VMware VSAN Can Stretch – Should It?
Pirmin Sidler read the stretched VSAN blog posts by Duncan Epping (intro, HA/DRS considerations, demo) and asked me what I think about stretched VSAN considering my opinions on long-distance vMotion.
TL&DR answer: it makes way more sense than long-distance vMotion. However…
Read more ...Mirantis Assembles Partners to Meet Demand for ‘NFV Magic’
 Mirantis says customers want it to deliver NFV magic with all the bells and whistles, so it's assembling vendor partners to make it happen.
Mirantis says customers want it to deliver NFV magic with all the bells and whistles, so it's assembling vendor partners to make it happen.
Python up and running
 Python has certainly become one of the top languages of the day. In this post, I want to spend some time to get you up and running with it. We’ll start with a base install of Python and then walk through an example to introduce some basic Python concepts. If you’re in infrastructure, particularly networking, then Python is a language you should be putting some time towards learning. Most of the vendors out there are coming out with some level of Python integration for their products. Matt Oswalt spends some time in one of his recent posts talking about how important this integration is as well as gives a couple of examples. Bottom line – all of us in infrastructure should be finding better ways to do things and Python is a good place to start.
Python has certainly become one of the top languages of the day. In this post, I want to spend some time to get you up and running with it. We’ll start with a base install of Python and then walk through an example to introduce some basic Python concepts. If you’re in infrastructure, particularly networking, then Python is a language you should be putting some time towards learning. Most of the vendors out there are coming out with some level of Python integration for their products. Matt Oswalt spends some time in one of his recent posts talking about how important this integration is as well as gives a couple of examples. Bottom line – all of us in infrastructure should be finding better ways to do things and Python is a good place to start.
Note: If you’re interested in the future of networking as a whole, check out this other post from Matt Oswalt where he talks about next gen networking skills. Good stuff.
I always like to start from the beginning so let’s start from absolute scratch. I’m going to start with a CentOS 7 host that has Continue reading
Juniper vSRX Automation with Ansible
Virtual appliances not only provide for a great lab environment, but are the future of how network services will be tested, validated, and delivered within an Enterprise. And Juniper gets this – they spent a lot of time covering the vSRX and vMX product lines at the most recent Networking Field Day event.
Over the next few months, I’ll more than likely be spending a lot of time on Juniper gear, and it will be the virtual platforms, so it was good timing to get to be in the room to learn more about them along with many of the automation capabilities Juniper supports across their product families.
NETCONF Rules All for Juniper
While I have not spent as much time on Juniper kit as I would have liked over the past few years, the one awesome thing to see and experience first-hand is that they have a unified API (NETCONF) across all of their products.
Why is this so valuable? Well, for one, we get to use the same libraries and integrations across platforms. As an example, we can use the Juniper Ansible modules across any of their devices. In this post, we’ll take a look at using one Continue reading
CCIE Recert Should Be Like Wilderness Medicine Recert
Last winter I had to recertify CCIE. This time it felt like a negative, adversarial ordeal: reviewing and relearning a lot of stuff that I don’t use in order to justify the sunk costs of obtaining the certification. It’s also a zero-sum game: time spent on recertification is time not spent learning newer, more relevant things. I’ve seen a couple of blog posts (here and here) lately related to this issue. How could recertification be done better?
Outside my professional life, I’ve long been a search and rescue volunteer here in rural Colorado. As part of that, I maintain a Wilderness First Responder (WFR) certification. WFR is a certification for remote emergency medical care that starts as an 80-hour class. It’s required for most types of guiding and outdoor education careers.
Unlike with the CCIE, I always look forward to WFR recertification, even though it’s expensive and I have to take vacation time in order to do it. Why? It’s fun, cooperative, progressive, educational, and encouraging. It’s done as a 16-24 hour class that mixes classroom review, hands-on lab practice, and new material that’s been introduced or updated in the preceding years. This allows recertification candidates to interact Continue reading
Alcatel-Lucent’s Elastic Networks: Jargon or Something Real?
 Lots of things are called 'elastic' lately, but Alcatel-Lucent's Elastic CDN is more about network virtualization than industry jargon.
Lots of things are called 'elastic' lately, but Alcatel-Lucent's Elastic CDN is more about network virtualization than industry jargon.
Securing the World’s Most Hostile Wi-Fi Network
Wi-Fi security recently took on the ultimate challenge at the infamous Black Hat USA 2015 security conference held this year at Mandalay Bay in Las Vegas. One of the world’s premiere hacking events, Black Hat attracts some 10,000 security super...CloudFlare + WHMCS: Faster Websites For Your Customers
We’re at the cPanel Conference in Denver this week, so feel free to drop by our booth and say hello. It’s a great opportunity to connect with our partners and better understand their needs. We’re always trying to streamline our partners’ user experience, and we thought it would be a fitting time to walk through our recently updated WHMCS integration.
CloudFlare’s WHMCS 6.0 plugin lets hosting providers and registrars extend all the benefits of CloudFlare directly to their customers. You can offer your entire user base a global CDN with 62 points of presence, automatic web content optimization, basic DDoS protection, reputation-based threat protection, and much more with virtually no extra work.
These benefits are seamlessly integrated into your WHMCS client. All your customers need to do is click a button, and a new CloudFlare account will be configured for them.
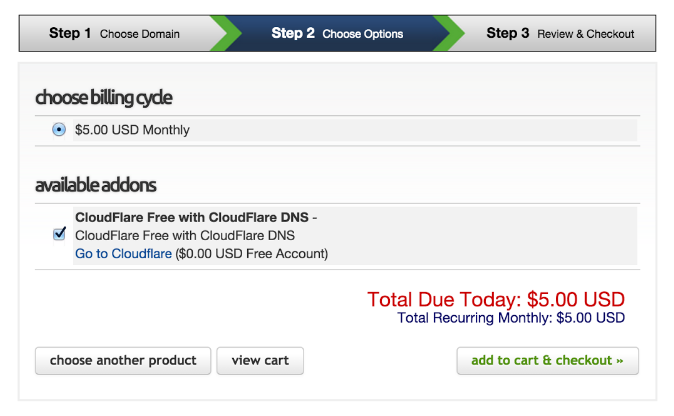
While signing up for an account on www.cloudflare.com only takes a few minutes, users do need to point the relevant DNS records to CloudFlare’s nameservers. Offerring a one-click solution via our WHMCS integration is a great opportunity for hosting providers and registrars to streamline the process for their customers.
Universal SSL with WHMCS
CloudFlare’s Universal Continue reading
Former Cisco President Lloyd Boards Hyperloop as CEO
 Rob Lloyd seems to have landed on his feet after leaving Cisco.
Rob Lloyd seems to have landed on his feet after leaving Cisco.
Killer SDN Applications: A view in 2015
Whilst on the DLR in London earlier this year (2015) a set of thoughts came to light whilst pondering centralised decision making for part of a network. It’s not uncommon to hear “Product X is a great platform that just needs the killer app”. Why the DLR? No drivers, swipe-in-swipe-out ticketing and a well defined service. A train still takes you from A to B, but the whole service around it has completely changed to keep up with the requirements. Thought provoking stuff.
TL;DR
Many people talk about killer apps and are seemingly waiting for them to pop in to existence. This post goes someway to come to terms with the lack of emerging killer apps and why we’re one paradigm shift away from seeing it happen.
The Rub
I’ve said this a million times, but traditional networking skill sets view the network as a CLI that is linked to features. Separation of the monolith seems mad! Why separate something out when what we have today works? Well, that’s the key issue.
The IPEngineer Laws of Humans
Networking as we mostly know it today:
a) Is massively reliant on error prone humans
b) Humans are an expensive resource to have Continue reading
Citrix White Paper: Integrate SDN & ADNs
 The ultimate guide for ADN masters. Read the Citrix white paper for the latest on ADN integration models, use cases and best practices!
The ultimate guide for ADN masters. Read the Citrix white paper for the latest on ADN integration models, use cases and best practices!
vCPE Is a Hot NFV Use Case for Masergy
 Virtual customer premises equipment is one of several use cases for NFV, but the topic gets top billing at an NFV industry conference.
Virtual customer premises equipment is one of several use cases for NFV, but the topic gets top billing at an NFV industry conference.
Featured Use Case: IMTC & ONF Release First UC SDN Use Case & Open Standard NBI to Automate QoE
 IMTC and ONF issue the first UC SDN use case and standardized NBI specification, which enables applications to communicate performance needs to better optimize the underlying network using SDN.
IMTC and ONF issue the first UC SDN use case and standardized NBI specification, which enables applications to communicate performance needs to better optimize the underlying network using SDN.
How the Internet Really Works


Way back in April of 2014, I started a series over on Packet Pushers called “How the Internet Really Works.” This is a long series, but well worth reading if you want to try and get a handle around how the different companies and organizations that make up the ecosystem of the ‘net actually do what they do.
Overview
DNS Lookups
The Business Side of DNS (1)
The Business Side of DNS (2)
Reverse Lookups and Whois
DNS Security
Provider Peering Types
Provider Peering and Revenue Streams (1)
Provider Peering and Revenue Streams (2)
Standards Bodies
IETF Organizational Structure
The IETF Draft Process
Reality at the Mic (Inside the IETF, Part 1)
Reality at the Mic (Inside the IETF, Part 2)
Reality at the Mic (Inside the IETF, Part 3)
Internet Exchange Points
That Big Number Database in the Sky (IANA)
NOG World (Network Operator Groups)
The Internet Society
The slides that go with this set of posts are available on slideshare, as well. This set is in Ericsson format, but I have older sets in “vendor neutral” formatting, and even cisco formatting (imagine that!).
The post How the Internet Continue reading
Worth Reading: How we ended up with microservices


The post Worth Reading: How we ended up with microservices appeared first on 'net work.