Palo Alto Networks Buys Endpoint Security Startup Secdo
 This is the third Israeli security startup that Palo Alto Networks has purchased.
This is the third Israeli security startup that Palo Alto Networks has purchased.
Container Security Should Be Simple, Serverless Is More of a Challenge
 New entrants, updates, and money continue to flow into the space, but organizations sometimes ignore the basics.
New entrants, updates, and money continue to flow into the space, but organizations sometimes ignore the basics.
Zyxel Chooses Enea to Boost Application Visibility on Its UTM Products
 Zyxel embedded Enea’s deep packet inspection engine within its UTM products to analyze traffic in real-time and identify application protocols.
Zyxel embedded Enea’s deep packet inspection engine within its UTM products to analyze traffic in real-time and identify application protocols.
Luminate Launches Secure Access Cloud Based on Google’s BeyondCorp
 It shifts access controls from the network perimeter to individual devices and users, allowing employees to work more securely from any location without a VPN.
It shifts access controls from the network perimeter to individual devices and users, allowing employees to work more securely from any location without a VPN.
Cisco Adds Tetration SaaS, Virtual Deployment Options
 The company also launched an integrated data center security architecture that includes four Cisco products.
The company also launched an integrated data center security architecture that includes four Cisco products.
Security Vendor Carbon Black Files for $100 Million IPO
 The security vendor posted $116.2 million in revenue for fiscal 2017, up about 39 percent over 2016.
The security vendor posted $116.2 million in revenue for fiscal 2017, up about 39 percent over 2016.
RSA Preview: Companies Are Still Wrestling With AI’s Role in Cybersecurity
 Organizations are automating security incident investigations and making use of deception grids to identify breaches more quickly.
Organizations are automating security incident investigations and making use of deception grids to identify breaches more quickly.
Verizon Data Breach Report Finds Ransomware Attacks Double Since 2017
 Organized crime groups account for 50 percent of all the attacks analyzed, with nation-state or state-affiliated actors involved in 12 percent.
Organized crime groups account for 50 percent of all the attacks analyzed, with nation-state or state-affiliated actors involved in 12 percent.
Mythology about security…
Ed Felton tweeted a few days ago: “Often hear that the reason today’s Internet is not more secure is that the early designers failed to imagine that security could ever matter. That is a myth.”
This is indeed a myth. Much of the current morass can be laid at the feet of the United States government, due to its export regulations around cryptography.
I will testify against the myth. Bob Scheifler and I started the X Window System in 1984 at MIT, which is a network transparent window system: that is, applications can reside on computers anywhere in the network and use the X display server. As keyboard events may be transmitted over the network, it was clear to us from the get-go that it was a security issue. It is in use to this day on Linux systems all over the world (remote X11 access is no longer allowed: the ssh protocol is used to tunnel the X protocol securely for remote use). By sometime in 1985 or 1986 we were distributing X under the MIT License, which was developed originally for use of the MIT X Window System distribution (I’d have to go dig Continue reading
Industrial IoT Group Releases Security Maturity Model
 The white paper helps companies meet industrial Internet of Things security goals and prioritize spending.
The white paper helps companies meet industrial Internet of Things security goals and prioritize spending.
Container Security through Segregation
One of my readers sent me a container security question after reading the Application Container Security Guide from NIST:
We are considering segregating dev/test/prod environments with bare-metal hardware. I did not find something in the standard concerning this. What should a financial institution do in your opinion?
I am no security expert and know just enough about containers to be dangerous, but there’s a rule that usually works well: use common sense and identify similar scenarios that have already been solved.
Read more ...Aella Data Emerges From Stealth, Launches AI-Based Threat Detection
 The security startup, founded by former Juniper, Fortinet, Barracuda, and Aerohive executives, exited stealth mode with its AI-based breach detection platform.
The security startup, founded by former Juniper, Fortinet, Barracuda, and Aerohive executives, exited stealth mode with its AI-based breach detection platform.
Huawei Shoots Back at FCC Proposal That Threatens Its Rural Biz
 The FCC wants to ban any spending from the Universal Service Fund on networking equipment that could pose a security threat.
The FCC wants to ban any spending from the Universal Service Fund on networking equipment that could pose a security threat.
New RFC 8360 – RPKI Validation Reconsidered – Offers Alternative Validation Procedures to Improve Routing Security
RFC 8360, Resource Public Key Infrastructure (RPKI) Validation Reconsidered, is now published in the RFC libraries.
What is RPKI?
Resource Public Key Infrastructure (RPKI) aims to improve the security of the Internet routing system, specifically the Border Gateway Protocol (BGP), by establishing a hierarchy of trust for BGP routes. Today, most organizations simply trust that routing updates they get are sent by authorized senders. This is how bad actors and misconfigurations can cause massive routing issues. With RPKI, the receiving organization can verify that the sending organization is authorized to send the routing update.
RPKI works by issuing X.509-based resource certificates to holders of IP addresses and AS numbers to prove assignment of these resources. These certificates are issued to Local Internet Registries (LIRs) by one of the five Regional Internet Registries (RIRs) who allocate and assign these resources in their service regions.
What Does This RFC Do?
In the IETF, participants have been discussing issues that may arise when resources move across registries. The problem happens when a subordinate certificate “over-claims” resources compared to its parent. According to the standard validation procedure specified in RFC 6487, the whole branch beneath would be invalidated. The closer to Continue reading
Infoblox Updates Cloud-Based DNS Security Offering To Block Malicious Sites
Infoblox updates its cloud-based DNS security service to run without agent software and improves its ability to filter unwanted and malicious sites.RSA Adds Security Orchestration, Automation to SIEM Platform
 RSA today rolled out an orchestration and automation tool for its SIEM product. It also reached a deal to acquire Fortscale, a behavioral analytics startup.
RSA today rolled out an orchestration and automation tool for its SIEM product. It also reached a deal to acquire Fortscale, a behavioral analytics startup.
Argo Tunnel: A Private Link to the Public Internet
Photo from Wikimedia Commons
Today we’re introducing Argo Tunnel, a private connection between your web server and Cloudflare. Tunnel makes it so that only traffic that routes through Cloudflare can reach your server.
You can think of Argo Tunnel as a virtual P.O. box. It lets someone send you packets without knowing your real address. In other words, it’s a private link. Only Cloudflare can see the server and communicate with it, and for the rest of the internet, it’s unroutable, as if the server is not even there.
How this used to be done
This type of private deployment used to be accomplished with GRE tunnels. But GRE tunnels are expensive and slow, they don’t really make sense in a 2018 internet.
GRE is a tunneling protocol for sending data between two servers by simulating a physical link. Configuring a GRE tunnel requires coordination between network administrators from both sides of the connection. It is an expensive service that is usually only available for large corporations with dedicated budgets. The GRE protocol encapsulates packets inside other packets, which means that you will have to either lower the MTU of your origin servers, or have your router do Continue reading
Combating Ransomware in Multi-Cloud Environments
 The rapidly evolving threat environment, coupled with a more vulnerable enterprise network signals a paradigm shift in how organizations will protect data residing on multi-cloud systems.
The rapidly evolving threat environment, coupled with a more vulnerable enterprise network signals a paradigm shift in how organizations will protect data residing on multi-cloud systems.
Juniper Networks’ Security Strategy: Unify Everything, Keep it Open
 Juniper Networks security team wants to unify threat detection, automated enforcement, and mitigation in a unified platform and integrate with other technology vendors to support non-Juniper gear.
Juniper Networks security team wants to unify threat detection, automated enforcement, and mitigation in a unified platform and integrate with other technology vendors to support non-Juniper gear.
Extend your security view from the data center to the edge
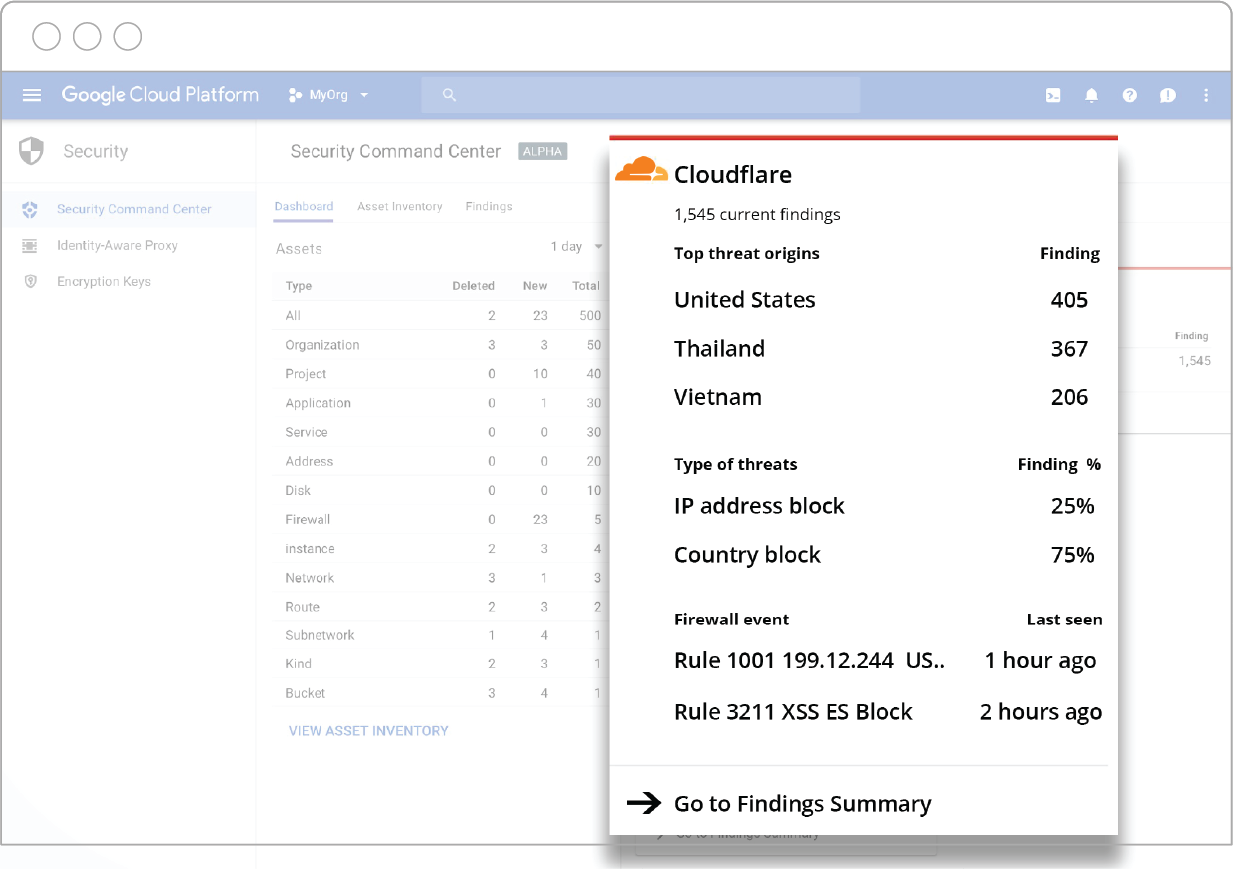
How great would it be to have a dashboard with a holistic view of threats, malicious server activity, vulnerabilities, sensitive data access levels and a daily scan of resources across all of your applications and services? Now you can.
Cloudflare is thrilled to announce its integration with Cloud Security Command Center (Cloud SCC) for Google Cloud Platform: A security and data risk platform helping enterprises gather data, identify threats, and act on them before they result in business damage or loss.
The advantage of the Cloud SCC solution is that it surfaces insights from both the Google Cloud Platform, as well as Cloudflare’s edge, in a unified dashboard.
What Cloudflare data is visible within the Cloud SCC dashboard?
Through Cloudflare’s API endpoints, data is pushed to Google’s Cloud SCC dashboard and domain name information mapped to the appropriate Google Cloud asset. Cloudflare’s branded card in the Cloud SCC dashboard is automatically populated with a summary of top theat origins, top types of threats, and latest Web Application Firewall (WAF) events.
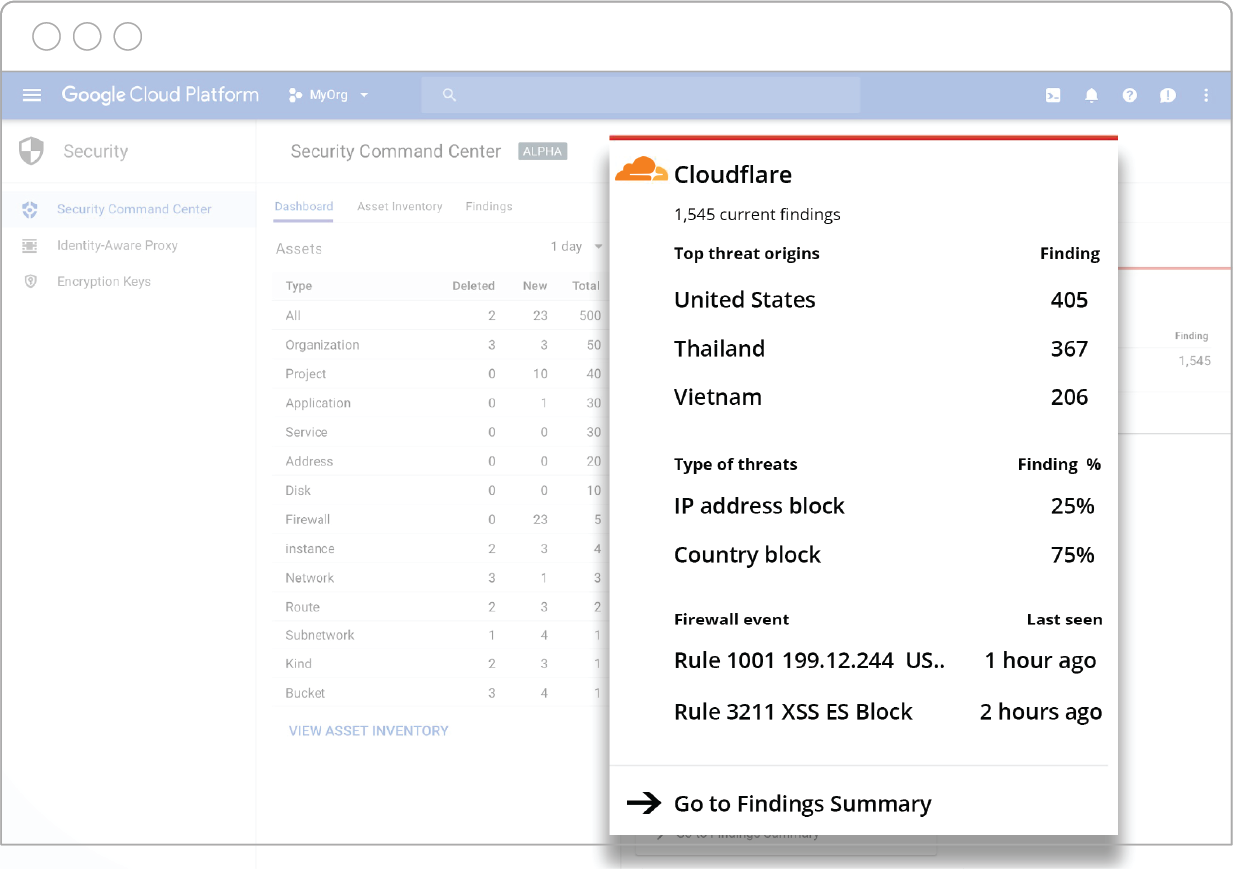
To view a full list of Cloudflare events, click on the Cloudflare card in Cloud SCC and it will take you to a “Cloudflare Findings” page. From there, you can Continue reading