Do You Need a Service Mesh? Understanding the Role of CNI vs. Service Mesh
The world of Kubernetes networking can sometimes be confusing. What’s a CNI? A service mesh? Do I need one? Both? And how do they interact in my cluster? The questions can go on and on.
Even for seasoned platform engineers, making sense of where these two components overlap and where the boundaries of responsibility end can be challenging. Seemingly bewildering obstacles can stand in the way of getting the most out of their complementary features.
One way to cut through the confusion is to start by defining what each of them is, then look at their respective capabilities, and finally clarify where they intersect and how they can work together.
This post will clarify:
- What a CNI is responsible for
- What a service mesh adds on top
- When you need one, the other, or both
What a CNI Actually Does
Container Network Interface (CNI) is a standard way to connect and manage networking for containers in Kubernetes. It is a set of standards defined by Kubernetes for configuring container network interfaces and maintaining connectivity between pods in a dynamic environment where network peers are constantly being created and destroyed.
Those standards are implemented by CNI plugins. A CNI plugin is Continue reading
How Istio Ambient Mode Delivers Real World Solutions
For years, platform teams have known what a service mesh can provide: strong workload identity, authorization, mutual TLS authentication and encryption, fine-grained traffic control, and deep observability across distributed systems. In theory, Istio checked all the boxes. In practice though, many teams hit a wall.
Across industries like financial services, media, retail, and SaaS, organizations told a similar story. They wanted mTLS between services to meet regulatory or security requirements. They needed safer deployment capabilities like canary rollouts and traffic splitting. They wanted visibility that went beyond IP addresses.
However, traditional sidecar based meshes came with real costs:
- High operational complexity
- Thousands of sidecars to manage
- Fragile upgrade paths
- Hard to debug failure modes
In several cases, teams started down the Istio service mesh path, only to pause or roll back entirely because the ongoing operational complexity was too high. The value of a service mesh was clear, but the service mesh architecture based on sidecars was not sustainable for many production environments.
The Reality Platform Teams Have Been Living With
In many cases, organizations evaluated service meshes with clear goals in mind. They wanted mTLS between services, better control over traffic during deployments, and observability that could keep up. Continue reading
Ingress NGINX Controller Is Dead — Should You Move to Gateway API?
Now What? Understanding the Impact of the Ingress NGINX Deprecation

Ingress NGINX Controller, the trusty staple of countless platform engineering toolkits, is about to be put out to pasture. This news was announced by the Kubernetes community recently, and very quickly circulated throughout the cloud-native space. It’s big news for any platform team that currently uses the NGINX Controller because, as of March 26, 2026, there will be no more bug fixes, no more critical vulnerability patches and no more enhancements when Kubernetes continues to release new versions.
If you’re feeling ambushed, you’re not alone. For many teams, this isn’t just an inconvenient roadmap update, its unexpected news that now puts long-term traffic management decisions front and center. You know you need to migrate yesterday but the best path forward can be a confusing labyrinth of platforms and unfamiliar tools. Questions you might ask yourself:
 Do you find a quick drop-in Ingress replacement?
Do you find a quick drop-in Ingress replacement?
 Does moving to Gateway API make sense and can you commit enough resources to do a full migration?
Does moving to Gateway API make sense and can you commit enough resources to do a full migration?
 If you decide on Gateway API then what is the best option for a smooth transition?
If you decide on Gateway API then what is the best option for a smooth transition?
With Ingress NGINX on the way out, platform teams are standing at a Continue reading
An In-Depth Look at Istio Ambient Mode with Calico
The Next Step Toward a Unified Kubernetes Platform: Istio Ambient Mode
Organizations are struggling with rising operational complexity, fragmented tools, and inconsistent security enforcement as Kubernetes becomes the foundation for modern application platforms. As a result of this complexity and fragmentation, platform teams are increasingly burdened by the need to stitch together separate solutions for networking, network security, and observability. This fragmentation also creates higher operating costs, security gaps, inefficient troubleshooting, and an elevated risk of outages in mission-critical environments. The challenge is even greater for companies running multiple Kubernetes distributions, as relying on each platform’s unique and often incompatible networking stack can lead to significant vendor lock-in and operational overhead.
The Tigera Unified Strategy: Addressing Fragmentation
Tigera’s unified platform strategy is designed to address these challenges by providing a single solution that brings together all the essential Kubernetes networking and security capabilities enterprises need, that includes Istio Ambient Mode, delivered consistently across every Kubernetes distribution.

Istio Ambient Mode brings sidecarless service-mesh functionality that includes authentication, authorization, encryption, L4/L7 traffic controls, and deep application-level (L7) observability directly into the unified Calico platform. By including Istio Ambient Mode with Calico and making it easy to install and manage with the Tigera Continue reading
AI Meets Kubernetes Security: Tigera CEO Reveals What Comes Next for Platform Teams
Kubernetes adoption is growing rapidly, but so are complexity and security risks.

Platform teams are tasked with keeping clusters secure and observable while navigating a skills gap. At KubeCon + CloudNativeCon North America, The New Stack spoke with Ratan Tipirneni, President and CEO of Tigera, about the future of Kubernetes security, AI-driven operations, and emerging trends in enterprise networking. The highlights from that discussion are summarized below.
Portions of this article are adapted from a recorded interview between The New Stack’s Heather Joslin and Tigera CEO Ratan Tipirneni. You can watch the full conversation on The New Stack’s YouTube channel. Watch the full interview here
How Can Teams Better Manage the Kubernetes Blast Radius and Skills Gap?
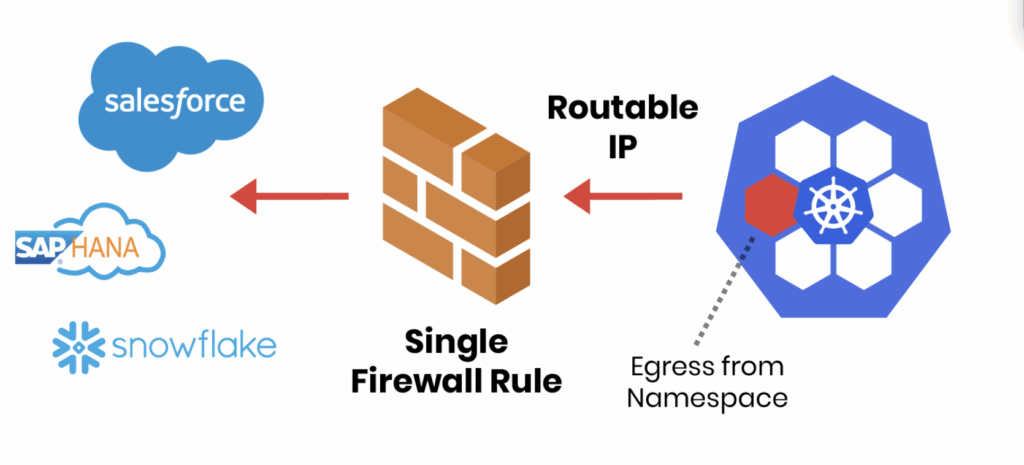
Tipirneni emphasizes the importance of controlling risk in Kubernetes clusters. “You want to be able to microsegment your workloads so that if you do come under an attack, you can actually limit the blast radius,” he says.
Egress traffic is another area of concern. According to Tipirneni, identifying what leaves the cluster is critical for security and compliance. Platform engineers are often navigating complex configurations without decades of Continue reading
KubeCon NA 2025: Three Core Kubernetes Trends and a Calico Feature You Should Use Now
The Tigera team recently returned from KubeCon + CloudNativeCon North America and CalicoCon 2025 in Atlanta, Georgia. It was great, as always, to attend these events, feel the energy of our community, and hold in-depth discussions at the booth and in our dedicated sessions that revealed specific, critical shifts shaping the future of cloud-native platforms.
We pulled together observations from our Tigera engineers and product experts in attendance to identify three key trends that are directly influencing how organizations manage Kubernetes today.
 Trend 1: Kubernetes is Central to AI Workload Orchestration
Trend 1: Kubernetes is Central to AI Workload Orchestration
A frequent and significant topic of conversation was the role of Kubernetes in supporting Artificial Intelligence and Machine Learning (AI/ML) infrastructure.
The consensus is clear: Kubernetes is becoming the standard orchestration layer for these specialized workloads. This requires careful consideration of networking and security policies tailored to high-demand environments. Observations from the Tigera team indicated a consistent focus on positioning Kubernetes as the essential orchestration layer for AI workloads. This trend underscores the need for robust, high-performance CNI solutions designed for the future of specialized computing.
 Trend 2: Growth in Edge Deployments Increases Complexity
Trend 2: Growth in Edge Deployments Increases Complexity
Conversations pointed to a growing and tangible expansion of Kubernetes beyond central data centers and Continue reading
How to Turbocharge Your Kubernetes Networking With eBPF
When your Kubernetes cluster handles thousands of workloads, every millisecond counts. And that pressure is no longer the exception; it is the norm. According to a recent CNCF survey, 93% of organizations are using, piloting, or evaluating Kubernetes, revealing just how pervasive it has become.
Kubernetes has grown from a promising orchestration tool into the backbone of modern infrastructure. As adoption climbs, so does pressure to keep performance high, networking efficient, and security airtight.
However, widespread adoption brings a difficult reality. As organizations scale thousands of interconnected workloads, traditional networking and security layers begin to strain. Keeping clusters fast, observable, and protected becomes increasingly challenging.
Innovation at the lowest level of the operating system—the kernel—can provide faster networking, deeper system visibility, and stronger security. But developing programs at this level is complex and risky. Teams running large Kubernetes environments need a way to extend the Linux kernel safely and efficiently, without compromising system stability.
Why eBPF Matters for Kubernetes Networking
Enter eBPF (extended Berkeley Packet Filter), a powerful technology that allows small, verified programs to run safely inside the kernel. It gives Kubernetes platforms a way to move critical logic closer to where packets actually flow, providing sharper visibility Continue reading
5 Reasons to Switch to the Calico Ingress Gateway (and How to Migrate Smoothly)
The End of Ingress NGINX Controller is Coming: What Comes Next?
The Ingress NGINX Controller is approaching retirement, which has pushed many teams to evaluate their long-term ingress strategy. The familiar Ingress resource has served well, but it comes with clear limits: annotations that differ by vendor, limited extensibility, and few options for separating operator and developer responsibilities.
The Gateway API addresses these challenges with a more expressive, standardized, and portable model for service networking. For organizations migrating off Ingress NGINX, the Calico Ingress Gateway, a production-hardened, 100% upstream distribution of Envoy Gateway, provides the most seamless and secure path forward.
If you’re evaluating your options, here are the five biggest reasons teams are switching now followed by a step-by-step migration guide to help you make the move with confidence.
Reason 1: The Future Is Gateway API and Ingress Is Being Left Behind
Ingress NGINX is entering retirement. Maintaining it will become increasingly difficult as ecosystem support slows. The Gateway API is the replacement for Ingress and provides:
- A portable and standardized configuration model
- Consistent behaviour across vendors
- Cleaner separation of roles
- More expressive routing
- Support for multiple protocols
Calico implements the Gateway API directly and gives you an Continue reading
Introducing Calico AI and Istio Ambient Mode
The Complexity of Modern Kubernetes Networking
Kubernetes has transformed how teams build and scale applications, but it has also introduced new layers of complexity. Platform and DevOps teams must now integrate and manage multiple technologies: CNI, ingress and egress gateways, service mesh, and more across increasingly large and dynamic environments. As more applications are deployed into Kubernetes clusters, the operational burden on these teams continues to grow, especially when maintaining performance, reliability, security, and observability across diverse workloads.
To address this complexity and tool sprawl, Tigera is incorporating Istio’s Ambient Service Mesh directly into the Calico Unified Network Security Platform. Service mesh has become the preferred solution for application-level networking, particularly in environments with a large number of services or highly regulated workloads. Among available service meshes, Istio stands out as the most popular and widely adopted, supported by a thriving open-source community. By leveraging the lightweight, sidecarless design of Istio Ambient Mode, Calico delivers all the benefits of service mesh, secure service-to-service communication, mTLS authentication, fine-grained authorization, traffic management, and observability, without the burden of sidecars.
Complementing this addition is Calico AI. Calico AI brings intelligence and automation to Kubernetes networking. It addresses the massive operational burden on teams Continue reading
What’s New in Calico – Fall 2025 Release
Simplify, Secure, and Scale Your Infrastructure
As organizations scale Kubernetes and hybrid infrastructures, many are realizing that more tools don’t mean better security. A recent Microsoft report found that organizations with 16+ point solutions see 2.8x more data security incidents than those with fewer tools. Yet platform teams are still expected to deliver resilience and performance across containers, VMs, and bare metal, often while juggling fragmented tools that introduce risk, downtime, and complexity.
The Fall 2025 release of Calico Enterprise and Calico Cloud cuts through that complexity. Its new features are designed to make your infrastructure more resilient, performant, and observable—right out of the box. From disaster recovery automation to modern data plane support and application traffic handling, these updates empower platform engineers to simplify operations while meeting strict reliability requirements.
The new features in this release can be grouped into two main categories:
1. Resilient, High-Performance Networking and Improved Quality of Service:
-
- High availability (HA) management planes for VM and bare metal hosts – Increases resiliency and helps reduce downtime.
- The official release (GA) of the nftables dataplane -Delivers faster and more scalable rule-processing than iptables.
- Maglev-Based Session Affinity – Maintain stable network traffic flow during failures Continue reading
Zero-Trust with Zero-Friction eBPF in Calico v3.31
Calico eBPF by default*
*some conditions may apply
 Calico has used eBPF as one of its dataplanes since version 3.13, released more than five years ago. At the time, this was an exciting step forward, introducing a new, innovative data plane that quickly gained traction within the Calico community. Since then, there have been many changes and continued evolution, all thanks to the many adopters of the then-new data plane.
Calico has used eBPF as one of its dataplanes since version 3.13, released more than five years ago. At the time, this was an exciting step forward, introducing a new, innovative data plane that quickly gained traction within the Calico community. Since then, there have been many changes and continued evolution, all thanks to the many adopters of the then-new data plane.
However, there has been one persistent challenge in the installation process since day one: bootstrapping the eBPF data plane required a manual setup step. This extra friction point often frustrated operators and slowed adoption.
With the launch of Calico v3.31, that hurdle to using the eBPF data plane has finally been removed. For many environments (see Limitations section below), you can now install Calico with eBPF enabled right out of the box with no manual setup required.
Simply use the provided installation manifest (custom-resources-bpf.yaml), which comes preconfigured with the data plane option set to eBPF.
To get started, follow the instructions in Install Calico networking and network policy for on-premises deployments to enjoy a much smoother installation experience.
See Calico eBPF in action with Continue reading
Calico Whisker in Action: Reading and Understanding Policy Traces
Kubernetes adoption is growing, and managing secure and efficient network communication is becoming increasingly complex. With this growth, organizations need to enforce network policies with greater precision and care. However, implementing these policies without disrupting operations can be challenging.
That’s where Calico Whisker comes in. It helps teams implement network policies that follow the principle of least privilege, ensuring workloads communicate only as intended. Since most organizations introduce network policies after applications are already running, safe and incremental rollout is essential.
To support this, Calico Whisker offers staged network policies, which allow teams to preview a policy’s effect in a live environment before enforcing it. Alongside this, policy traces in Calico Whisker provide deep visibility into how both enforced and pending policies impact traffic. This makes it easier to understand policy behaviour, validate intent, and troubleshoot issues in real time. In this post, we’ll walk through real-world policy trace outputs and show how they help teams confidently deploy and refine network policies in production Kubernetes clusters.
Kubernetes Network Policy Behaviour
It’s important to reiterate the network policy behaviour in Kubernetes, as understanding this foundation is key to effectively interpreting policy traces and ensuring the right traffic flow decisions are Continue reading
5 Essential Steps to Strengthen Kubernetes Egress Security
Securing what comes into your Kubernetes cluster often gets top billing. But what leaves your cluster, outbound or egress traffic, can be just as risky. A single compromised pod can exfiltrate data, connect to malicious servers, or propagate threats across your network. Without proper egress controls, workloads can reach untrusted destinations, creating serious security and compliance risks. This guide breaks down five practical steps to strengthen Kubernetes egress security, helping teams protect data, enforce policies, and maintain visibility across clusters.
Why Egress Controls Matter
|
Your Kubernetes Egress Security Checklist
To help teams tackle this challenge, we’ve put together a Kubernetes Egress Security Checklist, based on best practices from real-world Continue reading
What’s New in Calico v3.31: eBPF, NFTables, and More
We’re excited to announce the release of Calico v3.31,  which brings a wave of new features and improvements.
which brings a wave of new features and improvements.
For a quick look, here are the key updates and improvements in this release:
- Calico NFTables Dataplane is now Generally Available
- Calico eBPF Dataplane Enhancements
- Simplified installation: new template defaults to
eBPF, automatically disableskube-proxyviakubeProxyManagementfield, and addsbpfNetworkBootstrapfor auto API endpoint detection. - Configurable cgroupv2 path: support for immutable OSes (e.g., Talos).
- >>Learn More: See how Calico v3.31 makes eBPF installation frictionless and simplifies setup in our Zero-Trust with Zero-Friction eBPF in Calico v3.31 blog
- Simplified installation: new template defaults to
- Calico Whisker (Observability Stack)
- Improved UI and performance in Calico v3.31.
- New policy trace categories: Enforced vs Pending.
- Lower memory use, IPv6 fixes, and more efficient flow streaming.
- Networking & QoS
- New bandwidth and packet rate QoS controls across all dataplanes.
- DiffServ (
DSCP) support: prioritize traffic by marking packets (e.g.,EFfor VoIP). - Introduces new
QoSPolicyAPI for declarative traffic control.
- Encapsulation & Routing
- Tech Preview: Felix now handles encapsulation routes (
IP-in-IP,no-encap) directly — no BIRD required!
- Tech Preview: Felix now handles encapsulation routes (
- NAT Control
- New
natOutgoingExclusionsconfig for granular NAT management. - Choose between
Continue reading
- New
When to Use BGP, VXLAN, or IP-in-IP: A Practical Guide for Kubernetes Networking
When deploying a Kubernetes cluster, a critical architectural decision is how pods on different nodes communicate. The choice of networking mode directly impacts performance, scalability, and operational overhead. Selecting the wrong mode for your environment can lead to persistent performance issues, troubleshooting complexity, and scalability bottlenecks.
The core problem is that pod IPs are virtual. The underlying physical or cloud network has no native awareness of how to route traffic to a pod’s IP address, like 10.244.1.5 It only knows how to route traffic between the nodes themselves. This gap is precisely what the Container Network Interface (CNI) must bridge.
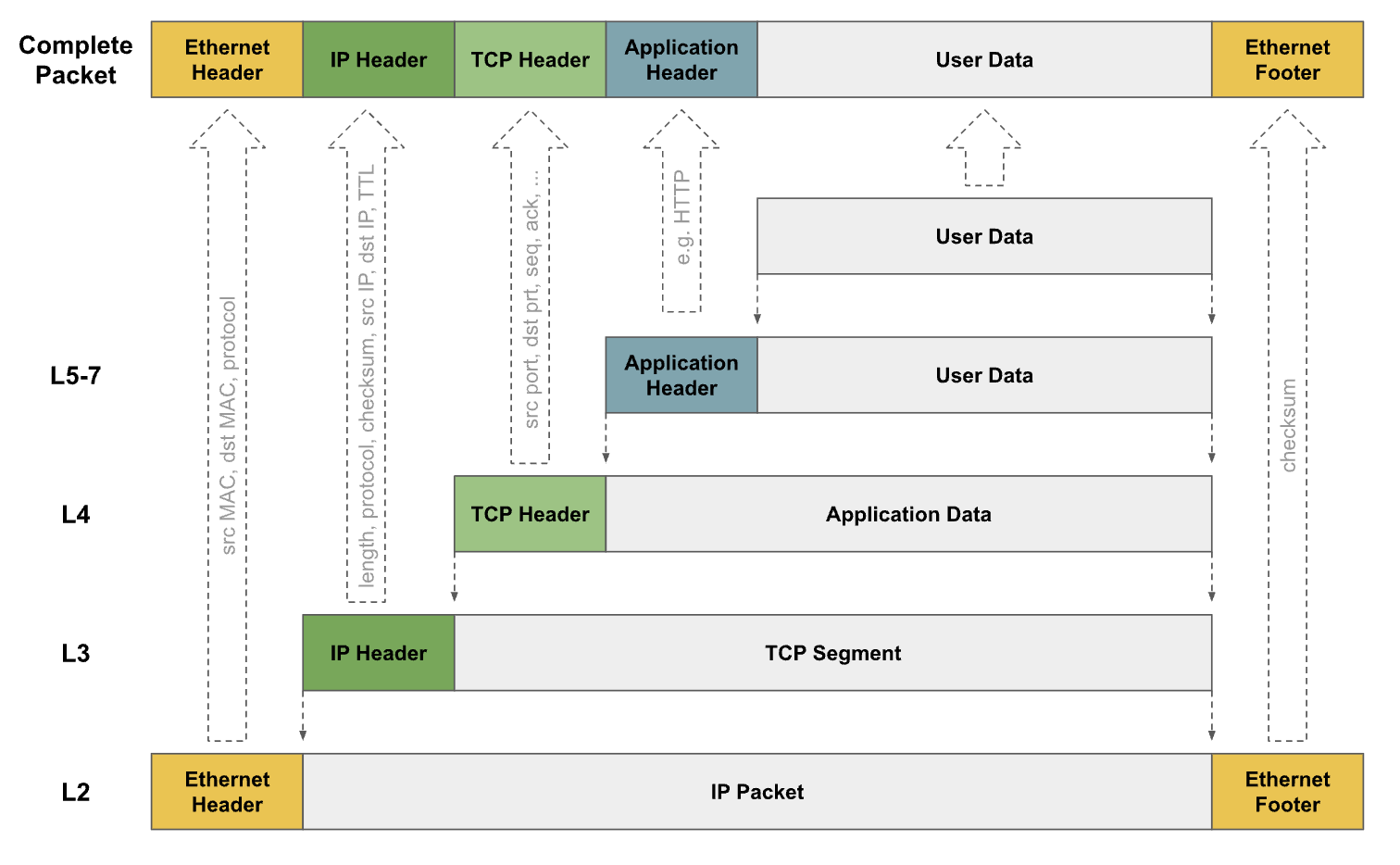
The CNI employs two primary methods to solve this problem:
- Overlay Networking (Encapsulation): This method wraps a pod’s packet inside another packet that the underlying network understands. The outer packet is addressed between nodes, effectively creating a tunnel. VXLAN and IP-in-IP are common encapsulation protocols.
- Underlay Networking (Routing): This method teaches the network fabric itself how to route traffic directly to pods. It uses a routing protocol like BGP to advertise pod IP routes to the physical Continue reading
How NRP Scales Global Scientific Research with Calico

The National Research Platform (NRP) operates a globally distributed, high-performance computing and networking environment, with an average of 15,000 pods across 450 nodes supporting more than 3,000 scientific project namespaces. With its head node in San Diego, NRP connects research institutions and data centers worldwide via links ranging from 10 to 400 Gbps, serving more than 5,000 users in 70+ locations.
- Non-profit company
- Uses Calico Open Source
NRP is a partnership of more than 50 institutions, led by researchers at UC San Diego, University of Nebraska-Lincoln, and Massachusetts Green High Performance Computing Center and includes contributions by the National Science Foundation, the Department of Energy, the Department of Defense, and many research universities and R&E networking organizations in the US and around the world.

Challenges
Complex Network Visibility and Debugging
NRP needed a way to diagnose connectivity problems across globally distributed storage nodes. Frequent changes to edge network configurations, ACLs, firewalls, and static routes caused blocked ports, forcing manual troubleshooting with tools such as nmap and iperf. This process slowed down root-cause analysis and problem resolution.
Balancing Performance with Granular Security at Scale
Scientific workflows demanded maximum throughput over 100/400 Gbps links and jumbo frames. Traditional host firewalls introduced unacceptable Continue reading
How to Deploy Whisker and Goldmane in Manifest Only Calico Setups
Your Step-by-Step to Observability Without the Operator
If you’re running Calico using manifests, you may have found that enabling the observability features introduced in version 3.30, including Whisker and Goldmane, requires a more hands-on approach. Earlier documentation focused on the Tigera operator, which automates key tasks such as certificate management and secure service configuration. In a manifest-based setup, these responsibilities shift to the user. While the process involves more manual steps, it provides greater transparency and control over each component. With the right guidance, setting up these observability tools is entirely achievable and offers valuable insight into the internal behavior of your Calico deployment.
We’ve heard from many of you in the Calico Slack community: you’re eager to try out Whisker and Goldmane but aren’t sure how to set them up without Helm or the operator. For anyone who’s up for a challenge, this blog post provides a step-by-step guide on how to get everything wired up the hard way.
However, even if you already use the operator, keep reading! We’re going to pull back the curtain on the magic it performs behind the scenes. Understanding these mechanics will help you troubleshoot, customize, and better appreciate a managed Continue reading
SUSE and Tigera: Empowering Secure, Scalable Kubernetes with Calico Enterprise
Modern Workloads Demand Modern Kubernetes Infrastructure
As organizations expand Kubernetes adoption—modernizing legacy applications on VMs and bare metal, running next-generation AI workloads, and deploying intelligence at the edge—the demand for infrastructure that is scalable, flexible, resilient, secure, and performant has never been greater. At the same time, compliance, consistent visibility, and efficient management without overburdening teams remain critical.
The combination of Calico Enterprise from Tigera and SUSE Rancher Prime delivers a resilient and scalable platform that combines high-performance networking, robust network security, and operational simplicity in one stack.
Comprehensive Security Without Compromise
Calico Enterprise provides a unified platform for Kubernetes networking, security, and observability:
- eBPF-powered networking for high performance without sidecar overhead
- One platform for all Kubernetes traffic: ingress, egress, in-cluster, and multi-cluster
- Security for every workload type: containers, VMs, and bare metal
- Seamless scaling with built-in multi-cluster networking and security
- Zero-trust security with identity-aware policies and workload-based microsegmentation
- Integrated observability for policy enforcement and troubleshooting
- Compliance features that simplify audits (PCI-DSS, HIPAA, SOC 2, FedRAMP)
Deployed with Rancher Prime, these capabilities extend directly into every cluster, enabling security-conscious industries such as finance, healthcare, and government to confidently run Kubernetes for any use case—from application modernization to AI and edge Continue reading
How to Connect Nested KubeVirt Clusters with Calico and BGP Peering
Running Kubernetes inside Kubernetes isn’t just a fun experiment anymore – it’s becoming a key pattern for delivering multi-environment platforms at scale. With KubeVirt, a virtualization add-on for Kubernetes that uses QEMU (an open-source machine emulator and virtualizer), you can run full-featured Kubernetes clusters as virtual machines (VMs) inside a parent Kubernetes cluster. This nested architecture makes it possible to unify containerized and virtualized workloads, and opens the door to new platform engineering use cases.
But here’s the challenge: how can you ensure that these nested clusters, and the workloads within, can reach, and be reached by, your physical network and are treated the same way as any other cluster?
That’s where Calico’s Advanced BGP (Border Gateway Protocol) peering with workloads comes into play. By enabling BGP route exchange between the parent cluster and nested KubeVirt VMs, Calico extends dynamic routing directly to virtualized workloads. This allows nested clusters to participate in the broader network topology and advertise their pod and service IPs just like any other node. Thus eliminating the need for tunnels or overlays to achieve true layer 3 connectivity.
In this blog, we’ll walk through the big picture, prerequisites, and step-by-step configuration for setting up BGP Continue reading
 Trend 1: Kubernetes is Central to AI Workload Orchestration
Trend 1: Kubernetes is Central to AI Workload Orchestration Trend 2: Growth in Edge Deployments Increases Complexity
Trend 2: Growth in Edge Deployments Increases Complexity