CoreOS – Using fleet to deploy an application
At this point we’ve deployed three hosts in our first and second CoreOS posts. Now we can do some of the really cool stuff fleet is capable of doing on CoreOS! Again – I’ll apologize that we’re getting ahead of ourselves here but I really want to give you a demo of what CoreOS can do with fleet before we spend a few posts diving into the details of how it does this. So let’s dive right back in where we left off…
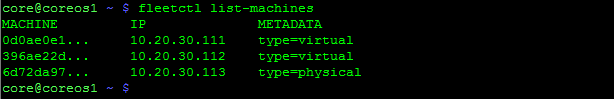
We should have 3 CoreOS hosts that are clustered. Let’s verify that by SSHing into one of CoreOS hosts…
Looks good, the cluster can see all three of our hosts. Let’s start work on deploying our first service using fleet.
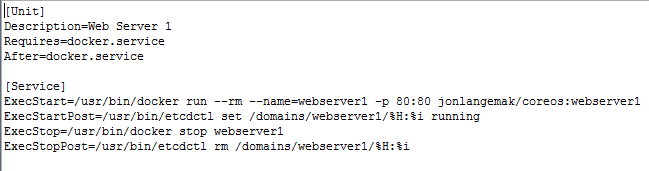
Fleet works off of unit files. This is a systemd construct and one that we’ll cover in greater detail in the upcoming systemd post. For now, let’s look at what a fleet unit file might look like…
Note: These config files are out on my github account – https://github.com/jonlangemak/coreos/
Systemd works off of units and targets. Suffice to say for now, the fleet service file describes a service Continue reading
iPexpert’s Newest “CCIE Wall of Fame” Additions 12/12/2014
Please Join us in congratulating the following iPexpert clients who have passed their CCIE lab!
- Chris Hayden, CCIE #45781 (Collaboration)
- Ahmed Samir , CCIE #45697 (Wireless)
We Want to Hear From You!
Have you passed your CCIE lab exam using any iPexpert or Proctor Labs self-study products, or attended our CCIE Bootcamp? If so, we’d like to add you to our CCIE Wall of Fame!
The End of Fixed Voice
IP Telephony is an end stage market. Here is why.
The post The End of Fixed Voice appeared first on EtherealMind.
The Definitive QEmu Guide for GNS3
Ahoy Matey! We'd be sailing through uncharted waters here! *Makes pirate voice*. Seriously, I have searched and searchedOn Policy in the Data Center: Congress
By Tim Hinrichs and Scott Lowe with contributions from Alex Yip, Dmitri Kalintsev, and Peter Balland
(Note: this post is also cross-published at RuleYourCloud.com, a new site focused on policy.)
In the first few parts of this series, we discussed the policy problem, we outlined dimensions of the solution space, and we gave a brief overview of the existing OpenStack policy efforts. In this post we do a deep dive into one of the (not yet incubated) OpenStack policy efforts: Congress.
Overview
Remember that to solve the policy problem, people take ideas in their head about how the data center ought to behave (“policy”) and codify them in a language the computer system can understand. That is, the policy problem is really a programming languages problem. Not surprisingly Congress is, at its core, a policy language plus an implementation of that language.
Congress is a standard cloud service; you install it on a server, give it some inputs, and interact with it via a RESTful API. Congress has two kinds of inputs:
- The other cloud services you’d like it to manage (for example, a compute manager like OpenStack Nova and a network manager like OpenStack Continue reading
PlexxiPulse—Reflections in Networking
2014 was a busy year in networking, and our friend Marcia Savage did a great job of summarizing the industry highs and lows – from ACI to white box switches – this week in a slideshow for Network Computing. It’s definitely worth a read before you head out for the weekend. Check out Marcia’s year end wrap up below as well as other happenings in the networking space this week.
In this week’s PlexxiTube video of the week, Dan Bachman explains how Plexxi incorporates optical transport into datacenter transport fabrics.
Computer Weekly: Cisco is missing the transition to software-defined networks
By Alex Scroxton
Little doubt remains that the future of networking will be defined by software, but market-watchers warn Cisco is missing this move. Cisco’s hardware forms the backbone of most enterprise networks around the world. But this world is changing and many buyers no longer see compute, storage and networking as distinct silos… Software-defined networking (SDN) company Plexxi, which recently appointed former EMC executive Richard Napolitano as its CEO, is one such company looking at the networking industry’s transition from networking towards an application and data-focused world. “We stand today at a transition point in the IT landscape,” says Continue reading
Friday News Analysis: Cisco Sues Arista For Patent + Copyright Infringement
Cisco is suing Arista in a pair of actions that will be interesting to follow as they wind their way through the courts. See post entitled “Protecting Innovation” here. In the thirteen years I’ve been General Counsel of Cisco, I can count on one hand the number of times we’ve initiated suit against a competitor, […]Basic Python Multithreading
The first ‘proper’ Python app I made logged onto a list of devices and pulled out OSPF state. This worked perfectly fine. The app correctly works out whether it can log into a device or not, and waits a few seconds to ensure a device actually responds. The issue is that if I have a […]Internets of Interest – 12 December 2014
Collection of useful, relevant or just fun places on the Internets for 12 December 2014 and a bit commentary about what I've found interesting about them:
The post Internets of Interest – 12 December 2014 appeared first on EtherealMind.
L2VPN over IPv6 with Snabb Switch on Software Gone Wild
Highly customizable high-speed virtual switch written in Lua sounds great, but is it really that easy to use? Simon Leinen was kind enough to get me in touch with Alex Gall, his colleague at Switch, who's working on an interesting project: implementing L2VPN over IPv6 with Snabb Switch.
Read more ...Big Switch Chaos Monkey Network Testing
Whenever you build a complex system, you need to test that it works as expected, including properly handling failures. It’s easy enough to do simple component failure testing, but harder to do rapid automated failure tests. Big Switch is showing that it can be done though. Hopefully we can keep improving our testing to pick up some more of the software failures.
Testing is hard
Over the course of my career I’ve built many clustered systems – HP-UX Serviceguard, firewalls, routers, load balancers, RedHat Clusters, etc. Good clusters have redundant everything – servers, power supplies, disks, NICs, etc.
The commissioning process always included testing. We’d go through each of the components, trying to simulate failures. Unplug each of the power cables, the network cables, unseat a hard drive, remove a hot-swappable fan, etc. That would test out the redundant components within each server, and then of course you’d simulate a complete system failure, forcing full failover.
This is all important stuff, but it doesn’t pick up all the failures – e.g. What happens if you’ve got a faulty patch lead, and the link starts flapping? Sometimes a simple failure gets messy when it happens repeatedly over a short Continue reading
phpipam 1.1.010 update released
phpipam 1.1.010 update released with following fixes:
== 1.1.010 Bugfixes: ---------------------------- + Fixed login fails with LDAP when escape characters are in password; + Fixed login not working with spaces in password for AD login; + Fixed Ivalid action when adding vlans from subnet popup menu; + Fixed custom fields not appearing properly on IP request editing; + Fixed Invalid ID error for IP address details on sorting; + Fixed warnings if no VLAN search results are present; + Fixed test mail not sending; + Fixed unable to login if $phpsessname not defined; + Fixed unable to login after upgrade;
I apologise for any inconvenience some users experienced with upgrade.
brm
How portable is your network operating system?
Conversations are swirling throughout the tech industry about whether white box switches are disrupting the networking industry, similarlyShow 216 – HP & SDN In The Campus – Sponsored
At HP Discover Barcelona 2014, the Packet Pushers had the chance to chat with Heather Giovanni, Craig Mills, and Chris Young about the HP 5400R and SDN in the campus. HP has a full line of switches and routers that some know about, and some just haven’t yet explored. The 5400R is a multi-slot chassis […]
Author information
The post Show 216 – HP & SDN In The Campus – Sponsored appeared first on Packet Pushers Podcast and was written by Ethan Banks.
Facebook Next-Generation Fabric
Facebook published their next-generation data center architecture a few weeks ago, resulting in the expected “revolutionary approach to data center fabrics” echoes from the industry press and blogosphere.
In reality, they did a great engineering job using an interesting twist on pretty traditional multi-stage leaf-and-spine (or folded Clos) architecture.
Read more ...CoreOS – Getting your second (and 3rd) host online
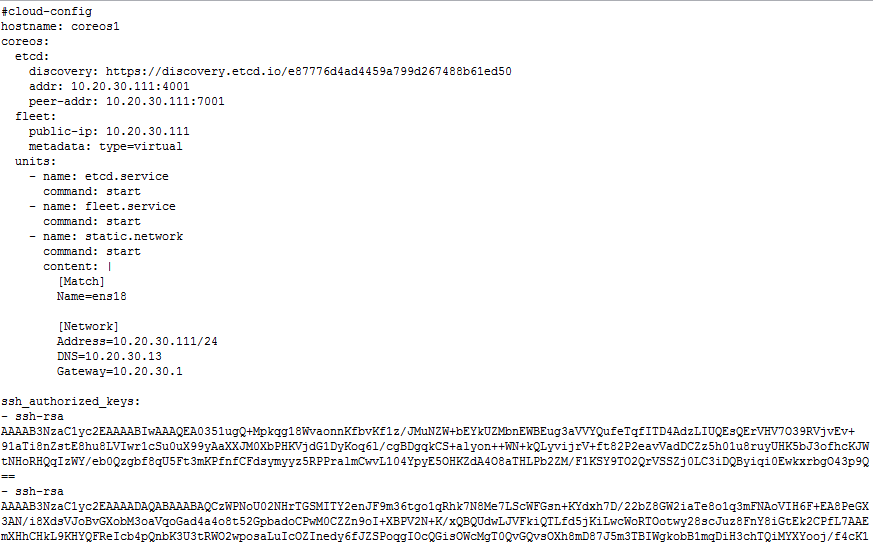
Quick note: For the sake of things formatting correctly on the blog I’m using a lot of screenshots of config files rather than the actual text. All of the text for the cloud-configs can be found on my github account here – https://github.com/jonlangemak/coreos/
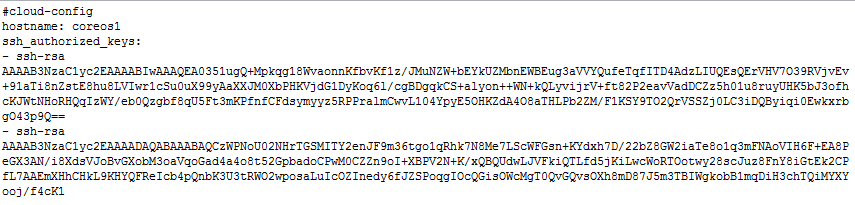
Now that we have our first CoreOS host online we can start the cool stuff. We’re going to pick up where we left off in my last post with our first installed CoreOS host which we called ‘coreOS1’. Recall we had started with a very basic cloud-config that looked something like this…
All this really did was get us up and running with a DHCP address and the base system services running. Since we’re looking to do a bit more in this post, we need to add some sections to the cloud-config. Namely, I’m going to configure a static IP address for the host, configure and start etcd, and configure and start fleet. So here’s what my new cloud config for coreOS1 will look like…
So there’s a lot more in this cloud-config. This config certainly deserves some explaining. However, in this post, I want to just get Continue reading
3 Ways To Get Started With VMware NSX
Over the past 12 months, VMware NSX momentum has continued to grow, as we’ve added  new platform capabilities, expanded our partner ecosystem, and of course, had more than 250+ customers purchase NSX for deployment. And as interest in VMware NSX has grown with both customers and IT professionals looking to evolve their careers by adding certification in network virtualization, one of the most common questions that we get is “How can I get started with NSX?.”
new platform capabilities, expanded our partner ecosystem, and of course, had more than 250+ customers purchase NSX for deployment. And as interest in VMware NSX has grown with both customers and IT professionals looking to evolve their careers by adding certification in network virtualization, one of the most common questions that we get is “How can I get started with NSX?.”
We understand that there is a strong demand for individuals and organizations to get their hands on the NSX technology. Many of you are working towards your initial VCP-NV certification. Others of you are exploring NSX as a way to improve your organization’s agility and security while reducing overall costs.
Here are three ways individuals and companies can get started with NSX.
Complete NSX: Install, Configure, Manage Training – for individuals on the NSX career path, we offer “NSX: Install, Configure, Manage” training. We are offering ICM training as part of our On-Demand Curriculum, or you can take a 5-day instructor led course. Here is the detailed course description and class schedule. ICM training is a pre-requisite for VMware NSX certification. Once Continue reading
Some common networking operations in Perl
A collection of various network- and socket API-related functions with code snippets.2014 in review
Looking back at 2014, it feels like a lot of progress was achieved in the past year in both the cloud infrastructure and NFV infrastructure markets. Some of that progress is technical, some is in terms of increased understanding of the key business and technical aspects. This post is my attempt to capture some changes I’ve observed from my particular vantage point.
This December marks the second anniversary of the acquisition of Contrail Systems by Juniper Networks. In the last year the Contrail team managed to deploy the Contrail network virtualization solution in several marquee customers; to solidify the image of the OpenContrail project as a production-ready implementation of the AWS VPC functionality; but, probably, more importantly to help transform attitudes at Juniper (and in the industry) regarding NFV.
In the late 90s and early naughts, the carrier wireline business went through a significant change with the deployment of provider managed virtual networks (using BGP L3VPN). From a business perspective, this was essentially outsourcing the network connectivity for distributed enterprises. Instead of a mesh of frame relay circuits managed by the enterprise; carriers provide a managed service that includes the circuit but also the IP connectivity. This is a service Continue reading
Will I Be Blogging Again?
Dan wrote in with a question:
Hey, I like your site as well… are you going to be doing any more posts? It just seems odd that your last blog post was the analyzation of the site and how it portends to your future work. anyway, good luck
I know it’s tacky to write a blog post about how you’re not writing enough blog posts… but here goes.
Yes, I will be blogging again. And I have lots of content ideas. And I’m actually itching to get back to writing. I’ve been working on something else for the past few months and I decided I couldn’t take that on and blog at the same time. So for now my writing is on hold, however I do see and respond to all comments in the articles and am reachable via email as well.
Thanks to everyone who reads and posts comments. I look forward to writing more posts in the new year!
Copyright Joel Knight. All Rights Reserved.
www.packetmischief.ca