Log every request to corporate apps, no code changes required
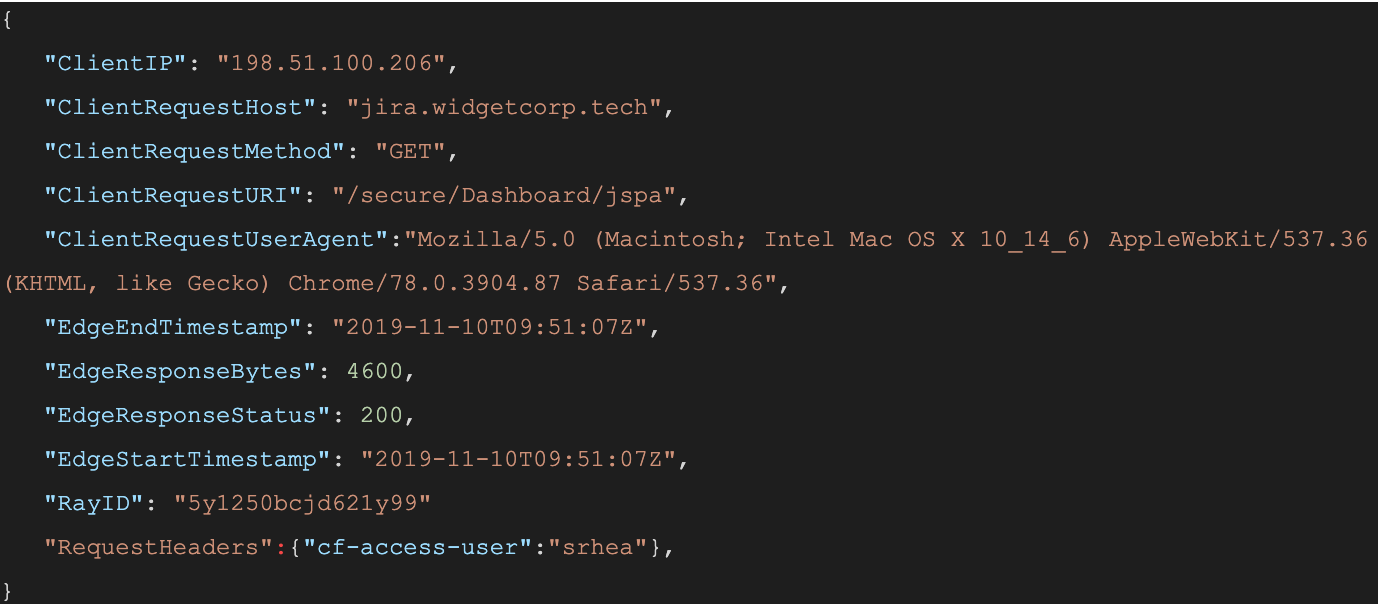
When a user connects to a corporate network through an enterprise VPN client, this is what the VPN appliance logs:
The administrator of that private network knows the user opened the door at 12:15:05, but, in most cases, has no visibility into what they did next. Once inside that private network, users can reach internal tools, sensitive data, and production environments. Preventing this requires complicated network segmentation, and often server-side application changes. Logging the steps that an individual takes inside that network is even more difficult.
Cloudflare Access does not improve VPN logging; it replaces this model. Cloudflare Access secures internal sites by evaluating every request, not just the initial login, for identity and permission. Instead of a private network, administrators deploy corporate applications behind Cloudflare using our authoritative DNS. Administrators can then integrate their team’s SSO and build user and group-specific rules to control who can reach applications behind the Access Gateway.
When a request is made to a site behind Access, Cloudflare prompts the visitor to login with an identity provider. Access then checks that user’s identity against the configured rules and, if permitted, allows the request to proceed. Access performs these checks on each request a user Continue reading
Dell Technologies CTO: Why AI Needs Empathy
If we want humans to trust artificial intelligence, then we need to teach the machines empathy,...
Palo Alto Networks Leaps Into SASE Market
Fulfilling Gartner's predictions, Palo Alto Networks announced its transition to a secure access...
Weekly Wrap: Juniper Guns for Cisco, Aruba With Mist AI
SDxCentral Weekly Wrap for Nov. 15, 2019: Juniper enhances its Mist AI platform and launches a new...
Librem13v2 TPM upgrade
I have upgraded my TPM firmware on my Librem13v2. Its keys are now safe. \o/
Back in 2017 we had the Infineon disaster (aka ROCA). I’ve written about it before about how bad it is and how to check if you’re affected with a simple tool.
I TAKE NO RESPONSIBILITY IF YOU BRICK YOUR DEVICE OR FOR ANYTHING ELSE BAD HAPPENING FROM YOU FOLLOWING MY NOTES.
Before the upgrade
$ tpm_version | grep Chip
Chip Version: 1.2.4.40 <--- Example vulnerable version
$ cbmem -c | grep Purism # I upgraded coreboot/SeaBIOS just before doing this.
coreboot-4.9-10-g123a4c6101-4.9-Purism-2 Wed Nov 13 19:54:43 UTC 2019 […]
[…]
Found mainboard Purism Librem 13 v2
Download upgrade tool
$ wget https://repo.pureos.net/pureos/pool/main/t/tpmfactoryupd/tpmfactoryupd_1.1.2459.0-0pureos9_amd64.deb
[…]
$ alien -t tpmfactoryupd_1.1.2459.0-0pureos9_amd64.deb
[…]
$ tar xfz tpmfactoryupd-1.1.2459.0.tgz
$ mv usr/bin/TPMFactoryUpd .
$ sudo systemctl stop trousers.service # Need to turn off tcsd for TPMFactoryUpd to work in its default mode.
[…]
$ ./TPMFactorUpd -info
**********************************************************************
* Infineon Technologies AG TPMFactoryUpd Ver 01.01.2459.00 *
**********************************************************************
TPM information:
----------------
Firmware valid : Yes
TPM family : 1.2
TPM firmware version Continue readingCisco Sinks on Rocky Q1, Dour Q2 Revenue Outlook
Service provider revenue dropped 13% year over year in Q1, while Cisco’s enterprise business...
How SD-Branch Enables Business Innovation
SD-branch can connect nearly any location, from a city office to a cabin in the woods. Here's how...
Money Moves: October 2019
Digital Reality dropped billions on European expansion; Ciena closed its acquisition of Centina;...
Beyond Thin Branch: Move Network Functions to Cloud
In-net SD-WAN allows maximum service delivery with minimum customer premises equipment (CPE)...
Aqua Buys CloudSploit, Moves Into Cloud Security Posture Management
Cloud security posture management includes processes and tools to avoid cloud misconfigurations...
AT&T Sounds Alarm on 5G Security
The top security concerns related to 5G include a larger attack surface, device proliferation, IoT...
Juniper Guns for Cisco, Aruba With Mist AI
“The larger vision here is that Mist is the cornerstone of Juniper’s AI-driven enterprise...
Analysts Debate SASE’s Merits as Vendors Board Hype Train
Gartner calls SASE a transformational technology but analysts from IHS Markit and IDC aren't...
Google Killed Chronicle, Report Claims
“The important thing to realize is we’re in this for the long haul,” Chronicle CEO Stephen...
Weekly Wrap: Fortinet Fortifies Firewall, SD-WAN Capabilities
SDxCentral Weekly Wrap for Nov. 8, 2019: Security and SD-WAN are Fortinet’s focus; Amazon is...
Kasten K10 v2.0 Targets Security and Simplicity
The company cited simplicity and security as being the heart of its K10 platform in order to target...
The Future of Hidden Features
 You may have noticed last week that Ubiquiti added a new “feature” to their devices in a firmware updated. According to this YouTube video from @TomLawrenceTech, Ubiquiti built an new service that contacts a URL to “phone home” and check in with their servers. It got some heavy discussion going, especially on Reddit.
You may have noticed last week that Ubiquiti added a new “feature” to their devices in a firmware updated. According to this YouTube video from @TomLawrenceTech, Ubiquiti built an new service that contacts a URL to “phone home” and check in with their servers. It got some heavy discussion going, especially on Reddit.
The consensus is that Ubiquiti screwed up here by not informing people they were adding the feature up front and also not allowing users to opt-out initially. The support people at Ubiquiti even posted a quick workaround of blocking the URL at a perimeter firewall to prevent the communications until they could patch in the option to opt-out. If this was an isolated incident I could see some manner of outcry about it, but the fact of the matter is that companies are adding these hidden features more and more every day.
The first issue comes from the fact that most release notes for apps any more are nothing aside from platitudes. “Hey, we fixed some bugs and stuff so turn on automatic updates so you get the best version of our stuff!” is somewhat common now when it comes to a list of Continue reading
Infoblox Snaps Up SnapRoute, Eyes SASE Market
SnapRoute's network operating system joins InfoBlox's growing software portfolio and helps fill out...
SEC 2. Data plane and control plane protection in the networking (Nokia, Cisco and Mellanox/Cumulus) for IPv6.
Hello my friend,
After the release of the previous article outlining the data and control plane security for IPv4 in Cisco, Nokia and Mellanox/Cumulus (link) I’ve got several requests about the security in IPv6. The requests were fair enough and with this article we close this gap.
2
3
4
5
retrieval system, or transmitted in any form or by any
means, electronic, mechanical or photocopying, recording,
or otherwise, for commercial purposes without the
prior permission of the author.
Thanks
Special thanks for Avi Alkobi from Mellanox and Pete Crocker and Attilla de Groot from Cumulus for providing me the Mellanox switch and Cumulus license for the tests.
Disclaimer
This is the fourth article in the series about the Mellanox/Cumulus switch. The three previous are:
- Building lab with Mellanox SN2010
- Configuring Segment Routing on Mellanox/Cumulus, Cisco IOS XR and Nokia SR OS and connecting physical and virtual networks
- Data and control plane protection in Mellanox/Cumulus, Cisco IOS XR and Nokia SR OS
Brief description
The importance of the security for the network in terms of the control and data plane protection was explained in the previous article Continue reading
VMware, Menlo Security Unite, Safeguard SD-WAN Stronghold
Menlo Security claims to provide VMware VeloCloud customers with direct access to the internet...
