. Die einzigartige Mission von Cloudflare ein besseres Internet zu gestalten, ist der Grund, warum ich diese Verantwortung übernommen habe. Heute kann ich es kaum erwarten dieses Ziel zu erreichen.
Cloudflare trägt dazu bei 10 Millionen Domains schneller und sicherer zu machen indem die Kunden gegen eine große Anzahl von Online-Angriffen geschützt werden und gleichzeitig die Verfügbarkeit garantiert wird. Dies ist die Grundlage für jedes erfolgreiche Geschäft.
Sicherheit, Datenschutz und Geschwindigkeit sind Schlüsselfunktionen für fast jedes Unternehmen: von sehr großen traditionellen bis hin zu reinen Online-Unternehmen oder Einzelpersonen, die ihre eigene persönliche Marke aufbauen. Dazu könnte ich endlos weitere Beispiele nennen und je mehr ich über Cloudflare’s Mission erfahre desto mehr bin ich begeistert.
Eine von Cloudflare’s größten Stärken ist das globale Netzwerk.
Cloudflare verfügt bereits über Rechenzentren in sieben Städten der DACH Region (weitere folgen), um sicherzustellen, dass das Internet für die Nutzer in der Region schnell, sicher und zuverlässig ist.
Ich bin stolz, das erste Büro in Deutschland eröffnen zu dürfen. Gleichzeitig habe ich Continue reading
Why I’m helping Cloudflare grow in Germany, Austria, and Switzerland
Why Cloudflare?
I am incredibly excited to announce that I’m joining Cloudflare as the Head of DACH to help to expand Cloudflare’s demand in Germany, Austria, and Switzerland. Having been in the technology industry for many years, Cloudflare’s mission to help build a better Internet was frankly the reason I joined, and I’m now very eager to start working towards this.
I quickly learned how Cloudflare helps to speed up and secure over 10 million Internet properties by protecting these customers from a wide range of online attacks and providing the reliability needed to run strong businesses. Security, privacy, and performance are key drivers for almost every business: from large traditional enterprises to purely online businesses and even individuals building their own personal brand. I could go on and on. The more I learned, the more excited I became.
One of Cloudflare’s major strengths is its global network. Cloudflare already has data centers in seven cities in the DACH region (with more to come) helping to ensure the Internet is fast, safe, and reliable for users online in the region. So while I get the honor of opening our first office in Germany (in Munich), I loved that Cloudflare had Continue reading
My First Grace Hopper Celebration


Cloudflare #GHC18 team
I am 25+ years into my career in technology, and this was the very first time I attended a conference geared towards women.
A couple of weeks ago I went to Grace Hopper Celebration (#GHC18), and I can still feel the exuberant energy from the 22,000 women over the intensive 3 day conference. I attended with our Cloudflare team; our purpose was to connect with women in the greater tech community and recruit new talent to join our team and mission to help build a better Internet.
Cloudflare prioritizes GHC because we recognize that diversity in our company, and particularly in our technical departments, is crucial to our success. We believe that the best companies are diverse companies. This was Cloudflare’s second time sponsoring GHC, and I was part of the planning committee. This year I headed to the event with 20 of my colleagues to meet all of the incredible attendees, hold on-site interviews, and even host our own Cloudflare panel and luncheon.
Getting to #GHC18
Early Tuesday morning, the day before the conference, as I joined the Southwest Airlines boarding line at Oakland Airport, my fellow passengers were not the usual contingent of Continue reading
A Question of Timing


When considering website performance, the term TTFB - time to first byte - crops up regularly. Often we see measurements from cURL and Chrome, and this article will show what timings those tools can produce, including time to first byte, and discuss whether this is the measurement you are really looking for.
Timing with cURL
cURL is an excellent tool for debugging web requests, and it includes the ability to take timing measurements. Let’s take an example website www.zasag.mn (the Mongolian government), and measure how long a request to its home page takes:
First configure the output format for cURL in ~/.curlrc:
$ cat .curlrc
-w "dnslookup: %{time_namelookup} | connect: %{time_connect} | appconnect: %{time_appconnect} | pretransfer: %{time_pretransfer} | starttransfer: %{time_starttransfer} | total: %{time_total} | size: %{size_download}\n"Now connect to the site dropping the output (-o /dev/null) since we’re only interested in the timing:
$ curl -so /dev/null https://www.zasag.mn
dnslookup: 1.510 | connect: 1.757 | appconnect: 2.256 | pretransfer: 2.259 |
starttransfer: 2.506 | total: 3.001 | size: 53107These timings are in seconds. Depending on your version of cURL, you may Continue reading
Serverless Rust with Cloudflare Workers
The Workers team just announced support for WebAssembly (WASM) within Workers. If you saw my post on Internet Native Apps, you'll know that I believe WebAssembly will play a big part in the apps of the future.
It's exciting times for Rust developers. Cloudflare's Serverless Platform, Cloudflare Workers, allows you to compile your code to WASM, upload to 150+ data centers and invoke those functions just as easily as if they were JavaScript functions. Today I'm going to convert my lipsum generator to use Rust and explore the developer experience (hint: it's already pretty nice).
The Workers teams notes in the documentation:
...WASM is not always the right tool for the job. For lightweight tasks like redirecting a request to a different URL or checking an authorization token, sticking to pure JavaScript is probably both faster and easier than WASM. WASM programs operate in their own separate memory space, which means that it's necessary to copy data in and out of that space in order to operate on it. Code that mostly interacts with external objects without doing any serious "number crunching" likely does not benefit from WASM.
OK, I'm unlikely to gain significant performance improvements on this particular Continue reading
DC CyberWeek Is Here!


Photo by Sarah Ferrante Goodrich / Unsplash
This October is the 15th annual National Cybersecurity Awareness Month in the United States, a collaboration between the US government and industry to raise awareness about the part we can all play in staying more secure online. Here at Cloudflare, where our mission is to help build a better internet, we look forward to this month all year.
As part of this month-long education campaign, Cloudflare is participating in D.C CyberWeek this week, the largest cybersecurity festival in the U.S, taking place in Washington, DC. This year’s event is expected to have over 10,000 attendees, more than 100 events, and feature representatives from over 180 agencies, private companies, and service providers. We will join with other leaders in cybersecurity, to share best practices, find ways to collaborate, and work to achieve common goals.
Along with the United States, the European Union also runs a month-long cyber awareness campaign in October, with the initiative having started back in 2012. The aim of this advocacy campaign is similar: promoting cybersecurity among citizens and organizations, and providing information on available tools and resources. Watch our CTO speak to some of the main considerations around Continue reading
Optimizing HTTP/2 prioritization with BBR and tcp_notsent_lowat
Getting the best end-user performance from HTTP/2 requires good support for resource prioritization. While most web servers support HTTP/2 prioritization, getting it to work well all the way to the browser requires a fair bit of coordination across the networking stack. This article will expose some of the interactions between the web server, Operating System and network and how to tune a server to optimize performance for end users.
tl;dr
On Linux 4.9 kernels and later, enable BBR congestion control and set tcp_notsent_lowat to 16KB for HTTP/2 prioritization to work reliably. This can be done in /etc/sysctl.conf:
net.core.default_qdisc = fq
net.ipv4.tcp_congestion_control = bbr
net.ipv4.tcp_notsent_lowat = 16384
Browsers and Request Prioritization
A single web page is made up of dozens to hundreds of separate pieces of content that a web browser pulls together to create and present to the user. The main content (HTML) for the page you are visiting is a list of instructions on how to construct the page and the browser goes through the instructions from beginning to end to figure out everything it needs to load and how to put it all together. Each piece of content requires a Continue reading
Happy National Coming Out Day: Stories from Proudflare

Today is the 30th Anniversary of National Coming Out Day. We wanted to share some coming out stories from members of Proudflare and draw attention to resources the Human Rights Campaign provides to those who are thinking about coming out or wish to be supportive of those who come out to them.
About National Coming Out Day
On October 11, 1987, about 500,000 people marched on Washington for Lesbian and Gay Rights. This was the second demonstration of this type in the capital and it resulted in the formation of several LGBTQ organizations.
In the late 1980s, the LGBTQ community recognized that they often reacted defensively to anti LGBTQIA+ actions and the community came up with the idea of a national day for celebrating coming out. The anniversary of the 1987 march was chosen as that national day.
Each year on October 11th, National Coming Out Day continues to promote a safe world for LGBTQ individuals to live truthfully and openly.
Source: https://www.hrc.org/resources/the-history-of-coming-out
Coming out stories from Proudflare
Here are seven examples of the coming out stories that surfaced from a company-wide awareness campaign. I hope you’ll enjoy reading these and will find inspiration in them. Let’s Continue reading
Graceful upgrades in Go

The idea behind graceful upgrades is to swap out the configuration and code of a process while it is running, without anyone noticing it. If this sounds error prone, dangerous, undesirable and in general a bad idea – I’m with you. However, sometimes you really need them. Usually this happens in an environment where there is no load balancing layer. We have these at Cloudflare, which led to us investigating and implementing various solutions to this problem.

Coincidentally, implementing graceful upgrades involves some fun low-level systems programming, which is probably why there are already a bajillion options out there. Read on to learn what trade-offs there are, and why you should really really use the Go library we are about to open source. For the impatient, the code is on github and you can read the documentation on godoc.
The basics
So what does it mean for a process to perform a graceful upgrade? Let’s use a web server as an example: we want to be able to fire HTTP requests at it, and never see an error because a graceful upgrade is happening.
We know that HTTP uses TCP under the Continue reading
Introducing Single Sign-On for the Cloudflare Dashboard
The Challenge of Managing User Access to SaaS Applications
As the number of SaaS services people use everyday grows, it has become more challenging to juggle the number of password and multi-factor authentication combinations users have to keep track of to get online.
Adopting identity services have allowed companies to centralize employee authentication. With Cloudflare Access, companies can ensure employees use a company managed identity provider when accessing websites behind Cloudflare. Last week, Sam published a blog on how Cloudflare has made it easier to connect Cloudflare Access to the Atlassian suite of tools.
Since Cloudflare has simplified access control for corporate applications, many enterprise customers have commonly asked for the ability to extend the same ease of access and control to the Cloudflare dashboard itself.
Single Sign-On for the Cloudflare Dashboard
Today, we are announcing support for enterprise customers to use single sign-on (SSO) through their identity provider to access the Cloudflare dashboard.
Cloudflare is a critical piece of infrastructure for customers, and SSO ensures that customers can apply the same authentication policies to access the Cloudflare dashboard as other critical resources.
Once onboarded for SSO, all company user logins to the Cloudflare dashboard redirect to the customer’s identity provider. Once all required authentication checks complete successfully, the user is seamlessly redirected back to dash.cloudflare.com and logged in.
Leveraging Access & Workers to Build SSO
At Cloudflare, we dogfood our own services as both a way to make them better for our customers and to make developing new services more efficient and robust. With SSO, this is no different. Authentication configurations are managed through Access, which allows us to launch with support for the same identity providers available in Access today, including SAML.
Cloudflare is 8 years old and we built our user authentication system way before Cloudflare Access existed. In order to connect Access to our existing authentication system, we built a Cloudflare Worker that converts Access authentication tokens to our own authentication tokens. This greatly simplified the code changes required in our system, and results in faster SSO logins because the Worker runs at the network edge and reduces the number of round trips required to authenticate users.
In addition to leveraging Cloudflare services to build Single Sign-On, we are moving all Cloudflare employees to use SSO through our existing G Suite setup. This ensures Cloudflare can uniformly enforce multi-factor authentication policies for the services we protect with Cloudflare itself.
How to Start using SSO for the Cloudflare Dashboard
Cloudflare Enterprise customers can reach out to their Customer Success Manager to learn how to start using SSO to log-in to the Cloudflare dashboard. If you are interested in using SSO yourself and becoming a Cloudflare Enterprise customer, then please get in touch.
A Tour Inside Cloudflare’s G9 Servers

Cloudflare operates at a significant scale, handling nearly 10% of the Internet HTTP requests that is at peak more than 25 trillion requests through our network every month. To ensure this is as efficient as possible, we own and operate all the equipment in our 154 locations around the world in order to process the volume of traffic that flows through our network. We spend a significant amount of time specing and designing servers that makes up our network to meet our ever changing and growing demands. On regular intervals, we will take everything we've learned about our last generation of hardware and refresh each component with the next generation…
If the above paragraph sounds familiar, it’s a reflecting glance to where we were 5 years ago using today’s numbers. We’ve done so much progress engineering and developing our tools with the latest tech through the years by pushing ourselves at getting smarter in what we do.
Here though we’re going to blog about muscle.
Since the last time we blogged about our G4 servers, we’ve iterated one generation each of the past 5 years. Our latest generation is now the G9 server. From a G4 server comprising 12 Intel Continue reading
Mapping Factorio with Leaflet
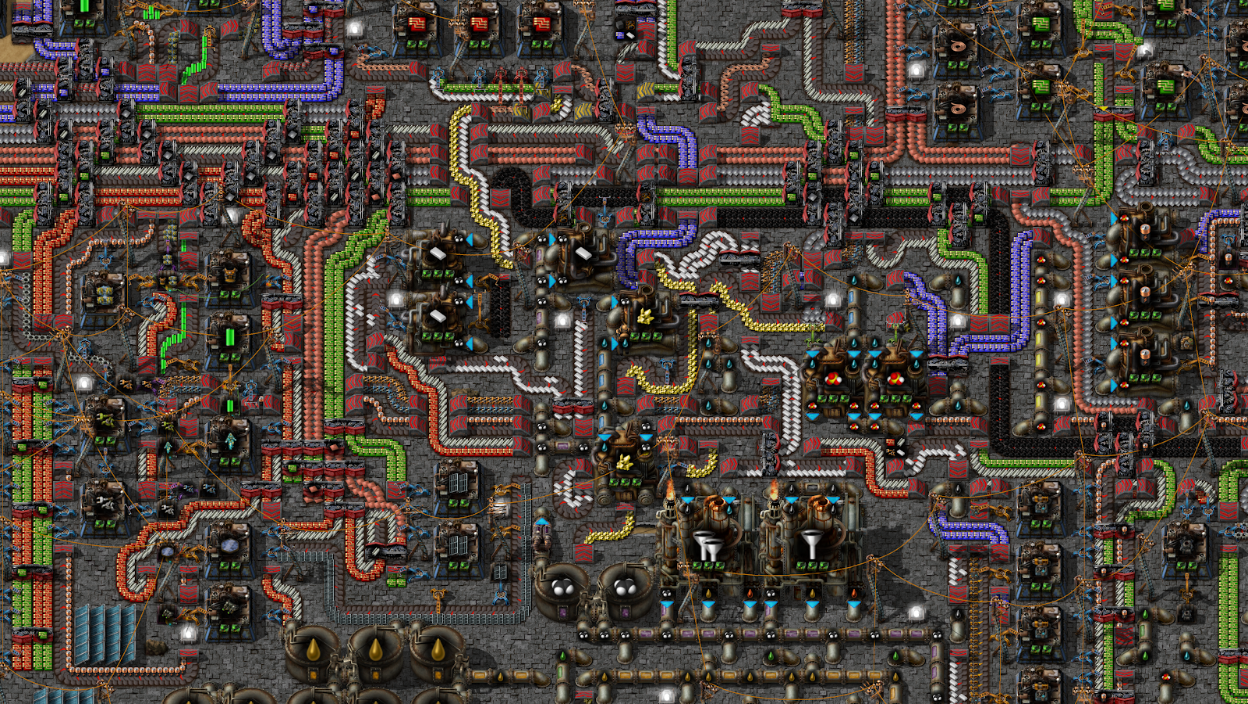
The following is a guest post by Jacob Hands, Creator of FactorioMaps.com. He is building a community site for the game Factorio centered around sharing user creations.
Factorio is a game about building and maintaining factories. Players mine resources, research new technology and automate production. Resources move along the production line through multiple means of transportation such as belts and trains. Once production starts getting up to speed, alien bugs start to attack the factory requiring strong defenses.
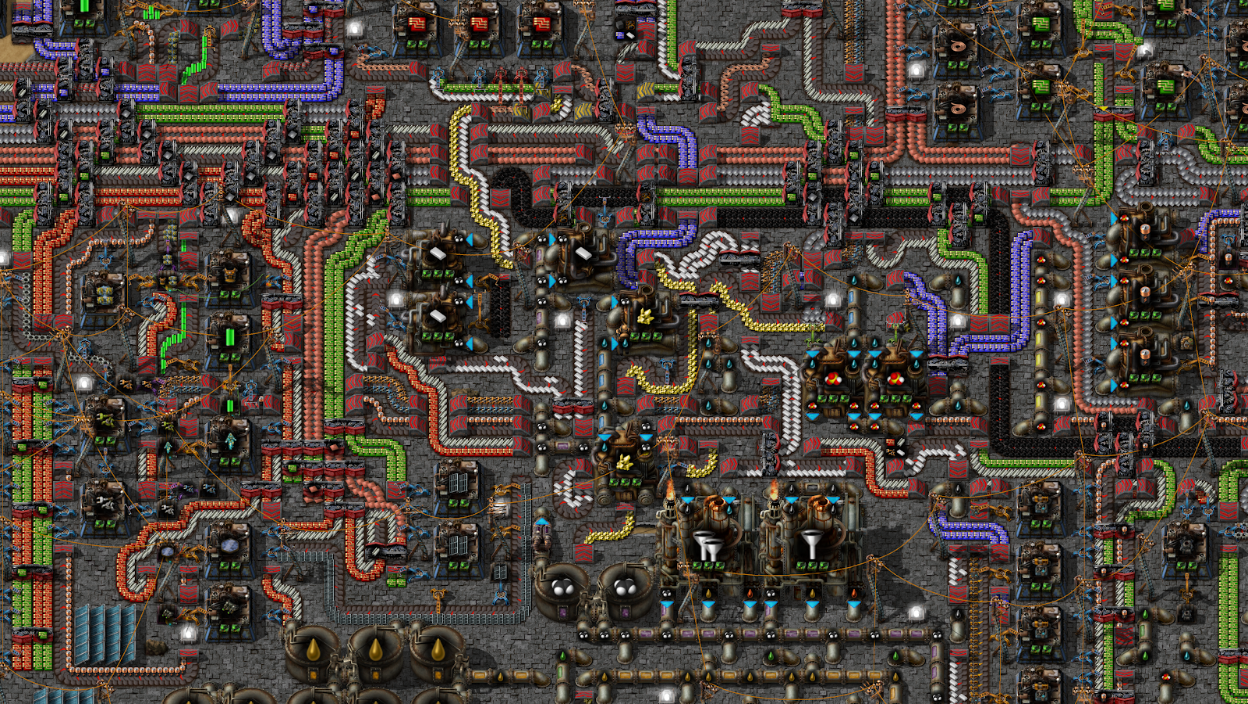
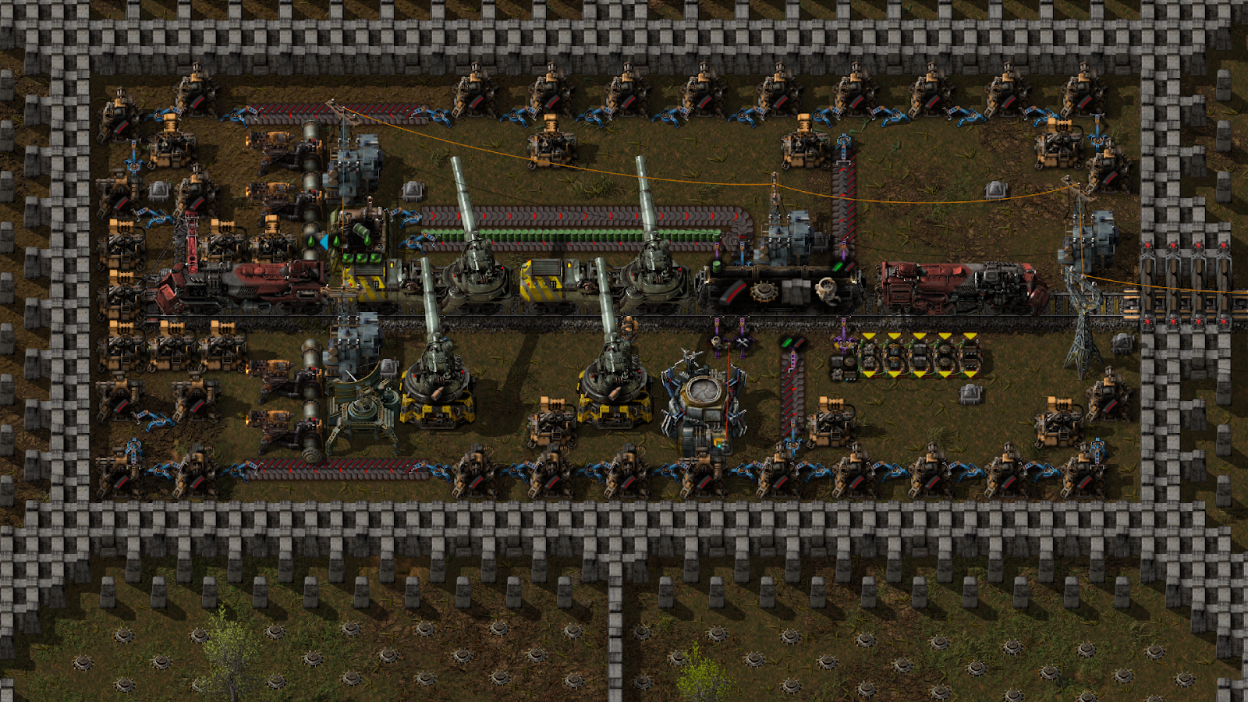

At FactorioMaps.com, I am building a place for the community of Factorio players to share their factories as interactive Leaflet maps. Due to the size and detail of the game, it can be difficult to share an entire factory through a few screenshots. A Leaflet map provides a Google Maps-like experience allowing viewers to pan and zoom throughout the map almost as if they are playing the game.
Hosting
Leaflet maps contain thousands of small images for X/Y/Z coordinates. Amazon S3 and Google Cloud Storage are Continue reading
Leave your VPN and cURL secure APIs with Cloudflare Access


We built Access to solve a problem here at Cloudflare: our VPN. Our team members hated the slowness and inconvenience of VPN but, that wasn’t the issue we needed to solve. The security risks posed by a VPN required a better solution.
VPNs punch holes in the network perimeter. Once inside, individuals can access everything. This can include critically sensitive content like private keys, cryptographic salts, and log files. Cloudflare is a security company; this situation was unacceptable. We need a better method that gives every application control over precisely who is allowed to reach it.
Access meets that need. We started by moving our browser-based applications behind Access. Team members could connect to applications faster, from anywhere, while we improved the security of the entire organization. However, we weren’t yet ready to turn off our VPN as some tasks are better done through a command line. We cannot #EndTheVPN without replacing all of its use cases. Reaching a server from the command line required us to fall back to our VPN.
Today, we’re releasing a beta command line tool to help your team, and ours. Before we started using this feature at Cloudflare, curling a server required me to Continue reading
Announcing Firewall Rules


Threat landscapes change every second. As attackers evolve, becoming more dynamic and devious, vulnerabilities materialize faster than engineers can patch their applications. Part of Cloudflare’s mission is to keep you and your applications safe. Today, Cloudflare is launching a new feature, giving customers what they have been requesting - fine-grained control over their incoming requests.
Cloudflare already offers a number of powerful firewall tools such as IP rules, CIDR rules, ASN rules, country rules, HTTP user-agent blocking, Zone Lockdown (for these URIs only allow traffic from those IPs), and our comprehensive managed rules within our WAF (Web Application Firewall). But sometimes, you need to combine the power of these to fully mitigate an attack, and to express a block rule that breaks the boundaries of the existing tools, to be able to “block traffic to this URI when the request comes from that IP and the user-agent matches one of these”.
Flexibility and Control

© Stefano Kocka : Source Wikipedia
Common themes arose when we spoke to customers about their needs and also reviewed feature requests that our customer support team had seen, and we categorised the top pieces of feedback and feature requests into three core needs:
- More flexibility Continue reading
Custom Load Balancing With Cloudflare Workers
The following is a guest post by Jayaprabhakar Kadarkarai, Developer of Codiva.io, an Online IDE used by computer science students across the world. He works full stack to deliver low latency and scalable web applications.
Have you launched your website? Getting a lot of traffic? And you are planning to add more servers? You’ll need load balancing to maintain the scalability and reliability of your website. Cloudflare offers powerful Load Balancing, but there are situations where off-the-shelf options can’t satisfy your specific needs. For those situations, you can write your own Cloudflare Worker.
In this post, we’ll learn about load balancers and how to set them up at a low cost with Cloudflare Service Workers.
This post assumes you have a basic understanding of JavaScript, as that’s the language used to write a Cloudflare Worker.
The Basic Pattern
The basic pattern starts with adding ‘fetch’ event listener to intercept the requests. You can configure which requests to intercept on the Cloudflare dashboard or using the Cloudflare API.
Then, modify the hostname of the URL and send the request to the new host.
addEventListener('fetch', event => {
var url = new URL(event.request.url);
// https://example.com/path/ Continue readingUlaanbaatar, Mongolia

Whenever you get into a conversation about exotic travel or ponder visiting the four corners of the globe, inevitably you end up discussing Ulaanbaatar in Mongolia. Travelers want to experience the rich culture and vivid blue skies of Mongolia; a feature which gives the country its nickname of “Land of the Eternal Blue Sky”.

Ulaanbaatar (or Ulan Bator; but shortened to UB by many) is the capital of Mongolia and located nearly a mile above sea level just outside the Gobi Desert - a desert that spans a good percentage of Central Asia’s Mongolia. (The rest of the Gobi Desert extends into China). The country is nestled squarely between Russia to the north and China to the south. It’s also home to some of the richest and ancient customs and festivals around. It’s those festivals that successfully draw in the tourists who want to experience something quite unique. Luckily, even with all the tourists, Mongolia has managed to keep its local customs; both in the cities and within its nomadic tribes.
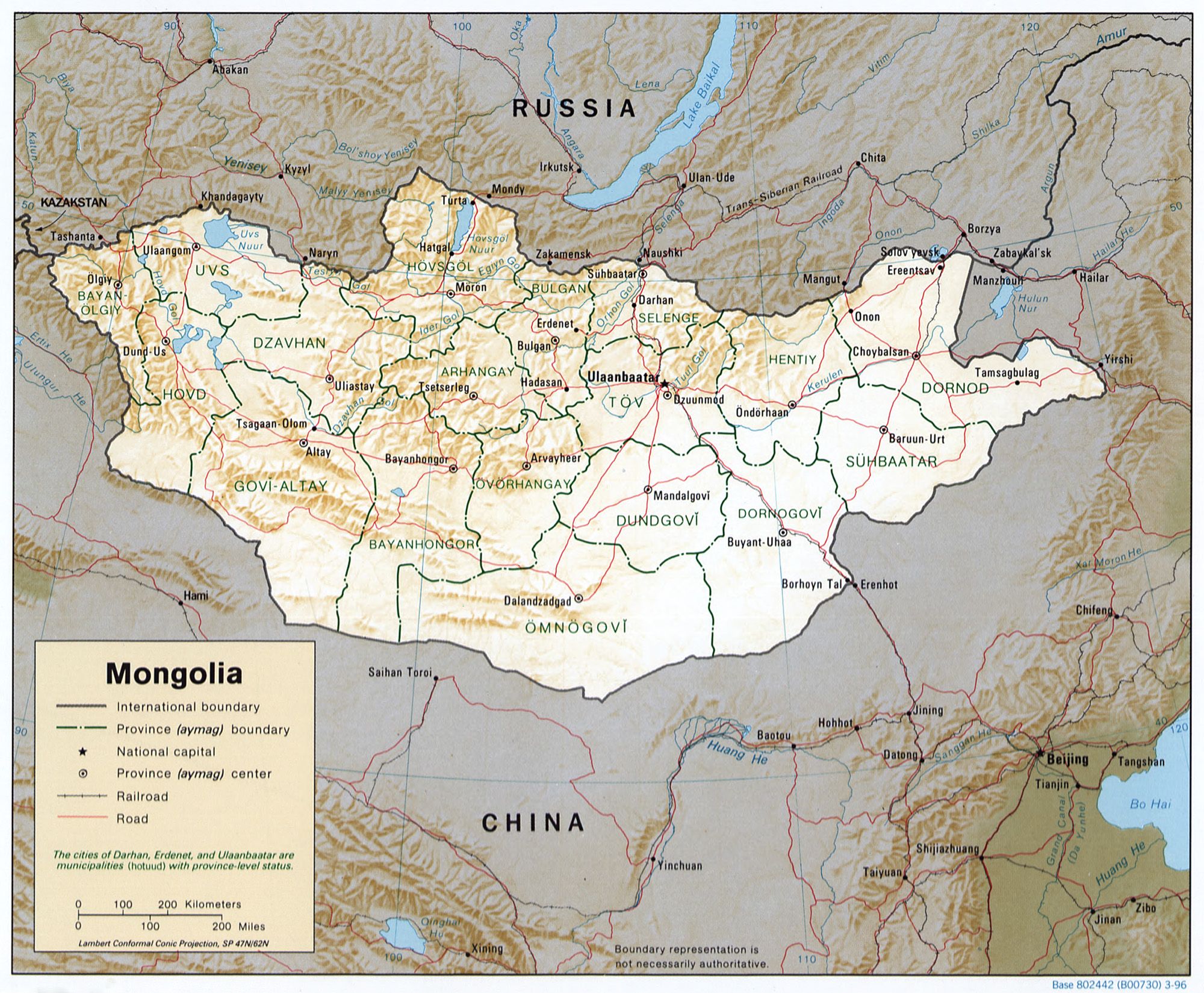
via Wikipedia
History also has drawn explorers and conquerors to and from the region; but more on that later.
Cloudflare is also drawn into Mongolia
Any avid reader of Continue reading
Cloudflare Access: Sharing our single-sign on plugin for Atlassian
Here at Cloudflare, we rely on a set of productivity tools built by Atlassian, including Jira and Confluence. We secure them with Cloudflare Access. In the past, when our team members wanted to reach those applications, they first logged in with our identity provider credentials to pass Access. They then broke out a second set of credentials, specific to Atlassian tools, to reach Jira. The flow is inconvenient on a desktop and downright painful on a mobile device.
While Access can determine who should be able to reach an application, the product alone cannot decide what the user should be able to do once they arrive at the destination. The application sets those specific permissions, typically by requiring another set of user credentials. The extra step slows down and frustrates end users. Access saves time by replacing a cumbersome VPN login. However, we wanted to also solve the SSO problem for our team.
We created a plugin, specific to Atlassian, that could take identity data from the token generated by Access and map it to a user account. Our team members log in with our identity provider to pass Access, and then Access could set their user permissions in Jira Continue reading
#BetterInternet: Join the Movement


When it comes to overall awareness of Cloudflare, it seems most folks fall into one of three camps: 1) those who don’t know much about Cloudflare at all, 2) those who are familiar with one or two of Cloudflare’s many solutions (i.e. DDoS protection, caching, DNS, etc.), and finally, 3) those who understand the full breadth and scope of Cloudflare’s global cloud network. This latter group of folks are especially excited about the broad scope of Cloudflare’s mission, which is: “to help build a better Internet.” Last week our co-founder Michelle Zatlyn explained in a blog post what this mission actually means:
“Our mission at Cloudflare is to help build a better Internet. That is a big, broad mission that means many things. It means that we push to make Internet properties faster. It means respecting individual’s privacy. It means making it harder for malicious actors to do bad things. It means helping to make the Internet more reliable. It means supporting new Internet standards and protocols, and making sure they are accessible to everyone. It means democratizing technology and making sure the widest possible group has access to it. It means increasing value for our community, Continue reading