VMware Evolve Transform Security is Coming to A City Near You!
Modern IT professionals face significant security challenges. As digital transformation continues to connect applications, users, and data in the cloud, perimeter security models that once offered businesses protection are no longer sufficient. Critical visibility into users and endpoints is missing, enforcing policies is difficult, and, in the meantime, cyberattacks are more sophisticated and costly than ever.
What do IT teams need to defend today’s applications, users, and data from potentially brand-damaging attacks?
That’s the question VMware experts will be tackling during our VMware EVOLVE Transform Security events, coming to a city near you. During these half-day, in-person events, you will learn how a ubiquitous software layer can help support the security challenges of the modern business.
VMware experts will guide you through how to:
- Secure application infrastructure and better align security controls to apps
- Secure identity and endpoints to control access and enforce data loss prevention
- Streamline governance, risk management and compliance to limit cyber-attack vectors
Reserve your spot at an upcoming Transform Security-focused VMware EVOLVE event in your city:
The post VMware Evolve Transform Security is Coming to A City Near You! appeared first on Network Virtualization.
As 5G Looms, Service Providers Need to Consider CGNAT
 The 5G buzz is building and along with it are projections that some 5G networks will launch in 2018, with more widespread deployment in 2019. The launch of 5G networks will contribute to the large-scale proliferation of Internet of Things (IoT) devices.
The 5G buzz is building and along with it are projections that some 5G networks will launch in 2018, with more widespread deployment in 2019. The launch of 5G networks will contribute to the large-scale proliferation of Internet of Things (IoT) devices.
Cisco Picks ExtraHop to Strengthen Tetration
 ExtraHop is focused on understanding the context of multiple transactions from the network level.
ExtraHop is focused on understanding the context of multiple transactions from the network level.
Cisco Jasper Expands IoT Connectivity to NB-IoT, LTE-M
 This is the first major upgrade to the platform since Cisco acquired Jasper.
This is the first major upgrade to the platform since Cisco acquired Jasper.
Security Startup Jask Raises $14.5M for AI-Based Network Monitoring
 It aims to ‘democratizes security data’ for customers.
It aims to ‘democratizes security data’ for customers.
Cisco, McAfee Take On Email Security
 Other Cisco-McAfee security integrations are in the works.
Other Cisco-McAfee security integrations are in the works.
SD-WAN Vendors Look to Service Providers to Target SMBs
 SMBs don’t have all of the IT networking expertise that a large enterprise might have.
SMBs don’t have all of the IT networking expertise that a large enterprise might have.
A kindly lesson for you non-techies about encryption
The following tweets need to be debunked:The answer to John Schindler's question is:
every expert in cryptography doesn't know thisOh, sure, you can find fringe wacko who also knows crypto that agrees with you but all the sane members of the security community will not.
Telegram is not trustworthy because it's closed-source. We can't see how it works. We don't know if they've made accidental mistakes that can be hacked. We don't know if they've been bribed by the NSA or Russia to put backdoors in their program. In contrast, PGP and Signal are open-source. We can read exactly what the software does. Indeed, thousands of people have been reviewing their software looking for mistakes and backdoors.
Encryption works. Neither the NSA nor the Russians can break properly encrypted content. There's no such thing as "military grade" encryption that is better than consumer grade. There's only encryption that nobody can hack vs. encryption that your neighbor's teenage kid can easily hack. There's essentially nothing in between. Those scenes in TV/movies about breaking encryption is as realistic as sound in space: good for dramatic presentation, but not how things work in the real world.
In particular, end-to-end encryption works. Continue reading
A New Perspective on Security and the Public Cloud
 Moving applications and data to the public cloud brings a number of security advantages.
Moving applications and data to the public cloud brings a number of security advantages.
Security Here I Come!
The announcement has been made! It is completely official! I can finally share the awesome great news I am so excited about. Security will be my absolute #1 focus now.
Security has always fascinated me. My entire career. ….. It’s just that the fundamentals of routing and design intrigued me even more. 
But now? Yeah baby! Now I get to flip a switch… dive into and completely surround myself with all things Security. And I just could not be any more tickled pink and excited. I feel like all my years of networking have been a build up towards this.
Am I leaving my CPOC lab and job I adore so much? Nah… I’d go through withdrawal. LOL. Nah… wouldn’t be pretty. It is just my role that will be changing.
Woot woot! Security here I come! ROCK!
Cisco CEO Chuck Robbins Predicts the Future is Intent-Based Networking
 Cisco claims it can detect malware threats in encrypted traffic.
Cisco claims it can detect malware threats in encrypted traffic.
AT&T and AWS Boost Cloud Software Connectivity and Security Pact
 The deal adds support for more than 100 cloud software and service providers.
The deal adds support for more than 100 cloud software and service providers.
NTT Launches SD-WAN Platform with Virtela’s SDN Expertise
 NTT sources SD-WAN technology from multiple vendors in the space.
NTT sources SD-WAN technology from multiple vendors in the space.
BlackBerry Cites Security Challenge Behind Proprietary Container Product
 Analysts note that open source security concerns are more about deployment, not technology.
Analysts note that open source security concerns are more about deployment, not technology.
Technology Short Take #84
Welcome to Technology Short Take #84! This episode is a bit late (sorry about that!), but I figured better late than never, right? OK, bring on the links!
Networking
- When I joined the NSX team in early 2013, a big topic at that time was overlay protocols (VXLAN, STT, etc.). Since then, that topic has mostly faded, though it still does come up from time to time. In particular, the move toward Geneve has prompted that discussion again, and Russell Bryant tackles the discussion in this post.
- Sjors Robroek describes his nested NSX-T lab that also includes some virtualized network equipment (virtualized Arista switches). Nice!
- Colin Lynch shares some details on his journey with VMware NSX (so far).
- I wouldn’t take this information as gospel, but here’s a breakdown of some of the IPv6 support available in VMware NSX.
Servers/Hardware
- Here’s an interesting article on the role that virtualization is playing in the network functions virtualization (NFV) space now that ARM hardware is growing increasingly powerful. This is a space that’s going to see some pretty major changes over the next few years, in my humble opinion.
Security
- Anthony Burke gives a little bit of a sneak peek Continue reading
Technology Short Take #84
Welcome to Technology Short Take #84! This episode is a bit late (sorry about that!), but I figured better late than never, right? OK, bring on the links!
Networking
- When I joined the NSX team in early 2013, a big topic at that time was overlay protocols (VXLAN, STT, etc.). Since then, that topic has mostly faded, though it still does come up from time to time. In particular, the move toward Geneve has prompted that discussion again, and Russell Bryant tackles the discussion in this post.
- Sjors Robroek describes his nested NSX-T lab that also includes some virtualized network equipment (virtualized Arista switches). Nice!
- Colin Lynch shares some details on his journey with VMware NSX (so far).
- I wouldn’t take this information as gospel, but here’s a breakdown of some of the IPv6 support available in VMware NSX.
Servers/Hardware
- Here’s an interesting article on the role that virtualization is playing in the network functions virtualization (NFV) space now that ARM hardware is growing increasingly powerful. This is a space that’s going to see some pretty major changes over the next few years, in my humble opinion.
Security
- Anthony Burke gives a little bit of a sneak peek Continue reading
Cisco Aims to ‘Meraki-fy’ its Software Business, Lohmeyer Says
 Company is making software sticky so it can move customers to a subscription model.
Company is making software sticky so it can move customers to a subscription model.
Notes on open-sourcing abandoned code
Code is Speech
First of all, code is speech. That was the argument why Phil Zimmerman could print the source code to PGP in a book, ship it overseas, and then have somebody scan the code back into a computer. Compelled speech is a violation of free speech. That was one of the arguments in the Apple vs. FBI case, where the FBI demanded that Apple write code for them, compelling speech.
Compelling the opening of previously closed source is compelled speech. Sure, demanding new products come with source would be one thing, but going backwards demanding source for products sold before 2017 is quite another thing.
For most people, "rights" are something that only their own side deserves. Whether something deserves the protection of "free speech" depends upon whether the speaker is "us" or the speaker is "them". If it's "them", then you'll find all sorts of reasons Continue reading
CCIE/CCDE Re-certification: An Opportunity to Learn and Grow
I did not pass my CCDE re-certification last week. Why write a blog about a “failure”? Honestly? Because I think we as an IT industry overly focus and give too many kudos to the passing only. Not to the hours and hours of studying and learning… not to the lessons learned… not to the growth gained from the studying journey. Just to the “pass/fail”. Well damn… no wonder people cheat. Their focus isn’t on the learning or the journey. Just the passing.
I thoroughly believe the expression –
Sometimes you win….. Sometimes you learn.
Did I want to pass last week? ROFL! Are you kidding? Of course I did! Did I “deserve” to pass? Well…. um…. err… not exactly.
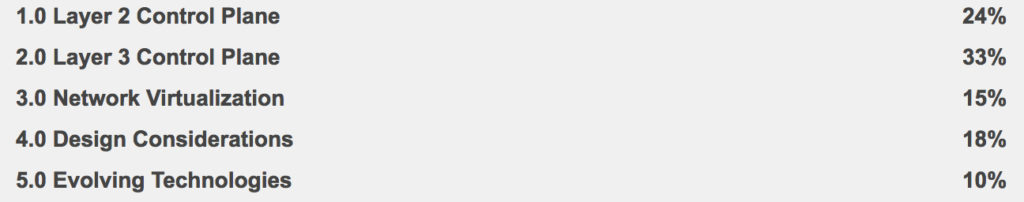
See that 10% at the bottom of the “Written Exam Topics v2.1?” Truth be told I didn’t quite exactly study that part very much.
So what is my plan now?
LEARN
Honestly in my job I am not doing much Cloud, SDN, or IoT. AND I have to admit I am quite happy I am now essentially forced to learn these to a Continue reading
More notes on US-CERTs IOCs
Yet another Russian attack against the power grid, and yet more bad IOCs from the DHS US-CERT.IOCs are "indicators of compromise", things you can look for in order to order to see if you, too, have been hacked by the same perpetrators. There are several types of IOCs, ranging from the highly specific to the uselessly generic.
A uselessly generic IOC would be like trying to identify bank robbers by the fact that their getaway car was "white" in color. It's worth documenting, so that if the police ever show up in a suspected cabin in the woods, they can note that there's a "white" car parked in front.
But if you work bank security, that doesn't mean you should be on the lookout for "white" cars. That would be silly.
This is what happens with US-CERT's IOCs. They list some potentially useful things, but they also list a lot of junk that waste's people's times, with little ability to distinguish between the useful and the useless.
An example: a few months ago was the GRIZZLEYBEAR report published by US-CERT. Among other things, it listed IP addresses used by hackers. There was no description which would be useful IP Continue reading