Loggly
 Loggly is a cloud logging and and analysis platform. This article will demonstrate how to integrate network events generated from industry standard sFlow instrumentation build into network switches.
Loggly is a cloud logging and and analysis platform. This article will demonstrate how to integrate network events generated from industry standard sFlow instrumentation build into network switches.Loggly offers a free 14 day evaluation, so you can try this example at no cost.ICMP unreachable describes how monitoring ICMP destination unreachable messages can help identify misconfigured hosts and scanning behavior. The article uses the sFlow-RT real-time analytics software to process the raw sFlow and report on unreachable messages.
The following script, loggly.js, modifies the sFlow-RT script from the article to send events to the Loggly HTTP/S Event Endpoint:
var token = 'xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx';Some notes on the script:
var url = 'https://logs-01.loggly.com/inputs/'+token+'/tag/http/';
var keys = [
'icmpunreachablenet',
'icmpunreachablehost',
'icmpunreachableprotocol',
'icmpunreachableport'
];
for (var i = 0; i < keys.length; i++) {
var key = keys[i];
setFlow(key, {
keys:'macsource,ipsource,macdestination,ipdestination,' + key,
value:'frames',
log:true,
flowStart:true
});
}
setFlowHandler(function(rec) {
var keys = rec.flowKeys.split(',');
var msg = {
flow_type:rec.name,
src_mac:keys[0],
src_ip:keys[1],
dst_mac:keys[2],
dst_ip:keys[3],
unreachable:keys[4]
};
try { http(url,'post','application/json',JSON.stringify(msg)); }
catch(e) { logWarning(e); };
}, keys);
- Modify the script to use the correct token for your Loggly account.
- Including MAC addresses can help identify Continue reading
NTT Security Acquires Application Security Provider WhiteHat Security
 Founded by former Yahoo security officer Jeremiah Grossman, WhiteHat takes a DevSecOpps approach to...
Founded by former Yahoo security officer Jeremiah Grossman, WhiteHat takes a DevSecOpps approach to...
SSH Compromise Detection Using Flow Data
The post SSH Compromise Detection Using Flow Data appeared first on Noction.
Anyone Using Intel Omni-Path?
One of my subscribers sent me this question after watching the latest batch of Data Center Fabrics videos:
You haven’t mentioned Intel's Omni-Path at all. Should I be surprised?
While Omni-Path looks like a cool technology (at least at the whitepaper level), nobody ever mentioned it (or Intel) in any data center switching discussion I was involved in.
Read more ...Citrix Leans In on Automation to Secure Its SD-WAN
 One of the ways that Citrix has bolstered its security and automation is through an integration...
One of the ways that Citrix has bolstered its security and automation is through an integration...
Stopping Drupal’s SA-CORE-2019-003 Vulnerability
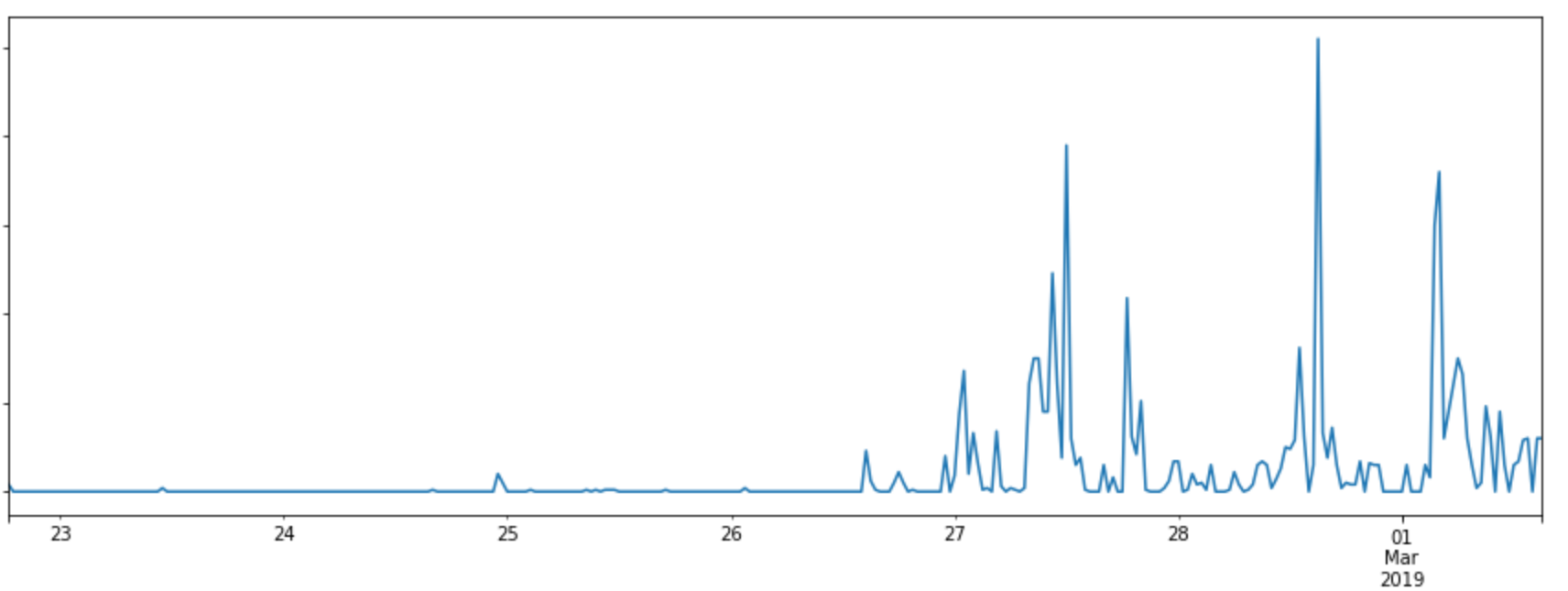
On the 20th February 2019, Drupal announced that they had discovered a severe vulnerability and that they would be releasing a patch for it the next day. Drupal is a Content Management System used by many of our customers, which made it important that our WAF protect against the vulnerability as quickly as possible.
As soon as Drupal released their patch, we analysed it to establish what kind of payloads could be used against it and created rules to mitigate these. By analysing the patch we were able to put together WAF rules to protect cloudflare customers running Drupal.
We identified the type of vulnerability we were dealing within 15 minutes. From here, we were able to deploy rules to block the exploit well before any real attacks were seen.
The exploit
As Drupal's release announcement explains, a site is affected if:
From looking at the patch we very quickly realised the exploit would be based on deserialization. The option ['allowed_classes' Continue reading
RSA Conference: Rise of the Robots (and the Women)
 The security landscape is essentially AI versus AI. May the best man, err, machine win.
The security landscape is essentially AI versus AI. May the best man, err, machine win.
Cumulus Networks Named to CRN Data Center 50
Cumulus Networks is proud to announce CRN®, a brand of The Channel Company, has named us to its 2019 Data Center 50 list.
This annual list identifies technology suppliers that offer the right management tools to help businesses and solution providers ensure data centers run with maximum performance and efficiency. We couldn’t be more thrilled! This accomplishment really solidifies our vision — to build the modern data center networks for applications of the future.
It’s been a while since we updated our blog community with our evolved vision for the modern data center, so we thought this would be a great opportunity to review a little bit about what Cumulus has been doing lately and how our products have evolved.
Our story — Building the modern data center
We pride ourselves on providing networking software to design, run and operate modern data centers that are simple, open, resilient, scalable and operationally efficient.
Our network operating system, Cumulus Linux, is a powerful, open network operating system that allows you to automate, customize and scale using web-scale principles like the world’s largest data centers.

When it comes to data center networks, traditional network solutions are unable keep up with the pace of Continue reading
Tips from a Network Detective
For over 30 years I’ve been in the playing in the “world of IT” and wow has that world changed a great deal in those years. But through all that change, there has been a thread, for me, that has always remained... Read More ›
The post Tips from a Network Detective appeared first on Networking with FISH.
Nokia, Ericsson to Provide 5G Gear to U.S. Cellular
 The Chicago-based regional carrier plans to begin offering 5G services by the end of this year.
The Chicago-based regional carrier plans to begin offering 5G services by the end of this year.
RSA Updates Archer, NetWitness Platforms
 Archer is a governance, risk management, and compliance platform. NetWitness is a threat detection...
Archer is a governance, risk management, and compliance platform. NetWitness is a threat detection...
History of Networking: George Swallow on MPLS/TE
Traffic engineering (TE) is one of the most complex technologies used in large scale networks today. George Swallow joins us for a look at how and why TE was invented, and where some of the ideas came from.
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3.0 License
http://creativecommons.org/licenses/by/3.0/
Cisco WiFi Routers Attacked After Code Hack Posted
 The attacks occurred after security research firm Pen Test Partners posted a blog containing...
The attacks occurred after security research firm Pen Test Partners posted a blog containing...