Response: Certifications Are Not A Big Deal. Stop Being a Princess About It.

Toothy McGrin left a comment after I talked how little effort is required to acheive a vendor certification. Its a hot topic. Here is the discussion, its about 2 minutes in. CCNA/CCNP may not be a big deal in the circles you travel in, but for a lot of employees and employers they […]
The post Response: Certifications Are Not A Big Deal. Stop Being a Princess About It. appeared first on EtherealMind.
Video: Ergonomics Expert Explains How to Set Up Your Desk – WSJ

I have the impression that I ‘know’ most of this but a refresher put it back to top of mind.
The post Video: Ergonomics Expert Explains How to Set Up Your Desk – WSJ appeared first on EtherealMind.
Incident response
The post Incident response appeared first on Noction.
Announcing news.internetsociety.org – a way to follow what is published across all Internet Society sites
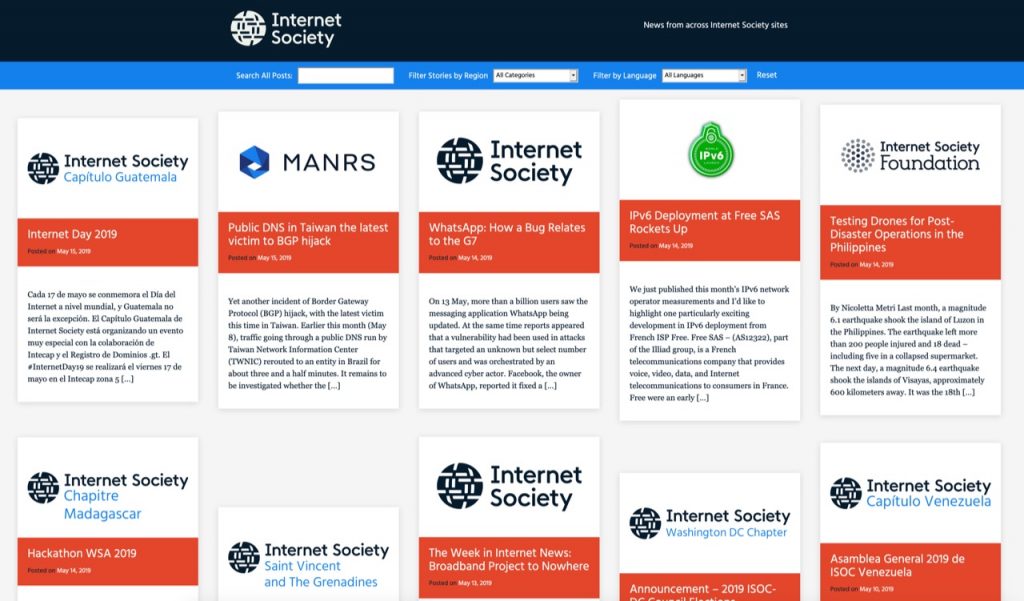
Today I’m pleased to announce a new site we have built that brings into one location links to all the content published across Internet Society websites:
This news site aggregates posts from our main website, from sites of our 130+ Chapters and Special Interest Groups (SIGs), and from certain other affiliated sites. On the site, you can:
- Search using keywords
- Filter the view based on the region
- Filter the view based on language
- Filter the view to see posts only from a specific source
For instance, you can see all the posts published by Chapters in Africa. Or you can see all the posts published in French, or Spanish, or Chinese… or Georgian.
Note that the filters can work together. By choosing “Africa” and “French” you will see only French posts from African Chapters. There’s a “Reset” link on the right side that will clear all the filters.
All the views also have unique URLs that you can share with people, or link to from other sites, email newsletters, etc. And of course the site has a master RSS feed that you can read in a RSS reader or other tool.
I find it quite Continue reading
Deeper Connection with the Local Tech Community in India

On June 6th 2019, Cloudflare hosted the first ever customer event in a beautiful and green district of Bangalore, India. More than 60 people, including executives, developers, engineers, and even university students, have attended the half day forum.

The forum kicked off with a series of presentations on the current DDoS landscape, the cyber security trends, the Serverless computing and Cloudflare’s Workers. Trey Quinn, Cloudflare Global Head of Solution Engineering, gave a brief introduction on the evolution of edge computing.

We also invited business and thought leaders across various industries to share their insights and best practices on cyber security and performance strategy. Some of the keynote and penal sessions included live demos from our customers.

At this event, the guests had gained first-hand knowledge on the latest technology. They also learned some insider tactics that will help them to protect their business, to accelerate the performance and to identify the quick-wins in a complex internet environment.

To conclude the event, we arrange some dinner for the guests to network and to enjoy a cool summer night.

Through this event, Cloudflare has strengthened the connection with the local tech community. The success of the event cannot be separated from the Continue reading
Deeper Connection with the Local Tech Community in India

On June 6th 2019, Cloudflare hosted the first ever customer event in a beautiful and green district of Bangalore, India. More than 60 people, including executives, developers, engineers, and even university students, have attended the half day forum.

The forum kicked off with a series of presentations on the current DDoS landscape, the cyber security trends, the Serverless computing and Cloudflare’s Workers. Trey Quinn, Cloudflare Global Head of Solution Engineering, gave a brief introduction on the evolution of edge computing.

We also invited business and thought leaders across various industries to share their insights and best practices on cyber security and performance strategy. Some of the keynote and penal sessions included live demos from our customers.

At this event, the guests had gained first-hand knowledge on the latest technology. They also learned some insider tactics that will help them to protect their business, to accelerate the performance and to identify the quick-wins in a complex internet environment.

To conclude the event, we arrange some dinner for the guests to network and to enjoy a cool summer night.

Through this event, Cloudflare has strengthened the connection with the local tech community. The success of the event cannot be separated from the Continue reading
We Are on a Break ;)
It’s high time for another summer break (I get closer and closer to burnout every year - either I’m working too hard or I’m getting older ;).
Of course we’ll do our best to reply to support (and sales ;) requests, but it might take us a bit longer than usual. I will publish an occasional worth reading or watch out blog post, but don’t expect anything deeply technical for the new two months.
We’ll be back (hopefully refreshed and with tons of new content) in early September, starting with network automation course on September 3rd and VMware NSX workshop on September 10th.
In the meantime, try to get away from work (hint: automating stuff sometimes helps ;), turn off the Internet, and enjoy a few days in your favorite spot with your loved ones!
Get Cloudflare insights in your preferred analytics provider
Today, we’re excited to announce our partnerships with Chronicle Security, Datadog, Elastic, Looker, Splunk, and Sumo Logic to make it easy for our customers to analyze Cloudflare logs and metrics using their analytics provider of choice. In a joint effort, we have developed pre-built dashboards that are available as a Cloudflare App in each partner’s platform. These dashboards help customers better understand events and trends from their websites and applications on our network.

|

|

|

|
|
|
Cloudflare insights in the tools you're already using
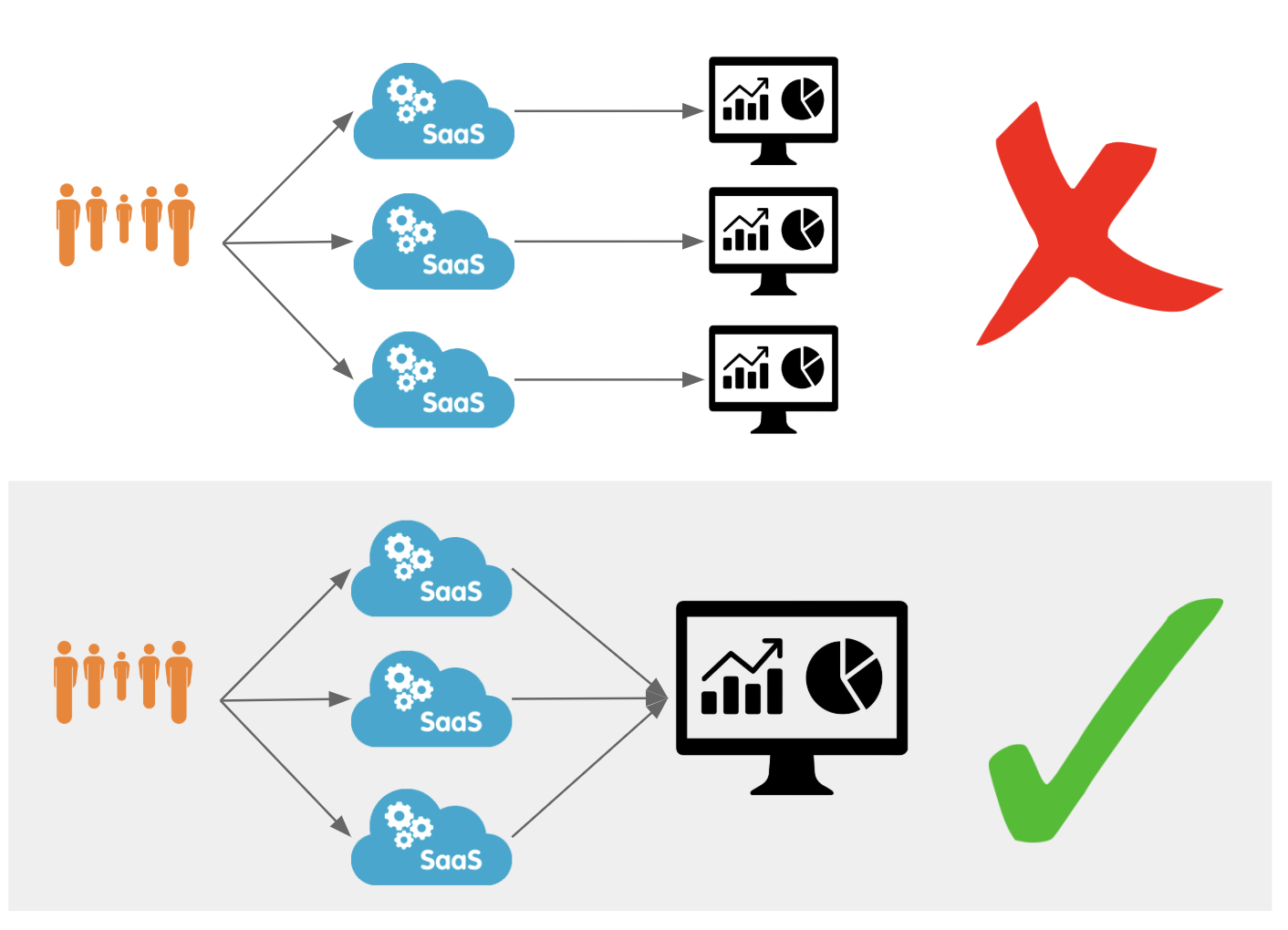
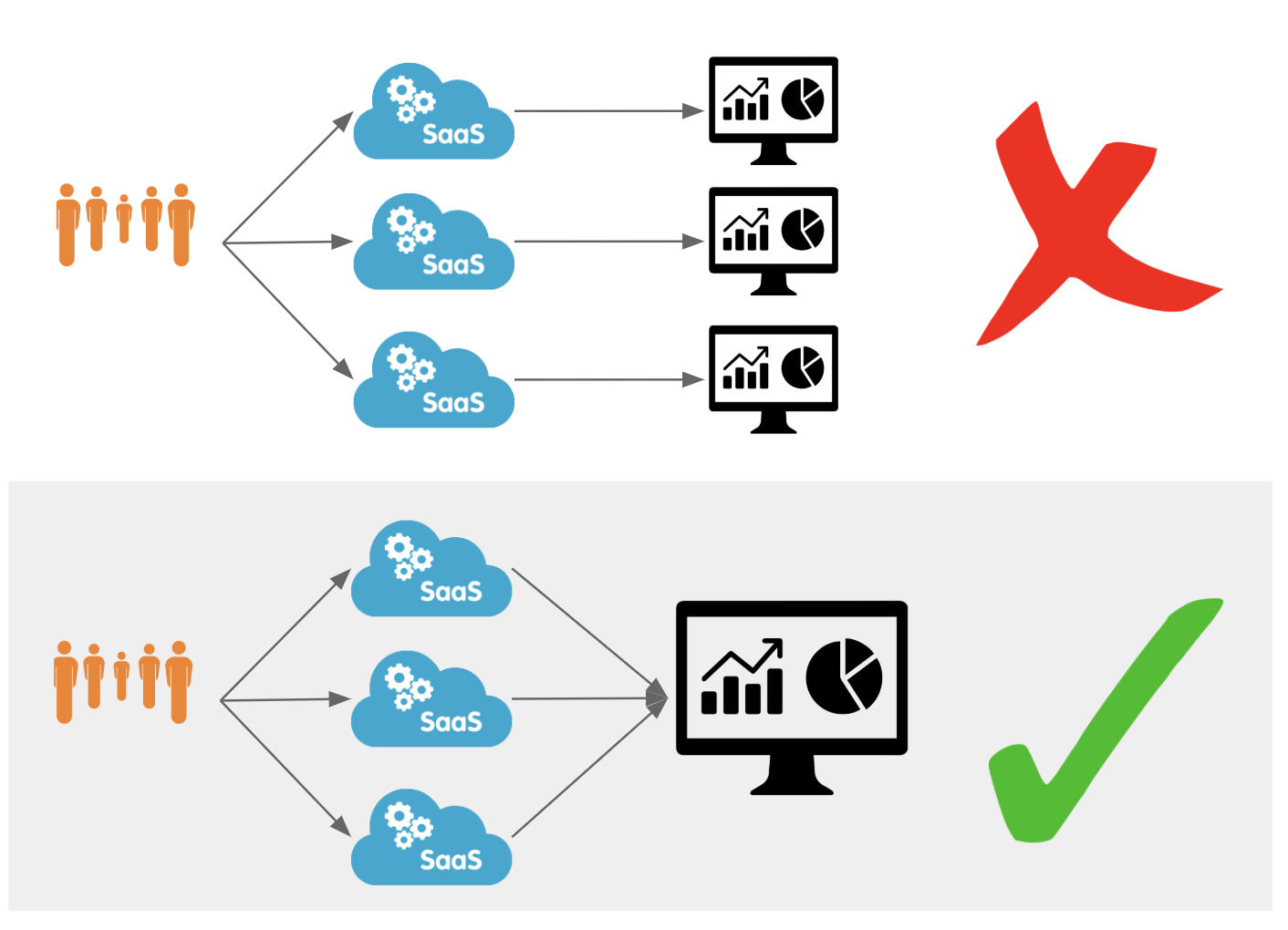
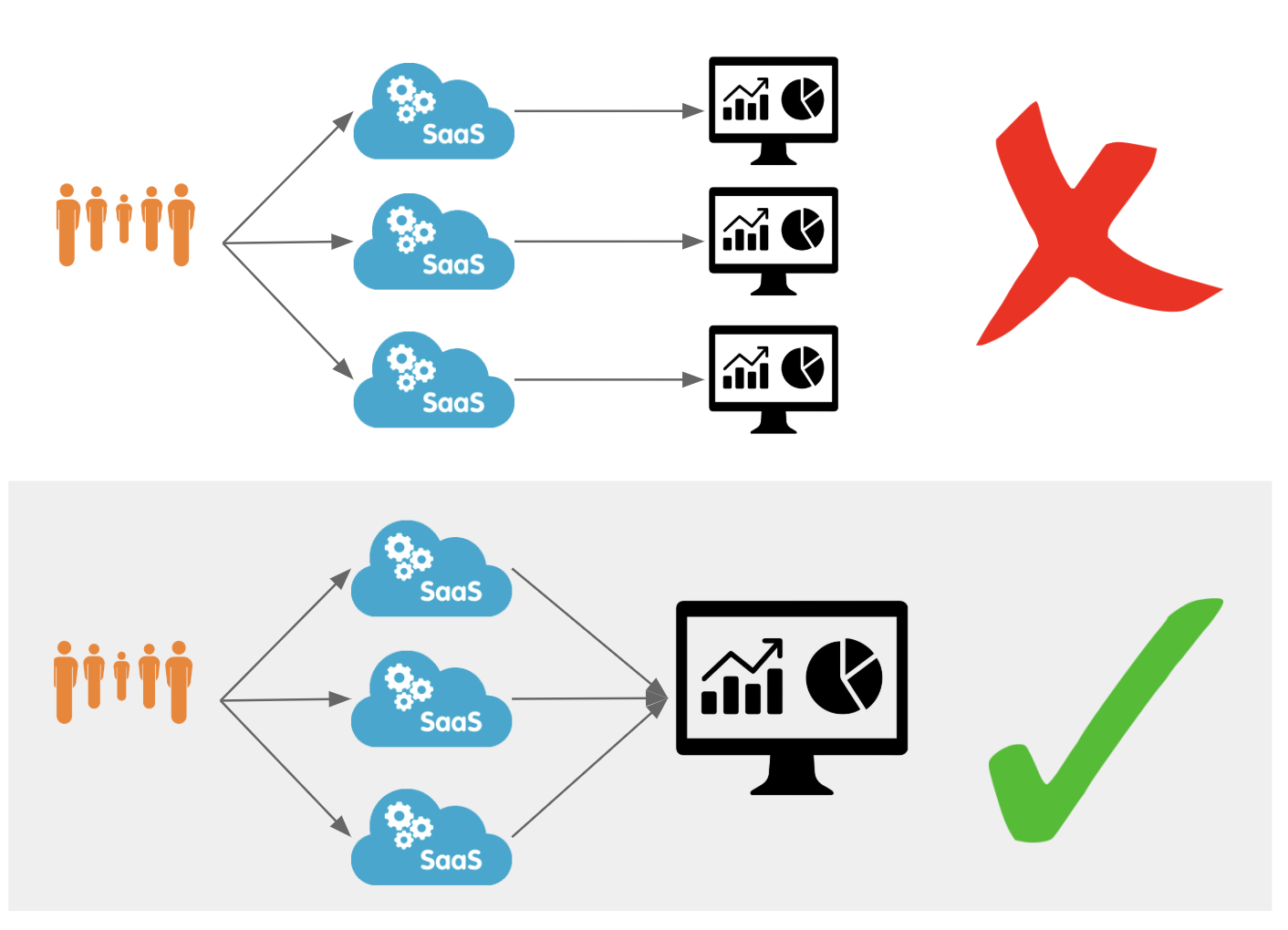
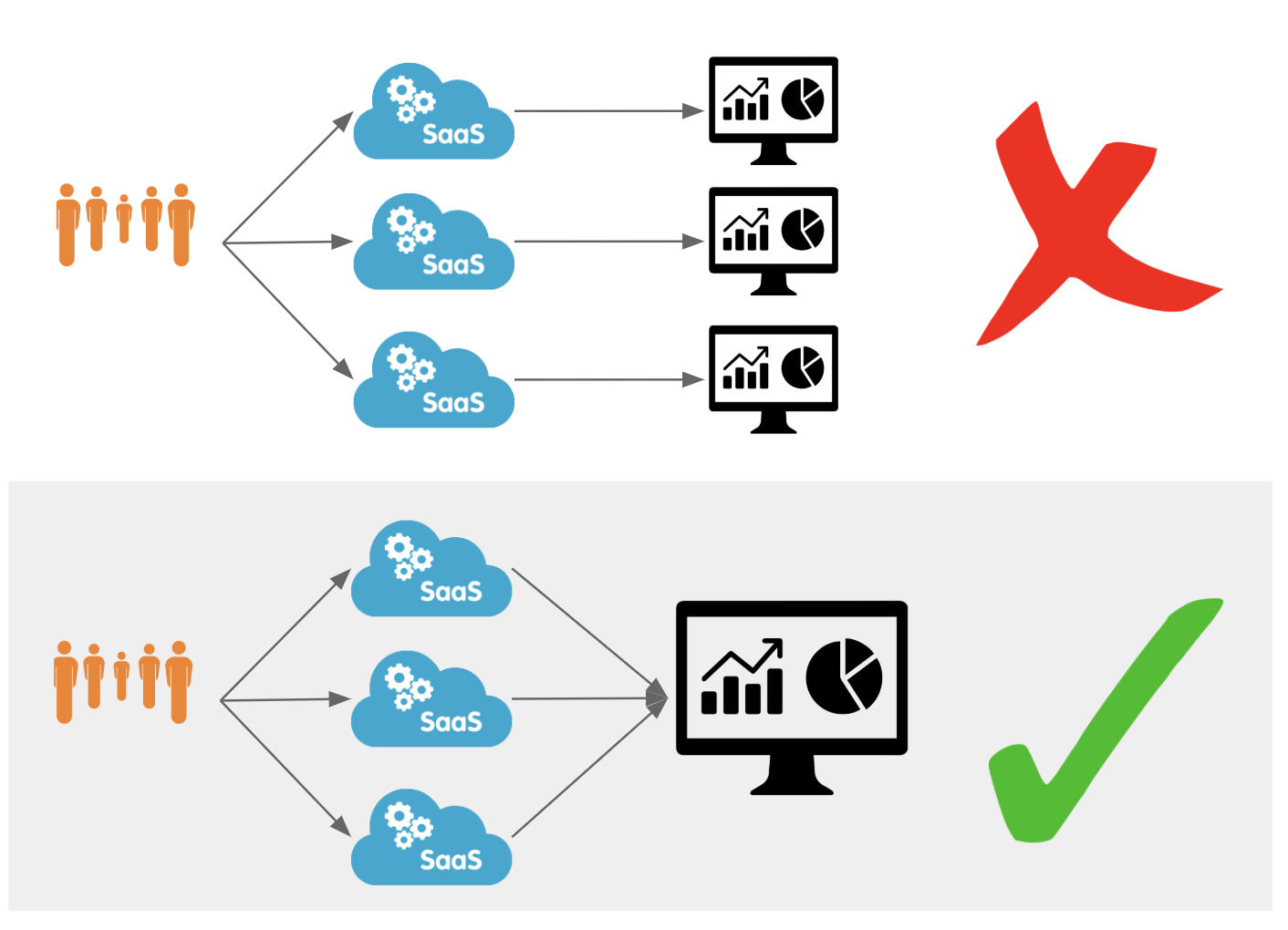
Data analytics is a frequent theme in conversations with Cloudflare customers. Our customers want to understand how Cloudflare speeds up their websites and saves them bandwidth, ranks their fastest and slowest pages, and be alerted if they are under attack. While providing insights is a core tenet of Cloudflare's offering, the data analytics market has matured and many of our customers have started using third-party providers to analyze data—including Cloudflare logs and metrics. By aggregating data from multiple applications, infrastructure, and cloud platforms in one dedicated analytics platform, customers can create a single pane of glass and benefit from better end-to-end visibility over their entire stack.
While these analytics Continue reading
Get Cloudflare insights in your preferred analytics provider
Today, we’re excited to announce our partnerships with Chronicle Security, Datadog, Elastic, Looker, Splunk, and Sumo Logic to make it easy for our customers to analyze Cloudflare logs and metrics using their analytics provider of choice. In a joint effort, we have developed pre-built dashboards that are available as a Cloudflare App in each partner’s platform. These dashboards help customers better understand events and trends from their websites and applications on our network.

|

|

|

|
|
|
Cloudflare insights in the tools you're already using
Data analytics is a frequent theme in conversations with Cloudflare customers. Our customers want to understand how Cloudflare speeds up their websites and saves them bandwidth, ranks their fastest and slowest pages, and be alerted if they are under attack. While providing insights is a core tenet of Cloudflare's offering, the data analytics market has matured and many of our customers have started using third-party providers to analyze data—including Cloudflare logs and metrics. By aggregating data from multiple applications, infrastructure, and cloud platforms in one dedicated analytics platform, customers can create a single pane of glass and benefit from better end-to-end visibility over their entire stack.
While these analytics Continue reading
Applying Essentialism to certifications and skills development in the Tech Industry
We often compare ourselves to others around us. We are impressed with the skills others possess, the content others produce, the appearances others maintain, the successes others have achieved, the feats others have conquered. This constant comparison can lead to melancholic states of ambivalence, and sometimes depression due to the artificial expectations of who we […]
The post Applying Essentialism to certifications and skills development in the Tech Industry appeared first on Overlaid.
The Serverlist: Serverless makes a splash at JSConf EU and JSConf Asia

Check out our sixth edition of The Serverlist below. Get the latest scoop on the serverless space, get your hands dirty with new developer tutorials, engage in conversations with other serverless developers, and find upcoming meetups and conferences to attend.
Sign up below to have The Serverlist sent directly to your mailbox.
The Serverlist: Serverless makes a splash at JSConf EU and JSConf Asia

Check out our sixth edition of The Serverlist below. Get the latest scoop on the serverless space, get your hands dirty with new developer tutorials, engage in conversations with other serverless developers, and find upcoming meetups and conferences to attend.
Sign up below to have The Serverlist sent directly to your mailbox.