HP network scripting
Dear HP Network Community, My name is Dobias van Ingen and I’m working within HP for almost 15 years. I’ve always been in networking and Unix / Linux infrastructures. Currently I’m leading an EMEA pre-sales overlay team with strong technical focus … Continue readingClassful IP Networks: An Introduction to IP Address Classes
When the concept of subnetting comes up, there is a need to first establish what networks were like before the Internet Standard Subnetting Procedure was introduced in RFC950. Prior to the use of subnet masks, networked devices made assumtions about the network and host portion of the address. This process by which these assumptions is made was defined in RFC791–
Addresses are fixed length of four octets (32 bits). An address
begins with a network number, followed by local address (called the
“rest” field). There are three formats or classes of internet
addresses: in class a, the high order bit is zero, the next 7 bits
are the network, and the last 24 bits are the local address; in
class b, the high order two bits are one-zero, the next 14 bits are
the network and the last 16 bits are the local address; in class c,
the high order three bits are one-one-zero, the next 21 bits are the
network and the last 8 bits are the local address.
If that leaves you a bit confused, you are in the right place. This article works through the concept of the IP Address Class. Readers should gain the understanding required to decipher things Continue reading
On Policy in the Data Center: The solution space
(This post was written by Tim Hinrichs and Scott Lowe with contributions from Martin Casado, Peter Balland, Pierre Ettori, and Dennis Moreau.)
In the first part of this series we described the policy problem: ensuring that the data center obeys the real-world rules and regulations that are pertinent to that data center. In this post, we look at the range of possible solutions by identifying some the key features that are important for any solution to the policy problem. Those key features correspond to the following four questions, which we use to structure our discussion.
- What are the policy sources a policy system must accommodate?
- How do those sources express the desired policy to the system?
- How does the policy system interact with data center services?
- What can the policy system do once it has the policy?
Let’s take a look at each of these questions one at a time.
Policy Sources: The origins of policy
Let’s start by digging deeper into an idea we touched on in the first post when describing the challenge of policy compliance: the sources of policy. While we sometimes talk about there being a single policy for a data center, the reality is Continue reading
SDN/NFV: More than Hot Air in the Windy City
SDN/NFV: More than Hot Air in the Windy City
by Steve Harriman, VP of Marketing - June 19, 2014
As reported in my last blog post - SDN: Déjà vu all over again? - Packet Design was a gold sponsor of Light Reading’s inaugural Big Telecom Event in Chicago this week. The organizers claim there were about 1,500 registered attendees with two thirds of them representing network operators. There were several really interesting presentations and panel discussions, and I’ve captured four key takeaways here.

Cengiz Alaettinoglu prepping to demo the Network Access Broker
SDN is getting the buzz, but NFV is where the early action is. This theme ran through the conference and there was much discussion on the relative merits of SDN vs. NFV and whether they should be implemented simultaneously or separately. While there are clear near-term benefits – including lower capex and faster time to revenue – for operators who virtualize network functions that today run on hardware appliances, most agreed that this is a first step only. To achieve maximum efficiency and flexibility as well as deliver the best customer experience (see below), an SDN-enabled network function virtualization infrastructure (NFVI) is needed in which pools Continue reading
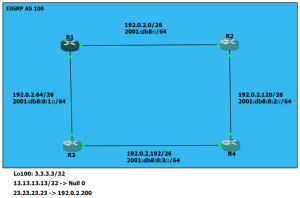
EIGRP Redistribution – Default Metrics of Connected and Static Routes
I wanted to do some analysis of the EIGRP topology table last night, so I fired up a small lab. I was especially interested in how external routes appear there and compare to internal entries. Like all good scientific endeavors, the whole thing got derailed when I made a realization.
Here’s the lab I set up. You can ignore the IPv6 info for this exercise.
It’s a simple little thing. All the networks you see are included in EIGRP 100 for simplicity. I limited the network statements to 192.0.2.0/24 to keep my options open. I went ahead and added Loopback100 on R3 with an address of 3.3.3.3/32 and added a redistribute connected with a route-map to get the route out in the wild. Here’s what I had.
R3#show run | section eigrp router eigrp 100 redistribute connected route-map RM-REDIST-CONN network 192.0.2.0 no auto-summary ! route-map RM-REDIST-CONN permit 100 match interface Loopback100
Alright. All looks good there, so I checked the topology table on R1 and saw it in there as an external and everything.
R1#sh ip eigrp topology 3.3.3.3/32 IP-EIGRP (AS 100): Topology entry for 3.3.3.3/32 State Continue reading
Another way to protect your SSH keys
Let's say you don't have a TPM chip, or you hate them, or for some other reason don't want to use it to protect your SSH keys. There's still hope! Here's a way to make it possible to use a key without having access to it. Meaning if you get hacked the key can't be stolen.
No TPM, but key can't be stolen anyway? Surely this is an elaborate ruse? Well yes, it is. My idea is that you essentially bounce off of a Raspberry Pi.
But doing that straightforward is too easy. I've instead made an SSH proxy, and will show you how to automatically bounce off of it. You could do the same by setting up a second SSH server (or the same one), and hack around with PAM and a restricted shell. But this solution can be run as any user, with just the binary and the set of keyfiles. Very simple.
The goal here is to log in to shell.foo.com from your workstation via
a Raspberry Pi. The workstation SSH client presents its SSH client key to the SSH Proxy
on the Raspberry Pi, and if allowed will connect on and present the SSH Continue reading
Docker essentials – Images and Containers
I’ll admit, I jumped into docker pretty quickly and found that I was getting a little ahead of myself. After much googling and discussion, I’ve come to realize a couple things about docker that I think are well worth sharing. I’m hoping to share them through a series of ‘Docker Essentials’ type posts.
NOTE: My first post was going to be about how to interact with docker on the CLI. However, there are lots of other resources out there for that. Namely, the really awesome docker documentation. In addition, the CLI provides help/syntax on commands as well. I’ll list a couple of resources that I used and try to explain along the way, but if you don’t recognize a command I’m using look it up!
The docker user guide – http://docs.docker.com/userguide/
The docker CLI reference – https://docs.docker.com/reference/commandline/cli/
The docker guide book – https://github.com/kencochrane/docker-guidebook
Working with images and Containers
On first glance, I made some assumptions about this images and containers that proved to be wrong. So let’s start with some basics.
Images are read-only. That is, they can never be altered. Containers are built using Continue reading
Port mirroring with Linux bridges
Port mirroring with the most popular Linux bridge implementations.Thought: Why Are There No Good Open Source BGP Implementations ?
It is common wisdom that BGP is awesome because, you know, … something. It runs the Internet therefore it must good. It can be extended and that makes it good. Lots of vendors use it ….. Hang on. When you think about it there are no good, solid BGP implementation in open source. Quagga is […]
The post Thought: Why Are There No Good Open Source BGP Implementations ? appeared first on EtherealMind.
HTIRW: DNS Reverse Lookups and Whois
In our last episode, we discussed how DNS is paid for in the real world — who builds, maintains, and manages all those servers that allow us to put in a domain name, and end up with a web page? This post will look at two other tools or protocols in the DNS system that […]
Author information
Change of focus
I have decided to change my focus quite a bit.
I was planning on tackling the IOS-XR exam this year and was preparing for it by going through the blueprint. However another track kept pulling me towards it, and ofcourse thats the CCDE track.
I have spent the last 6 years learning how to do something, but so far i havent spent alot of time thinking about why that is.
I am not doing the CCDE track in order to pass the exam. I might not even go as far as giving the practical exam a go. I am however going to pursue the written exam for now, as it will give me a target for which to learn new stuff.
To that end, a few of us have created a study group, which im very thrilled about. It will provide an outlet for any ideas and thoughts as well as input. All in all great stuff.
So thats a quick update ![]()
Visibility, Trustship,Sub optimality or whatever you want to call it.
To be honest I really tried hard to find a name for this article. Maybe it is not convenient and if you have better idea please let me know in the comment. I want to mention sub optimality and stretch in the networks while using routing protocols but the idea actually came to me from […]
Author information
The post Visibility, Trustship,Sub optimality or whatever you want to call it. appeared first on Packet Pushers Podcast and was written by Orhan Ergun.
Where to Start with SDN
For the 3rd installment on my three part SDN series, building on A Business Case for SDN, and the SDN Ecosystem, the most practical way to start exploring an SDN deployment is with a proof of concept (POC). But even if you have the approval to go ahead with an SDN POC, it can be difficult to know where to start. Let’s cut through the uncertainty and lay out what it takes to do a successful SDN POC.
Identify a pain point
Start by identifying a key pain point in networking that you’d like to address with SDN. For example, you might want to improve campus security, or improve the performance of collaborative tools, or streamline your data center. Specific tasks in these areas include adding a network tap, increasing the speed of a LAN link, or reassigning VLANs.
We’ll assume you have surveyed business unit leaders, ranked overall IT strategies and come back with one SDN application to start your evolution. Similar to a cloud or BYOD initiative, giving visibility for SDN can help you bring the company together, and can also build support for improving how IT can drive the business. If you understand the Continue reading
ANET Cloud Infrastructure – Arista Definition of ACI
You may have noticed Arista being uncharacteristically quiet throughout an imposed “quiet period” leading up to our IPO (ANET). While the industry continued to speak out on behalf of, or against, Arista, the company remained true to its focus on solving customer problems through disruptive cloud networking architectures and technology. Enabling innovative applications to take advantage of modern networking through Arista EOS remains a key priority for the company.
The migration from legacy “policy per application” to universal cloud networks is crystal clear and underway. The classical 1990s web, file and database tier in client-server architectures, with north-south traffic, is migrating to universal workflow telemetry and workload automation for east-west, server-to-server traffic of the 21st Century. This is particularly true as networks move to mandates of terabit scale for data, control, and management. Arista invented the concept of “Leaf-Spine” and late last year introduced the “SplineTM” as architectures to support these next generation network requirements. Five years later others are still trying to mimic the approach but lack the fundamental software or scale to achieve it.
Through the years we’ve witnessed many failed attempts to lock-in customers with proprietary fabrics (FabricPath, QFabric, etc.) and once again we are witnessing Continue reading
Switch Prices Will Get Cheaper. Design Models Will Change.
For the last 20 years, L2 tree-based network topologies meant that the only practical design methodology was to buy large, vertically scaled switch chassis for the core of the data centre. This limitation was largely due to the tree-structure forced on LAN networking by Spanning Tree Protocol. For every new device at point Access/1 we […]
The post Switch Prices Will Get Cheaper. Design Models Will Change. appeared first on EtherealMind.
Show 192 – Logging Design & Best Practices
Jay Swan, Lennart Koopman, and Wes Kennedy join the Packet Pushers co-hosts Ethan Banks and Greg Ferro in this discussion of effectively managing event logging. Why discuss logging on a show about networking? Because networking has a huge volume of logs coming from routers, switches, and firewalls that need to be managed. And frankly, it’s […]
Author information
The post Show 192 – Logging Design & Best Practices appeared first on Packet Pushers Podcast and was written by Ethan Banks.
Not So Random Thoughts on Privacy and Positioning
Earlier this month at the Apple’s Worldwide Developer’s Conference (WWDC) it was uncovered by Frederic Jacobs that with the upcoming Apple iOS8 operating system, Apple devices will be able to, as a privacy mechanism, hide or mask their MAC address...The Disconnect. Good Enough Is Good Enough.
A Meeting room. Discussing the possible options for product and vendor strategy. Company urgently needs to avoid capital expenditure and reduce maintenance costs. The engineer across the table is wearing a vendor t-shirt, a few years old and looks a bit tatty. The table and chairs are tired and a bit worn. I took a […]
Author information
The post The Disconnect. Good Enough Is Good Enough. appeared first on Packet Pushers Podcast and was written by Greg Ferro.
6125XLG console/aux port access for IRF renumber
For HP Blade enclosures, the 6125XLG can be used as a non-blocking 10G blade server access switch with 4x40G uplink ports. Since it is based on Comware 7 (very similar to the 5900AF model, but in a blade switch form … Continue readingGetting Started with Docker
It can’t be helped. There’s just too much cool stuff out there and not enough time to spend dedicating myself to one piece of technology. That being said, I fully intend on continuing the Chef posts, but Im going to be mixing in some docker posts as well. Im hoping that there’s some cross-connect as well where we can talk about using docker in conjunction with Chef as well.
Docker is something that I haven’t seen before. From what I have seen so far, it appears to be an incredibly easy way to containerize applications and software on a linux system. The docker website summarizes docker as..
“An open platform for distributed applications for developers and sysadmins.”
That summarizes things nicely, but again, why is a network guy interested in this? First off, I’m a little tired of VMware. Don’t confuse me being tired with a general dislike of the product. I’ve been using VMware for years and for the most part, it works well and provides the functions I need. On the flip side, Im not convinced there’s anything particularly special about VMware.
I’ve been using ProxMox at home for some time and it does everything that I Continue reading