RIPE 76 Sees Strong Focus on Routing Security
The RIPE 76 meeting is happening this week in Marseille, France, held at the fantastic location of the Palais du Pharo overlooking Marseille’s Old Port. And it’s also another record attendance with over 850 people registered.
The first couple of days have primarily been devoted to plenary sessions, and there’s been a big focus on routing security. Erik Bais (A2B Internet) kicked off the discussion with a presentation on ‘Why are we still seeing DDoS traffic?‘, which highlighted that DDoS attacks are still originating from the same networks. Looking at the list of the worst offenders, there’s even one amongst the regular RIPE attendees, and he called for networks to clean up their acts. This was also a good opportunity to highlight the MANRS initiative, which of course includes measures to mitigate amplification attacks, and encourages networks to make good routing practices the norm.
Alexander Azimov (Qrator Labs) reinforced this message by outlining the current problems with BGP, including the ongoing route leaks and hijacks affecting the Internet. There are currently only moral obligations to not use other providers’ address space or to support anti-spoofing policies, yet major providers (including Tier 1 providers) continue to both originate Continue reading
Barracuda Drops Cloud-Delivered Web Application Firewall Service
 Verizon’s annual data breach report found web applications had the most breaches in 2017.
Verizon’s annual data breach report found web applications had the most breaches in 2017.
Why I’m Joining Cloudflare

I love working as a Chief Security Officer because every day centers around building something that makes people safer. Back in 2002, as I considered leaving my role as a cybercrime federal prosecutor to work in tech on e-commerce trust and safety, a mentor told me, “You have two rewarding but very different paths: you can prosecute one bad actor at a time, or you can try to build solutions that take away many bad actors' ability to do harm at all.” And while each is rewarding in its own way, my best days are those where I get to see harm prevented—at Internet scale.
In 2016, while traveling the United States to conduct hearings on the condition of Internet security as a member of President Obama's cyber commission, my co-commissioners noticed I had fallen into a pattern of asking the same question of every panelist: “Who is responsible for building a safer online environment where small businesses can set up shop without fear?” We heard many answers that all led to the same “not a through street” conclusion: Most law enforcement agencies extend their jurisdiction online, but there are no digital equivalents to the Department of Continue reading
Trump Axes Top Cybersecurity Role, Kaspersky Moves to Switzerland
 A new U.S. cybersecurity strategy calls on government agencies to work more closely with private sector companies to reduce risks.
A new U.S. cybersecurity strategy calls on government agencies to work more closely with private sector companies to reduce risks.
You get TLS 1.3! You get TLS 1.3! Everyone gets TLS 1.3!
It's no secret that Cloudflare has been a big proponent of TLS 1.3, the newest edition of the TLS protocol that improves both speed and security, since we have made it available to our customers starting in 2016. However, for the longest time TLS 1.3 has been a work-in-progress which meant that the feature was disabled by default in our customers’ dashboards, at least until all the kinks in the protocol could be resolved.
With the specification finally nearing its official publication, and after several years of work (as well as 28 draft versions), we are happy to announce that the TLS 1.3 feature on Cloudflare is out of beta and will be enabled by default for all new zones.

For our Free and Pro customers not much changes, they already had TLS 1.3 enabled by default from the start. We have also decided to disable the 0-RTT feature by default for these plans (it was previously enabled by default as well), due to its inherent security properties. It will still be possible to explicitly enable it from the dashboard or the API (more on 0-RTT soon-ish in another blog post).
Our Business and Continue reading
Cryptojacking Is the New Black, Cloud Security Reports Say
 One report found that 25 percent of organizations currently have illicit cryptomining activity in their cloud environments.
One report found that 25 percent of organizations currently have illicit cryptomining activity in their cloud environments.
ADVA Drives Cloud-Native Encryption Into ConnectGuard Platform
 The cloud-native update also bolsters the platform's ability to protect against the Spectre and Meltdown processor vulnerabilities.
The cloud-native update also bolsters the platform's ability to protect against the Spectre and Meltdown processor vulnerabilities.
Tap the Full Potential of Failsafe SD-WAN Q&A
 Thanks to all who joined us for the Talari Networks DemoFriday, Tap the Full Potential of Failsafe SD-WAN. During the webinar, Talari Networks demonstrated the latest innovations, product feature updates and UI enhancements to its award-winning SD-WAN platform. After the demo, we took questions from the audience. Below is the full Tap the Full Potential of Failsafe SD-WAN Q&A.
Thanks to all who joined us for the Talari Networks DemoFriday, Tap the Full Potential of Failsafe SD-WAN. During the webinar, Talari Networks demonstrated the latest innovations, product feature updates and UI enhancements to its award-winning SD-WAN platform. After the demo, we took questions from the audience. Below is the full Tap the Full Potential of Failsafe SD-WAN Q&A.
Will Intel White Box uCPE Pass Service Providers’ Taste Tests?
 A handful of OEMs are already building products based on the new reference architecture for uCPE.
A handful of OEMs are already building products based on the new reference architecture for uCPE.
Encryption Isn’t Perfect, That’s Why Choices Are Important
Encryption is a critical building block for online trust, but it’s never perfect. Any encryption you use is the product of many steps. Encryption methods have to be defined; protocols for implementation have to be specified; and then the protocols have to be implemented. Each step is handled by different people and potentially introduces vulnerabilities along the way. Even with the best lock design in the world, if someone builds the lock with variations in the design (either intentionally or accidentally), it might be easily picked.
When you own a broken lock, you have it fixed or use a different one – encryption is no different.
Yesterday (14 May 2018), the Internet security community was alerted to newly discovered vulnerabilities in the secure email ecosystem, dubbed “EFAIL”. EFAIL can make the content of emails encrypted with PGP and S/MIME readable to an attacker. While there are some fixes users and companies can make to mitigate EFAIL, cases like this underscore the importance of choice when it comes to secure communications.
How does the EFAIL attack work?
EFAIL abuses a combination of vulnerabilities in the OpenPGP and S/MIME specifications and the way that many email clients render remote content in Continue reading
Fortanix Scores Partnerships with IBM Cloud and Equinix, Encrypts Data in Use
 The encryption software only runs on Intel hardware now, but the startup isn’t ruling out support for other vendors in the future.
The encryption software only runs on Intel hardware now, but the startup isn’t ruling out support for other vendors in the future.
Research: Bridging the Air Gap
Way back in the old days, the unit I worked at in the US Air Force had a room with a lot of equipment used for processing classified information. Among this equipment was a Zenith Z-250 with an odd sort of keyboard and a very low resolution screen. A fine metal mesh embedded in a semi-clear substrate was glued to the surface of the monitor. This was our TEMPEST rated computer, on which we could type up classified memos, read classified email, and the like. We normally connected it to the STU-3 through a modem (remember those) to send and receive various kinds of classified information.
Elovici, Mordechai Guri, Yuval. “Bridgeware: The Air-Gap Malware.” Accessed May 13, 2018. https://cacm.acm.org/magazines/2018/4/226377-bridgeware/abstract.
The idea of TEMPEST begins way back in 1985, when a Dutch researcher demonstrated “reading” the screen of a computer using some relatively cheap, and easy to assemble, equipment, from several feet away. The paper I’m looking at today provides a good overview of the many ways which have been discovered since this initial demonstration to transfer data from one computer to another across what should be an “air gap.” For instance, the TEMPEST rated computer described Continue reading
End-to-End Segmentation with NSX SD-WAN and NSX Data Center
As you may have read earlier this month, NSX Data Center and NSX SD-WAN by VeloCloud are part of the expanded VMware NSX portfolio to enable virtual cloud networking. A Virtual Cloud Network provides end-to-end connectivity for applications and data, whether they reside in the data center, cloud or at the edge. I wanted to follow up, and walk through an example using NSX Data Center and NSX SD-WAN of how one could build an end to end segmentation model from the data center to the branch.
 NSX SD-WAN Segmentation
NSX SD-WAN Segmentation
Beyond lowering cost and increasing agility and simplicity of branch connectivity, one of the key values provided by NSX SD-WAN by VeloCloud is enterprise segmentation, which provides isolated network segments across the entire enterprise, enabling data isolation or separation by user or line of business, support for overlapping IP addresses between VLANs and support for multiple tenants. NSX SD-WAN provides this segmentation using a VRF-like concept with simplified, per-segment topology insertion. This is accomplished by inserting a “Segment ID” into the SD-WAN Overlay header as traffic is carried from one NSX SD-WAN Edge device to another Edge. Networks on the LAN-side of an NSX SD-WAN Edge with different Continue reading
Some notes on eFail
I've been busy trying to replicate the "eFail" PGP/SMIME bug. I thought I'd write up some notes.PGP and S/MIME encrypt emails, so that eavesdroppers can't read them. The bugs potentially allow eavesdroppers to take the encrypted emails they've captured and resend them to you, reformatted in a way that allows them to decrypt the messages.
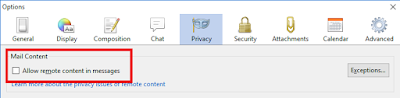
Disable remote/external content in email
The most important defense is to disable "external" or "remote" content from being automatically loaded. This is when HTML-formatted emails attempt to load images from remote websites. This happens legitimately when they want to display images, but not fill up the email with them. But most of the time this is illegitimate, they hide images on the webpage in order to track you with unique IDs and cookies. For example, this is the code at the end of an email from politician Bernie Sanders to his supporters. Notice the long random number assigned to track me, and the width/height of this image is set to one pixel, so you don't even see it:Such trackers are so pernicious they are disabled by default in most email clients. This is an example of the settings in Thunderbird:
The problem is Continue reading
Leaking securely, for White House staffers
Spencer Ackerman has this interesting story about a guy assigned to crack down on unauthorized White House leaks. It's necessarily light on technical details, so I thought I'd write up some guesses, either as a guide for future reporters asking questions, or for people who want to better know the risks when leak information.Symantec Cops to Internal Investigation, Sends Stock Crashing 35%
 The mysterious probe isn’t related to a breach or any security concern about its products.
The mysterious probe isn’t related to a breach or any security concern about its products.
Inaudible voice commands: the long-range attack and defense
Inaudible voice commands: the long-range attack and defense Roy et al., NSDI’18
Although you can’t hear them, I’m sure you heard about the inaudible ultrasound attacks on always-on voice-based systems such as Amazon Echo, Google Home, and Siri. This short video shows a ‘DolphinAttack’ in action:
To remain inaudible, the attack only works from close range (about 5ft). And it can work at up to about 10ft when partially audible. Things would get a whole lot more interesting if we could conduct inaudible attacks over a longer range. For example, getting all phones in a crowded area to start dialling your premium number, or targeting every device in an open plan office, or parking your car on the road and controlling all voice-enabled devices in the area. “Alexa, open my garage door…”. In today’s paper, Roy et al. show us how to significantly extend the range of inaudible voice command attacks. Their experiments are limited by the power of their amplifier, but succeed at up to 25ft (7.6m). Fortunately, the authors also demonstrate how we can construct software-only defences against the attacks.
We test our attack prototype with 984 commands to Amazon Echo and 200 commands to smartphones Continue reading
Protego Scores $2M in Seed Funds to Target Serverless Security
 A recent report found 21 percent of open source serverless projects contained at least one critical vulnerability or misconfiguration.
A recent report found 21 percent of open source serverless projects contained at least one critical vulnerability or misconfiguration.
Cycle Pedals Bare Metal Container Orchestrator as Kubernetes Alternative
 The barebones platform is available through Packet's bare metal compute, network, and storage resources.
The barebones platform is available through Packet's bare metal compute, network, and storage resources.


 NSX SD-WAN Segmentation
NSX SD-WAN Segmentation