Palo Alto Acquires Aporeto for $150M, Posts Mixed Q1
The acquisition will enable customers to secure their applications at scale. Meanwhile, weak Q2...
Deconstructing Google’s excuses on tracking protection

At worst Google is lying, at best, they are white lies ?
The post Deconstructing Google’s excuses on tracking protection appeared first on EtherealMind.
FCC Bans Huawei, ZTE From USF-Funded Projects
The new FCC order only singles out Huawei and ZTE, but the agency has also established a process to...
Operators Dish on Edge Computing Strategies at MEF 2019
Edge computing is a dispersion or distribution of the cloud and latency is the driving force of...
TCP MD5
TCP_MD5 (RFC 2385) is something that doesn’t come up often. There’s a couple of reasons for that, good and bad.
I used it with tlssh, but back then (2010) it was not practical due to the limitations in the API on Linux and OpenBSD.
This is an updated post, written after I discovered TCP_MD5SIG_EXT.
What it is
In short it’s a TCP option that adds an MD5-based signature to every TCP packet. It signs the source and destination IP addresses, ports, and the payload. That way the data is both authenticated and integrity protected.
When an endpoint enables TCP MD5, all unsigned packets (including SYN packets) are silently dropped. For a signed connection it’s not even possible for an eavesdropper to reset the connection, since the RST would need to be signed.
Because it’s on a TCP level instead of part of the protocol on top of TCP, it’s the only thing that can protect a TCP connection against RST attacks.
It’s used by the BGP protocol to set a password on the connection, instead of sending the password in the handshake. If the password doesn’t match the TCP connection doesn’t even establish.
But outside of BGP it’s essentially Continue reading
A10 Hires New CEO, No Word on Potential Sale
Almost four months after announcing that its founding CEO Lee Chen was on his way out, A10 Networks...
Weekly Wrap: Palo Alto Networks Leaps Into SASE Market
SDxCentral Weekly Wrap for Nov. 22, 2019: The burgeoning SASE market lures another entrant; Nokia...
Cisco Shakeup Hits Cloud, Networking Teams
The changes will "strongly position the company against our competitors," according to an internal...
Verizon Drives SDP Into Its Zero Trust Architecture
The new Zero Trust Architecture blocks connectivity to servers and applications from unknown...
Rachel Player Honored by Internet Security Research Group with Radiant Award
Internet security is accomplished by many unsung heroes. People who put their talent and passion into improving the Internet, making it secure and trustworthy. This is a feature of the Internet: security isn’t achieved through a central mandate but through the hard work and tenacity of individuals working across the globe.

Rachel Player, a cryptographic researcher, is one of those unsung heroes. She’s just been awarded the Radiant Award from the Internet Security Research Group, the folks behind Let’s Encrypt, for her work in post-quantum cryptography and homomorphic encryption. Homomorphic encryption allows people to do computations on encrypted data, so that information can remain private and still be worked with. This is a highly-relevant field in any area that deals with sensitive and personal data, such as medicine and finance. Player is also interested in lowering the barriers for young people – young women, especially – to work professionally on topics like cryptography.
Want to know more about Let’s Encrypt? Read a comprehensive overview of the initiative – from inspiration to Continue reading
Introducing Flan Scan: Cloudflare’s Lightweight Network Vulnerability Scanner
Today, we’re excited to open source Flan Scan, Cloudflare’s in-house lightweight network vulnerability scanner. Flan Scan is a thin wrapper around Nmap that converts this popular open source tool into a vulnerability scanner with the added benefit of easy deployment.
We created Flan Scan after two unsuccessful attempts at using “industry standard” scanners for our compliance scans. A little over a year ago, we were paying a big vendor for their scanner until we realized it was one of our highest security costs and many of its features were not relevant to our setup. It became clear we were not getting our money’s worth. Soon after, we switched to an open source scanner and took on the task of managing its complicated setup. That made it difficult to deploy to our entire fleet of more than 190 data centers.
We had a deadline at the end of Q3 to complete an internal scan for our compliance requirements but no tool that met our needs. Given our history with existing scanners, we decided to set off on our own and build a scanner that worked for our setup. To design Flan Scan, we worked closely with our auditors to understand Continue reading
Google Cloud Toughens Up Encryption, Network Security
This includes a new External Key Manager, which allows companies to store and manage encryption...
MEF Presses Managed Security in SD-WAN
“SD-WAN is the gateway for security,” MEF CTO Pascal Menezes said during his keynote at MEF...
IBM Boosts Open Tech With Cloud Pak for Security
The platform uses an open-source connector to integrate with IBM and other vendors’ security...
Even faster connection establishment with QUIC 0-RTT resumption

One of the more interesting features introduced by TLS 1.3, the latest revision of the TLS protocol, was the so called “zero roundtrip time connection resumption”, a mode of operation that allows a client to start sending application data, such as HTTP requests, without having to wait for the TLS handshake to complete, thus reducing the latency penalty incurred in establishing a new connection.
The basic idea behind 0-RTT connection resumption is that if the client and server had previously established a TLS connection between each other, they can use information cached from that session to establish a new one without having to negotiate the connection’s parameters from scratch. Notably this allows the client to compute the private encryption keys required to protect application data before even talking to the server.
However, in the case of TLS, “zero roundtrip” only refers to the TLS handshake itself: the client and server are still required to first establish a TCP connection in order to be able to exchange TLS data.
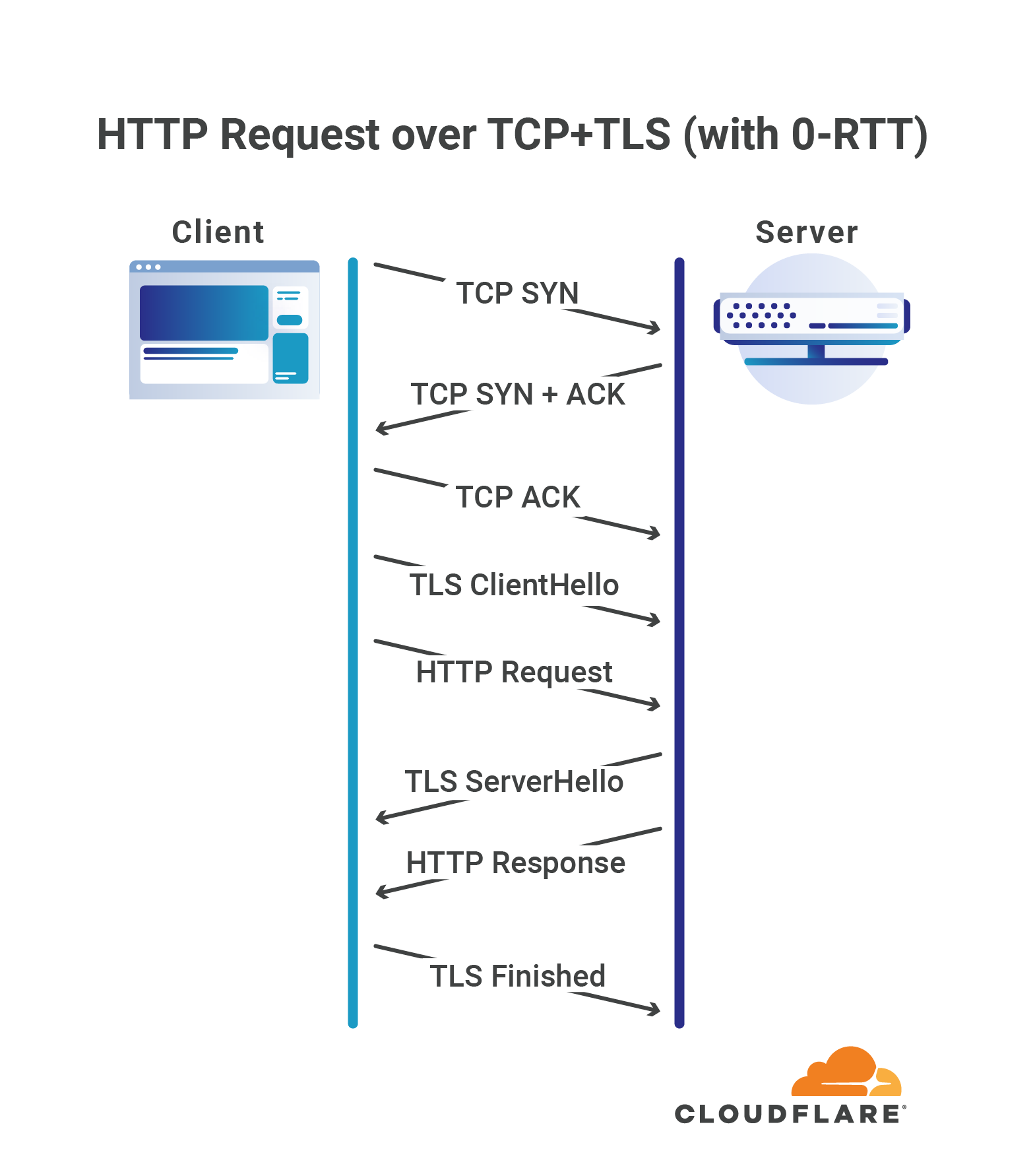
Zero means zero
QUIC goes a step further, and allows clients to send application data in the very first roundtrip of the connection, without requiring any other handshake to be Continue reading
Cloud Storage Startup Storj Hypes ‘Airbnb for Disk Drives’
The startup claims its decentralized storage costs less than half the price of AWS and cloud...
Orange, SoftBank Pick Fortinet SD-WAN
In addition to expanding its service provider reach, Fortinet announced an alliance with Siemens to...
Aryaka Breaks Out SD-WAN Into Smart Services Suite
Aryaka's restructured SmartServices product line breaks out many features previously only available...
Microsoft Drives Confidential Computing Into Kubernetes
The initiative taps into Intel’s Software Guard Extension platform to support confidential...
MEF Trumpets Progress on SD-WAN, Eyes Edge on 5G
MEF’s community has grown about 70% to more than 200 organizations during the last 18 months, and...