Announcing the Cloudflare Apps Platform and Developer Fund

When we started Cloudflare we had no idea if anyone would validate our core idea. Our idea was what that everyone should have the ability to be as fast and secure as the Internet giants like Google, Facebook, and Microsoft. Six years later, it's incredible how far that core idea has taken us.
 CC BY-SA 2.0 image by Mobilus In Mobili
CC BY-SA 2.0 image by Mobilus In Mobili
Today, Cloudflare runs one of the largest global networks. We have data centers in 115 cities around the world and continue to expand. We've built a core service that delivers performance, security, availability, and insight to more than 6 million users.
Democratizing the Internet
From the beginning, our goal has been to democratize the Internet. Today we're taking another step toward that goal with the launch of the Cloudflare Apps Platform and the Cloudflare Developer Fund. To understand that, you have to understand where we started.
When we started Cloudflare we needed two things: a collection of users for the service, and finances to help us fund our development. In both cases, people were taking a risk on Cloudflare. Our first users came from Project Honey Pot, which Lee Holloway and I created back in 2004. Members Continue reading
Network Cabling Primer
Learn about the different types of cables and where they work best in the enterprise.
Testing Docker networking with GNS3, Part1: MaCVLAN
Introduction MacVLAN allows to connect containers in separate docker networks to your VLAN infrastructure, so they act like being directly connected to your network. From the main interface, MacVLAN driver creates subinterfaces to handle 802.1q tags for each VLAN, and assign to them separate IP and MAC addresses. Because the main interface (with its own […]OSPF Basic configuration Step by step on Cisco Routers
OSPF Basics- Theory
OSPF point to Multipoint Configuration- Cisco & Juniper
OSPF States
Difference between OSPF Vs RIP routing Protocols
From the above given links, you will able to understand much more about the OSPF. This article is all about the basic configurations on router about the OSPF.
Below is the basic topology of the OSPF which has not any relevance with the configuration part. The topology is just to show you what kind of network you have in the OSPF separated in the areas but with have one process id.
 |
| Fig 1.1- Sample OSPF Topology |
There is no relevance of the IP addresses uses here with any of the live networks or with any of the enterprise networks.
Lets talk step by step in OSPF
In Step 1, I am talking about how to enable the OSPF routing protocol on Cisco routers by putting the OSPF process id. Make sure you know about the process id, It is similar Continue reading
To Jumbo or Not to Jumbo?
Here’s the question I got from one of my readers:
Do you have any data available to show the benefits of jumbo frames in 40GE/100GE networks?
In case you’re wondering why he went down this path, here’s the underlying problem:
Read more ...Announcing the New Cloudflare Apps
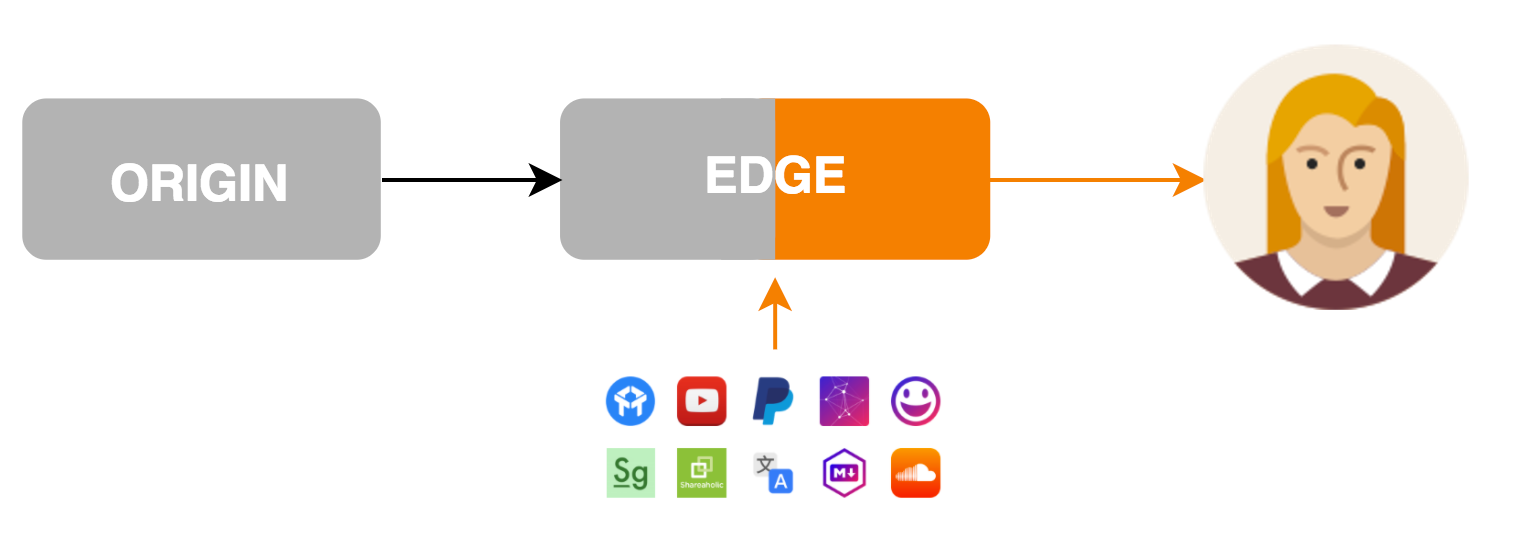
Today we’re excited to announce the next generation of Cloudflare Apps. Cloudflare Apps is an open platform of tools to build a high quality website. It’s a place where every website owner can select from a vast catalog of Apps which can improve their websites and internet properties in every way imaginable. Selected apps can be previewed and installed instantly with just a few clicks, giving every website owner the power of technical expertise, and every developer the platform only Cloudflare can provide.
Apps can modify content and layout on the page they’re installed on, communicate with external services and dramatically improve websites. Imagine Google Analytics, YouTube videos, in-page chat tools, widgets, themes and every other business which can be built by improving websites. All of these and more can be done with Cloudflare Apps.
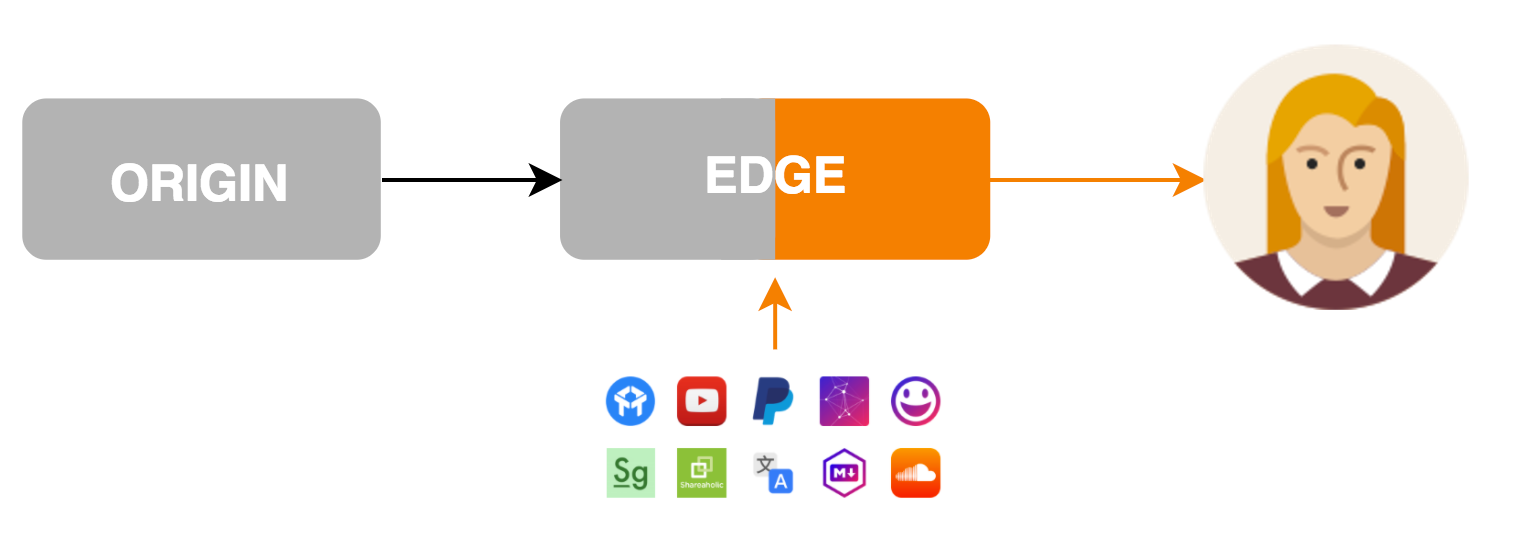
Cloudflare Apps makes it possible for a developer in her basement to build the next great new tool and get it on a million websites overnight. With Cloudflare Apps, even the smallest teams can get massive distribution for their apps on the web so that the best products win. With your help we will make it possible for developers like you to build a new Continue reading
SevOne Integrates SDN Monitoring with Cisco ACI
 SevOne will soon be able to monitor VMware and Nuage SDN environments too.
SevOne will soon be able to monitor VMware and Nuage SDN environments too.
Worth Reading: A different kind of bubble
The post Worth Reading: A different kind of bubble appeared first on rule 11 reader.
Telefónica Peru Transforms Central Office to Cloud Data Center
 It hired Huawei to make the transition.
It hired Huawei to make the transition.
Ericsson to Prep Vodafone UK’s 4G LTE Network for 5G
 Deal calls for deployment of MIMO antenna and carrier aggregation technology.
Deal calls for deployment of MIMO antenna and carrier aggregation technology.
Disaggregated, Hyperconverged, and Composed (part 2)
The post Disaggregated, Hyperconverged, and Composed (part 2) appeared first on rule 11 reader.