The Big Trends That Were set to Shape MWC Barcelona
The event might not be happening, but that doesn't mean we are going to ignore the big trends we...
Kubernetes Security Plagued by Human Error, Misconfigs
Exposures and data breaches due to misconfigurations have become an “alarmingly common” trend...
Cisco Viptela Joins ConvergeOne’s SD-WAN Lineup
The announcement marks Cisco's second service provider announcement in the past month.
Using your devices as the key to your apps
I keep a very detailed budget. I have for the last 7 years. I manually input every expense into a spreadsheet app and use a combination of sumifs functions to track spending.
Opening the spreadsheet app, and then the specific spreadsheet, every time that I want to submit an expense is a little clunky. I'm working on a new project to make that easier. I'm building a simple web app, with a very basic form, into which I will enter one-off expenses. This form will then append those expenses as rows into the budget workbook.
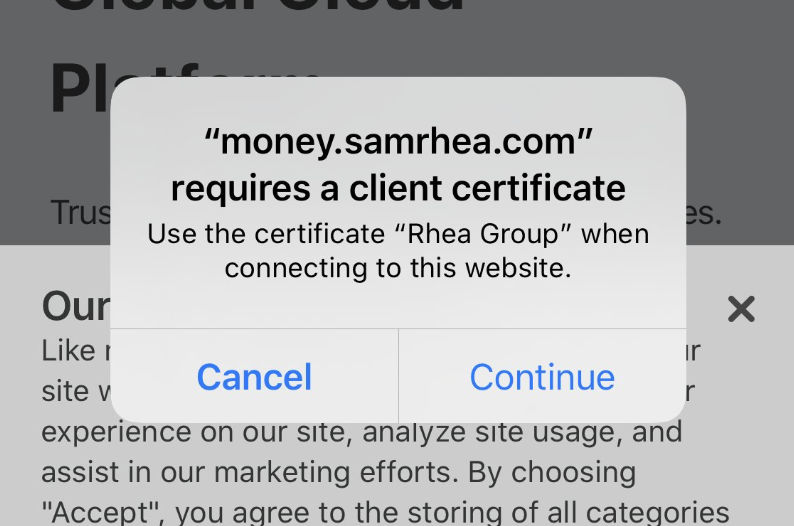
I want to lock down this project; I prefer that I am the only person with the power to wreck my budget. To do that, I'm going to use Cloudflare Access. With Access, I can require a login to reach the page - no server-side changes required.
Except, I don't want to allow logins from any device. For this project, I want to turn my iPhone into the only device that can reach this app.
To do that, I'll use Cloudflare Access in combination with an open source toolkit from Cloudflare, cfssl. Together, I can convert my device into a secure key for this application Continue reading
Weekly Wrap: Dell Sells RSA Security Biz for $2 Billion
SDxCentral Weekly Wrap for Feb. 21, 2020: The RSA deal includes the upcoming RSA security...
Why TIA Calls Supply Chain Security the ‘Most Critical Global Telecom Issue’
The industry group recently launched an initiative to develop telecommunications supply chain...
Banks and the Digital Revolution: Can this arranged marriage lead to love?
Networks at financial branches like banks require high security, low latency and constant...
Huawei Fails to Reverse Federal Ban
"Contracting with the federal government is a privilege, not a constitutionally guaranteed right,"...
Fortinet Firewall Update Tames 5G, IoT ‘Elephant Flows’
The company claims the appliance is capable of simultaneously juggling millions of connections per...
Daily Roundup: Dell Sells RSA, Bags $2B
Dell bagged $2B with the sale of RSA; AT&T shared threat intelligence; and Orange teamed up...
ExtraHop Extends Network Detection and Response to IoT
It becomes increasingly important as operators rollout 5G networks and enterprises connect billions...
Dell Sells RSA Security Biz for $2.075 Billion
The companies announced the deal a week before the annual RSA mega-cybersecurity conference kicks...
AT&T, Singtel, and Telefónica Share Threat Intel, Boost Customers’ Security
This anonymized data from the operators’ security operations centers and investigations is then...
Weekly Wrap: Coronavirus Kills MWC Barcelona
SDxCentral Weekly Wrap for Feb. 14, 2020: GSMA cancels this year's MWC Barcelona event; Cisco CEO...
Cisco’s Robbins: US Should Not Invest in 5G Companies
Double-digit declines in service provider sales continue to plague Cisco earnings. The vendor...
RSA Conference 2020 Expands Education Programs
RSA Conference, the world’s leading information security conferences and expositions, today...
Perimeter 81 Vows to Win SASE Space Race
“We believe there is a space race right now for SASE,” CEO Amit Bareket said. “Perimeter 81...
Let’s Encrypt: an automated certificate authority to encrypt the entire web
Let’s encrypt: an automated certificate authority to encrypt the entire web, Aas et al., CCS’19
This paper tells the story of Let’s Encrypt, from it’s early beginnings in 2012/13 all the way to becoming the world’s largest HTTPS Certificate Authority (CA) today – accounting for more currently valid certificates than all other browser-trusted CAs combined. Beyond the functionality that Let’s Encrypt provides, the story stands out to me for two key ingredients. Firstly, whereas normally we trade-off between security and ease-of-use, Let’s Encrypt made the web more secure through ease-of-use. Secondly, Let’s Encrypt managed to find a sustainable funding model for a combination of an open source project and free online service, as compared to the more normal pattern which sadly seems to involve running a small number of beneficent maintainers into the ground.
Since it’s launch in December 2015, Let’s Encrypt has steadily grown to become the largest CA in the Web PKI by certificates issued and the fourth largest known CA by Firefox Beta TLS full handshakes. As of January 21, 2019, the CA had issued a total of 538M certificates for 223M unique FQDNs… Let’s Encrypt has been responsible for significant growth in HTTPS deployment.
Network Field Day #NFD22
NSX: Networking and Security
Join us for #NFD22. The agenda is locked down and our in-house VMware experts are ready to go! They will be sharing their NSX know-how on the following:
- Full-Stack Kubernetes Networking Services
- Seamlessly automate micro-segmentation at scale with NSX Intelligence
- Load balancing and Web Application Firewalling across any private or public cloud with NSX Advanced Load Balancer
Here is a snapshot of the agenda and demo times:


The post Network Field Day #NFD22 appeared first on Network Virtualization.
Istio Security Bug Found, Quickly Squashed
The bug was in its authentication policy and allowed an attacker unauthorized access to information...
