Imperva Acquires Application Security Vendor Prevoty for $140M
 Prevoty’s product uses runtime application self-protection (RASP), an emerging security technology that is built into an application and can detect and respond to attacks in real time.
Prevoty’s product uses runtime application self-protection (RASP), an emerging security technology that is built into an application and can detect and respond to attacks in real time.
Q2 FY 18 Product Releases, for a better Internet “end-to-end”

Photo by Liu Zai Hou / Unsplash
In Q2, Cloudflare released several products which enable a better Internet “end-to-end” — from the mobile client to host infrastructure. Now, anyone from an individual developer to large companies and governments, can control, secure, and accelerate their applications from the “perimeter” back to the “host.”
On the client side, Cloudflare’s Mobile SDK extends control directly into your mobile apps, providing visibility into application performance and load times across any global carrier network.
On the host side, Cloudflare Workers lets companies move workloads from their host to the Cloudflare Network, reducing infrastructure costs and speeding up the user experience. Argo Tunnel lets you securely connect your host directly to a Cloudflare data center. If your host infrastructure is running other TCP services besides HTTP(S), you can now protect it with Cloudflare’s DDoS protection using Spectrum.
So for end-to-end control that is easy and fast to deploy, these recent products are all incredible “workers” across the “spectrum” of your needs.
But there’s more to the story
End users want richer experiences, such as more video, interactivity, and images. Meeting those needs can incur real costs in bandwidth, hardware, and time. Cloudflare addresses these with Continue reading
Nation-States, Criminals Increasing Attacks on ERP Systems, DHS Warns
 Threat researchers found a rise in attacks on widely-used enterprise resource planning (ERP) applications such as SAP and Oracle, which currently have a combined 9,000 known security vulnerabilities.
Threat researchers found a rise in attacks on widely-used enterprise resource planning (ERP) applications such as SAP and Oracle, which currently have a combined 9,000 known security vulnerabilities.
Tenable Could Raise $288M, Making It Largest Security IPO in 5 Years
 While it’s not the first security firm to go public this year — Zscaler and Carbon Black also completed successful IPOs — at $288 million it would be the most profitable.
While it’s not the first security firm to go public this year — Zscaler and Carbon Black also completed successful IPOs — at $288 million it would be the most profitable.
The Road to QUIC

QUIC (Quick UDP Internet Connections) is a new encrypted-by-default Internet transport protocol, that provides a number of improvements designed to accelerate HTTP traffic as well as make it more secure, with the intended goal of eventually replacing TCP and TLS on the web. In this blog post we are going to outline some of the key features of QUIC and how they benefit the web, and also some of the challenges of supporting this radical new protocol.

There are in fact two protocols that share the same name: “Google QUIC” (“gQUIC” for short), is the original protocol that was designed by Google engineers several years ago, which, after years of experimentation, has now been adopted by the IETF (Internet Engineering Task Force) for standardization.
“IETF QUIC” (just “QUIC” from now on) has already diverged from gQUIC quite significantly such that it can be considered a separate protocol. From the wire format of the packets, to the handshake and the mapping of HTTP, QUIC has improved the original gQUIC design thanks to open collaboration from many organizations and individuals, with the shared goal of making the Internet faster and more secure.
So, what are the improvements QUIC provides?
Built-in security (and Continue reading
Financial Services Take Containers to the Bank
 Big banks find more to like with container technology, which offers security plus tools to innovate and better compete in a dogged marketplace.
Big banks find more to like with container technology, which offers security plus tools to innovate and better compete in a dogged marketplace.
How BCG Gamma is Transforming Analytics with Docker
Changing the culture and service offerings of a big consulting firm isn’t easy, but BCG has been on that path for the past five years. BCG has evolved from traditional consulting services into a digital transformation powerhouse with six divisions that deliver strategic and technical services to clients.
One of those divisions, BCG Gamma, is a global team of world-class data scientists who build data analytics, machine learning, and artificial intelligence solutions for the firm’s clients. But building and shipping analytics, ML and AI applications to clients is challenging. Andrea Gallego, CTO of the division, is charged with creating an infrastructure that can support delivering high-quality ML and AI models at scale.
The Challenge: Shipping ML and AI Software to Clients at Scale
The big question on her mind was how BCG Gamma could not only build models, but deliver them to clients at the edge with real-time orchestration, monitoring and updates. GDPR and other regulations also meant she had to do this while ensuring integrity, consistency and lineage across data models.
Andrea and her team launched the BCG GammaX initiative, a core team of 30 engineers specializing in analytics software engineering, data engineering, UX design, distributed systems, and Continue reading
Qualcomm Nixes $44B NXP Acquisition
![]() China’s refusal to approve the deal was viewed as part of the growing trade war between the U.S. and China.
China’s refusal to approve the deal was viewed as part of the growing trade war between the U.S. and China.
Rubrik’s Radar Tackles Ransomware With Machine Learning
 Unlike traditional security platforms that target this type of malware from a threat prevention vantage point, the data protection and management company comes at it from a backup perspective.
Unlike traditional security platforms that target this type of malware from a threat prevention vantage point, the data protection and management company comes at it from a backup perspective.
Security Startups LoginRadius and Siemplify Score Millions More in Funding
 Microsoft's venture fund, M12, is just one of the VC firms pouring money into security startups.
Microsoft's venture fund, M12, is just one of the VC firms pouring money into security startups.
EdgeX Foundry Adds Security to IoT Open Source Software
 The beauty of EdgeX open source software is that companies can “mix-and-match” components.
The beauty of EdgeX open source software is that companies can “mix-and-match” components.
Episode 31 – Analytics and Security
Security is facing a crisis of well trained engineers. As a result, operators are relying more heavily on analytics to provide security intelligence. In this show, Eric Osterweil joins Network Collective to discuss the use of analytics in security, and the role analytics can play to augment engineering talent.
 We would like to thank Core BTS for sponsoring this episode of Network Collective. Core BTS focuses on partnering with your company to deliver technical solutions that enhance and drive your business. If you’re looking for a partner to help your technology teams take the next step, you can reach out to Core BTS by emailing them here.
We would like to thank Core BTS for sponsoring this episode of Network Collective. Core BTS focuses on partnering with your company to deliver technical solutions that enhance and drive your business. If you’re looking for a partner to help your technology teams take the next step, you can reach out to Core BTS by emailing them here.
We also would also like to thank Cumulus Networks for sponsoring this episode of Network Collective. Cumulus is bringing S.O.U.L. back to the network. Simple. Open. Untethered. Linux. For more information about how you can bring S.O.U.L. to your network, head on over to https://cumulusnetworks.com/ncautomation. There you can find out how Cumulus Networks can help you build a datacenter as efficient and as flexible as the worlds largest data centers and try Cumulus technology absolutely free.
Google Cloud CEO: Enterprise Table Stakes and Cutting Edge
 At the annual Google Next conference the company launched an integrated portfolio of cloud services that combine open source projects with Google’s cloud infrastructure and security services.
At the annual Google Next conference the company launched an integrated portfolio of cloud services that combine open source projects with Google’s cloud infrastructure and security services.
Going Proactive on Security: Driving Encryption Adoption Intelligently
It's no secret that Cloudflare operates at a huge scale. Cloudflare provides security and performance to over 9 million websites all around the world, from small businesses and WordPress blogs to Fortune 500 companies. That means one in every 10 web requests goes through our network.
However, hidden behind the scenes, we offer support in using our platform to all our customers - whether they're on our free plan or on our Enterprise offering. This blog post dives into some of the technology that helps make this possible and how we're using it to drive encryption and build a better web.
Why Now?
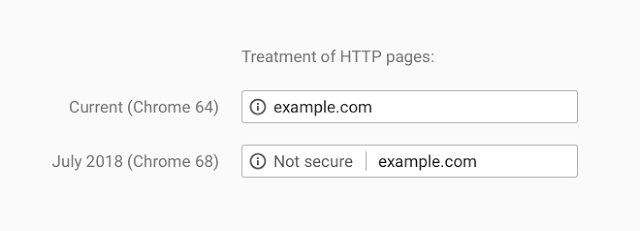
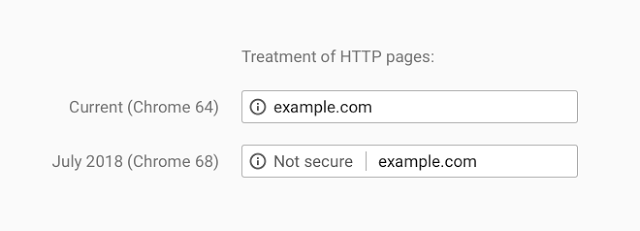
Recently web browser vendors have been working on extending encryption on the internet. Traditionally they would use positive indicators to mark encrypted traffic as secure; when traffic was served securely over HTTPS, a green padlock would indicate in your browser that this was the case. In moving to standardise encryption online, Google Chrome have been leading the charge in marking insecure page loads as "Not Secure". Today, this UI change has been pushed out to all Google Chrome users globally for all websites: any website loaded over HTTP will be marked as insecure.
That's not all though; Continue reading
James Feger Ditches CenturyLink for F5 Networks
 Adding Feger is the latest in a number of hires by F5 as it shifts its business model to prepare for 5G, IoT, and the cloud.
Adding Feger is the latest in a number of hires by F5 as it shifts its business model to prepare for 5G, IoT, and the cloud.
Cloudflare Access: Now teams of any size can turn off their VPN

Using a VPN is painful. Logging-in interrupts your workflow. You have to remember a separate set of credentials, which your administrator has to manage. The VPN slows you down when you're away from the office. Beyond just inconvenience, a VPN can pose a real security risk. A single infected device or malicious user can compromise your network once inside the perimeter.
In response, large enterprises have deployed expensive zero trust solutions. The name sounds counterintuitive - don’t we want to add trust to our network security? Zero trust refers to the default state of these tools. They trust no one; each request has to prove that itself. This architecture, most notably demonstrated at Google with Beyondcorp, has allowed teams to start to migrate to a more secure method of access control.
However, users of zero trust tools still suffer from the same latency problems they endured with old-school VPNs. Even worse, the price tag puts these tools out of reach for most teams.
Here at Cloudflare, we shared those same frustrations with VPNs. After evaluating our options, we realized we could build a better zero trust solution by leveraging some of the unique capabilities we have here at Cloudflare:
Our Continue reading
Gigamon Dives Deeper Into Security Space With Icebrg Acquisition
 Gigamon will combine its network traffic visibility capabilities with Icebrg’s security platform and allow SOC teams to deploy new security technologies as “security applications” on top of it.
Gigamon will combine its network traffic visibility capabilities with Icebrg’s security platform and allow SOC teams to deploy new security technologies as “security applications” on top of it.
Today, Chrome Takes Another Step Forward in Addressing the Design Flaw That is an Unencrypted Web

The following is a guest post by Troy Hunt, awarded Security expert, blogger, and Pluralsight author. He’s also the creator of the popular Have I been pwned?, the free aggregation service that helps the owners of over 5 billion accounts impacted by data breaches.
I still clearly remember my first foray onto the internet as a university student back in the mid 90's. It was a simpler online time back then, of course; we weren't doing our personal banking or our tax returns or handling our medical records so the whole premise of encrypting the transport layer wasn't exactly a high priority. In time, those services came along and so did the need to have some assurances about the confidentiality of the material we were sending around over other people's networks and computers. SSL as it was at the time was costly, but hey, banks and the like could absorb that given the nature of their businesses. However, at the time, there were all sorts of problems with the premise of serving traffic securely ranging from the cost of certs to the effort involved in obtaining and configuring them through to the performance hit on the Continue reading
IBM-Led Nabla Container Platform Touts Isolation for Its Security Posture
 The design differs from traditional Docker-based containers that allow for a host kernel to be shared by running containers, which leads to more interaction between the host and container pods.
The design differs from traditional Docker-based containers that allow for a host kernel to be shared by running containers, which leads to more interaction between the host and container pods.