‘Major Initiatives in Cybersecurity’ Shows Everyone Can Contribute to Trust

How do we work toward a more secure Internet?
In the Cyber Security discussions that take place in the various policy fora around the world, there is often little appreciation that the security of the Internet is a distributed responsibility, where many stakeholders take action.
By design, the Internet is a distributed system with no central core or point of control. Instead, Internet security is achieved by collaboration where multiple companies, organizations, governments, and individuals take action to improve the security and trustworthiness of the Internet – so that it is open, secure, and available to all.
Today we’ve published Major Initiatives in Cybersecurity: Public & Private Contributions Towards Increasing Internet Security to illustrate, via a handful of examples regarding Internet Infrastructure, there are a great number initiatives working, sometimes together and sometimes independently, in improving the Internet’s security. An approach we call collaborative security.
Major Initiatives in Cybersecurity describes Internet security as the part of cybersecurity that, broadly speaking, relates to the security of Internet infrastructure, the devices connected to it, and the technical building blocks from which applications and platforms are built.
We make no claim to completeness, but we do hope that the paper illustrates the complexity, breath, Continue reading
Money Moves: December 2019
Intel challenges Nvidia with its $2 billion Habana purchase; Cisco buys Exablaze; Fortinet snapped...
Aruba SD-Branch Update Targets Retail
The update includes new branch hardware with built-in cellular capabilities, improved security...
Veeam Snatched Up by Insight for $5B
Strong growth, high customer retention, and expansion opportunities make Veeam "one of the most...
How SD-Branch Rises to the Next-Gen Demands of Financial Services Networks
Financial networks require high speeds and solid security. Here's how SD-branch meets the needs of...
Falco Soars From CNCF Sandbox to Incubation
The Falco project joins 14 other Incubating projects as the first and, so far, only security...
FCC Chair Sets Ambitious 5G Goals for 2020
"Using the software layer to address not just the security but also the cost element, the cost...
Decentralized Calico Network Security Policy Deployment for GitOps – Part 2
In part 1 of the GitOps blog series, we discussed the value of using GitOps for Calico policies, and how to roll out such a framework. In this second part of the series, we will expand the scope to include decentralized deployment and GitOps.
We see different personas among our customers deploying three types of controls:
- Cluster hardening policies are enforced and controlled by the platform admin
- Organizational security controls are enforced and controlled by the security admin
- Each application team may have their own unique requirements. This is controlled by the DevOps admin for the specific application.
This is different from the traditional firewall world, where the security admin is responsible for managing security policies, and the change management window could be several weeks in duration. Adopting that model in Kubernetes is simply counter to the very principles of enabling the developers. So how can we make policy creation and enforcement simple, yet adhere to organizational processes? The answer lies in simple tooling, GitOps and governance.
Policies have business logic that must be implemented in YAML. The business logic (allow access for service A to service B, open port 443 inbound on service B, permit access to slack webhook Continue reading
Decentralized Calico Network Security Policy Deployment for GitOps – Part 2
In part 1 of the GitOps blog series, we discussed the value of using GitOps for Calico policies, and how to roll out such a framework. In this second part of the series, we will expand the scope to include decentralized deployment and GitOps.
We see different personas among our customers deploying three types of controls:
- Cluster hardening policies are enforced and controlled by the platform admin
- Organizational security controls are enforced and controlled by the security admin
- Each application team may have their own unique requirements. This is controlled by the DevOps admin for the specific application.
This is different from the traditional firewall world, where the security admin is responsible for managing security policies, and the change management window could be several weeks in duration. Adopting that model in Kubernetes is simply counter to the very principles of enabling the developers. So how can we make policy creation and enforcement simple, yet adhere to organizational processes? The answer lies in simple tooling, GitOps and governance.
Policies have business logic that must be implemented in YAML. The business logic (allow access for service A to service B, open port 443 inbound on service B, permit access to slack webhook Continue reading
Broadcom Sells Accenture Symantec Security Services Biz
The business unit had a long list of “potential suitors,” said Symantec’s John Lioanto....
Iran Cyberattacks Targeting US Companies Imminent, Experts Warn
“Beginning in the next 24 hours you will see cyberattacks manifesting as a harbinger for kinetics...
Deep Dive: How Does the Consumer Sector Score on Privacy and Security?

In April 2019 the Internet Society’s Online Trust Alliance released its 10th annual Online Trust Audit & Honor Roll. The Audit looks at the security and privacy practices of over 1,000 of the top sites on the Internet from retailers to government sites. In this post we will take a deeper dive into the Consumer section of the Audit. The Consumer section is a diverse set of sites including travel sites, hotels, and dating sites (see the methodology of the report for the full list).
In 2018 the Consumer section improved its standings with 85% making the honor roll, up from 76% in 2017. This was largely due to improvements in email security. Despite these gains in overall email security, TLS 1.3 adoption was actually down in 2018 (largely due to a change in the list of retail sites). Despite this OTA advocates the adoption of TLS 1.3.
Where these sites did stand out, compared to other sectors, was in privacy scores. Overall, the Consumer sector scored 43 out of 55 on their privacy tracker score, among the highest of any sector, and 33 out of 55 on their privacy statement, also among the highest.
The Consumer section Continue reading
Introducing Cloudflare for Teams

Ten years ago, when Cloudflare was created, the Internet was a place that people visited. People still talked about ‘surfing the web’ and the iPhone was less than two years old, but on July 4, 2009 large scale DDoS attacks were launched against websites in the US and South Korea.
Those attacks highlighted how fragile the Internet was and how all of us were becoming dependent on access to the web as part of our daily lives.
Fast forward ten years and the speed, reliability and safety of the Internet is paramount as our private and work lives depend on it.
We started Cloudflare to solve one half of every IT organization's challenge: how do you ensure the resources and infrastructure that you expose to the Internet are safe from attack, fast, and reliable. We saw that the world was moving away from hardware and software to solve these problems and instead wanted a scalable service that would work around the world.
To deliver that, we built one of the world's largest networks. Today our network spans more than 200 cities worldwide and is within milliseconds of nearly everyone connected to the Internet. We have built the capacity to stand Continue reading
Security on the Internet with Cloudflare for Teams


Your experience using the Internet has continued to improve over time. It’s gotten faster, safer, and more reliable. However, you probably have to use a different, worse, equivalent of it when you do your work. While the Internet kept getting better, businesses and their employees were stuck using their own private networks.
In those networks, teams hosted their own applications, stored their own data, and protected all of it by building a castle and moat around that private world. This model hid internally managed resources behind VPN appliances and on-premise firewall hardware. The experience was awful, for users and administrators alike. While the rest of the Internet became more performant and more reliable, business users were stuck in an alternate universe.
That legacy approach was less secure and slower than teams wanted, but the corporate perimeter mostly worked for a time. However, that began to fall apart with the rise of cloud-delivered applications. Businesses migrated to SaaS versions of software that previously lived in that castle and behind that moat. Users needed to connect to the public Internet to do their jobs, and attackers made the Internet unsafe in sophisticated, unpredictable ways - which opened up every business to a Continue reading
Cloudflare + Remote Browser Isolation
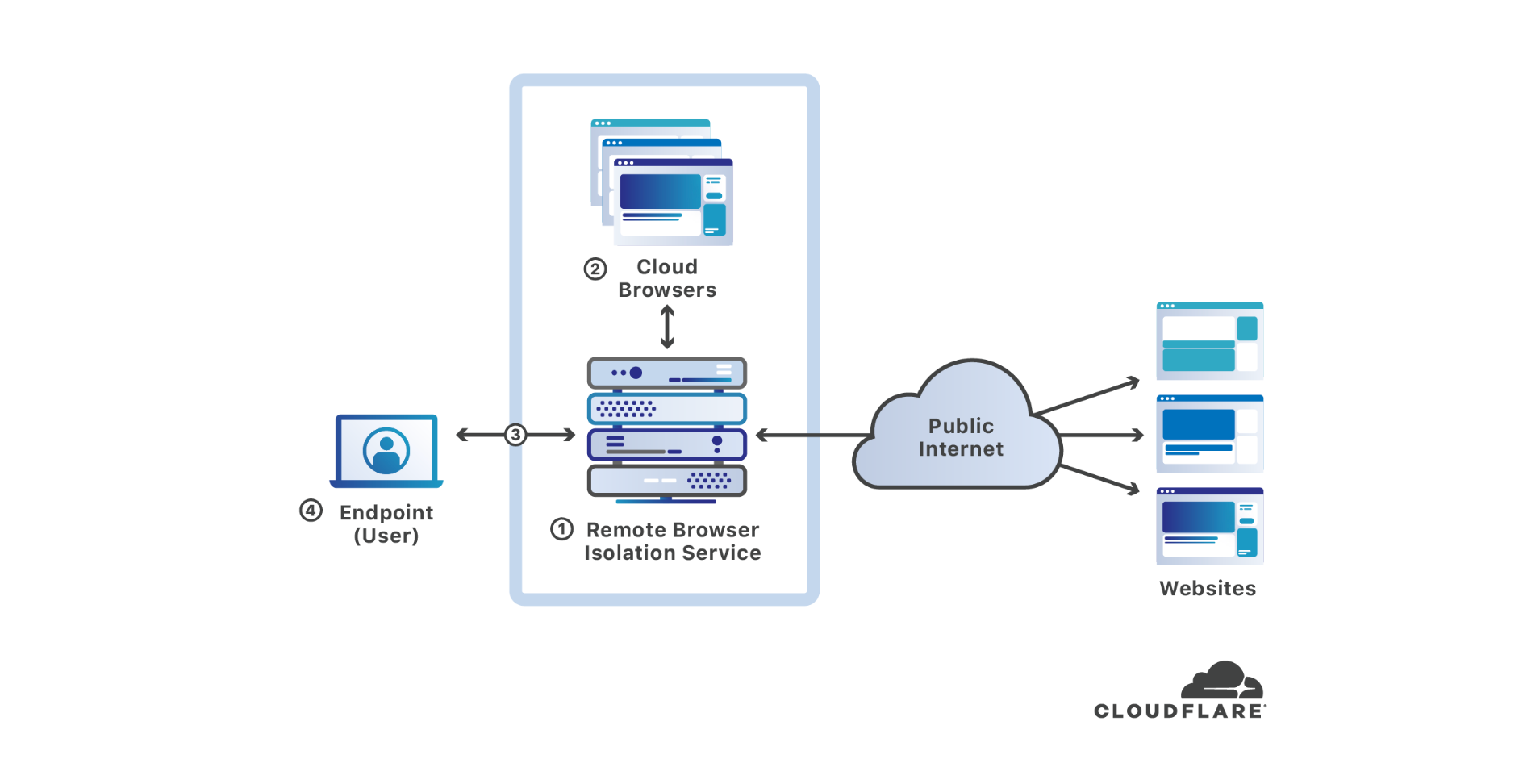
Cloudflare announced today that it has purchased S2 Systems Corporation, a Seattle-area startup that has built an innovative remote browser isolation solution unlike any other currently in the market. The majority of endpoint compromises involve web browsers — by putting space between users’ devices and where web code executes, browser isolation makes endpoints substantially more secure. In this blog post, I’ll discuss what browser isolation is, why it is important, how the S2 Systems cloud browser works, and how it fits with Cloudflare’s mission to help build a better Internet.
What’s wrong with web browsing?
It’s been more than 30 years since Tim Berners-Lee wrote the project proposal defining the technology underlying what we now call the world wide web. What Berners-Lee envisioned as being useful for “several thousand people, many of them very creative, all working toward common goals”[1] has grown to become a fundamental part of commerce, business, the global economy, and an integral part of society used by more than 58% of the world’s population[2].
The world wide web and web browsers have unequivocally become the platform for much of the productive work (and play) people do every day. However, as the pervasiveness Continue reading
Insight Scoops Up IoT Security Startup Armis for $1.1B
The deal marks the first cybersecurity acquisition of 2020, and it’s the largest-ever enterprise...
Cisco Patches More ‘Critical’ DCNM Flaws
The latest vulnerabilities are in the Data Center Network Manager authentication mechanism and...
Will Dell Technologies Fetch $3B for RSA?
Dell acquired the cybersecurity software company when it bought EMC in 2016. Since then it has...
Headcount: Firings, Hirings, and Retirings — December 2019
Juniper CTO Bikash Koley calls it quits; Larry Ellison says Oracle will not replace Hurd; plus the...
Security is a Glaring, Moving Target for IoT
“Security is one of the biggest factors limiting IoT expansion,” said Bill Curtis, resident...