Gap Weaves a Global SD-WAN Strategy
 Gap is using Viptela's platform for its SD-WAN.
Gap is using Viptela's platform for its SD-WAN.
Deadline 3 May: Recognize an outstanding technologist
Do you know someone who has made an outstanding contribution to the development of the Internet?
We are pleased to announce that candidate nominations for the 2017 Jonathan B. Postel Service Award are open.
This annual award is presented to an individual or organization that has made outstanding contributions in service to data communications and places particular emphasis on those who have supported and enabled others.
Nominations are encouraged for individuals or teams of individuals from across the data communications industry around the world who are dedicated to the efforts of advancing the Internet for the benefit of everybody.
Ixia Updates CloudLens for Public Cloud Visibility
 CloudLens is available on AWS, and Azure is coming soon.
CloudLens is available on AWS, and Azure is coming soon.
MicroSegmentation of Applications using Application Rule Manager
“Micro-Segmentation provides a way to build a zero-trust network – where all networks, perimeters and application are inherently untrusted.” – declared Forrester Consulting in 2015 with their white paper Leveraging Micro-Segmentation to build zero-trust model. The last mile in creating a truly zero-trust network implies not trusting each application and also tiers within an application (Figure 1). To complete the last mile, network, security and risk professionals are increasingly looking for tools to understand application communication patterns and providing access controls to them. With version 6.3.0, NSX has unveiled 2 new tools, namely, Application Rule Manager (ARM) and Endpoint Monitoring (EM), to help professionals understand application patterns.
 Figure 1: Zero-Trust Model using NSX
Figure 1: Zero-Trust Model using NSX
From Theory to Practice
Micro-Segmenting each application requires understanding of application communication patterns. Users should allow the flows required by the application. To accomplish zero-trust, users should be closing all unwanted flows & ports. Figure 2., is a sample practical firewall policy model to achieve that. In this model, ARM/EM provides application patterns and a one-click conversion of those patterns into distributed firewall rules to achieve inter/intra application rules.
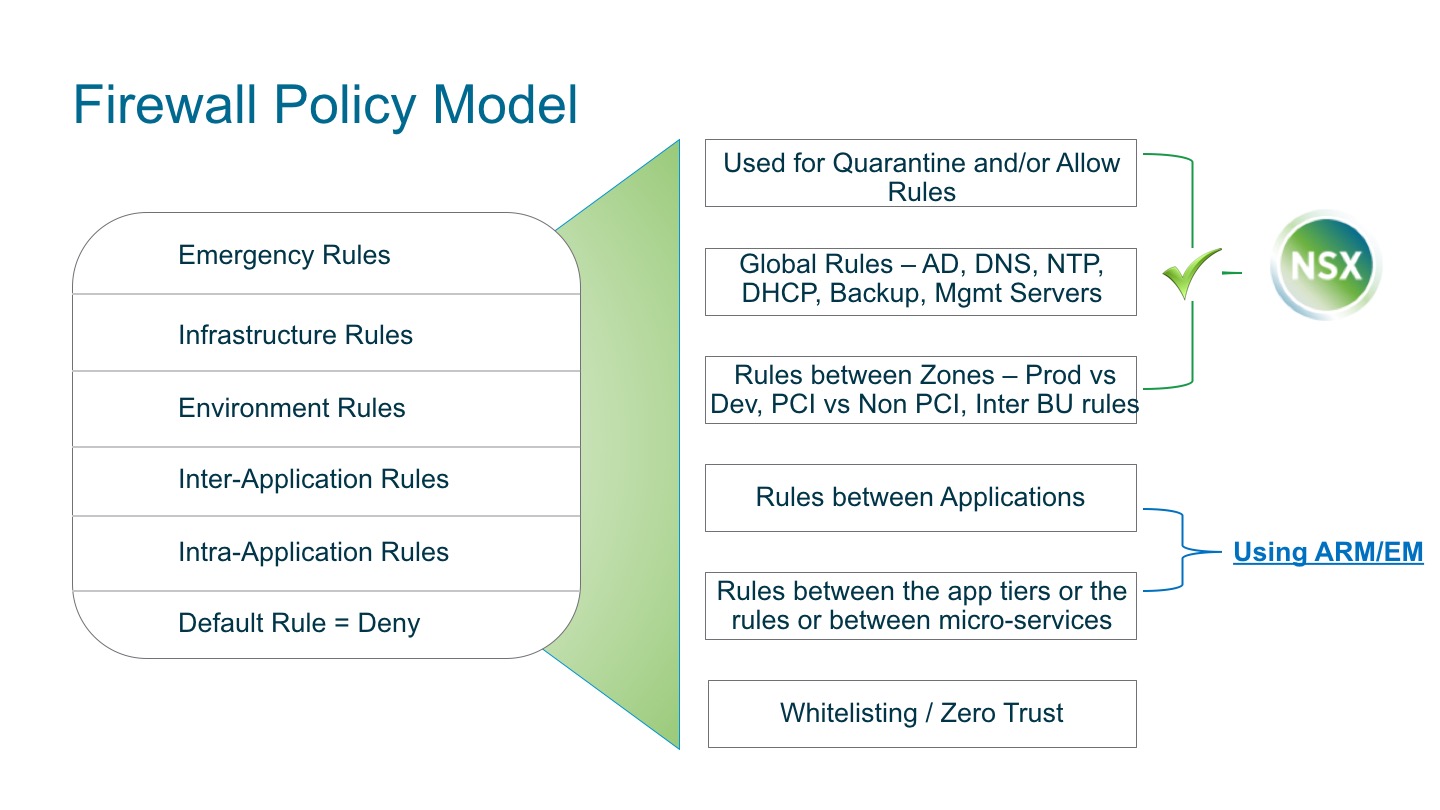 Figure 2: Firewall Policy Model
Figure 2: Firewall Policy Model
Generating Distributed Firewall Rules Rapidly
Any application in the datacenter can be Continue reading
Application Rule Manager (ARM) Practical Implementation – Healthcare
This post originally appears as part of a series of VMware NSX in Healthcare blogs on Geoff Wilmington’s blog, vWilmo. To read more about VMware NSX and its applications in healthcare, check out Geoff’s blog series.
Originally this series on Micro-segmentation was only going to cover Log Insight, vRealize Network Insight (vRNI), and VMware NSX. With the release of VMware NSX 6.3, there is a new toolset within NSX that can be leveraged for quick micro-segmentation planning The Application Rule Manager (ARM) within NSX, provides a new way to help create security rulesets quickly for new or existing applications on a bigger scale than Log Insight, but smaller scale than vRNI. With that in mind, we’re going to take the previous post using Log Insight, and perform the same procedures with ARM in NSX to create our rulesets using the same basic methodologies.
The Application Rule Manager in VMware NSX leverages real-time flow information to discover the communications both in and out, and between an application workload so a security model can be built around the application. ARM can monitor up to 30 VMs in one session and have 5 sessions running at a time. Continue reading
5 Practical Cloud Tips for SMBs
Interop ITX expert offers advice for making a cloud migration more successful.