IT, OT Worlds Collide With 5G Security
Converged IT and OT security platforms are one way that service providers and security vendors are...
Juniper Security VP: Networks Must Be Threat Aware
Samantha Madrid joined the company with a very specific security strategy: change how we secure...
Speeding up Linux disk encryption
Data encryption at rest is a must-have for any modern Internet company. Many companies, however, don't encrypt their disks, because they fear the potential performance penalty caused by encryption overhead.
Encrypting data at rest is vital for Cloudflare with more than 200 data centres across the world. In this post, we will investigate the performance of disk encryption on Linux and explain how we made it at least two times faster for ourselves and our customers!
Encrypting data at rest
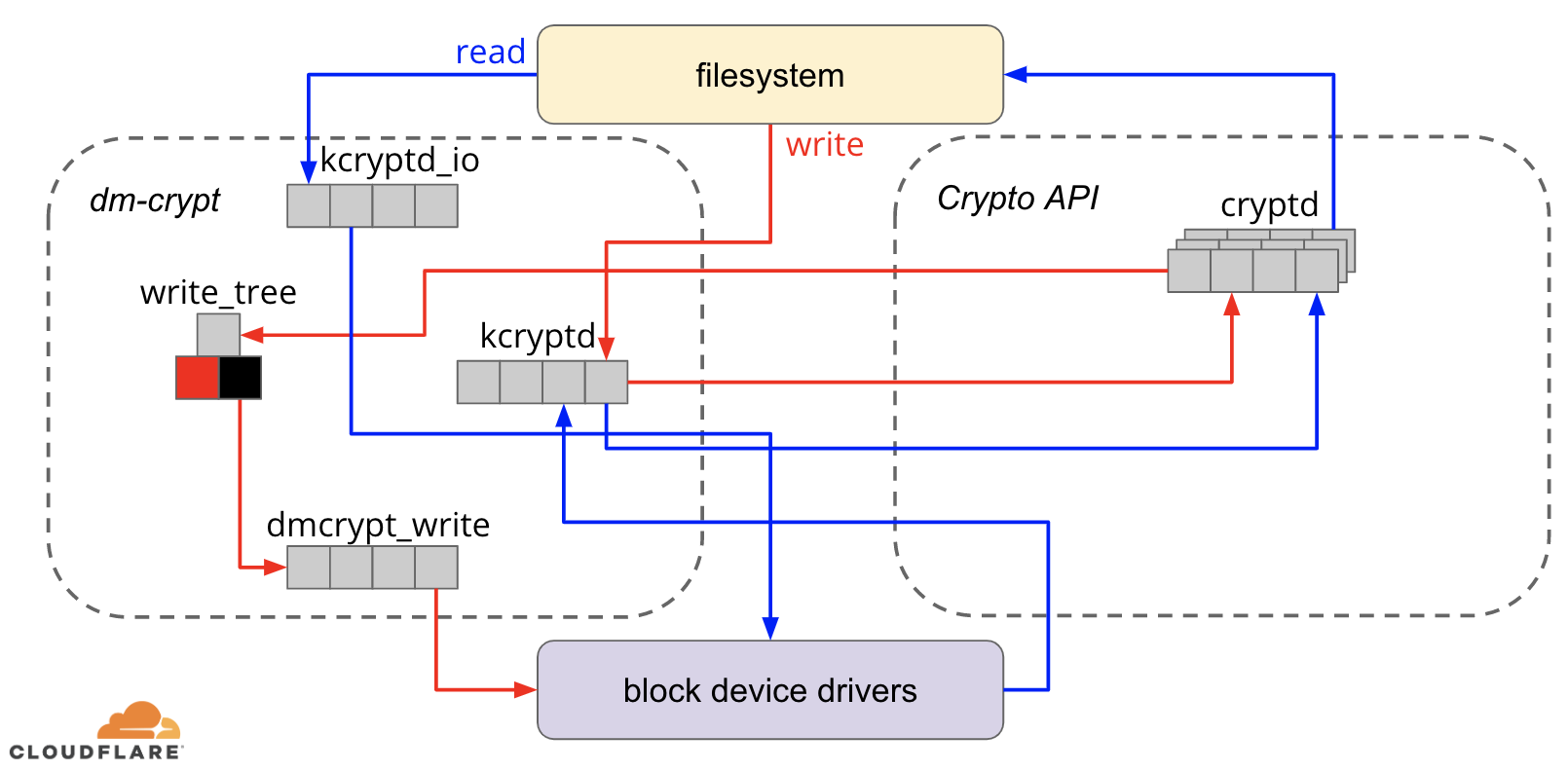
When it comes to encrypting data at rest there are several ways it can be implemented on a modern operating system (OS). Available techniques are tightly coupled with a typical OS storage stack. A simplified version of the storage stack and encryption solutions can be found on the diagram below:
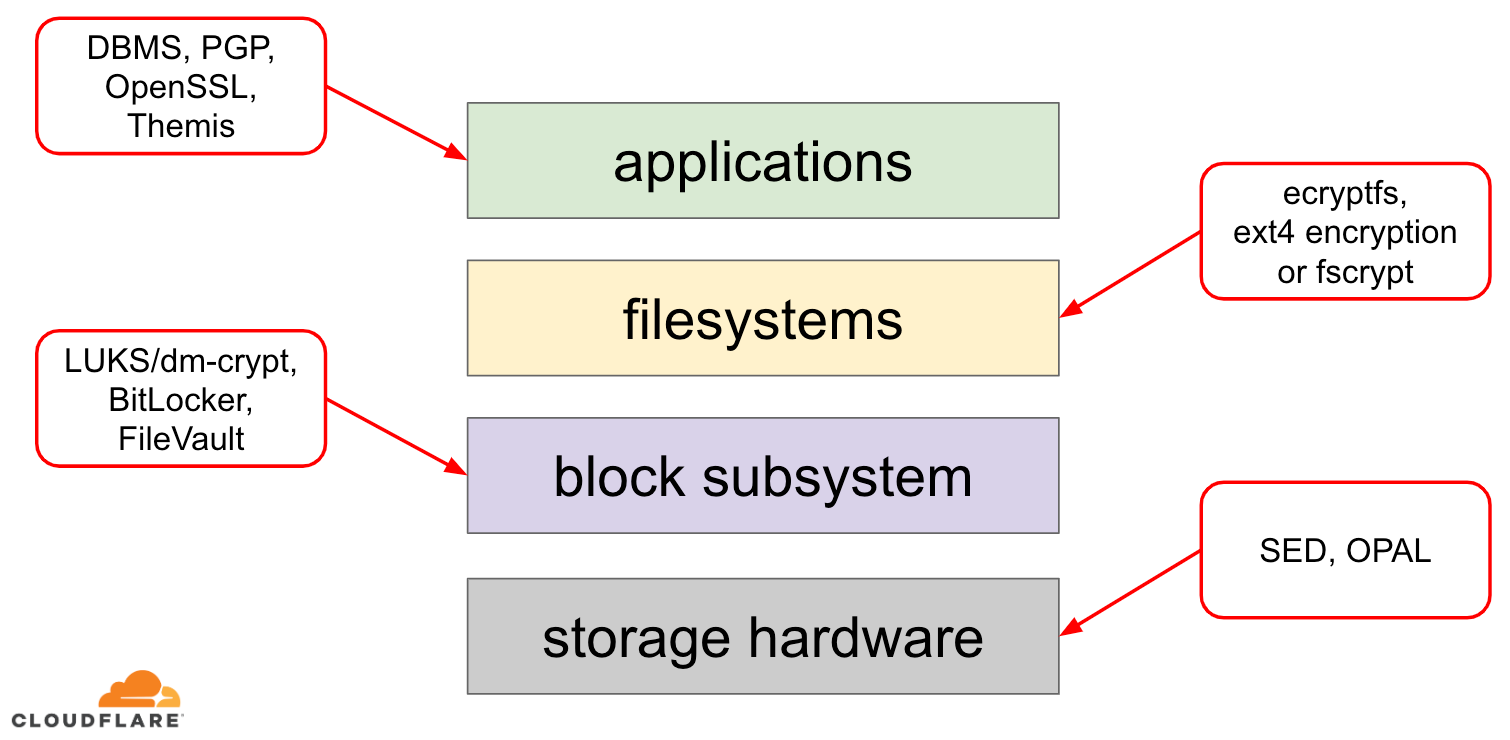
On the top of the stack are applications, which read and write data in files (or streams). The file system in the OS kernel keeps track of which blocks of the underlying block device belong to which files and translates these file reads and writes into block reads and writes, however the hardware specifics of the underlying storage device is abstracted away from the filesystem. Finally, the block subsystem actually Continue reading
Daily Roundup: Intel Warns of Financial Hit
Intel warned of financial hit; Attackers exploited remote-code execution vulnerabilities in...
Microsoft Warns of Attacks Exploiting Zero-Day Flaws
Microsoft said it’s “aware of limited targeted attacks” using the remote-code execution...
Cato Bolsters SASE-Based SDP to Serve Remote Workers
The vendor said the SASE architecture promises less complexity, shorter deployment times, improved...
SwiftStack Deploys Scalable Telecom Data Platform with Dell Technologies
SwiftStack’s data platform uses a combination of software-defined architecture engineered for the...
Deploying security.txt: how Cloudflare’s security team builds on Workers
When the security team at Cloudflare takes on new projects, we approach them with the goal of achieving the “builder first mindset” whereby we design, develop, and deploy solutions just as any standard engineering team would. Additionally, we aim to dogfood our products wherever possible. Cloudflare as a security platform offers a lot of functionality that is vitally important to us, including, but not limited to, our WAF, Workers platform, and Cloudflare Access. We get a lot of value out of using Cloudflare to secure Cloudflare. Not only does this allow us to test the security of our products; it provides us an avenue of direct feedback to help improve the roadmaps for engineering projects.
One specific product that we get a lot of use out of is our serverless platform, Cloudflare Workers. With it, we can have incredible flexibility in the types of applications that we are able to build and deploy to our edge. An added bonus here is that our team does not have to manage a single server that our code runs on.
Today, we’re launching support for the security.txt initiative through Workers to help give security researchers a common location to learn about how Continue reading
White Hat Hackers Fight COVID-19, Donate GPUs for a Cure
Security company Critical Start and its threat hunters are among the global contributors running...
Using Cloudflare Gateway to Stay Productive (and turn off distractions) While Working Remotely
This week, like many of you reading this article, I am working from home. I don’t know about you, but I’ve found it hard to stay focused when the Internet is full of news related to the coronavirus.
CNN. Twitter. Fox News. It doesn’t matter where you look, everyone is vying for your attention. It’s totally riveting…
… and it’s really hard not to get distracted.
It got me annoyed enough that I decided to do something about it. Using Cloudflare’s new product, Cloudflare Gateway, I removed all the online distractions I normally get snared by — at least during working hours.
This blog post isn’t very long, but that’s a function of how easy it is to get Gateway up and running!
Getting Started
To get started, you’ll want to set up Gateway under your Cloudflare account. Head to the Cloudflare for Teams dashboard to set it up for free (if you don’t already have a Cloudflare account, hit the ‘Sign up’ button beneath the login form).
If you are using Gateway for the first time, the dashboard will take you through an onboarding experience:
The onboarding flow will help you set up your first location. A location is Continue reading
HashiCorp Scores $175M Funding Round, $5B Valuation
The company has posted a 100% year-over-year increase in revenue during the past four years, and...
Announcing Network Analytics
Our Analytics Platform

Back in March 2019, we released Firewall Analytics which provides insights into HTTP security events across all of Cloudflare's protection suite; Firewall rule matches, HTTP DDoS Attacks, Site Security Level which harnesses Cloudflare's threat intelligence, and more. It helps customers tailor their security configurations more effectively. The initial release was for Enterprise customers, however we believe that everyone should have access to powerful tools, not just large enterprises, and so in December 2019 we extended those same enterprise-level analytics to our Business and Pro customers.

Since then, we’ve built on top of our analytics platform; improved the usability, added more functionality and extended it to additional Cloudflare services in the form of Account Analytics, DNS Analytics, Load Balancing Analytics, Monitoring Analytics and more.
Our entire analytics platform harnesses the powerful GraphQL framework which is also available to customers that want to build, export and share their own custom reports and dashboards.
Extending Visibility From L7 To L3
Until recently, all of our dashboards were mostly HTTP-oriented and provided visibility into HTTP attributes such as the user agent, hosts, cached resources, etc. This is valuable to customers that use Cloudflare to protect and accelerate HTTP Continue reading
FortiGuard Labs’ Derek Manky Talks Swarm Attacks, War of Deception
Collaboration and deception are two tools that Manky says should play a prominent role in...
Juniper Drives Kubernetes Into the Networking Conversation
The vendor has a twofold strategy to address multiple orchestration and enterprise challenges in...
SD-WAN Vendors Target SMBs as Competition Ramps Up
With at least 70 SD-WAN vendors on the market, standing out from the pack can be tricky. In an...
Weekly Wrap: Telia Taps Cisco Viptela SD-WAN
SDxCentral Weekly Wrap for March 13, 2020: The Sweden-based vendor cited Viptela's remote...
Cloudflare’s COVID-19 FAQs

As the status of COVID-19 continues to impact people and businesses around the world, Cloudflare is committed to providing awareness and transparency to our customers, employees, and partners about how we are responding. We do not anticipate any significant disruptions in Cloudflare services.
Our Business Continuity Team is monitoring the situation closely and all company personnel are kept up to date via multiple internal communication channels including a live chat room. Customers and the public are encouraged to visit this blog post for the latest information.
You can check the status of our network at www.cloudflarestatus.com. For COVID-19-related questions that aren’t answered below, please contact our Customer Support Team.
Does Cloudflare have a Business Continuity Team (BCT)?
Yes, Cloudflare’s Business Continuity Team is a cross-functional, geographically diverse group dedicated to navigating through a health crisis like COVID-19 as well as a variety of other scenarios that may impact employee safety and business continuity.
What is Cloudflare’s Business Continuity Plan in the light of COVID-19?
In addition to Cloudflare’s existing Disaster Recovery Plan we have implemented the following strategies:
- Daily Business Continuity Team meetings to determine if updates, changes, or communication need to be provided to customers, partners, and Continue reading
Cloudflare During the Coronavirus Emergency
This email was sent to all Cloudflare customers a short while ago
From: Matthew Prince
Date: Thu, Mar 12, 2020 at 4:20 PM
Subject: Cloudflare During the Coronavirus Emergency
We know that organizations and individuals around the world depend on Cloudflare and our network. I wanted to send you a personal note to let you know how Cloudflare is dealing with the Coronavirus emergency.
First, the health and safety of our employees and customers is our top priority. We have implemented a number of sensible policies to this end, including encouraging many employees to work from home. This, however, hasn't slowed our operations. Our network operations center (NOC), security operations center (SOC), and customer support teams will remain fully operational and can do their jobs entirely remote as needed.
Second, we are tracking Internet usage patterns globally. As more people work from home, peak traffic in impacted regions has increased, on average, approximately 10%. In Italy, which has imposed a nationwide quarantine, peak Internet traffic is up 30%. Traffic patterns have also shifted so peak traffic is occurring earlier in the day in impacted regions. None of these traffic changes raise any concern for us. Cloudflare's network is well provisioned Continue reading
Daily Roundup: AT&T Touts 5G Lead
AT&T peddled its 5G lead; AWS launched Bottlerocket Container OS; and Splunk made security...
Splunk Makes Security Hygiene Sexy Again
“Vulnerability management, configuration management, patch management — those things should...