Author Archives: networkingnerd
Author Archives: networkingnerd

One of the things I like to do in my twenty-eight minutes of spare time per week is play Battletech. It’s a table top wargame that involves big robots and lots of weapons. Some of them are familiar, like missiles and artillery. Because it’s science fiction there are also lasers and other crazy stuff. It’s a game of resource allocation. Can my ammunition last through this fight? You might be asking yourself “why not just carry lots of lasers?” After all, they don’t need ammo. Except the game designers thought of that too. Lasers produce heat. And heat, like ammunition, must be managed. Generate too much and you will shut down. Or boil your pilot alive in the cockpit. Rewind a thousand years and the modern network in a data center is facing a similar issue.
The average AI rack is expected to consume 600 kilowatts of power by next year. GPUs and CPUs are hungry beasts. They need to be fed as much power as possible in order to do whatever math makes AI happen. They have to come up with creative ways to cool those devices as well. We’re quickly reaching the Continue reading
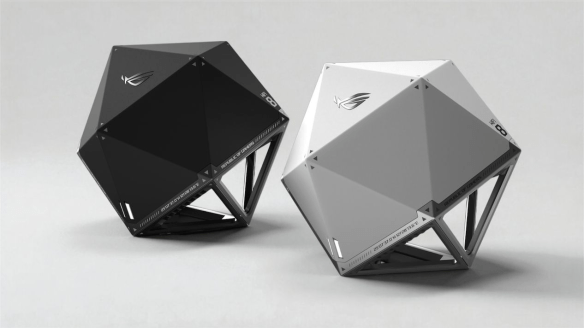
The ASUS ROG Wi-Fi 8 AP
Did you see the big news from CES? Wi-Fi 8 is here! Broadcom was talking about it. ASUS rolled out a d20 Wi-Fi 8 AP. MediaTek made sure they had one too. I guess I should probably take down all these Wi-FI 7 APs and just install the new stuff, right?
Before my favorite people start jumping out there to talk about how the newest iPhone and Samsung Galaxy phones are trash because they don’t support Wi-Fi 8, we need to make sure we’re all on the same page here. The standard behind the Wi-Fi 8 marketing term, 802.11bn, is a proposed working standard. It’s not finalized yet. It’s still in the draft phases, with final standards approval not expected until September 2028.
The focus of 802.11bn is not speed. It’s reliability. When you look at the way that vendors have been pushing more and more throughput for the past several revisions you might ask yourself how much faster things could get. For the eighth release of the Wi-Fi standard the answer is “not any faster.” Wi-Fi 8 is keeping the same speed numbers that Wi-Fi 7 Continue reading

Hey everyone. It’s January 1 again, which means it’s time for me to own up to the fact that I wrote five posts in 2025. Two of those were about AI. Not surprising given that everyone was talking about it. But that seemed to be all I was talking about. What else was I doing instead?

The IT world is on fire right now with solutions to every major problem we’ve ever had. Wouldn’t you know it that the solution appears to be something that people are very intent on selling to you? Where have I heard that before? You wouldn’t know it looking at the landscape of IT right now but AI has iterated more times than you can think over the last couple of years. While people are still carrying on about LLMs and writing homework essays the market has moved on to agentic solutions that act like employees doing things all over the place.
The result is people are more excited about the potential for AI than ever. Well, that is if you’re someone that has problems that need to be solved. If you’re someone doing something creative, like making art or music or poetry you’re worried about what AI is going to do to your profession. That divide is what I’ve been thinking about for a while. I don’t think it should come as a shock to anyone but I’ve figured out why AI is hot for every executive out there.
AI appeals to people that have someone doing work for them.

I have a little confession. Sometimes I like to go into Best Buy and just listen. I pretend to be shopping or modem bearings or a left handed torque wrench. What I’m really doing is hearing how people sell computers. I remember when 8x CD burners were all the rage. I recall picking one particular machine because it had an integrated Sound Blaster card. Today, I just marvel at how the associates rattle off a long string of impressive sounding nonsense that consumers will either buy hook, line, and sinker or refute based on some Youtube reviewer recommendation. Every once in a while, though, I hear someone that actually does understand the lingo and it is wonderful. They listen and understand the challenges and don’t sell a $3,000 gaming computer to a grandmother just to play Candy Crush and look up grandkid photos on Facebook.
What does that story have to do with the title of this post? Well, dear young readers, you may not remember the time when Best Buy Blue was locked in mortal competition with Circuit City Red. In a time before Amazon was ascendant you had to pick between the two giants of Continue reading

You may recall from my post about Cisco Live last year that I talked about legacy and passing the torch to a new generation of people being active at the event. It was a moment where I was happy for what was occurring and thrilled to see the continuation of the community. It’s now a year later and I have a very different outlook on Cisco Live that isn’t nearly as rosy. Which is why I asked the question in the post title.
If you are a Cisco customer or partner that wants the latest news about Cisco products and services then Cisco Live is the place you need to be to get them. Sure, you can watch the keynotes virtually and read all the press releases online. However, if you really want to get up close and personal with the technology you have to be there. After all, it was this need to be in-person that inspired our community in the first place. We showed up. We met up. And we made the event even better because we were there.
That was then. 2025 is a different story. The first hints about the situation came when I Continue reading

Photo by Pixabay on Pexels.com
We’ve all been in a situation where we’re listening to a presentation or in a class where someone is sharing knowledge. The presenter or expert finishes a point and stops to take a breath or move on to the next point when you hear a voice.
“What they meant to say was…”
You can already picture the person doing it. I don’t need to describe the kind of person that does this. We all know who it is and, if you’re like me, it drives you crazy. I know it because I’ve found myself being that person several times and it’s something I’m working hard to fix.
People that want to chime in feel like they have important things to share. Maybe they know something deeper about the subject. Perhaps they’ve worked on a technology and have additional information to add to the discussion. They mean well. They’re eager to add to the discussion. They mean well. Most of the time.
What about the other times? Maybe it’s someone that thinks they’re smarter than the presenter. I know I’ve had to deal with that plenty of times. It could be an Continue reading

2024 was a year of being busy. You probably noticed as a loyal reader because my output on this blog fell off quite a bit. I wanted to get back on track per my New Year’s Day post. How did I do? Sixteen posts for the whole year. Barely more than one a month.
That doesn’t mean I wasn’t busy. I have been working hard to bring great Tech Field Day events to the community. I’ve become more active on BlueSky as the community shifts there due to the craziness happening on Twitter/X. I have been getting more and more briefings on technology, which I’ve been writing up on LinkedIn. And of course I’ve been active on the Gestalt IT Rundown and the Tech Field Day Podcast
I also ran almost every day in 2024. I mentioned on Facebook that “consistency beats quantity”, which was a phrase that encouraged me to try and run at least one mile a day in 2024. That ended up being 901 miles of running for the year, with November and December having a LOT or running. I plan on keeping that going in 2025, where I’m aiming for 1,000 miles. It will be a Continue reading

No doubt you’ve seen the news that Intel has parted ways with Pat Gelsinger. There is a lot of info to unpack on that particular story but we did a good job of covering it on the Rundown this week. What I really wanted to talk about was a quote that I brought up in the episode that I heard from my friend Michael Bushong a couple of months ago:
No one cuts their way back into relevance.
It’s been rattling around in my head for a while and I wanted to talk about why he’s absolutely right.
Do you remember the coupon clipping craze of ten years ago? I think it started from some show on TLC about people that were ultra crazy couponers. They would do the math and they could buy like 100 lbs of rice for $2. They would stock up on a year’s worth of toothpaste at a time because you could pay next to nothing for it. However, the trend died out after a year or so. In part, that was because the show wasn’t very exciting after the shock of buying two years of hand soap wore off. The other Continue reading
One of the things that I’ve noticed about the rise of AI is that everything feels so wordy now. I’m sure it’s a byproduct of the popularity of ChatGPT and other LLMs that are designed for language. You’ve likely seen it too on websites that have paragraphs of text that feel unnecessary. Maybe you’re looking for an answer to a specific question. You could be trying to find a recipe or even a code block for a problem. What you find is a wall of text that feels pieced together by someone that doesn’t know how to write.
I feel like the biggest issue with those overly word-filled answers comes down to the way that people feel about unnecessary exposition. AI is built to write things on a topic and fill out word count. Much like a student trying to pad out the page length for a required report, AI doesn’t know when to shut up. It specifically adds words that aren’t really required. I realize that there are modes of AI content creation that value being concise but those are the default.
I use AI quite a bit to summarize long articles, many of which Continue reading

By now I’m sure you’re familiar with Murphy’s Law: “Anything that can go wrong will go wrong.” If you work in IT or events or even in a trade you’ve seen things go upside down on many occasions. Did you ever ask yourself why this happens? Or even what you can do to fix it? What about avoiding it completely?
I have done a lot in IT over the years. I’ve also been working hard as an event planner and coordinator with Tech Field Day. The best lessons that I’ve learned about anticipating disaster have come from my time in Scouting. I’m often asked by companies “how did you know that would happen?” I almost always answer the same way: “I didn’t know THAT would go wrong, but I knew something would. I just kept my eye out for it.” It almost sounds too simple, right? But if you are familiar with event planning you know it’s almost a law, just like Mr. Murphy’s famous version.
How can you anticipate problems and still manage to make things happen? You can’t always fix everything. However, you can make sure that people don’t notice the issues. You just have Continue reading

I once again loved this episode of the Art of Network Engineering featuring Mike Bushong. He is a very astute judge of character as well as how to apply social skills to your tech role. Definitely listen to the above episode if you’re interested in countering cognitive biases.
In the episode, he told a great story of how he had a pivotal career moment with one of his managers that led to some important introspection. I won’t tell his story but the summary is that he had taken on way too much work and way too many roles and he blew up at his manager because of the stress. She leveled him with a quote that rang true for me:
“No one knows everything you’re working on. They just see that the thing that’s important to them is late.”
That’s not the verbatim quote but that’s how I remember it. It’s definitely something that I’ve been thinking about since the previous episode when he mentioned it the first time.
The odds are good that we’re all doing way too many things right now. Whether it’s doing more work in our role or taking on way Continue reading

Recently at Networking Field Day, one of the presenters for cPacket had a wonderful line that stuck with me:
There’s no compression algorithm for experience.
Like, floored. Because it hits at the heart of a couple of different things that are going on in the IT industry right now that showcase why it feels like everything is on the verge of falling apart and what we can do to help that.
Let’s just get this out of the way: you are going to screw up. Anyone doing any job ever for any amount of time has made a mistake. I know I’ve made my fair share of them over the years. When I finished chastising myself I looked back at what happened, figured out what went wrong, and made sure that it didn’t happen that exact same way again. That’s experience.
Experience is key to understanding why we do things the way we do them or why we don’t do something a certain way. You know how you get experience? By doing it. It’s rare that someone can read a book or a blog post about some topic and instantly know everything there is to know about Continue reading

Good morning! How are you?
I’d like to talk about keynotes, again. You know, one of my favorite subjects. I’ve been watching them intently for the past few years just hoping that we’re going to see something different. As a technical analyst and practitioner I love to see and hear the details behind the technology that drive the way our IT companies develop. Yet every year I feel more and more disappointed by the way that keynotes take everything and push it into the stratosphere to get an 80,000 foot view of the technology. It’s almost like the keynotes aren’t written for practitioners. Why? The answer lies in the statement at the top of this post.
When most people ask someone how their day is going they’re not actually looking for a real response. They most certainly aren’t asking for details on how exactly the person’s day is going. They’re usually looking for one of two things:
Any more than that drags someone down into a conversation that they don’t want to have. Asking someone about their day is a polite way of acknowledging them and making a bit of small Continue reading

Legacy: Something transmitted by or received from an ancestor or predecessor or from the past. — Merriam-Webster
Cisco Live 2024 is in the books. I could recap all the announcements but that would take forever. You can find an AI that can summarize them for you much faster. That’s because AI was the largest aspect of what was discussed. Love it or hate it, AI has taken over the IT industry for the time being. More importantly it has also focused companies on the need to integrate AI functions into their product lines to avoid being left behind by upstarts.
That’s what you see in the headlines. Something I noticed while I was there was how the march of time has affected us all. After eighteen years I finally realized the sessions today have less in common with the ones I was attending back in 2010 than ever before. Development and advanced features configuration have replaced the tuning of routing protocols and CallManager deployment tips. It’s a game for younger engineers that have less to unlearn from the legacy technologies I’ve spent my career working on.
But legacy is a word with more than one definition. It’s Continue reading

I once heard a quote that said, “The hardest part of being a butcher is knowing where to cut.” If you’ve ever eaten a cut of meat you know that the difference between a tender steak and a piece of meat that needs hours of tenderizing is just inches apart. Butchers train for years to be able to make the right cuts in the right pieces of meat with speed and precision. There’s even an excellent Medium article about the dying art of butchering.
One thing that struck me in that article is how the art of butchering relates to AI. Yes, I know it’s a bit corny and not an easy segue into a technical topic but that transition is about as subtle as the way AI has come crashing through the door to take over every facet of our lives. It used to be that AI was some sci-fi term we used to describe intelligence emerging in computer systems. Now, AI is optimizing my PC searches and helping with image editing and creation. It’s easy, right?
Except some of those things that AI promises to excel at doing are things that professionals have spent years honing their Continue reading

I saw a recent post on LinkedIn from Alex Henthorn-Iwane that gave me pause. He was talking about how nearly 2/3rds of Github projects are maintained by one or two people. He also quoted some statistics around how projects are maintained by volunteers and unpaid members as opposed to more institutional support from people getting paid to do the work. It made me reflect on my own volunteering journey and how the parallels between open source and other organizations aren’t so different after all.
Most of my readers know that one of my passion projects outside of Tech Field Day and this humble blog is the involvement of my children in Scouting. I spend a lot of my free time volunteering as a leader and organizer for various groups. I get to touch grass quite often. At least I do when I’m not stuck in meetings or approving paperwork.
One of the things that struck me in Alex’s post was how he talked about the lack of incoming talent to help with projects as older maintainers are aging out. We face a similar problem in scouting. Rather than our volunteers getting too old to do the Continue reading

I’ve noticed a trend recently with a lot of AI-related features being added to software. They’re being branded as “copilot” solutions. Yes, Microsoft Copilot was the first to use the name and the rest are just trying to jump in on the brand recognition, much like using “GPT” last year. The word “copilot” is so generic that it’s unlikely to be to be trademarked without adding more, like the company name or some other unique term. That made me wonder if the goal of using that term was simply to cash in on brand recognition or if there was more to it.
Did you know that an airplane can land entirely unassisted? It’s true. It’s a feature commonly called Auto Land and it does exactly what it says. It uses the airports Instrument Landing System (ILS) to land automatically. Pilots rarely use it because of a variety of factors, including the need for minute last-minute adjustments during a very stressful part of the flight as well as the equipment requirements, such as a fairly modern ILS system. That doesn’t even mention that use of Auto Land snarls airport traffic because of the need to hold other planes outside Continue reading

If you grew up in the 80s watching movies like me, you’ll remember Wargames. I could spend hours lauding this movie but for the purpose of this post I want to call out the sequence at the beginning when the two airmen are trying to operate the nuclear missile launch computer. It requires the use of two keys, one each in the possession of one of the airmen. They must be inserted into two different locks located more than ten feet from each other. The reason is that launching the missile requires two people to agree to do something at the same time. The two key scene appears in a number of movies as a way to show that so much power needs to have controls.
However, one thing I wanted to talk about in this post is the notion that those controls need to be visible to be effective. The two key solution is pretty visible. You carry a key with you but you can also see the locks that are situated apart from each other. There is a bit of challenge in getting the keys into the locks and turning them simultaneously. That not only shows that the Continue reading

I’ve taken a number of briefings in the last few months that all mention how companies are starting to get into AI by building an AI virtual assistant. In theory this is the easiest entry point into the technology. Your network already has a ton of information about usage patterns and trouble spots. Network operations and engineering teams have learned over the years to read that information and provide analysis and feedback.
If marketing is to be believed, no one in the modern world has time to learn how to read all that data. Instead, AI provides a natural language way to ask simple questions and have the system provide the data back to you with proper context. It will highlight areas of concern and help you grasp what’s going on. Only you don’t need to get a CCNA to get there. Or, more likely, it’s more useful for someone on the executive team to ask questions and get answers without the need to talk to the network team.
I have some questions that I always like to ask when companies start telling me about their new AI assistant that help me understand how it’s being built.