Microsoft Unleashes a Tsunami of IoT Updates
The company unveiled a bevy of new updates to its burgeoning IoT portfolio aimed at addressing...
Supporting the latest version of the Privacy Pass Protocol


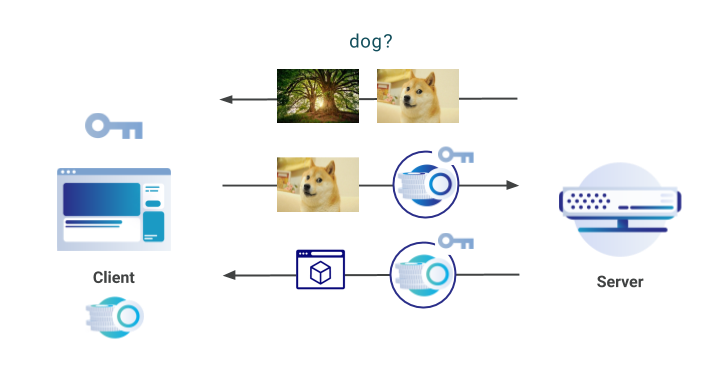
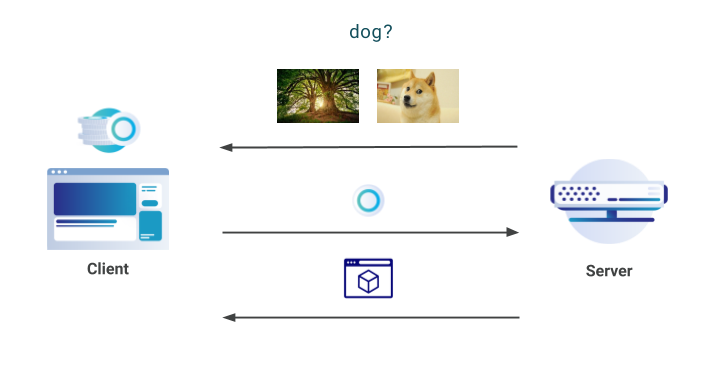
At Cloudflare, we are committed to supporting and developing new privacy-preserving technologies that benefit all Internet users. In November 2017, we announced server-side support for the Privacy Pass protocol, a piece of work developed in collaboration with the academic community. Privacy Pass, in a nutshell, allows clients to provide proof of trust without revealing where and when the trust was provided. The aim of the protocol is then to allow anyone to prove they are trusted by a server, without that server being able to track the user via the trust that was assigned.
On a technical level, Privacy Pass clients receive attestation tokens from a server, that can then be redeemed in the future. These tokens are provided when a server deems the client to be trusted; for example, after they have logged into a service or if they prove certain characteristics. The redeemed tokens are cryptographically unlinkable to the attestation originally provided by the server, and so they do not reveal anything about the client.
To use Privacy Pass, clients can install an open-source browser extension available in Chrome & Firefox. There have been over 150,000 individual downloads of Privacy Pass worldwide; approximately 130,000 in Chrome and Continue reading
Tales from the Crypt(o team)

Halloween season is upon us. This week we’re sharing a series of blog posts about work being done at Cloudflare involving cryptography, one of the spookiest technologies around. So bookmark this page and come back every day for tricks, treats, and deep technical content.
A long-term mission
Cryptography is one of the most powerful technological tools we have, and Cloudflare has been at the forefront of using cryptography to help build a better Internet. Of course, we haven’t been alone on this journey. Making meaningful changes to the way the Internet works requires time, effort, experimentation, momentum, and willing partners. Cloudflare has been involved with several multi-year efforts to leverage cryptography to help make the Internet better.
Here are some highlights to expect this week:
- We’re renewing Cloudflare’s commitment to privacy-enhancing technologies by sharing some of the recent work being done on Privacy Pass
- We’re helping forge a path to a quantum-safe Internet by sharing some of the results of the Post-quantum Cryptography experiment
- We’re sharing the rust-based software we use to power time.cloudflare.com
- We’re doing a deep dive into the technical details of Encrypted DNS
- We’re announcing support for a new technique we developed with industry partners Continue reading
Cisco Networking Trends Report: ‘Intent-Based Networking Is Coming’
Winter is coming, and according to Cisco's 2020 Global Networking Trends Report released today, so...
Slow Service Provider Sales Muddle Juniper’s Q3 Earnings
Growth within the company's enterprise, security and software businesses wasn't enough to offset...
The End of SD-WAN’s Party In China

As I was listening to Network Break Episode 257 from my friends at Packet Pushers, I heard Greg and Drew talking about a new development in China that could be the end of SD-WAN’s big influence there.
China has a new policy in place, according to Axios, that enforces a stricter cybersecurity stance for companies. Companies doing business in China or with offices in China must now allow Chinese officials to get into their networks to check for security issues as well as verifying the supply chain for network security.
In essence, this is saying that Chinese officials can have access to your networks at any time to check for security threats. But the subtext is a little less clear. Do they get to control the CPE as well? What about security constructs like VPNs? This article seems to indicate that as of January 1, 2020, there will be no intra-company VPNs authorized by any companies in China, whether Chinese or foreign businesses in China.
Tunnel Collapse
I talked with a company doing some SD-WAN rollouts globally in China all the way back in 2018. One of the things that was brought up in that interview was that Continue reading
Weekly Wrap: Ex-Cisco Execs Launch Pensando, Target Amazon
SDxCentral Weekly Wrap for Oct. 25, 2019: Pensando wants to democratize the cloud; Amazon continues...
Public keys are not enough for SSH security
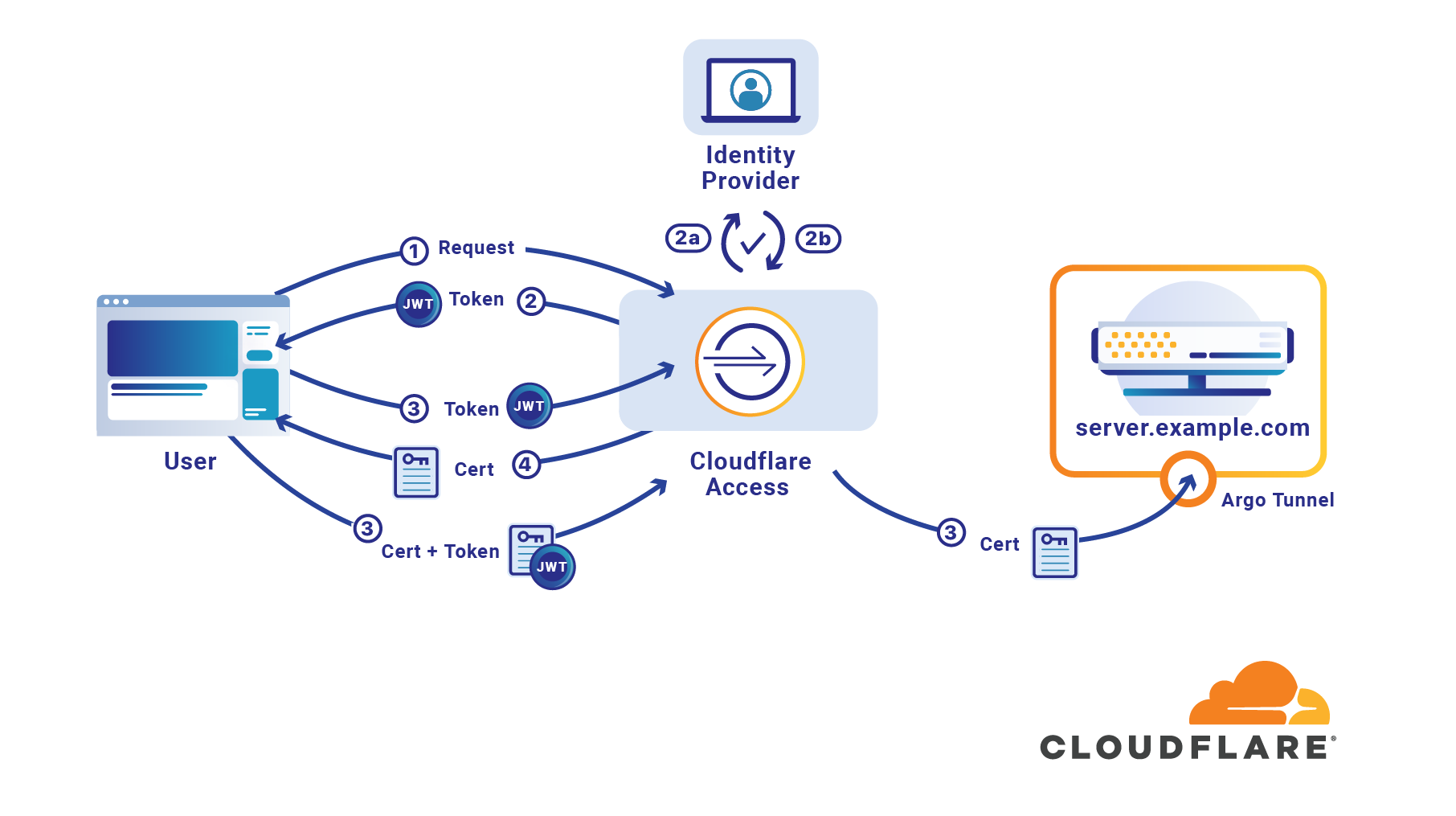
If your organization uses SSH public keys, it’s entirely possible you have already mislaid one. There is a file sitting in a backup or on a former employee’s computer which grants the holder access to your infrastructure. If you share SSH keys between employees it’s likely only a few keys are enough to give an attacker access to your entire system. If you don’t share them, it’s likely your team has generated so many keys you long lost track of at least one.
If an attacker can breach a single one of your client devices it’s likely there is a known_hosts file which lists every target which can be trivially reached with the keys the machine already contains. If someone is able to compromise a team member’s laptop, they could use keys on the device that lack password protection to reach sensitive destinations.
Should that happen, how would you respond and revoke the lost SSH key? Do you have an accounting of the keys which have been generated? Do you rotate SSH keys? How do you manage that across an entire organization so consumed with serving customers that security has to be effortless to be adopted?
Cloudflare Access launched support Continue reading
Enable GitOps for Kubernetes Security – Part 1
“How do I enable GitOps for my network policies?”
That is a common question we hear from security teams. Getting started with Kubernetes is relatively simple, but moving production workloads to Kubernetes requires alignment from all stakeholders – developers, platform engineering, network engineering, security.
Most security teams already have a high-level security blueprint for their data centers. The challenge is in implementing that in the context of a Kubernetes cluster and workload security. Network policy is a key element of Kubernetes security. Network policy is expressed as an YAML configuration, and works very well with GitOps.
We will do a 3 part blog series covering GitOps for network policies. In part 1 (this part), we cover the overview and getting started with a working example tutorial. In part 2, we will extend the tutorial to cover an enterprise-wide decentralized security architecture. In the final part, we will delve into policy assurance with examples. Note that all policies in Tigera Secure (network policy, RBAC, Threat detection, Logging configuration, etc.) are enforced as YAML configuration files, and can be enforced via a GitOps practice.
By adopting GitOps, security teams benefit as follows.
- Take your policies with you. Kubernetes cluster creation Continue reading
Teridion’s Cloud SD-WAN Service Glides Into China
The company aims to help multinational enterprises with branch offices in China shift their traffic...
VMware on White House Cybersecurity: ‘The Night’s Watch Is Very Thin’
An internal memo warns that “the White House is posturing itself to be electronically compromised...
What to Look for When Choosing a VPN

We welcome this guest post from Top10VPN.com, an Organization Member of the Internet Society.
The search for online privacy has driven a quarter of the world’s Internet users to download a Virtual Private Network (VPN). VPN services are now an important tool for anyone concerned about security and privacy on public networks.
There’s a world of difference between VPNs, though. Without clear and unbiased information many users are forced to navigate their choice of VPN without much clarity.
Why is choosing the right VPN provider so important?
Whenever you switch on a VPN you are entrusting its provider with your personal data, browsing activity, and sometimes even your security. For this reason, VPN providers must be held to a higher standard than most products. It’s important you do your due diligence when making a decision.
What should I look out for?
A good VPN will ensure that no one – even the VPN itself – can see what the user is doing online. Consider the following qualities:
Technical Security
The most secure VPN services will be transparent about the measures they have in place to safeguard their users and their business.
Any VPN worth its salt will offer Continue reading
Nokia VP: 5G Security Risks Are Huge
5G's impacts on society will be immense, and so will its security implications, said Mary O'Neill,...
BlackBerry CTO: ‘More Security, Less Friction Is The Dream’
BlackBerry has invested billions in security technologies and acquisitions in its quest to replace...
5G Spectrum Crunch Drives Conversation at MWC LA 2019
FCC Chairman Ajit Pai echoed other speakers sentiments about the need for more low-, mid-, and...
Microsoft Moves on Mover Months After Movere Move
Mover supports the migration of files from more than a dozen cloud providers, including Box,...
GSMA Warns Industry About Threatening Challenges
Challenges include the loss of trust in global supply chains, the loss of trust in the protection...
Splunk Buys Another Startup, Launches Mission Control
CTO Tim Tully kicked off the annual user conference by announcing Splunk reached a deal to buy open...
Your Day with Encryption

How often do you use encryption? It seems like the stuff of spy films, but you might be surprised to find out how often it touches your daily life.
Encryption is the process of scrambling or enciphering data, and only someone with the key can read or access it. You can use it for things like shopping online, using mobile banking, or using secure messaging apps. So while you may not be smuggling encrypted government secrets across borders, you do rely on it, along with your passwords and settings, to keep your data secure and private.
Learn about all of the ways you use encryption.
07:21

Your alarm vibrates. You reach for your phone, ready to snooze before you think better of it. You’ve got a big presentation at work and you’re going to need every minute today. There’s a message from your friend in Australia wishing you luck. How thoughtful! Even more thoughtful: your friend used an end-to-end encrypted messaging app. Sure, they saved on international phone charges, but the added security is nice too.
08:13

You’re ready to go, but before heading out, you check a news website for the traffic report. There’s a lock icon on the Continue reading
Designing Docker Hub Two-Factor Authentication

We recognize the central role that Docker Hub plays in modern application development and are working on many enhancements around security and content. In this blog post we will share how we are implementing two-factor authentication (2FA).
Using Time-Based One-Time Password (TOTP) Authentication
Two-factor authentication increases the security of your accounts by requiring two different forms of validation. This helps ensure that you are the rightful account owner. For Docker Hub, that means providing something you know (your username and a strong password) and something you have in your possession. Since Docker Hub is used by millions of developers and organizations for storing and sharing content – sometimes company intellectual property – we chose to use one of the more secure models for 2FA: software token (TOTP) authentication.
TOTP authentication is more secure than SMS-based 2FA, which has many attack vectors and vulnerabilities. TOTP requires a little more upfront setup, but once enabled, it is just as simple (if not simpler) than text message-based verification. It requires the use of an authenticator application, of which there are many available. These can be apps downloaded to your mobile device (e.g. Google Authenticator or Microsoft Authenticator) or it can Continue reading