BGP AS Numbers on MLAG Members
I got this question about the use of AS numbers on data center leaf switches participating in an MLAG cluster:
In the Leaf-and-Spine Fabric Architectures you made the recommendation to have the same AS number on all members of an MLAG cluster and run iBGP between them. In the Autonomous Systems and AS Numbers article you discuss the option of having different AS number per leaf. Which one should I use… and do I still need the EBGP peering between the leaf pair?
As always, there’s a bit of a gap between theory and practice ;), but let’s start with a leaf-and-spine fabric diagram illustrating both concepts:
Scaling EVPN Multi-Site Overlays using Route-Servers
Cisco’s EVPN Multi-Site it’s a great technology that allows us to achieve massive scale of an EVPN network. With the latest release, the official scalability numbers give us something in the realm of over 12000 VTEPs (512 VTEPs per site x 25 sites).
I’m in no way suggesting that you would need such a big topology and you definitely should segment way sooner you reach the limit, but still…
The main configuration requirement for the Multi-Site overlay is to have a full mesh of eBGP peering between all border gateways.
This has scalability drawbacks as usual. Not only each leaf will have ever growing number of peers which will soon grow out of control, but maybe, worse is the fact that after one site is added, every other site must be touched too.

To avoid a full mesh, for iBGP topologies we would be using a Route Reflector, but with eBGP that’s obviously not an option. So, instead of a RR they way to scale eBGP peerings is to leverage a Route-Server.

A Route-Server provides route reflection capabilities and as such it must ensure that NLRIs attributes like the Next Hop and route-targets aren’t changed.
In Cisco’s EVPN implementation, the Continue reading
The Hedge Episode 36: Rich Alderson and the Living Computer History Museum
The Living Computers History Museum and Labs was founding by Paul Allen to collect early computer systems and keep the constrained resource coding practices used on these systems alive. Over time it has developed into a living museum and lab, with hands-on access to some of the earliest examples of computing history. Rich Alderson joins us for this episode of the Hedge to describe the museum and its exhibits.
Central African Peering Forum: A Defining Moment for Peering and Interconnection

The first-ever Central African Peering Forum comes at a defining moment for Internet peering and interconnection. In the midst of the COVID-19 pandemic, countries have implemented measures to restrict people from moving from their homes, while only allowing essential movements and services.
But life cannot stop.
Kids still need to study and attend school. People still need to access financial services, conduct personal and business transactions, access government services, pay their taxes, and access health services. Most importantly, people need to access accurate and timely information. But now these services must be provided at a larger scale – via reliable Internet infrastructure. Moreover, some of this content and these services do not exist in digital format. They need to be created, sometimes in the language of local communities.
COVID-19 has uncovered gaps, missing elements, and key challenges, which need to be addressed so that life can smoothly transition to the new normal. Failing to address these challenges may result in severe socioeconomic consequences.
We are now a few months down the path since lockdown measures have been implemented in most countries. It is time to reflect on the lessons learnt so far, with respect to the reliability of the Internet Continue reading
Day Two Cloud 049: The Gritty Details Of Designing And Running A Private Cloud
On today's Day Two Cloud we tackle the practical aspects of private cloud, including designing the infrastructure and creating policies before you start racking gear, and why thinking about services is critical. Our guest is Brett Johnson, a Senior Consultant at VMware.
The post Day Two Cloud 049: The Gritty Details Of Designing And Running A Private Cloud appeared first on Packet Pushers.
Day Two Cloud 049: The Gritty Details Of Designing And Running A Private Cloud
On today's Day Two Cloud we tackle the practical aspects of private cloud, including designing the infrastructure and creating policies before you start racking gear, and why thinking about services is critical. Our guest is Brett Johnson, a Senior Consultant at VMware.The Latest Modern Innovation in Architecture
Architecture is constantly changing. New materials and ideas, as well as the needs of clients, drive new innovation in architecture. The latest innovation in architecture is that there are no defining standards, allowing for a wide variety of different styles and designs.
Modern architecture places emphasis on horizontal and vertical lines, as well as 90-degree angles. Modern architecture depends a great deal on sculpture forms, smooth surfaces, circular voids, and overhead shading systems.
Innovations in architecture include such features as large horizontal windows and ample natural light, as well as outdoors entertainment areas.
Architecture Innovations for Those on a Budget
In the last few years, one of the biggest innovations in architecture is the designing of tiny houses for those on a budget. These tiny homes need to be well thought out and the innovation comes in when architects have to come up with innovative ways to fit everything that normal homes have in a small space often no larger than a small bedroom.
Some of the innovations in this include such things as built in storage solutions and multifunctional furniture to make the most of the limited living space.
Another architecture innovation is the turning shipping containers into cute Continue reading
Using Technology In Disaster Response
Have you ever wondered how emergency communications get re-established after major disasters? Who are the people who rush in to enable first responders to do their jobs efficiently in the most trying of circumstances. In this episode we talk with Dustin Li and Andrew White of ITDRC (Information Technology Disaster Resource Center) to find out exactly what it takes to use technology in disaster response and why it is so important.
You can learn more about what ITDRC is doing as well as help out the cause at the following locations:
- https://itdrc.org/
- https://itdrc.org/projectconnect
- https://itdrc.org/donate
- https://volunteer.itdrc.org
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3.0 License
http://creativecommons.org/licenses/by/3.0/
The post Using Technology In Disaster Response appeared first on Network Collective.
Feedback: Data Center for Networking Engineers
When I started designing Data Center Infrastructure for Networking Engineers webinar I wanted to create something that would allow someone fluent in networking but not in adjacent fields like servers or storage to grasp the fundamentals of data center technologies, from server virtualization and containers to data center fabrics and storage protocols.
Here’s what a network architect said about the webinar:
Mutable References To ‘self’ In Rust’s Object Methods
Lately I’ve been working on graphics programming in Rust, as a continuation of my first steps with the language. As part of this work, I created a type I created called Vec3f, to hold cartesian coordinates for a given vector: #[derive(Copy, Clone, Debug)] struct Vec3f { x: f32, y: f32, z: f32 } In the natural course of this work, I needed to add certain methods for this type to allow me to perform calculations like cross product, and dot/scalar product.Full Stack Journey 042: How An IT Specialist Chooses Adjacent Competencies
David Klee is a SQL database expert, but he's also knowledgeable about virtualization, networking, and infrastructure. In today's Full Stack Journey podcast, host Scott Lowe talks with David about how and why IT specialists should be competent in other disciplines, how to decide which areas to branch out into, and how adjacent competencies enrich can enrich your specialization.
The post Full Stack Journey 042: How An IT Specialist Chooses Adjacent Competencies appeared first on Packet Pushers.
Full Stack Journey 042: How An IT Specialist Chooses Adjacent Competencies
David Klee is a SQL database expert, but he's also knowledgeable about virtualization, networking, and infrastructure. In today's Full Stack Journey podcast, host Scott Lowe talks with David about how and why IT specialists should be competent in other disciplines, how to decide which areas to branch out into, and how adjacent competencies enrich can enrich your specialization.Resolve internal hostnames with Cloudflare for Teams
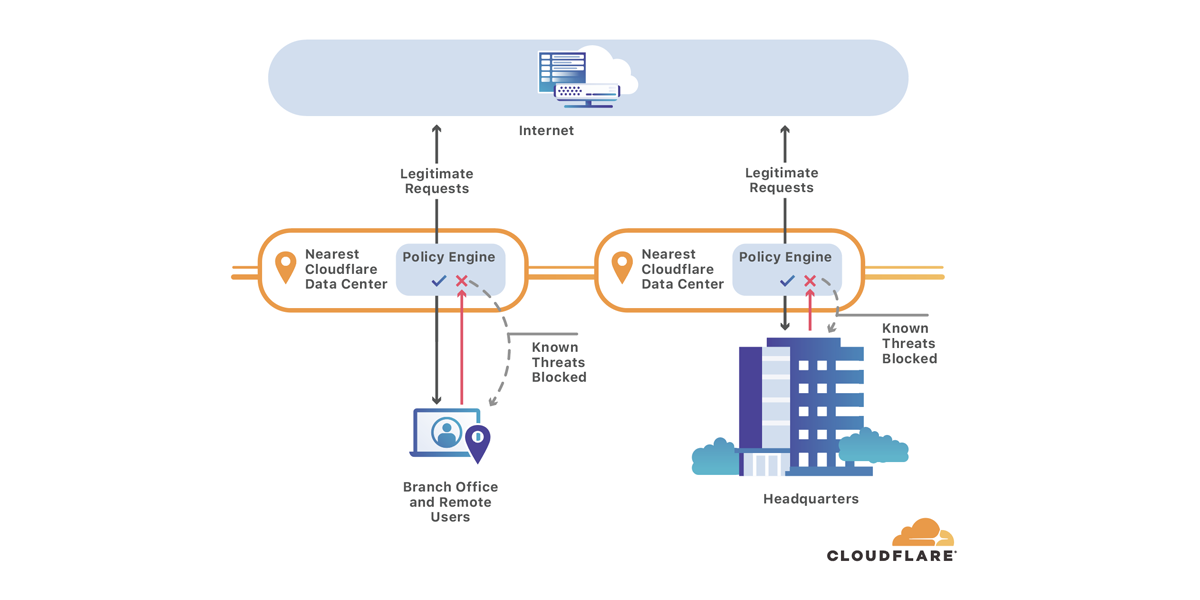
Phishing attacks begin like any other visit to a site on the Internet. A user opens a suspicious link from an email, and their DNS resolver looks up the hostname, then connects the user to the origin.
Cloudflare Gateway’s secure DNS blocks threats like this by checking every hostname query against a constantly-evolving list of known threats on the Internet. Instead of sending the user to the malicious host, Gateway stops the site from resolving. The user sees a “blocked domain” page instead of the malicious site itself.
As teams migrate to SaaS applications and zero-trust solutions, they rely more on the public Internet to do their jobs. Gateway's security works like a bouncer, keeping users safe as they navigate the Internet. However, some organizations still need to send traffic to internal destinations for testing or as a way to make the migration more seamless.
Starting today, you can use Cloudflare Gateway to direct end user traffic to a different IP than the one they originally requested. Administrators can build rules to override the address that would be returned by a resolver and send traffic to a specified alternative.
Like the security features of Cloudflare Gateway, the redirect function is Continue reading
Musings on IP Packet Reordering
During the Comparing Transparent Bridging and IP Routing part of How Networks Really Work webinar I said something along the lines of:
While packets should never be reordered in transit in transparent bridging, there’s no such guarantee in IP networks, and IP applications should tolerate out-of-order packets.
One of my regular readers who designs and builds networks supporting VoIP applications disagreed with that citing numerous real-life examples.
Of course he was right, but let’s get the facts straight first: