eBrief: Minimizing Security Challenges in the Cloud
 In this SDxCentral eBrief, we look at the types of security threats that are becoming more prevalent and examine some of the latest techniques and tools that enterprises are employing to make sure that their business assets in the cloud are secure.
In this SDxCentral eBrief, we look at the types of security threats that are becoming more prevalent and examine some of the latest techniques and tools that enterprises are employing to make sure that their business assets in the cloud are secure.
Now You Can Setup Centrify, OneLogin, Ping and Other Identity Providers with Cloudflare Access

We use Cloudflare Access to secure our own internal tools instead of a VPN. As someone that does a lot of work on the train, I can attest this is awesome (though I might be biased). You can see it in action below. Instead of having to connect to a VPN to reach our internal jira, we just login with our Google account and we are good to go:

Before today, you could setup Access if you used GSuite, Okta or Azure AD to manage your employee accounts. Today we would like to announce support for two more Identity Providers with Cloudflare Access: Centrify and OneLogin.
We launched Cloudflare Access earlier this year and have been overwhelmed by the response from our customers and community. Customers tell us they love the simplicity of setting up Access to secure applications and integrate with their existing identity provider solution. Access helps customers implement a holistic solution for both corporate and remote employees without having to use a VPN.
If you are using Centrify or OneLogin as your identity provider you can now easily integrate them with Cloudflare Access and have your team members login with their accounts to securely reach your internal Continue reading
Networking Gets Entangled in Geo-Political Feuds
 ZTE might look to judicial remedies after the U.S. ban; Huawei lays off its Washington, D.C. liason; and Twitter bans ads from Kaspersky Labs.
ZTE might look to judicial remedies after the U.S. ban; Huawei lays off its Washington, D.C. liason; and Twitter bans ads from Kaspersky Labs.
Will Artificial Intelligence Be Used for Good or Evil?
 As AI and ML begin to reach their full potential, the race is on between network administrators and attackers to implement the technologies into their procedures, for better or for worse.
As AI and ML begin to reach their full potential, the race is on between network administrators and attackers to implement the technologies into their procedures, for better or for worse.
Introducing a New MANRS IXP Programme for Routing Security
- Facilitate Continue reading
OMG The Stupid It Burns
This article, pointed out by @TheGrugq, is stupid enough that it's worth rebutting.“The views and opinions expressed are those of the author and not necessarily the positions of the U.S. Army, Department of Defense, or the U.S. Government.” <- I sincerely hope so…— the grugq (@thegrugq) April 22, 2018
“the cyber guns of August” https://t.co/xdybbr5B0E
Micro-segmentation Starter Kit
Traditional security solutions are designed to protect the perimeter. As applications and data are becoming increasingly distributed, they are often spanning not only multiple sites, but also multiple clouds. This is making it harder to identify where the perimeter actually is in order to secure it. But even if the perimeter can be reliably identified, securing it alone is not enough. The east-west traffic inside of the environment must be secured as well. VMware NSX makes security an intrinsic part of the infrastructure that applications and data live on, rather than a bolted-on afterthought; security is built in Day 0.
VMware created a Micro-segmentation Starter Kit to help you get started with securing your network from Planning to Enforcement to Troubleshooting. Each kit includes 6 CPUs of both NSX ADV and vRealize Network Insight ADV at 25% off the global list price.
- Plan: Take the manual and subjective process out of determining what security policies to put in place and where. vRealize Network Insight provides a comprehensive net flow assessment and analysis to model and recommend security groups and firewall rules across your physical, virtual, and cloud environments.

- Enforce: Micro-segmentation, the implementation of security policy Continue reading
It’s Time For Security Apprenticeships

Breaking into an industry isn’t easy. When you look at the amount of material that is necessary to learn IT skills it can be daunting and overwhelming. Don’t let the for-profit trade school ads fool you. You can’t go from ditch digger to computer engineer in just a few months. It takes time and knowledge to get there.
However, there is one concept in non-technical job roles that feels very appropriate to how we do IT training, specifically for security. And that’s the apprenticeship.
Building For The Future
Apprenticeship is a standard for electricians and carpenters. It’s the way that we train new people to do the work of the existing workforce. It requires time and effort and a lot of training. But, it also fixes several problems with the current trend of IT certification:
- You Can’t Get a Job Without Experience – Far too often we see people getting rejected for jobs at the entry level because they have no experience. But how are they supposed to get the experience without doing the job? IT roles paradoxically require you to be cheap enough to hire for nothing but expect you to do the job on day one. Apprenticeships fix Continue reading
Keeping Drupal sites safe with Cloudflare’s WAF

Cloudflare’s team of security analysts monitor for upcoming threats and vulnerabilities and where possible put protection in place for upcoming threats before they compromise our customers. This post examines how we protected people against a new major vulnerability in the Drupal CMS, nicknamed Drupalgeddon 2.
Two weeks after adding protection with WAF rule ID D0003 which mitigates the critical remote code execution Drupal exploit (SA-CORE-2018-002/CVE-2018-7600), we have seen significant spikes of attack attempts. Since the 13th of April the Drupal security team has been aware of automated attack attempts and it significantly increased the security risk score of the vulnerability. It makes sense to go back and analyse what happened in the last seven days in Cloudflare’s WAF environment.
What is Drupalgeddon 2
The vulnerability potentially allows attackers to exploit multiple attack vectors on a Drupal site, which could make a site completely compromised.
Drupal introduced renderable arrays, which are a key-value structure, with keys starting with a ‘#’ symbol, that allows you to alter data during form rendering. These arrays however, did not have enough input validation. This means that an attacker could inject a custom renderable array on one of these keys in the form structure.
Continue reading
Cisco Teases SD-WAN Security Bundle
 An integrated SD-WAN security product would likely involve at least three Cisco technologies: Viptela SD-WAN, Meraki network automation, and Umbrella cloud security.
An integrated SD-WAN security product would likely involve at least three Cisco technologies: Viptela SD-WAN, Meraki network automation, and Umbrella cloud security.
U.S. Leads the World in the Origination of DDoS Attacks, Says CenturyLink Report
 CenturyLink tracks botnets and the C2 servers they communicate with to thwart distributed denial of service attacks.
CenturyLink tracks botnets and the C2 servers they communicate with to thwart distributed denial of service attacks.
McAfee CEO Warns Security Breach Fatigue Could Lead to ‘Digital 9-11’
 One in four organizations using public cloud has had their data stolen, according to McAfee’s latest cloud security report.
One in four organizations using public cloud has had their data stolen, according to McAfee’s latest cloud security report.
Cisco’s John Stewart Calls on Security Sector to ‘Stop the Madness’
 Cybercrime will be a $6 trillion business by 2021, up from $3 trillion in 2016.
Cybercrime will be a $6 trillion business by 2021, up from $3 trillion in 2016.
Qualcomm’s Vision Intelligence IoT Platform Features an AI Engine
 The chip company’s IoT strategy includes pushing processing to the edge, instead of the cloud.
The chip company’s IoT strategy includes pushing processing to the edge, instead of the cloud.
No More Meltdowns: Cisco and Microsoft Will Use Intel’s Silicon-Level Security
![]() An integration with Cisco Tetration will combine platform telemetry with machine learning algorithms to improve threat detection.
An integration with Cisco Tetration will combine platform telemetry with machine learning algorithms to improve threat detection.
Google Kaniko Tool Wrenches on Container Privilege Concern
 The open source tool allows for the building of a container image without providing privileged root access.
The open source tool allows for the building of a container image without providing privileged root access.
mmproxy – Creative Linux routing to preserve client IP addresses in L7 proxies
In previous blog post we discussed how we use the TPROXY iptables module to power Cloudflare Spectrum. With TPROXY we solved a major technical issue on the server side, and we thought we might find another use for it on the client side of our product.
This is Addressograph. Source Wikipedia
When building an application level proxy, the first consideration is always about retaining real client source IP addresses. Some protocols make it easy, e.g. HTTP has a defined X-Forwarded-For header[1], but there isn't a similar thing for generic TCP tunnels.
Others have faced this problem before us, and have devised three general solutions:
(1) Ignore the client IP
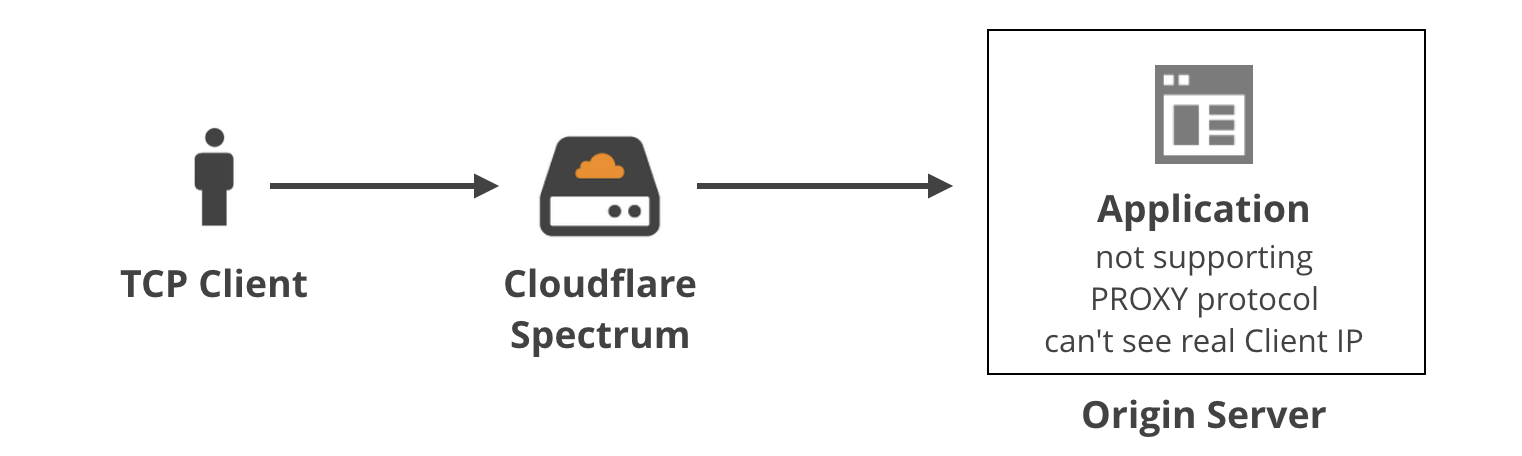
For certain applications it may be okay to ignore the real client IP address. For example, sometimes the client needs to identify itself with a username and password anyway, so the source IP doesn't really matter. In general, it's not a good practice because...
(2) Nonstandard TCP header
A second method was developed by Akamai: the client IP is saved inside a custom option in the TCP header in the SYN packet. Early implementations of this method weren't conforming to any standards, e.g. using option field 28 Continue reading
Microsoft’s Smith Calls for Digital Geneva Convention, Launches Cybersecurity Tech Accord
 War and the battlefield themes dominated the opening keynotes at the annual RSA Conference 2018, just a day after a joint U.S. and U.K. alert warned that Russians are targeting American and British organizations’ network infrastructure devices, such as routers.
War and the battlefield themes dominated the opening keynotes at the annual RSA Conference 2018, just a day after a joint U.S. and U.K. alert warned that Russians are targeting American and British organizations’ network infrastructure devices, such as routers.