NTT Launches SD-WAN Platform with Virtela’s SDN Expertise
 NTT sources SD-WAN technology from multiple vendors in the space.
NTT sources SD-WAN technology from multiple vendors in the space.
BlackBerry Cites Security Challenge Behind Proprietary Container Product
 Analysts note that open source security concerns are more about deployment, not technology.
Analysts note that open source security concerns are more about deployment, not technology.
Technology Short Take #84
Welcome to Technology Short Take #84! This episode is a bit late (sorry about that!), but I figured better late than never, right? OK, bring on the links!
Networking
- When I joined the NSX team in early 2013, a big topic at that time was overlay protocols (VXLAN, STT, etc.). Since then, that topic has mostly faded, though it still does come up from time to time. In particular, the move toward Geneve has prompted that discussion again, and Russell Bryant tackles the discussion in this post.
- Sjors Robroek describes his nested NSX-T lab that also includes some virtualized network equipment (virtualized Arista switches). Nice!
- Colin Lynch shares some details on his journey with VMware NSX (so far).
- I wouldn’t take this information as gospel, but here’s a breakdown of some of the IPv6 support available in VMware NSX.
Servers/Hardware
- Here’s an interesting article on the role that virtualization is playing in the network functions virtualization (NFV) space now that ARM hardware is growing increasingly powerful. This is a space that’s going to see some pretty major changes over the next few years, in my humble opinion.
Security
- Anthony Burke gives a little bit of a sneak peek Continue reading
Technology Short Take #84
Welcome to Technology Short Take #84! This episode is a bit late (sorry about that!), but I figured better late than never, right? OK, bring on the links!
Networking
- When I joined the NSX team in early 2013, a big topic at that time was overlay protocols (VXLAN, STT, etc.). Since then, that topic has mostly faded, though it still does come up from time to time. In particular, the move toward Geneve has prompted that discussion again, and Russell Bryant tackles the discussion in this post.
- Sjors Robroek describes his nested NSX-T lab that also includes some virtualized network equipment (virtualized Arista switches). Nice!
- Colin Lynch shares some details on his journey with VMware NSX (so far).
- I wouldn’t take this information as gospel, but here’s a breakdown of some of the IPv6 support available in VMware NSX.
Servers/Hardware
- Here’s an interesting article on the role that virtualization is playing in the network functions virtualization (NFV) space now that ARM hardware is growing increasingly powerful. This is a space that’s going to see some pretty major changes over the next few years, in my humble opinion.
Security
- Anthony Burke gives a little bit of a sneak peek Continue reading
Cisco Aims to ‘Meraki-fy’ its Software Business, Lohmeyer Says
 Company is making software sticky so it can move customers to a subscription model.
Company is making software sticky so it can move customers to a subscription model.
Notes on open-sourcing abandoned code
Code is Speech
First of all, code is speech. That was the argument why Phil Zimmerman could print the source code to PGP in a book, ship it overseas, and then have somebody scan the code back into a computer. Compelled speech is a violation of free speech. That was one of the arguments in the Apple vs. FBI case, where the FBI demanded that Apple write code for them, compelling speech.
Compelling the opening of previously closed source is compelled speech. Sure, demanding new products come with source would be one thing, but going backwards demanding source for products sold before 2017 is quite another thing.
For most people, "rights" are something that only their own side deserves. Whether something deserves the protection of "free speech" depends upon whether the speaker is "us" or the speaker is "them". If it's "them", then you'll find all sorts of reasons Continue reading
CCIE/CCDE Re-certification: An Opportunity to Learn and Grow
I did not pass my CCDE re-certification last week. Why write a blog about a “failure”? Honestly? Because I think we as an IT industry overly focus and give too many kudos to the passing only. Not to the hours and hours of studying and learning… not to the lessons learned… not to the growth gained from the studying journey. Just to the “pass/fail”. Well damn… no wonder people cheat. Their focus isn’t on the learning or the journey. Just the passing.
I thoroughly believe the expression –
Sometimes you win….. Sometimes you learn.
Did I want to pass last week? ROFL! Are you kidding? Of course I did! Did I “deserve” to pass? Well…. um…. err… not exactly.
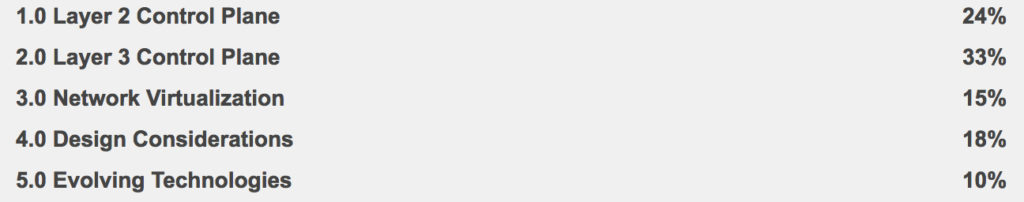
See that 10% at the bottom of the “Written Exam Topics v2.1?” Truth be told I didn’t quite exactly study that part very much.
So what is my plan now?
LEARN
Honestly in my job I am not doing much Cloud, SDN, or IoT. AND I have to admit I am quite happy I am now essentially forced to learn these to a Continue reading
More notes on US-CERTs IOCs
Yet another Russian attack against the power grid, and yet more bad IOCs from the DHS US-CERT.IOCs are "indicators of compromise", things you can look for in order to order to see if you, too, have been hacked by the same perpetrators. There are several types of IOCs, ranging from the highly specific to the uselessly generic.
A uselessly generic IOC would be like trying to identify bank robbers by the fact that their getaway car was "white" in color. It's worth documenting, so that if the police ever show up in a suspected cabin in the woods, they can note that there's a "white" car parked in front.
But if you work bank security, that doesn't mean you should be on the lookout for "white" cars. That would be silly.
This is what happens with US-CERT's IOCs. They list some potentially useful things, but they also list a lot of junk that waste's people's times, with little ability to distinguish between the useful and the useless.
An example: a few months ago was the GRIZZLEYBEAR report published by US-CERT. Among other things, it listed IP addresses used by hackers. There was no description which would be useful IP Continue reading
Security as an Enabler?
I have often wondered why the “security as an enabler” model is as unique as unicorns in the wild. I think the logic works in a vacuum and it would be great if it held true. However when humans and politics (layer 8 stuff) come into the mix, it seems that the cybersecurity team tend to be viewed as the naysayers that block progress. Quite honestly, the “security as an enabler” mantra only seems to work for those organizations that are directly profiting from the sale of cybersecurity. Those that understand the role cybersecurity plays in a typical organization realize that this is unfortunate.
With this thought in mind, I was reading through an article about the traits of CEO’s and found identified points that I think contribute to these challenges for information security:
- Bias toward action
- Forward Thinking
By no means am I criticizing CEO’s for these traits—they are primary contributors to keeping a given business relevant in its industry. I’m just using these to help explain the fallacy of a “security as an enabler” mindset within a given organization.
CEO’s are the highest single point of authority within an organization. They often appoint CSO’s (Chief Security Officers) or CISO’s Continue reading
BlackBerry Hypervisor Uses Containers for Connected Car Security
 Hypervisor platform uses containers to isolate hacks from spreading to critical car functions.
Hypervisor platform uses containers to isolate hacks from spreading to critical car functions.
Enterprises Need ‘Security 101’ to Keep IoT Devices Safe
 Almost half of US firms that use an IoT network have been hit by a security breach.
Almost half of US firms that use an IoT network have been hit by a security breach.
VMware NSX and Check Point vSEC
One of the current challenges of data center security is the East-West traffic that has become so pervasive as modern applications communicate a great deal between their different components. Conventional perimeter security is poorly placed to secure these lateral flows, to promote a zero-trust model in order to prevent threats moving within each application layer. VMware NSX addresses this, providing virtual firewall at the virtual NIC of each VM with a management framework where micro-segmentation is achievable with a sensible level of overhead. Check Point vSEC can be deployed in conjunction to provide threat and malware protection.
The VMware NSX Distributed Firewall (DFW) protects East-West L2-L4 traffic within the virtual data center. The DFW operates in the vSphere kernel and provides a firewall at the NIC of every VM. This enables micro-segmented, zero-trust networking with dynamic security policy leveraging the vCenter knowledge of VMs and applications to build policy rather than using IP or MAC addresses that may change. Tools for automation and orchestration as well as a rich set of APIs for partner and customer extensibility complete the toolset for security without impossible management overhead. While this is a dramatic improvement in the security Continue reading
Cisco: DDoS Attacks Grew 172% in 2016, Expect 3.1M by 2021
 The peak attack size increased 60 percent year-over-year.
The peak attack size increased 60 percent year-over-year.
Security Startup’s Predictive Risk Map IDs Breach Scenarios
 Cavium and Aon are customers.
Cavium and Aon are customers.
Cisco’s Ulevitch: We Say SDN Stands for ‘Still Does Nothing’
 Cisco aims to be one-stop shop for security.
Cisco aims to be one-stop shop for security.
Kalaam Telecom Launches Versa SD-WAN in the Persian Gulf
 Kalaam will build a managed service on top of Versa's Cloud IP Platform.
Kalaam will build a managed service on top of Versa's Cloud IP Platform.
Counting things, a lot of different things…

Back in April we announced Rate Limiting of requests for every Cloudflare customer. Being able to rate limit at the edge of the network has many advantages: it’s easier for customers to set up and operate, their origin servers are not bothered by excessive traffic or layer 7 attacks, the performance and memory cost of rate limiting is offloaded to the edge, and more.
In a nutshell, rate limiting works like this:
Customers can define one or more rate limit rules that match particular HTTP requests (failed login attempts, expensive API calls, etc.)
Every request that matches the rule is counted per client IP address
Once that counter exceeds a threshold, further requests are not allowed to reach the origin server and an error page is returned to the client instead
This is a simple yet effective protection against brute force attacks on login pages and other sorts of abusive traffic like L7 DoS attacks.
Doing this with possibly millions of domains and even more millions of rules immediately becomes a bit more complicated. This article is a look at how we implemented a rate limiter able to run quickly and accurately at the edge of the network which Continue reading
The First Question in Cybersecurity
Cybersecurity professionals know that security cannot be a bolt on process or technology. Likewise, I also believe that that the thought of including the security team is rarely goes far enough. To be effective, security should be ingrained and it should be pervasive. With a this commitment, there is at least one primary question that every organization should be asking in regards to Cybersecurity. That question is simply “Why?”
Not only should this question be asked organizationally, it should also be asked by individuals that are assuming security related roles within an organization. Some would think that the answer is simple or obvious. In many cases it is, but the complete answer WILL differ from organization to organization and differ based on the type of organization. What is important is that the organization itself agree upon the answer to this question.
Relevant answers to the Why question might be any or all of the following:
Governance—Specific regulatory requirements that the organization is required to meet. When these exist, they are often considered a top priority and a baseline requirement to transact business.
Cost/Expense—This could be direct and/or indirect. A direct example would be the typical scenario that occurs with ransomeware. Continue reading
What about other leaked printed documents?
So nat-sec pundit/expert Marci Wheeler (@emptywheel) asks about those DIOG docs leaked last year. They were leaked in printed form, then scanned in an published by The Intercept. Did they have these nasty yellow dots that track the source? If not, why not?The answer is that the scanned images of the DIOG doc don't have dots. I don't know why. One reason might be that the scanner didn't pick them up, as it's much lower quality than the scanner for the Russian hacking docs. Another reason is that the printer used my not have printed them -- while most printers do print such dots, some printers don't. A third possibility is that somebody used a tool to strip the dots from scanned images. I don't think such a tool exists, but it wouldn't be hard to write.
Scanner quality
The printed docs are here. They are full of whitespace where it should be easy to see these dots, but they appear not to be there. If we reverse the image, we see something like the following from the first page of the DIOG doc:Compare this to the first page of the Russian hacking doc which shows Continue reading
OneLogin and Password Managers
An interesting incident this last week brings password managers back to the front of the pile—
I used to use LastPass, but moved off of their product/service when LogMeIn bought them—my previous encounters with LogMeIn have all been negative, and I have no intention of using their service again in any form. During that move, I decided it was important to make another decision about the tradeoff between an online (cloud based) password manager, or one that keeps information in a local file. The key problem with cloud based services of this kind are they paint a huge target onto your passwords. The counter argument is that such cloud based services are more likely to protect your passwords than you are, because they focus their time and energy on doing so.
First lesson: moving to a cloud based application does not mean moving to a situation where the cloud provider actually knows what you are storing, nor how to access Continue reading