Daily Roundup: Cisco Advances Intent-Based Networking
Cisco advanced intent-based networking; SK boasted standalone 5G first; and Citrix swatted ADC,...
Snyk Secures $150M, Snags $1B Valuation
The open source security startup reported over 400% revenue growth in 2019 and says its customers...
Telefónica Scores SD-WAN, Security Deal With Arlanxeo
The five-year contract will span more than 20 production sites in 11 countries across four...
Deep Dive: Scoring ISPs and Hosts on Privacy and Security

In April 2019 the Internet Society’s Online Trust Alliance (OTA) released its 10th Annual Online Trust Audit & Honor Roll. The Audit looks at the security and privacy practices of over 1,000 of the top sites on the Internet from retailers to governments. In this post we will take a deeper dive into the ISP/Hosts sector of the Audit. This sector is comprised of the top ISPs and other hosting organizations in the U.S. It includes everything from organizations that provide network access to organizations that host email services.
In the Audit, privacy statements are scored across 30 variables. ISP/Hosts were a decidedly mixed bag compared to other sectors, which tended to do either relatively well or poorly across the board in their statements. (Though to clear, the vast majority of organizations in the Audit had poor privacy statements, it was the most common reason for failure across privacy and security scoring.)
ISP/Hosts fell somewhat short in the presentation of their statements. OTA advocates several best practices that deal with how the privacy statement is displayed to make it as easy as possible for users to understand.
The simplest practice OTA advocates is a link to the privacy Continue reading
Citrix Swats ADC, Gateway Bugs, SD-WAN Fix in the Wings
“We urge customers to immediately install these fixes,” noted Citrix Chief Information Security...
IBM Secures $1.1B Contract With Banco Sabadell
The contract calls for IBM to simplify the bank's dispersed IT infrastructure and improve customer...
Oracle Fixes 334 Bugs in Record-Breaking Critical Patch Update
Almost 40 vulnerabilities with a 9.8 severity rating can be exploited over a network without...
Weekly Wrap: Nokia Cuts 180 Jobs With More to Come
SDxCentral Weekly Wrap for Jan. 17, 2020: 5G competition has been rough on Nokia; Citrix promises a...
McAfee Hires New CEO, Mulls Sale or IPO
“If they hired Peter Leav they are setting up to sell,” said analyst Zeus Kerravala.
Announcing the Cloudflare Access App Launch

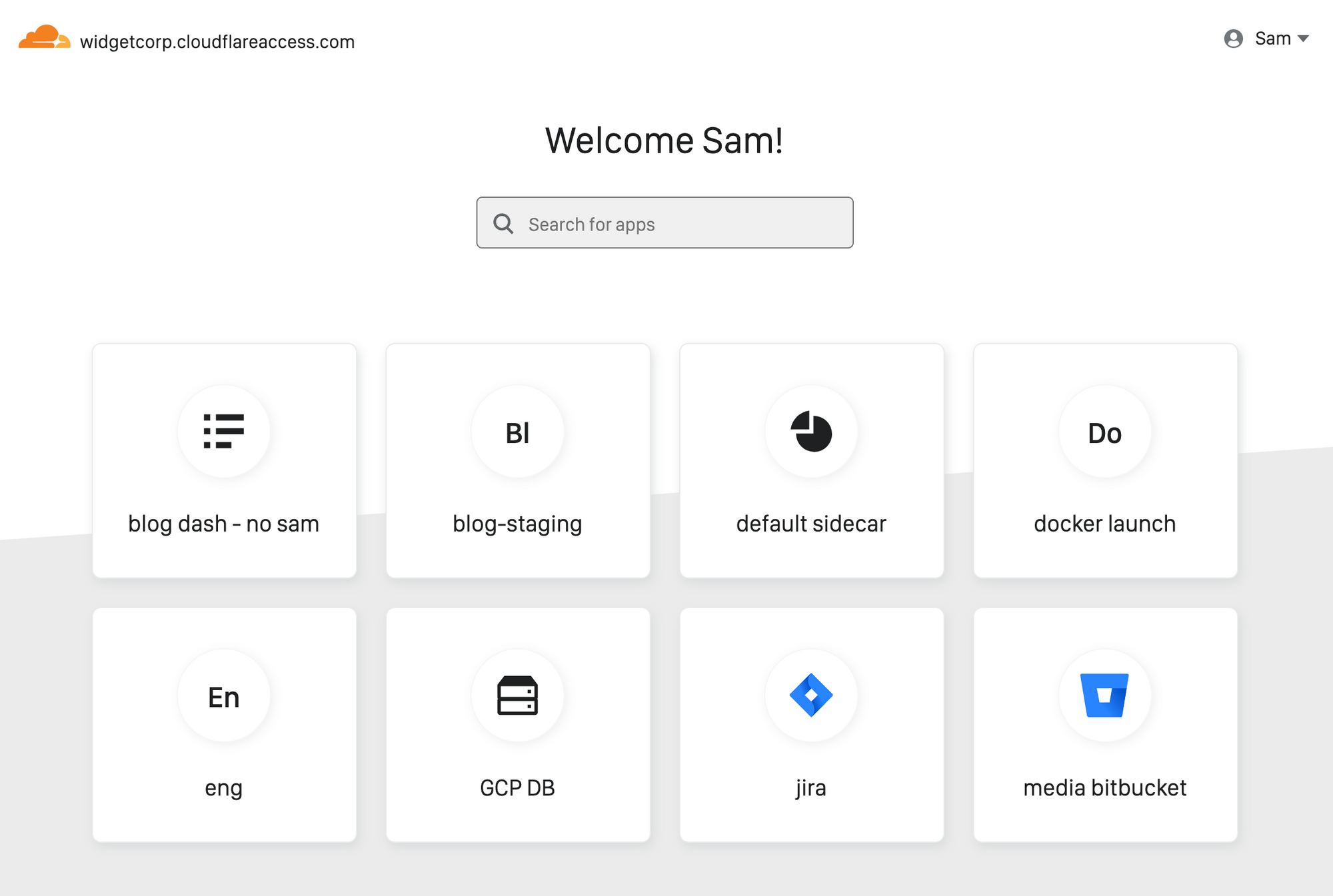
Every person joining your team has the same question on Day One: how do I find and connect to the applications I need to do my job?
Since launch, Cloudflare Access has helped improve how users connect to those applications. When you protect an application with Access, users never have to connect to a private network and never have to deal with a clunky VPN client. Instead, they reach on-premise apps as if they were SaaS tools. Behind the scenes, Access evaluates and logs every request to those apps for identity, giving administrators more visibility and security than a traditional VPN.
Administrators need about an hour to deploy Access. End user logins take about 20 ms, and that response time is consistent globally. Unlike VPN appliances, Access runs in every data center in Cloudflare’s network in 200 cities around the world. When Access works well, it should be easy for administrators and invisible to the end user.
However, users still need to locate the applications behind Access, and for internally managed applications, traditional dashboards require constant upkeep. As organizations grow, that roster of links keeps expanding. Department leads and IT administrators can create and publish manual lists, but those become Continue reading
SASE as Described in Gartner’s Hype Cycle for Enterprise Networking
In its recent Hype Cycle for Enterprise Networking, 2019, Gartner recognized Cato Networks as a...
Will SD-WAN Solve IoT’s Toughest Questions?
SD-WAN has the potential to address many of IoT's security and operational challenges, says Apcela...
Red Hat OpenShift Updates Hit Multi-Cloud, Security
The updates tap into Red Hat's NooBaa acquisition in 2018.
Introducing Cloudflare for Campaigns


During the past year, we saw nearly 2 billion global citizens go to the polls to vote in democratic elections. There were major elections in more than 50 countries, including India, Nigeria, and the United Kingdom, as well as elections for the European Parliament. In 2020, we will see a similar number of elections in countries from Peru to Myanmar. In November, U.S citizens will cast their votes for the 46th President, 435 seats in the U.S House of Representatives, 35 of the 100 seats in the U.S. Senate, and many state and local elections.
Recognizing the importance of maintaining public access to election information, Cloudflare launched the Athenian Project in 2017, providing U.S. state and local government entities with the tools needed to secure their election websites for free. As we’ve seen, however, political parties and candidates for office all over the world are also frequent targets for cyberattack. Cybersecurity needs for campaign websites and internal tools are at an all time high.
Although Cloudflare has helped improve the security and performance of political parties and candidates for office all over the world for years, we’ve long felt that we could do more. So today, Continue reading
Microsoft Patches Critical Windows Security Flaw
“For the U.S. government to share its discovery of a critical vulnerability with a vendor is...
Deep Dive: U.S. Federal Government’s Security and Privacy Practices

In April 2019, the Internet Society’s Online Trust Alliance released its 10th Annual Online Trust Audit & Honor Roll. The Audit looks at the security and privacy practices of over 1,000 of the top sites on the Internet, from retailers to government sites. In this post we will take a deeper dive into the U.S. Federal Government sector of the Audit. The Government sector is defined as the top 100 sites in the U.S. Federal Government by traffic (based on Alexa ranking). Given the nature of the U.S. Government compared to companies, this sample has some unique properties, namely site security.
The most obvious place the government excels is in the area of encryption. The reason for this is largely due to a mandate from the Homeland Security Department that all U.S. Government sites be encrypted, but the standard should still be the same for any site. Put another way, the other sectors in the Audit do not have an excuse for lagging in security.
In site security the Government sector fared the best with 100% adoption of “Always-On Secure Socket Layer” (AOSSL) and/or “HTTP Strict Transport Security” (HSTS), compared to 91% of sites overall. The Continue reading
Google Partners With CNCF, HackerOne on Kubernetes Bug Bounty
With more people looking for vulnerabilities, the safer and more secure Kubernetes will be,...
Public Cloud Networking Security is Different
If you’re running a typical (somewhat outdated) enterprise data center, you’re using tons of VLANs and firewalls, use VLANs as security zones, and push inter-VLAN traffic through firewalls for inspection. Security vendors love that approach - when inspecting traffic they can add no value to (like database- or backup sessions), the firewalls quickly become choke points that have to be upgraded.
Read more ...Citrix ACD, Gateway Bug Gets Even Uglier
Over the weekend two groups released proof-of-concept (PoC) exploit codes for this vulnerability on...
Cuckoo Installation and Configuration on Debian 10 Buster
The tutorial covers installation and configuration of Cuckoo Malware Sandbox on Debian 10 Buster. Once you complete successfully all steps, your Cuckoo installation will be ready to perform analysis of malware uploaded to guest VM. It is Windows 7 x64 SP1 VM running on Oracle VirtualBox. The tutorial is based on an excellent YouTube videos […]Continue reading...