VMware: What to Do When Cybercriminals Hunt Your Company in Your Home
The worse-case scenario is “whether your entire brand will be used to attack your customers,”...
Weekly Wrap: Palo Alto Folds CloudGenix in $420M SASE Play
SDxCentral Weekly Wrap for April 3, 2020: CloudGenix had been targeting Cisco in the SD-WAN space;...
Do Coronavirus SOCs Look Like Zoom War Rooms?
When an incident occurs, enterprises typically rely on their on-site security operations centers to...
MUST READ: Using BGP RPKI for a Safer Internet
As I explained in How Networks Really Work and Upcoming Internet Challenges webinars, routing security, and BGP security in particular remain one of the unsolved challenges we’ve been facing for decades (see also: what makes BGP a hot mess).
Fortunately, due to enormous efforts of a few persistent individuals BGP RPKI is getting traction (NTT just went all-in), and Flavio Luciani and Tiziano Tofoni decided to do their part creating an excellent in-depth document describing BGP RPKI theory and configuration on Cisco- and Juniper routers.
There are only two things you have to do:
- Read the document;
- Implement RPKI in your network.
Thank you, the Internet will be grateful.
About them Zoom vulns…
Today a couple vulnerabilities were announced in Zoom, the popular work-from-home conferencing app. Hackers can possibly exploit these to do evil things to you, such as steal your password. Because of the COVID-19, these vulns have hit the mainstream media. This means my non-techy friends and relatives have been asking about it. I thought I'd write up a blogpost answering their questions.The short answer is that you don't need to worry about it. Unless you do bad things, like using the same password everywhere, it's unlikely to affect you. You should worry more about wearing pants on your Zoom video conferences in case you forget and stand up.
Now is a good time to remind people to stop using the same password everywhere and to visit https://haveibeenpwned.com to view all the accounts where they've had their password stolen. Using the same password everywhere is the #1 vulnerability the average person is exposed to, and is a possible problem here. For critical accounts (Windows login, bank, email), use a different password for each. (Sure, for accounts you don't care about, use the same password everywhere, I use 'Foobar1234'). Write these passwords down on paper and put that paper in Continue reading
SDxCentral’s Top 10 Articles — March 2020
Cisco Networking lessons learned during COVID-19; AT&T slashed more jobs; Microsoft topped...
Announcing the Beta for WARP for macOS and Windows


Last April 1 we announced WARP — an option within the 1.1.1.1 iOS and Android app to secure and speed up Internet connections. Today, millions of users have secured their mobile Internet connections with WARP.
While WARP started as an option within the 1.1.1.1 app, it's really a technology that can benefit any device connected to the Internet. In fact, one of the most common requests we've gotten over the last year is support for WARP for macOS and Windows. Today we're announcing exactly that: the start of the WARP beta for macOS and Windows.
What's The Same: Fast, Secure, and Free
We always wanted to build a WARP client for macOS and Windows. We started with mobile because it was the hardest challenge. And it turned out to be a lot harder than we anticipated. While we announced the beta of 1.1.1.1 with WARP on April 1, 2019 it took us until late September before we were able to open it up to general availability. We don't expect the wait for macOS and Windows WARP to be nearly as long.
The WARP client for macOS and Windows relies on the Continue reading
Introducing 1.1.1.1 for Families

Two years ago today we announced 1.1.1.1, a secure, fast, privacy-first DNS resolver free for anyone to use. In those two years, 1.1.1.1 has grown beyond our wildest imagination. Today, we process more than 200 billion DNS requests per day making us the second largest public DNS resolver in the world behind only Google.

Yesterday, we announced the results of the 1.1.1.1 privacy examination. Cloudflare's business has never involved selling user data or targeted advertising, so it was easy for us to commit to strong privacy protections for 1.1.1.1. We've also led the way supporting encrypted DNS technologies including DNS over TLS and DNS over HTTPS. It is long past time to stop transmitting DNS in plaintext and we're excited that we see more and more encrypted DNS traffic every day.
1.1.1.1 for Families

Since launching 1.1.1.1, the number one request we have received is to provide a version of the product that automatically filters out bad sites. While 1.1.1.1 can safeguard user privacy and optimize efficiency, it is designed for direct, fast DNS resolution, not for blocking or Continue reading
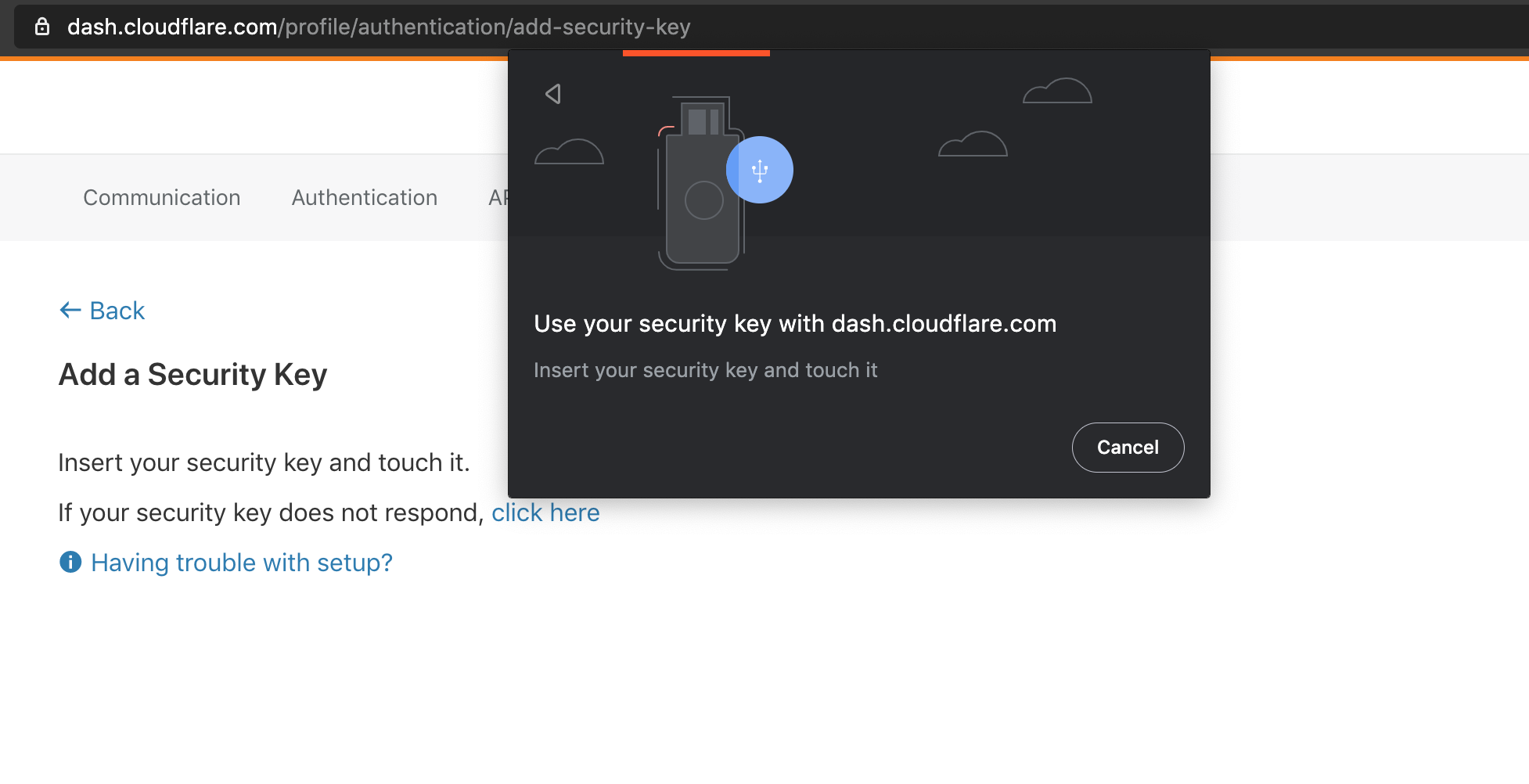
Cloudflare now supports security keys with Web Authentication (WebAuthn)!


We’re excited to announce that Cloudflare now supports security keys as a two factor authentication (2FA) method for all users. Cloudflare customers now have the ability to use security keys on WebAuthn-supported browsers to log into their user accounts. We strongly suggest users configure multiple security keys and 2FA methods on their account in order to access their apps from various devices and browsers. If you want to get started with security keys, visit your account's 2FA settings.
What is WebAuthn?
WebAuthn is a standardized protocol for authentication online using public key cryptography. It is part of the FIDO2 Project and is backwards compatible with FIDO U2F. Depending on your device and browser, you can use hardware security keys (like YubiKeys) or built-in biometric support (like Apple Touch ID) to authenticate to your Cloudflare user account as a second factor. WebAuthn support is rapidly increasing among browsers and devices, and we’re proud to join the growing list of services that offer this feature.
To use WebAuthn, a user registers their security key, or “authenticator”, to a supporting application, or “relying party” (in this case Cloudflare). The authenticator then generates and securely stores a public/private keypair on the device. The keypair Continue reading
CybersecurityCares Lists Free Tools During Coronavirus
It all started with a blog post by Axonius’ Nathan Burke: Things will be weird in cybersecurity...
Palo Alto Folds CloudGenix in $420M SASE Play
CloudGenix will form the second pillar of Palo Alto's emerging secure access service edge offering,...
Lenovo, Microsoft Push HCI to the Edge
Lenovo also rolled out new NVMe storage systems that integrate with AWS, Azure, Google, and IBM...
Comcast’s Jeffrey Lewis: ‘Job No. 1 Is Customer Experience’
Comcast's Jeffery Lewis sat down to share his thoughts on ActiveCore and how it is improving the...
Daily Roundup: VMware Pulls FY21 Forecast
VMware withdrew FY21 guidance citing coronavirus concerns; Kubernetes 1.18 ramped up Windows...
Security Experts Battle Hackers, COVID-19 Cyberattacks
Threat researchers at Microsoft, ClearSky, and Okta are among the hundreds of security experts...
Using Cloudflare to secure your cardholder data environment


As part of our ongoing compliance efforts Cloudflare’s PCI scope is reviewed quarterly and after any significant changes to ensure all in-scope systems are operating in accordance with the PCI DSS. This review also allows us to periodically review each product we offer as a PCI validated service provider and identify where there might be opportunities to provide greater value to our customers.
With our customers in mind, we completed our latest assessment and have increased our PCI certified product offering!
Building trust in our products is one critical component that allows Cloudflare’s mission of “Building a Better Internet” to succeed. We reaffirm our dedication to building trust in our products by obtaining industry standard security compliance certifications and complying with regulations.
Cloudflare is a Level 1 Merchant, the highest level, and also provides services to organizations to help secure their cardholder data environment. Maintaining PCI DSS compliance is important for Cloudflare because (1) we must ensure that our transmission and processing of cardholder data is secure for our own customers, (2) that our customers know they can trust Cloudflare’s products to transmit cardholder data securely, and (3) that anyone who interacts with Cloudflare’s services know that their information is Continue reading
Video: IPv6 Security Overview
When I’ve seen my good friends Christopher Werny and Enno Rey talk about IPv6 security at RIPE78 meeting, another bit of one of my puzzles fell in place. I was planning to do an update of the IPv6 security webinar I’d done with Eric Vyncke, and always wanted to get it done by a security practitioner focused on enterprise networks, making Christopher a perfect fit.
As it was almost a decade since we did the original webinar, Christopher started with an overview of IPv6 security challenges (TL&DR: not much has changed).
What Cisco Networking Learned During the Pandemic
Now that all Cisco employees work remotely, it sees more than 170,000 remote network connections...
Daily Roundup: Tier-1 Operators Back New TIP Spec
Tier-1 operators backed new TIP specifications; Juniper VP shared security strategy to make...
Is Kubernetes the Cure to Cantankerous 5G Core?
The promise of 5G hinges on adoption of cloud-native technologies and specifically Kubernetes as...