Palo Alto Networks Pays $173M for Cloud Security Startup RedLock
 Palo Alto Networks plans to combine technologies from RedLock and Evident, another recent acquisition, into one product that provides cloud security analytics, advanced threat detection, continuous security, and compliance monitoring.
Palo Alto Networks plans to combine technologies from RedLock and Evident, another recent acquisition, into one product that provides cloud security analytics, advanced threat detection, continuous security, and compliance monitoring.
Datanauts 148: What’s New In Azure And Azure Stack – Microsoft Ignite 2018
Chris Wahl and guests dive into the latest announcements about Azure and Azure Stack, including the Data Box storage device, new networking features, and more. This Datanauts episode was recorded live at Microsoft Ignite 2018.
The post Datanauts 148: What’s New In Azure And Azure Stack – Microsoft Ignite 2018 appeared first on Packet Pushers.
6 Ways SD-WAN Simplifies Network Management
SD-WAN offers network management capabilities that can streamline operations while lightening workloads.
Useful links for Observium + Rancid
I recently decided that i would like to utilize Observium as well as rancid for configuration backups on my home network. To that effect, the following links really helped me out getting it all setup correctly:
https://docs.observium.org/rancid/
http://packetsandpings.blogspot.com/2013/05/installing-and-configuring-rancid.html
https://layer77.net/2016/08/10/upgrading-from-rancid-2-3-8-to-3-4-1/
Let me know if you run into anything i might help out with.
/Kim
Custom Load Balancing With Cloudflare Workers
The following is a guest post by Jayaprabhakar Kadarkarai, Developer of Codiva.io, an Online IDE used by computer science students across the world. He works full stack to deliver low latency and scalable web applications.
Have you launched your website? Getting a lot of traffic? And you are planning to add more servers? You’ll need load balancing to maintain the scalability and reliability of your website. Cloudflare offers powerful Load Balancing, but there are situations where off-the-shelf options can’t satisfy your specific needs. For those situations, you can write your own Cloudflare Worker.
In this post, we’ll learn about load balancers and how to set them up at a low cost with Cloudflare Service Workers.
This post assumes you have a basic understanding of JavaScript, as that’s the language used to write a Cloudflare Worker.
The Basic Pattern
The basic pattern starts with adding ‘fetch’ event listener to intercept the requests. You can configure which requests to intercept on the Cloudflare dashboard or using the Cloudflare API.
Then, modify the hostname of the URL and send the request to the new host.
addEventListener('fetch', event => {
var url = new URL(event.request.url);
// https://example.com/path/ Continue readingNetwork Automation Development Environments
Building the network automation lab environment seems to be one of the early showstoppers on everyone’s network automation journey. These resources might help you get started:
- I wrote an installation script that installs the myriad dependencies needed by Ansible and NAPALM in just the right order on a Ubuntu VM (step-by-step instructions for ipSpace.net subscribers).
- Carl Buchmann open-sourced a full-blown infrastructure-as-code development environment he uses for his automation projects.
- Jaap de Vos described how he creates a Docker image containing Ansible, NAPALM and Nornir.
Hint: after setting up your environment, you might want to enroll into the Spring 2019 network automation course ;)
Ulaanbaatar, Mongolia

Whenever you get into a conversation about exotic travel or ponder visiting the four corners of the globe, inevitably you end up discussing Ulaanbaatar in Mongolia. Travelers want to experience the rich culture and vivid blue skies of Mongolia; a feature which gives the country its nickname of “Land of the Eternal Blue Sky”.

Ulaanbaatar (or Ulan Bator; but shortened to UB by many) is the capital of Mongolia and located nearly a mile above sea level just outside the Gobi Desert - a desert that spans a good percentage of Central Asia’s Mongolia. (The rest of the Gobi Desert extends into China). The country is nestled squarely between Russia to the north and China to the south. It’s also home to some of the richest and ancient customs and festivals around. It’s those festivals that successfully draw in the tourists who want to experience something quite unique. Luckily, even with all the tourists, Mongolia has managed to keep its local customs; both in the cities and within its nomadic tribes.
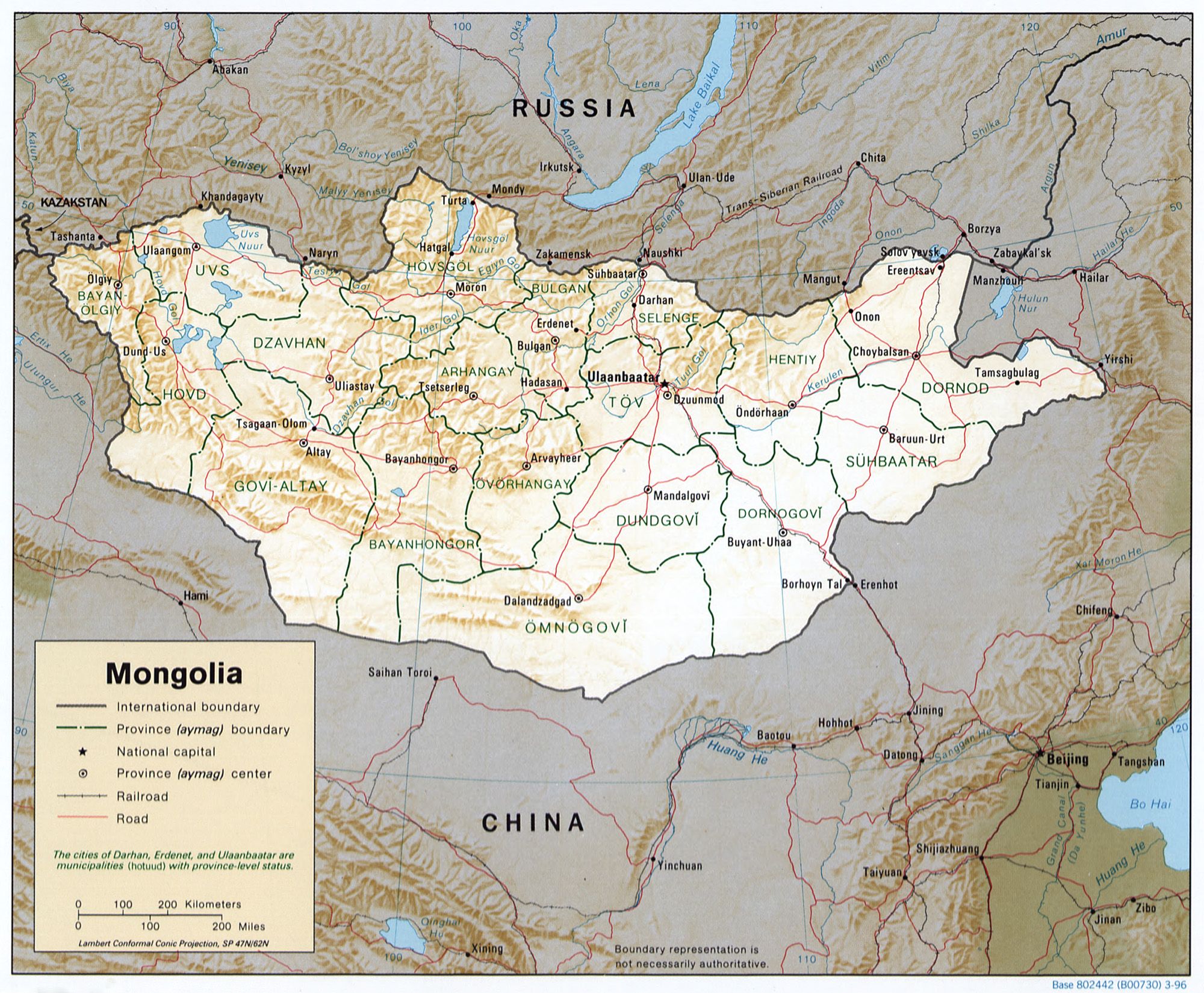
via Wikipedia
History also has drawn explorers and conquerors to and from the region; but more on that later.
Cloudflare is also drawn into Mongolia
Any avid reader of Continue reading
Cisco’s David Ulevitch Leaves to Join a VC Firm
 David Ulevitch, who was once in charge of Cisco’s security business, is leaving to become a general partner at Andreesson Horowitz.
David Ulevitch, who was once in charge of Cisco’s security business, is leaving to become a general partner at Andreesson Horowitz.
European Companies Launch OCP Experience Center to Test Hardware
 Three companies opened the OCP Experience Center for testing new and proposed OCP technologies and for conducting demonstrations of open OCP hardware designs.
Three companies opened the OCP Experience Center for testing new and proposed OCP technologies and for conducting demonstrations of open OCP hardware designs.
Digital Realty’s New Global Command Center Provides Centralized Network Monitoring
 The new facility plays into the data center provider’s plan to pull hyperscale cloud deals away from competitors including Equinix.
The new facility plays into the data center provider’s plan to pull hyperscale cloud deals away from competitors including Equinix.
SDxCentral’s Top 10 Articles — September 2018
 eBay ditches OpenStack in favor of Kubernetes and Docker; AT&T awards 5G contracts; Arista makes second acquisition.
eBay ditches OpenStack in favor of Kubernetes and Docker; AT&T awards 5G contracts; Arista makes second acquisition.
Related Stories
Technology often thought of as SDN !!!
What is SDN ? SDN Definition varies from Vendor to vendor ,commonly the architecture of SDN defined by each vendor includes use of different technology to make network automate, flexible, agile, dynamic ,scalable and most importantly cost effective.
I was going through Network automation article and found the different technology/trends which are some or other way often thought of a SDN, or are important part of SDN discussion .It’s good to go through it :-
OpenFlow : Its low level protocol used to decouple the control plane from the data plane.
NFV Network function Virtualization: It refers to taking functions that have traditionally have been deployed as hardware ,instead deploy them as software.
Virtual Switching :They are software based switches VDS(VMware Distributed switch ) ,AVS(cisco application virtual switch ),VSS(VMware Std. switch) etc. that resides in hypervisor kernel providing local network connectivity b/w virtual machines.
Network Virtualization: It refers to software-only overlay-based solution. A key characteristic of these solutions is that an overlay-based protocol such as Virtual eXtensible LAN (VxLAN) is used to build connectivity between hypervisor-based virtual switches. This connectivity and tunneling approach provides Layer 2 adjacency between virtual machines that exist on different physical hosts independent of Continue reading
Cloudflare Access: Sharing our single-sign on plugin for Atlassian
Here at Cloudflare, we rely on a set of productivity tools built by Atlassian, including Jira and Confluence. We secure them with Cloudflare Access. In the past, when our team members wanted to reach those applications, they first logged in with our identity provider credentials to pass Access. They then broke out a second set of credentials, specific to Atlassian tools, to reach Jira. The flow is inconvenient on a desktop and downright painful on a mobile device.
While Access can determine who should be able to reach an application, the product alone cannot decide what the user should be able to do once they arrive at the destination. The application sets those specific permissions, typically by requiring another set of user credentials. The extra step slows down and frustrates end users. Access saves time by replacing a cumbersome VPN login. However, we wanted to also solve the SSO problem for our team.
We created a plugin, specific to Atlassian, that could take identity data from the token generated by Access and map it to a user account. Our team members log in with our identity provider to pass Access, and then Access could set their user permissions in Jira Continue reading
Platform9 Open Sources Its Kubernetes Etcd Support Tool
 The etcdadm tool automates the configuration, deployment, and management of etcd clusters used by Kubernetes to store control plane information.
The etcdadm tool automates the configuration, deployment, and management of etcd clusters used by Kubernetes to store control plane information.
GTT Scoops Up the Service Provider Access Point for $40M
 GTT is also working with another recent acquisition, Interoute, to move its SD-WAN to a universal CPE approach with an integrated firewall.
GTT is also working with another recent acquisition, Interoute, to move its SD-WAN to a universal CPE approach with an integrated firewall.
Cohesity Targets Service Providers With Multi-Tenant Platform
 The software-defined platform runs on top of Cohesity, Cisco, HPE, or Dell EMC hyperconverged secondary storage appliances.
The software-defined platform runs on top of Cohesity, Cisco, HPE, or Dell EMC hyperconverged secondary storage appliances.
Aryaka’s New CEO Plans to Sharpen SD-WAN Firm’s Message to Customers
 The former Sprint executive says that there are too many SD-WAN competitors in the market muddying the message to enterprises.
The former Sprint executive says that there are too many SD-WAN competitors in the market muddying the message to enterprises.