NSX Layer 2 VPN: Deploying for datacentre migrations
In my previous post, NSX Layer 2 VPN: Migrating workloads between Datacentres, I described the process and theory behind using an NSX Layer 2 VPN (L2VPN) to migrate workloads from a soon-to-be-retired VLAN backed datacentre, to an NSX Managed logical switch backed datacentre. In this post I will take you through the deployment of the L2VPN in my lab environment, following these high-level steps:
- Prepare the NSX Managed Site
- Deploy the Layer 2 VPN Server
- Prepare the Standalone Site
- Deploy the Layer 2 VPN Client
- Validate the Layer 2 VPN connectivity
Current lab environment
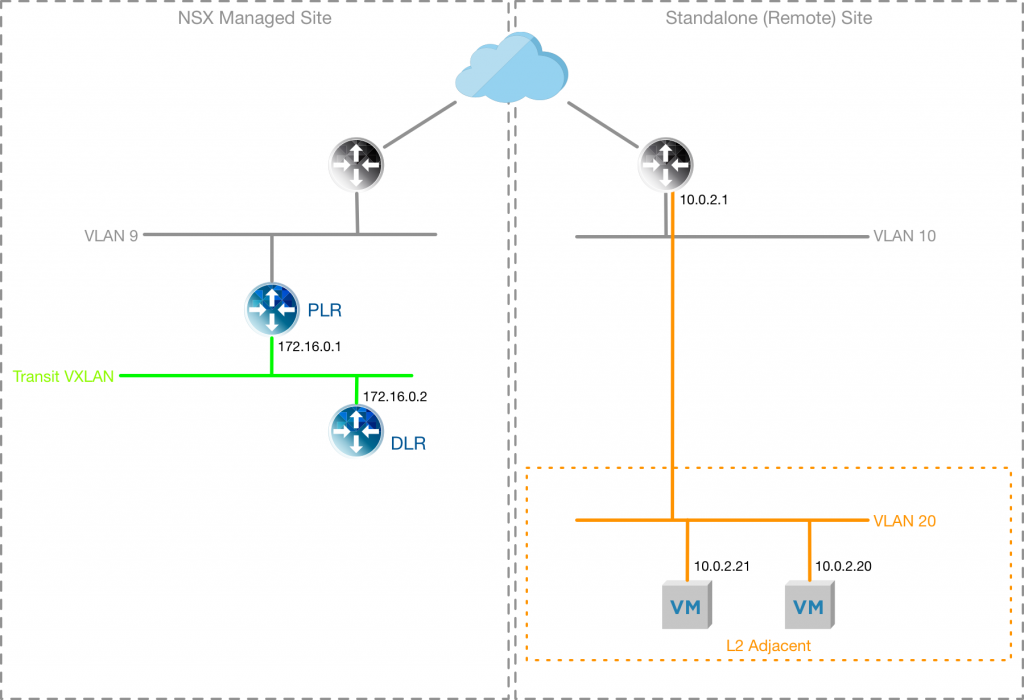
The Lab environment I am using currently reflects the diagram below, with two VMs deployed onto VLAN 20 within my “remote” site (my remote site is actually just a separate cluster from my “NSX Managed Site”, which is my workload cluster). In my NSX Managed site I have a Provider Logical Router (PLR) and Distributed Logical Router (DLR) configured.
Configure the NSX Managed Site
To prepare the NSX Managed Site the L2VPN-Server needs to be connected to a “trunk” interface, which allows multiple VLAN or Logical Switches to be configured as sub-interfaces, rather than having an interface in each VLAN/Logical Switch.
The Continue reading
NSX Layer 2 VPN: Migrating workloads between Datacentres
Selecting a migration strategy
As a consultant within the NSX PSO practice, one of the conversations that comes up with customers often is how NSX enables migration from a legacy datacentre to an NSX managed datacentre. This was the case with a customer recently who were looking to move out of a datacentre that was scheduled to be decommissioned. The problem was that the customer workloads needed to be migrated to a Logical Switch within the new datacentre without changing IP addressing, and with minimal downtime.
There are four approaches available to us with NSX for vSphere that might help solve this problem:
- Universal Logical Switching – we could deploy NSX to the remote site and extend L2 networks using Cross-vCenter NSX and Universal Logical Switches, then migrate the workload
- Native L2 Bridging – within the same datacentre we could use the NSX Distributed Logical Router native functionality to create a Layer 2 Bridge between a VLAN and a Logical Switch
- Hardware VTEP – using a compatible hardware device from a VMware Partner that acts as a VXLAN Tunnel Endpoint and can bridge between a VLAN and a Logical Switch
- Layer 2 VPN – using an NSX managed Edge, or Continue reading
What’s Your #TechConfession?

Think back to the first moment you fell in love with technology. Was it love at first deployment? What about developing code to trick your school’s bell system into letting your class out early? If you love all things technology, or you’re a technologist, then you should definitely put #TechConfessions, the podcast and YouTube playlist, on your radar.
#TechConfessions is a weekly podcast and web series that uncovers the deep, dark tech secrets of some of high tech’s finest minds. The series looks to expose the inner thoughts and forgotten stories of tech professionals. Hear from top tech pros as they divulge the early beginnings of their tech careers and proclaim their favorite software-defined moments. Get insights into what makes these tech leaders tick, and discover their long-burning passion for all things tech.
Director of Influence Marketing at VMware, Amy Lewis, one of the hosts of #TechConfessions, gives a voice to the professionals witnessing industry changes. Going from a hardware to a software state of mind happens differently for everyone. As the host of #TechConfessions, Amy digs deep to get the real backstory behind each individual’s transition into the world of software.
So far, season one Continue reading
Take Application Security to the Next Level – VMware and Carbon Black team up

Perhaps you’ve already begun to secure virtualized applications by rolling out micro-segmentation with NSX, but segmentation of the network is only the beginning to embracing least privilege in your environment.
VMware has teamed up with Carbon Black to go beyond network protection and change the way your data center endpoints themselves are protected. By leveraging the unique properties of virtualization and the hypervisor, along with next-generation detection and response, VMware and Carbon Black are able to shrink your environment’s attack surface and respond to detected threats with precision and speed.
Learn more here, and come see the solution in action at the Cloud Force Security road show (coming to a city near you)!
The post Take Application Security to the Next Level – VMware and Carbon Black team up appeared first on Network Virtualization.
Ready for Take-Off with Kubernetes, Cloud Foundry, and vSphere
A complex and diverse world
Singapore. Etihad. Wow. I always found it impressive when airlines were able to build a business and a brand without a significant domestic customer base to start off from. They instead focus on the global market, which is much more challenging. There is a competitive landscape of many players. There is the complexity of interconnecting a world of disparate lands and diverse customer cultures and preferences. An impressive feat.
The world of networking is becoming quite similar. From private, hybrid, and public cloud models, to increased use of SaaS, to the way SaaS and other apps are built using microservices architectures and containers, the landscape of islands to connect in an inherently secure and automated fashion is increasingly diverse and complex.
An app built to demonstrate this diversity
If the airline to networking analogy is lost on you, or you think it’s too much of a stretch, let me pull up the second reason I used planes in my symbolism. My brilliant colleague Yves Fauser built an app to demonstrate how NSX is connecting and securing this variety of new app frameworks, and it happens to be a “plane spotter” app. You may have already Continue reading
NSX-T: Multi-Tiered Routing Architecture
Multi-tenancy exists in some shape or form in almost every network. For an Enterprise network, it can be the separation of tenants based on different business units, departments, different security/network policies or compliance requirements. For a service provider, multi-tenancy can simply be separation of different customers (tenants).
Multi-tenancy doesn’t just allow separation of tenants, but also provides control boundaries as to who controls what. For instance, tenant administrators can control/configure the network and security policies for their specific tenants and a service provider administrator can either provide a shared service or provide inter-tenant or WAN connectivity.
In the logical routing world of NSX-T, this provider function can provide connectivity between the tenant logical networks and physical infrastructure. It can also provide inter-tenant communication or some shared services (like NAT, Load Balancer etc.) to the tenants.
In my previous post, NSX-T: Routing where you need it (Part 1), I discussed how NSX-T provides optimized E-W distributed routing and N-S centralized routing. In addition to that, NSX-T supports a multi-tiered routing model with logical separation between provider router functions and tenant routing functions. The concept of multi-tenancy is built into the routing model. The top-tier logical router is referred to Continue reading
Context-Aware Micro-segmentation – Remote Desktop Session Host Enhancements for Citrix
In a previous post by my colleague, Stijn, discussed the new changes to how NSX for vSphere 6.4 handles Remote Desktop Session Host, RDSH, systems with the Identity-based Firewall and context-aware micro-segmentation.
RDSH is an underlying technology from Microsoft that many vendors take advantage of to provide overlay management and application deployment technologies for. In this post, we’re going to discuss how NSX 6.4 and the new changes to support RDSH hosts works with Citrix XenApp systems.
Citrix XenApp can provide multiple users the ability to connect to a single system to access their applications using the RDSH technology. These users can be of the same type, for example all HR users, or of multiple types, HR and Engineering users. NSX has supported User Identity based firewalling for Virtual Desktops since the 6.0 release, but it did not address RDSH in which multiple user sessions are connecting to the same host This meant less flexibility in controlling what users could access data center application servers without isolating one set of users to one RDSH server. This model created a very rigid architecture for XenApp customers to follow, which brought about the use of Continue reading
Introducing VMware NSX-T Reference Design

Available now is the VMware NSX-T Reference Design Guide, a deployment path to adopting NSX with diverse multi-domain workload requirements – multi-cloud (private/public), multi-hypervisor, and multiple application frameworks (VMs, PaaS and containers).
Since VMware acquired Nicira almost five years ago, NSX for vSphere has become de-facto standard for private cloud solutions, delivering key use cases in private cloud – namely security, automation and application continuity. Since then, we’ve witnessed our customers datacenter and workload requirements changing; therefore, the demand for a platform that not only can deliver current private cloud requirements, but now many enterprises are looking for integration with the likes of cloud native apps, public/hybrid cloud, and other compute domains covering multiple hypervisors.
VMware NSX-T was introduced last year to meet the demands of the containerized workload, multi-hypervisor and multi-cloud. The NSX-T platform is focused on a diverse set of use cases – from private to public, traditional (multi-tiered architecture) to container (microservices architecture) based apps, automation and monitoring of security at IaaS, to programmatic devops workloads in PaaS and CaaS environments. It is very important to start with an understanding of NSX-T architecture and its components, and some topics (ex. routing) have been discussed Continue reading
Context-Aware Micro-segmentation – Remote Desktop Session Host Enhancements for VMware Horizon
In a previous post my colleague, Stijn, discussed the enhancements to how NSX for vSphere 6.4 handles Remote Desktop Session Host, RDSH, systems with the Identity-based Firewall and Context-Aware Micro-segmentation.
Remote Desktop Services is an underlying technology from Microsoft that many vendors take advantage of to provide overlay management and application deployment technologies for. In this post, we’re going to discuss how NSX for vSphere 6.4 allows customers to run RDS hosts with granular security for VMware Horizon systems.
VMware Horizon can provide multiple users the ability to connect to a single system to access their applications using the RDSH technology. These users can be of the same type, for example all HR users, or of multiple types, HR and Engineering users. In previous versions of NSX, it was not possible to individually secure user sessions and create Distributed Firewall (DFW) rule sets according to the user session logged into an RDSH server. This meant less flexibility in controlling what users could access data center application servers without isolating one set of users to one RDSH server. This model created a very rigid architecture for Horizon customers to follow.
Horizon allows customers Continue reading
Context-Aware Micro-segmentation – an innovative approach to Application and User Identity Firewall
Summary: With Context-awareness, NSX for vSphere 6.4 enables customers to enforce policy based on Application and Protocol Identification and expands the Identity Firewall support to Multiple User Sessions.
A few weeks ago, VMware released version 6.4 of NSX for vSphere. The 6.4 release brings many new features, with Context-awareness being key from a security perspective. Micro-segmentation enables East-West security controls, and is a key building block to a secure datacenter. Context-awareness builds-on and expands Micro-segmentation by enabling customers even more fine-grained visibility and control. NSX has supported the use infrastructure or application-centric constructs such as Security Groups based on criteria like VM name or OS version, or Dynamic Security Tags describing things like the workload function, the environment it’s deployed in, or any compliance requirements the workload falls under, enabling fine-grained control and allowing customers to automate the lifecycle of a security policy from the time an application is provisioned to the time it’s decommissioned. Prior to 6.4, rules with infrastructure or application-centric grouping constructs on the Management plane, are eventually translated to 5-tuple based rules in the dataplane.
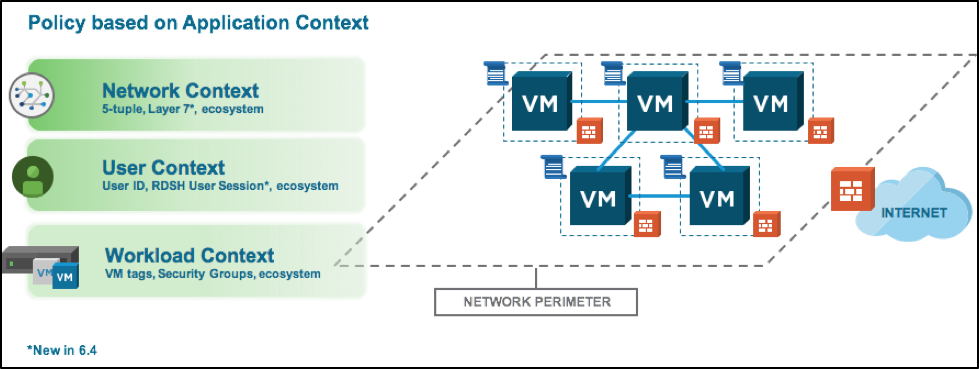 Figure: NSX drives policy based on Network, User and Workload Context
Figure: NSX drives policy based on Network, User and Workload Context
A crucial aspect of Context-awareness Continue reading
Top 5 From The Last 3 Months

In today’s day and age, content is king. It’s nearly impossible to keep up with the deluge of information, especially in the tech space where change is constant. We’re aware that the struggle is real. To keep you up-to-date on the latest and greatest in networking, we’ve compiled a round-up blog of the top posts from the past few months.
VMware Closes Acquisition of VeloCloud Networks
In December, VMware NSX completed its acquisition of VeloCloud Networks, bringing their industry-leading, cloud-delivered SD-WAN solution to our own growing software-based networking portfolio. The acquisition of VeloCloud significantly advances our strategy of enabling customers to run, manage, connect and secure any application on any cloud to any device. Learn all about the acquisition from SVP and GM, Networking and Security Business Unit Jeff Jennings.
VMware SDDC with NSX Expands to AWS
With VMware Cloud on AWS, customers can now leverage the best of both worlds – the leading compute, storage and network virtualization stack enabling enterprises for SDDC can now all be enabled with a click of a button on dedicated, elastic, bare-metal and highly available AWS infrastructure. Bonus: because it’s a managed service by VMware, customers can focus on the Continue reading
Rapid Micro-segmentation using Application Rule Manager Recommendation Engine
Customers understand the need for micro-segmentation and benefits it provides to enhance the security posture within their datacenter. However, one of the challenges for a Security admin is how to define micro-segmentation policies for applications owned and managed by application teams. This is even more challenging especially when you have tens or hundreds of unique applications in your data center, all of which use different port and protocols and resources across the cluster. The traditional manual perimeter firewall policy modeling may not be ideal and may not be able to scale for the micro-segmentation of your applications as it would be error-prone, complex and time consuming.
NSX addresses the how & where to start micro-segmentation challenge by providing the built-in tool called Application Rule Manager (ARM), to automate the application profiling and the onboarding of applications with micro-segmentation policies. NSX ARM has been part of NSX, since the NSX 6.3.0 release but here we will talk about Application Rule Manager (ARM) enhancement, Recommendation Engine, introduced as part of NSX 6.4.0 release. This enhancement allows you to do Rapid Micro-segmentation to your data center application by recommending “ready to consume” workload grouping & firewall policy rules.
Free 5-Part Webcast Series on NSX

Mark your calendars now for this free VMware NSX: Things You Need to Know webcast series presented by VMware Education Services. Each 60-minute session is delivered by VMware Certified Instructors and offered at 3 different times so you can choose what works for your schedule.
- Feb 1: Simplify Network Provisioning with Logical Routing and Switching using VMware NSX
- Feb 22: Automate Your Network Services Deployments with VMware NSX and vRealize Automation
- Mar 8: Design Multi-Layered Security in the Software-Defined Datacenter using VMware vSphere 6.5 and VMware NSX 6.4
- Mar 29: Advanced VMware NSX: Demystifying the VTEP, MAC, and ARP Tables
- Apr 19: That Firewall Did What? Advanced Troubleshooting for the VMware NSX Distributed Firewall
RSVP for one or all five here. (See below for more info.)
Feb 1:
Simplify Network Provisioning with Logical Routing and Switching using VMware NSX
Did you know it’s possible to extend LANs beyond their previous boundaries and optimize routing in the data center? Or decouple virtual networkoperations from your physical environment to literally eliminate potential network disruptions for future deployments? Join us to learn how VMware NSX can make these a reality. We’ll also cover the networking components of NSX to Continue reading
VMware NSX for vSphere 6.4 Eases Operations, Improves Application Security with Context
Summary: Generally available today, VMware NSX for vSphere 6.4 raises the bar for application security and planning, and introduces context-aware micro-segmentation
For those working in security, thinking and talking about the cyber threats in the world is a constant, a necessary evil. So, for a moment, let’s summon a better time to our memory. Remember when breaches didn’t keep us up at night? The threat of a breach didn’t hang over our heads with an associated cost of millions of dollars and the privacy of our users. In fact, it did, but they weren’t frequent or public enough to cause the awakening that they do today. We put up a wall at the perimeter to keep the bad guys out, and prayed.
OK, back to modern times. Today, we know the story is much different, for better and for worse. Breaches are more prevalent, but our defenses are more sophisticated and more importantly, they’re continuously evolving (just like the breaches). One major piece of this newer defense picture is micro-segmentation. With micro-segmentation, security policies traditionally only enforced at the perimeter are now brought down to the application. Micro-segmentation has gained massive traction and entered the mainstream, with most cloud Continue reading
NSX-T: OpenAPI and SDKs
Nowadays everything is about automation. Organizations are moving away from the traditional static infrastructure to full automation and here the need of NSX is significant. There are many use-cases for NSX, but the common in all of them is that they all need to be automated.
VMware is investing heavenly for different tools to ease the automation aspect of NSX but in order to take full advantage of it one need to understand what happens under the hood. It is also important if someone wants to build their own custom automation tool or CMP (Cloud Management Platform). Many existing solutions like Openstack, Kubernetes, vRO and so on automate NSX-T using different plugins. In fact, those plugins are sending REST API calls to NSX Manager in order to automate logical topology CRUD(Create, Read, Update, Delete) operations.
Based on our experience we decided that NSX-T APIs will be based on JSON format following OpenAPI standard. The use of Open APIs is to enable third party developers to build applications and services around NSX-T by standardising on how REST APIs are described. This means one can use standard tools like Swagger to read and use those APIs. Below is a quick example from my Mac on Continue reading
NSX-T: Routing where you need it (Part 2, North-South Routing)
In the first part of this blog series, NSX-T: Routing where you need it (Part 1), I discussed how East-West (E-W) routing is completely distributed on NSX-T and how routing is done by the Distributed Router (DR) running as a kernel module in each hypervisor.
In this post, I will explain how North-South (N-S) routing is done in NSX-T and we will also look at the ECMP topologies. This N-S routing is provided by the centralized component of logical router, also known as Service Router. Before we get into the N-S routing or packet walk, let’s define Service Router.
Service Router (SR)
Whenever a service which cannot be distributed is enabled on a Logical Router, a Service Router (SR) is instantiated. There are some services today on NSX-T which are not distributed such as:
1) Connectivity to physical infrastructure
2) NAT
3) DHCP server
4) MetaData Proxy
5) Edge Firewall
6) Load Balancer
Let’s take a look at one of these services (connectivity to physical devices) and see why a centralized routing component makes sense for running this service. Connectivity to physical topology is intended to exchange routing information from NSX domain to external networks (DC, Campus or Continue reading
VMware NSX Micro-segmentation – Horizon 7
Organizations that embark on the journey of building our virtual desktop environments, are taking traditionally external endpoints and bringing them into the data center. These endpoints are now closer and most times, reside on the same networking infrastructure as the backend application servers that they may access. These endpoints run Windows or even Linux desktop operating systems with multiple end-users that can access them. Malicious attacks that would traditionally take place outside the data center should an end-user find their desktop or laptop machine infected, could now take place on their virtual desktops inside the data center. With physical equipment, it’s easy to isolate the physical desktop or laptop and remediate the attack. Securing virtual desktop environments requires a different approach, but not one that’s unattainable. Securing an end user computing deployments is one of the primary security use cases for VMware NSX and can help provide a layered approach to securing virtual desktop workloads in the data center.
The NSX platform covers several business cases for securing an end user computing deployment. Each of these use cases, helps provide a multi-layered approach to ensure end user endpoints are as secure as possible in the Continue reading
Enhancing NSX with Check Point vSEC
While VMware NSX enables micro-segmentation of the Software Defined Data Center, it mostly polices traffic in layers 3 and 4, with only limited application level (layer 7) support. Sometimes additional layers of protection are needed for use cases such as Secure DMZ or meeting regulatory compliance requirements like PCI, in which case partner solutions can be added to the platform, with traffic steered into the supplemental solution prior to reaching the vSwitch (virtual wire). The resulting combination is high throughput due to the scale-out nature of NSX, but can also provide deep traffic analysis from the partner solution.
The usual enemy of deep traffic inspection in the data center is bandwidth. NSX addresses this issue, micro-segmentation security policy is zero trust – only traffic explicitly permitted out of a VM can pass, then steering policy to 3rd party solutions can be designed in order that bulk protocols such as storage and backup bypass them, leaving a more manageable amount of traffic for Check Point vSEC to provide IPS, anti-virus and anti-malware protection on, including Check Point’s Sandblast Zero-Day Protection against zero day attacks.

The connection between vSEC and NSX enables dynamic threat tagging, where traffic from an VM reaches Continue reading
“Building NSX Powered Clouds and Data Centers for SMBs” is available now
I am honored and humbled to announce my new book “Building NSX Powered Clouds and Data Centers for Small and Medium Businesses”.
This is a concise book that provides step by step information to design and deploy NSX in Small and Medium size data centers. My aim for writing this book is to give architects and engineers the necessary tools and techniques to transform their data center from legacy architecture to software defined (SDN) architecture. The SDN architecture is the foundation to build the private cloud.
The book has about 90 pages covering following topics:
- NSX and SMB data center introduction
- Important vSphere design considerations
- vSphere cluster design and NSX deployment models
- NSX individual component design and deployment considerations
- NSX Operations: monitoring and troubleshooting
- Growing NSX deployments
Many technology vendors tend to focus efforts in the large data center space, the fact remains that the small/medium business (SMB) space represents a substantial part of the IT marketplace.
The book is available to purchase from NSX Store.
Electronic version of the book can be downloaded from here.
The post “Building NSX Powered Clouds and Data Centers for SMBs” is available now appeared first on Network Virtualization.
VMware Cloud on AWS with NSX: Communicating with Native AWS Resources
If you haven’t already, please read my prior two blogs on VMware Cloud on AWS: VMware SDDC with NSX Expands to AWS and VMware Cloud on AWS with NSX – Connecting SDDCs Across Different AWS Regions; also posted on my personal blog at humairahmed.com. The prior blogs provide a good intro and information of some of the functionality and advantages of the service. In this blog post I expand the discussion to the advantages of VMware Cloud on AWS being able to communicate with native AWS resources. This is something that would be desired if you have native AWS EC2 instances you want VMware Cloud on AWS workloads to communicate with or if you want to leverage other native AWS services like AWS S3 VPC Endpoint or RDS. Continue reading