Hedge 172: Roundtable! SONiC, Open Source, and Complexity
It’s roundtable time at the Hedge! Eyvonne Sharp, Tom Ammon, and I start the conversation talking about the SONiC open source NOS, and then wander into using open source, build versus buy, and finally complexity in design and deployment.
Thanks for listening–if you have an idea for a Hedge episode, would like to be a guest, or know someone you think would be a good guest, let one us know!
Outburst: Bombs Made From USB Sticks Target Journalists
 Show topic from Network Break Episode 423
Show topic from Network Break Episode 423
Outburst: SASE Revenues Reach $6 Billion
 Show topic from Network Break Episode 423
Show topic from Network Break Episode 423
Day Two Cloud 188: Out-Of-Band Management And Infrastructure Automation With ZPE Systems (Sponsored)
On today's Day Two Cloud podcast we talk through out-of-band management network design with sponsor ZPE Systems. If your idea of OOB management is a jump box and some terminal servers, there’s a lot more to the story when you bring automation tooling into the picture. We'll learn how ZPE gear works and talk with customer Vapor IO about using ZPE gear in its edge compute sites.
The post Day Two Cloud 188: Out-Of-Band Management And Infrastructure Automation With ZPE Systems (Sponsored) appeared first on Packet Pushers.
Day Two Cloud 188: Out-Of-Band Management And Infrastructure Automation With ZPE Systems (Sponsored)
On today's Day Two Cloud podcast we talk through out-of-band management network design with sponsor ZPE Systems. If your idea of OOB management is a jump box and some terminal servers, there’s a lot more to the story when you bring automation tooling into the picture. We'll learn how ZPE gear works and talk with customer Vapor IO about using ZPE gear in its edge compute sites.NVIDIA Struts Its Telco Transformation Stuff at GTC, Announces AT&T Adoption of AI
The use of artificial intelligence (AI), and especially GPU-powered AI, can help telcos solve some of their biggest challenges.Killnet and AnonymousSudan DDoS attack Australian university websites, and threaten more attacks — here’s what to do about it


Over the past 24 hours, Cloudflare has observed HTTP DDoS attacks targeting university websites in Australia. Universities were the first of several groups publicly targeted by the pro-Russian hacker group Killnet and their affiliate AnonymousSudan, as revealed in a recent Telegram post. The threat actors called for additional attacks against 8 universities, 10 airports, and 8 hospital websites in Australia beginning on Tuesday, March 28.
Killnet is a loosely formed group of individuals who collaborate via Telegram. Their Telegram channels provide a space for pro-Russian sympathizers to volunteer their expertise by participating in cyberattacks against western interests.
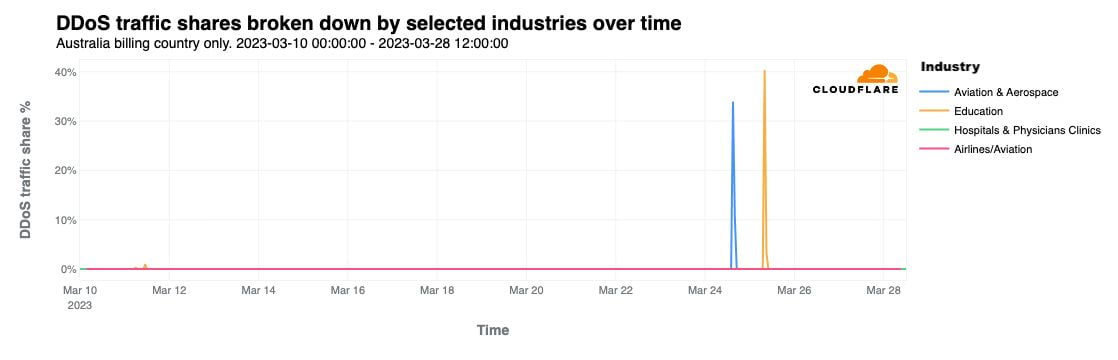
This is not the first time Cloudflare has reported on Killnet activity. On February 2, 2023 we noted in a blog that a pro-Russian hacktivist group — claiming to be part of Killnet — was targeting multiple healthcare organizations in the US. In October 2022, Killnet called to attack US airport websites, and attacked the US Treasury the following month.
As seen with past attacks from this group, these most recent attacks do not seem to be originating from a single botnet, and the attack methods and sources seem to vary, suggesting Continue reading
Studying EVPN to Prepare for a Job Interview
An ipSpace.net subscriber sent me this question:
I am on job hunting. I have secured an interview and they will probably ask me about VxLAN BGP EVPN fabrics. If you have some time, it would be a great help for me if you could tell me 1 or 2 questions that you would ask in such interviews.
TL&DR: He got the job. Congratulations!
Studying EVPN to Prepare for a Job Interview
An ipSpace.net subscriber sent me this question:
I am on job hunting. I have secured an interview and they will probably ask me about VxLAN BGP EVPN fabrics. If you have some time, it would be a great help for me if you could tell me 1 or 2 questions that you would ask in such interviews.
TL&DR: He got the job. Congratulations!
Myth Busting: You Can’t Use Packet Monitoring for Enterprise Security
Security teams today realize the value of packet monitoring for cybersecurity. As they find more uses for packet monitoring, they shatter the myth that the latter is insufficient on its own.Cloudflare’s commitment to the 2023 Summit for Democracy

On Tuesday, March 28, 2023, the US Government will launch the Summit for Democracy 2023, following up on the inaugural Summit for Democracy 2021. The Summit is co-hosted by the United States, Costa Rica, Zambia, the Netherlands, and South Korea. Cloudflare is proud to participate in and contribute commitments to the Summit because we believe that everyone should have access to an Internet that is faster, more reliable, more private, and more secure. We work to ensure that the responsibility to respect human rights is embedded throughout our business functions. Cloudflare’s mission — to help build a better Internet — reflects a long-standing belief that we can help make the Internet better for everyone.
Our mission and core values dovetail with the Summit’s goals of strengthening democratic governance, respect for human rights and human rights defenders, and working in partnership to strengthen respect for these values. As we have written about before, access to the Internet allows activists and human rights defenders to expose abuses across the globe, allows collective causes to grow into global movements, and provides the foundation for large-scale organizing for political and social change in ways that have never been possible before.

What is Continue reading
What Happened to Leaf Switches with Four Uplinks?
The last time I spent days poring over vendor datasheets collecting information for the overview part of Data Center Fabrics webinar a lot of 1RU data center leaf switches came in two form factors:
- 48 low-speed server-facing ports and 4 high-speed uplinks
- 32 high-speed ports that you could break out into four times as many low-speed ports (but not all of them)
I expected the ratios to stay the same when the industry moved from 10/40 GE to 25/100 GE switches. I was wrong – most 1RU leaf data center switches based on recent Broadcom silicon (Trident-3 or Trident-4) have between eight and twelve uplinks.
What Happened to Leaf Switches with Four Uplinks?
The last time I spent days poring over vendor datasheets collecting information for the overview part of Data Center Fabrics webinar a lot of 1RU data center leaf switches came in two form factors:
- 48 low-speed server-facing ports and 4 high-speed uplinks
- 32 high-speed ports that you could break out into four times as many low-speed ports (but not all of them)
I expected the ratios to stay the same when the industry moved from 10/40 GE to 25/100 GE switches. I was wrong – most 1RU leaf data center switches based on recent Broadcom silicon (Trident-3 or Trident-4) have between eight and twelve uplinks.
Tech Bytes: Choosing Single-Vendor SASE For Networking And Security (Sponsored)
Today on the Tech Bytes podcast, sponsored by Palo Alto Networks, we get into Secure Access Services Edge (SASE), which combines SD-WAN with cloud-delivered security services. You can integrate parts from different vendors, but Palo Alto Networks is here to make a case for why you might want to consider a single-vendor approach.
The post Tech Bytes: Choosing Single-Vendor SASE For Networking And Security (Sponsored) appeared first on Packet Pushers.
Tech Bytes: Choosing Single-Vendor SASE For Networking And Security (Sponsored)
Today on the Tech Bytes podcast, sponsored by Palo Alto Networks, we get into Secure Access Services Edge (SASE), which combines SD-WAN with cloud-delivered security services. You can integrate parts from different vendors, but Palo Alto Networks is here to make a case for why you might want to consider a single-vendor approach.Network Break 423: Arista Woos Large Enterprises With New SD-WAN Router; Google Breaks Glass Enterprise
This week's Network Break covers Arista's new WAN routers that get the company into the SD-WAN market, debates whether Aryaka targeting SMEs is a sign of problems or opportunity, and discusses an update on the size of the SASE market. We also look at an HPE acquisition, the use of exploding USBs to target journalists, space networking, and more.
The post Network Break 423: Arista Woos Large Enterprises With New SD-WAN Router; Google Breaks Glass Enterprise appeared first on Packet Pushers.