Amazon, Google Vulnerable to Zip Slip, Says Snyk Security Research
 The security startup maintains a massive database of vulnerabilities in open source libraries.
The security startup maintains a massive database of vulnerabilities in open source libraries.
Integrating 3rd Party Firewalls with Amazon Web Services (AWS) VPC Networking
After figuring out how packet forwarding really works within AWS VPC (here’s an overview, the slide deck is already available to ipSpace.net subscribers) the next obvious question should be: “and how do I integrate a network services device like a next-generation firewall I have to use because $securityPolicy into that environment?”
Please don’t get me started on whether that makes sense, that’s a different discussion.
Christer Swartz, an old-time CCIE and occasional guest on Software Gone Wild podcast will show you how to do it with a Palo Alto firewall during my Amazon Web Services Networking Deep Dive workshop on June 13th in Zurich, Switzerland (register here).
Palo Alto Networks Replaces CEO With Former Google Exec Nikesh Arora
 The company wanted an accomplished business leader who has experience with large-scale platforms.
The company wanted an accomplished business leader who has experience with large-scale platforms.
Securing with NSX – Beyond the DevSecOps Paradigm
There are two digital explosions simultaneously happening in enterprises across all verticals. Enterprises are moving at a breakneck speed on every aspect of their business. From managing their supply-chain, making purchasing decisions, targeted marketing campaign to users, creating apps to connect with users and making it easier for users to consume their products.
The good news is technology is keeping pace and is a step ahead in helping the business achieve their goals. These business imperatives are forcing software iterations to be faster and be more efficient. This is leading to newer innovative models around people/processes/tools that we collectively call Continuous Integration(CI)/Continuous Development (CD). Teams leading the charge on CI/CD models are working in a “DevOps” model.
The second explosion is related to the first explosion. As complex software become easy-to-use and be ubiquitous, sophisticated tools can be used to attack enterprises. Managing Security is getting harder. Last decade – there was a belief – I am not going to be attacked. Fast forward today – enterprises expect to be attacked and breached. This is not just a baseless impression. Forrester’s 2018 survey shows that 66% of survey respondents have faced a major security incident.

”It’s kind Continue reading
VMware’s Future Is Networking, CEO Pat Gelsinger Says
 In addition to NSX, the company’s software-defined storage and hyperconverged products also saw strong growth during the first quarter of its fiscal 2019.
In addition to NSX, the company’s software-defined storage and hyperconverged products also saw strong growth during the first quarter of its fiscal 2019.
FBI Blames North Korea for Malware, Kaspersky Lawsuits Dismissed
 The two malware families target U.S. media, aerospace, financial, and critical infrastructure sectors’ networks.
The two malware families target U.S. media, aerospace, financial, and critical infrastructure sectors’ networks.
The First Lady’s bad cyber advice
First Lady Melania Trump announced a guide to help children go online safely. It has problems.Melania's guide is full of outdated, impractical, inappropriate, and redundant information. But that's allowed, because it relies upon moral authority: to be moral is to be secure, to be moral is to do what the government tells you. It matters less whether the advice is technically accurate, and more that you are supposed to do what authority tells you.
That's a problem, not just with her guide, but most cybersecurity advice in general. Our community gives out advice without putting much thought into it, because it doesn't need thought. You should do what we tell you, because being secure is your moral duty.
This post picks apart Melania's document. The purpose isn't to fine-tune her guide and make it better. Instead, the purpose is to demonstrate the idea of resting on moral authority instead of technical authority.
<-- --="" more="">
Strong Passwords
"Strong passwords" is the quintessential cybersecurity cliché that insecurity is due to some "weakness" (laziness, ignorance, greed, etc.) and the remedy is to be "strong".
The first flaw is that this advice is outdated. Ten years ago, important websites would frequently get hacked and Continue reading
APNIC Labs/CloudFlare DNS 1.1.1.1 Outage: Hijack or Mistake?
At 29-05-2018 08:09:45 UTC, BGPMon (A very well known BGP monitoring system to detect prefix hijacks, route leaks and instability) detected a possible BGP hijack of 1.1.1.0/24 prefix. Cloudflare Inc has been announcing this prefix from AS 13335 since 1st April 2018 after signing an initial 5-year research agreement with APNIC Research and Development (Labs) to offer DNS services.
Shanghai Anchang Network Security Technology Co., Ltd. (AS58879) started announcing 1.1.1.0/24 at 08:09:45 UTC, which is normally announced by Cloudflare (AS13335). The possible hijack lasted only for less than 2min. The last announcement of 1.1.1.0/24 was made at 08:10:27 UTC. The BGPlay screenshot of 1.1.1.0/24 is given below:

Anchang Network (AS58879) peers with China Telecom (AS4809), PCCW Global (AS3491), Cogent Communications (AS174), NTT America, Inc. (AS2914), LG DACOM Corporation (AS3786), KINX (AS9286) and Hurricane Electric LLC (AS6939). Unfortunately, Hurricane Electric (AS6939) allowed the announcement of 1.1.1.0/24 originating from Anchang Network (AS58879). Apparently, all other peers blocked this announcement. NTT (AS2914) and Cogent (AS174) are also MANRS Participants and actively filter prefixes.
Dan Goodin (Security Editor at Ars Technica, who extensively covers malware, computer espionage, botnets, and hardware hacking) reached Continue reading
French Hosting Provider Fends Off DDoS Attacks With NetScout vAPS
 As a hosting provider, Jaguar Networks has a higher risk of DDoS attacks because it aggregates its customers' risks in a shared infrastructure.
As a hosting provider, Jaguar Networks has a higher risk of DDoS attacks because it aggregates its customers' risks in a shared infrastructure.
New Features of Docker Enterprise Edition 2.0 – Top 12 Questions from the Docker Virtual Event
In the recent Docker Virtual Event, Unveiling Docker Enterprise Edition 2.0, we demonstrated some of the key new capabilities of the Docker Enterprise Edition – the enterprise-ready container platform that enables IT leaders to choose how to cost-effectively build and manage their entire application portfolio at their own pace, without fear of architecture and infrastructure lock-in. Designed to address enterprise customers’ needs, these net-new features extend across both Swarm and Kubernetes (Part 1 of this blog) and across Windows and Linux applications (Part 2 of this blog).
In this blog post, we’ll go over some of the most common questions about these new features as well as some of the common questions that were asked about how Docker Enterprise Edition is packaged and deployed.
If you missed the live event, don’t worry! You can still catch the recording on-demand here.
Docker Enterprise Edition 2.0 Features
Q: Can I connect my corporate directory to permissions inside Docker Enterprise Edition?
A: Yes! You can integrate your corporate LDAP or Active Directory to Docker Enterprise Edition. Permissions can be mapped to one of the 5 built-in roles or administrators can create very granular and flexible Continue reading
Extending the Power of NSX to Bare-metal Workloads
Authors – Sridhar Subramanian and Geoff Wilmington
VMware NSX Data Center was built with the goal of consistent networking and security services independent of changing application frameworks or physical infrastructure. In the last couple of years, NSX Data Center has focused on delivering network and security abstractions for applications on any compute platform. In our journey, we have handled VM’s, containers, cloud, and now we are also looking to help our customers with scenarios where they need a unified experience for bare-metal workloads. The goal being to maintain a consistent security experience regardless of location or platform the workload is running on.
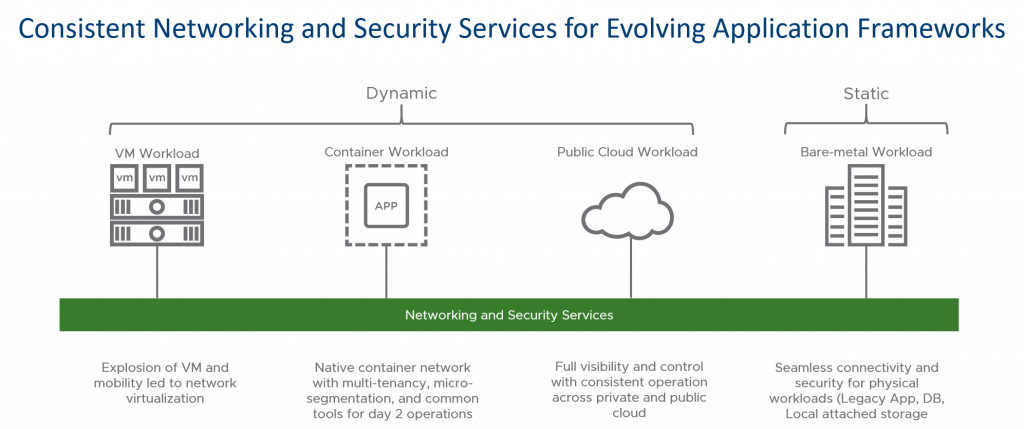
This experience means being able to take any workload, add it to an NSX Data Center Security Group and through the NSX Data Center Distributed Firewall have a consistent policy applied regardless of location and workload type. This consistent approach leverages the NSX DFW capabilities with stateful firewalling for the workloads. This is accomplished outside of using native OS capabilities like IP Tables or Windows Firewall so security admins only need to understand how to apply security through NSX DFW, and not have to understand the myriad of native OS approaches and complexity. By centralizing Continue reading
To Tackle the VPNFilter Botnet, It’s Going to Take Help from You and Me
If you’ve been reading the news lately, you might have seen headlines like “FBI to America: Reboot Your Routers, Right Now” or “F.B.I.’s Urgent Request: Reboot Your Router to Stop Russia-Linked Malware”. These headlines can be pretty alarming, and you may find yourself thinking, “things must be pretty bad if the FBI is putting out such an urgent warning.”
Cyber threats are not uncommon, but the good news is that the security community is working around the clock to tackle these threats as early and quickly as possible. Most of the time we do not see all this hard work, nor are we often asked to play a large part in taking down a botnet. But this time, by rebooting our routers, we can help the law enforcement and information security communities to identify infected routers so they can be cleaned up, moving us closer to a permanent fix for a particular kind of malware – VPNFilter.
Here is what happened …
From Discovery to Takedown
On 23 May, 2018, researchers at Cisco’s Talos publicly shared their findings about a large botnet of infected networking devices (home routers) they called “VPNFilter” because of concerns that the Continue reading
The Week in Internet News: The FBI Has Fewer Unopened Encrypted Devices Than Reported
Going dark with encryption: The U.S. FBI, for years now, has complained about its inability to access encrypted information held on the smartphones and other devices owned by criminal suspects. But the agency may have been overstating this so-called “going dark” problem, the Washington Post reported this week. A programming error at the FBI led the agency to report that it has seized about 7,800 mobile devices that it cannot open, but the actual number may be less than 2,000, the story says.
AI as Big Brother: Artificial intelligence is being used to track down criminals by combing through data faster than humans can, reports The Telegraph. The story features AI startup Senzing, an IBM spinoff. Meanwhile, the government of China is increasingly using AI to assist its Great Firewall program, says Internet of Business.
A bad year for security: This year is shaping up to be a terrible year for cybersecurity, due in part to poor Internet of Things security, reports Security Boulevard. In addition to the IoT concerns, 85 percent security executives surveyed worry their countries will experience a crucial infrastructure attack in the next five years.
Banking on blockchain and AI: Banks’ use of blockchain, AI, Continue reading
Large-scale analysis of style injection by relative path overwrite
Large-scale analysis of style injection by relative path overwrite Arshad et al., WWW’18
(If you don’t have ACM Digital Library access, the paper can be accessed either by following the link above directly from The Morning Paper blog site, or from the WWW 2018 proceedings page).
We’ve all been fairly well trained to have good awareness of cross-site scripting (XSS) attacks. Less obvious, and also less well known, is that a similar attack is possible using style sheet injection. A good name for these attacks might be SSS: same-site style attacks.
Even though style injection may appear less serious a threat than script injection, it has been shown that it enables a range of attacks, including secret exfiltration… Our work shows that around 9% of the sites in the Alexa top 10,000 contain at least one vulnerable page, out of which more than one third can be exploited.
I’m going to break today’s write-up down into four parts:
- How on earth do you do secret exfiltration with a stylesheet?
- Injecting stylesheet content using Relative Path Overwite (RPO)
- Finding RPO vulnerabilities in the wild
- How can you defend against RPO attacks?
Secret exfiltration via stylesheets
Style sheet injection Continue reading
Kip Compton’s Promotion Signals Bigger Cloud Strategy for Cisco
 The cloud touches all parts of Cisco’s business making this an important investment area for the company.
The cloud touches all parts of Cisco’s business making this an important investment area for the company.
Is There a Security Crisis in the Open Source Software Supply Chain?
 Following the Equifax breach, which exploited an open source framework library, many organizations increased their security postures, but that doesn't mean that open source is safe to use again.
Following the Equifax breach, which exploited an open source framework library, many organizations increased their security postures, but that doesn't mean that open source is safe to use again.
Nutanix CEO Talks ‘Sherlock’ Edge Platform, Blurred Lines Between Containers and VMs
 Sherlock, a cloud-based platform-as-a-service, will target IoT use cases and verticals including retail, manufacturing, health care, and oil and gas.
Sherlock, a cloud-based platform-as-a-service, will target IoT use cases and verticals including retail, manufacturing, health care, and oil and gas.
Fortinet Security Fabric Connectors Automate Management for Multi-Vendor Environments
 It does this through one-click integrations with partners including AWS, Cisco ACI, Google Cloud Platform, Microsoft Azure, and VMware NSX.
It does this through one-click integrations with partners including AWS, Cisco ACI, Google Cloud Platform, Microsoft Azure, and VMware NSX.
Podcast: Talking Data Privacy and GDPR with Todd M. Tolbert
“Let’s raise the bar on data privacy and make the Internet safer.” With the imminent arrival of the EU’s General Data Protection Regulation (GDPR), this was one of the points raised by Todd M. Tolbert, our Chief Administrative Officer, in an episode of the Non-Profit Tech Podcast published yesterday. Hosted by fusionSpan’s Justin Burniske, the 35-minute episode covered a wide range of topics, including:
- the difference between data privacy and data protection
- Todd’s thinking about the value the GDPR brings in terms of thinking about data
- mistakes organizations make with regard to handling their data
- resources for organizations to do more
- how you can’t be liable for data that you don’t have in the first place
- asking the question… do you really need to keep those 700 email addresses that no longer work?
And, of course, Todd being who he is, there were some Texan things mixed in to the conversation as well. I very much enjoyed the episode and found it a useful contribution to the ongoing privacy discussions that tomorrow’s GDPR deadline has generated.
Some of the resources Todd shared included:
- Online Trust Alliance’s Online Trust Audit and Honor Roll
- Online Trust Alliance’s Cyber Incident Continue reading