Some notes on #MacronLeak
Tonight (Friday May 5 2017) hackers dumped emails (and docs) related to French presidential candidate Emmanuel Macron. He's the anti-Putin candidate running against the pro-Putin Marin Le Pen. I thought I'd write up some notes.Update: Several people [*] have pointed out Trend Micro reporting that Russian/APT28 hackers were targeting Macron back on April 24. Coincidentally, this is also the latest that emails appear in the dump.
Technology Short Take #82
Welcome to Technology Short Take #82! This issue is a bit behind schedule; I’ve been pretty heads-down on some projects. That work will come to fruition in a couple weeks, so I should be able to come up for some air soon. In the meantime, here’s a few links and articles for your reading pleasure.
Networking
- Kristian Larsson shows how to validate data using YANG. Practical examples like this have really helped me better understand YANG and its relationship to structured data you might exchange with a device or service.
- There’s lots of talk about applying test-driven development (TDD) principles in various automation contexts, but I like the fact that Ajay Chenampara provides some practical examples in his blog post on applying TDD in network automation using Ansible.
- Matt Oswalt talks about how the combination of NAPALM and StackStorm enables some interesting results, including the ability to verify configuration consistency. StackStorm isn’t something I’ve had the opportunity to learn/use at all, but it’s on my (ever-growing) list of things to check out.
- Aaron Conole provides an overview of using the
ovs-dpctlcommand to “program” the Open vSwitch (OVS) kernel module. It’s a bit geeky, but does provide some insight into Continue reading
FBI’s Comey dangerous definition of “valid” journalism
The First Amendment, the "freedom of speech" one, does not mention journalists. When it says "freedom of the press" it means the physical printing press. Yes, that does include newspapers, but it also includes anybody else publishing things, such as the famous agitprop pamphlets published by James Otis, John Dickinson, and Thomas Paine. There was no journalistic value to Thomas Paine's Common Sense. The pamphlet argued for abolishing the monarchy and for American independence.Today in testimony before congress, FBI directory James Comey came out in support of journalism, pointing out that they would not prosecute journalists doing their jobs. But he then modified his statement, describing "valid" journalists as those who in possession of leaks would first check with the government, to avoid publishing anything that would damage national security. It's a power the government has abused in the past to delay or censor leaks. It's specifically why Edward Snowden contacted Glenn Greenwald and Laura Poitras -- he wanted journalists who would not kowtow the government on publishing the leaks.
Comey's testimony today was in regards to prosecuting Assange and Wikileaks. Under the FBI's official "journalist" classification scheme, Wikileaks are not real journalists, but instead publish "intelligence porn" and Continue reading
Juniper Control Plane Protection
How Does Internet Work - We know what is networking
I already wrote about Control Plane Protection in one of my previous posts focused on Cisco device configuration. Here we will make the same thing on Juniper device, I was using Juniper SRX300 and Juniper SRX1500 devices in my lab. CoPP ?? Control Plane Protection (CoPP) is a method of protecting processor unit, running services on your network device, against excessive flooding. Excessive flooding of traffic aimed towards your router/firewall processor, being that valid or malicious, is always undesirable and can also be dangerous. A network device, which starts the receive more control traffic that his processor can process, will
Securing Network Automation Video Is Online
The awesome Troopers crew published conference videos, including my Securing Network Automation presentation (more, including slide deck).
Research: Verizon Data Breach Investigations Report 2017
Must read report to stay informed on security.
The post Research: Verizon Data Breach Investigations Report 2017 appeared first on EtherealMind.
The Myth of Pure Cloud
 Despite the movement to cloud, data centers will still be around for the foreseeable future.
Despite the movement to cloud, data centers will still be around for the foreseeable future.
Introducing TLS with Client Authentication
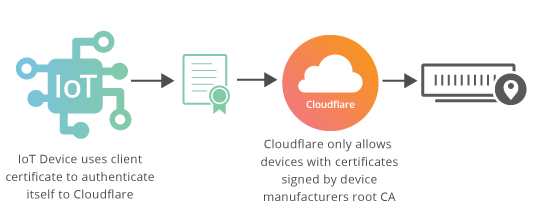
In a traditional TLS handshake, the client authenticates the server, and the server doesn’t know too much about the client. However, starting now, Cloudflare is offering enterprise customers TLS with client authentication, meaning that the server additionally authenticates that the client connecting to it is authorized to connect.
TLS Client Authentication is useful in cases where a server is keeping track of hundreds of thousands or millions of clients, as in IoT, or in a mobile app with millions of installs exchanging secure information. For example, an IoT company can issue a unique client certificate per device, and then limit connections to their IoT infrastructure to only their devices by blocking connections where the client doesn’t present a certificate signed by the company’s certificate authority.
Or in the case of a mobile banking app, where the bank wants to ensure customers’ secure financial data doesn’t get stolen by bots spoofing their mobile app, they can issue a unique certificate to every app install and in the TLS handshake validate requests are coming from their mobile app. Client authentication is also useful for VPNs, enterprise networks or staging sites, where corporations and developers need to lock down connections to only laptops Continue reading
Fortinet Reports Another Impressive Quarter
 Fortinet scored a $12M customer deal this quarter.
Fortinet scored a $12M customer deal this quarter.
vRealize Network Insight, NSX and Palo Alto Networks for micro-segmentation
Data Center cyber security is a fast-moving target where the IT teams need to constantly stay ahead of those that wish to do evil things. As security attacks can come from all directions, externally, and internally as well, the IT teams must fortify all the data, with a zero-trust security approach. Perimeter security augmented with intrusion detection and protection at the application level are the tools of choice for most data centers. This protects outsiders from getting in, as well as ensuring that the applications do not get impacted by a virus or other forms of malicious activities.
What has not been addressed is the intercommunications of applications amongst themselves, especially within the hypervisor layer, where virtual machines are communicating in an East-West traffic pattern. Traffic never hits the perimeter, and the conversations are happening several layers below the application layers where IDS sits. East-west traffic, from within the data center, has been an area overlooked as there is a gap organizationally. Simply put no one is paying attention to this area of vulnerability. The network infrastructure security teams are fortifying the perimeter, while the server teams are deploying IDS/IPS solutions. What has gone unnoticed is the East-West Continue reading
DockerCon 2017: The Top Rated Sessions
After the general session videos from DockerCon Day 1 and Day 2 yesterday, we’re happy to share with you the video recordings of the top rated sessions by DockerCon attendees. All the slides will soon be published on our slideshare account and all the breakout session video recordings available on our DockerCon 2017 youtube playlist.

Cilium: Network and Application Security with BPF and XDP by Thomas Graf
Docker?!? But I am a Sysadmin by Mike Coleman
Creating Effective Images by Abby Fuller
Taking Docker from Local to Production at Intuit by JanJaap Lahpor and Harish Jayakumar
Container Performance Analysis by Brendan Gregg
Secure Substrate: Least Privilege Container Deployment by Diogo Mónica and Riyaz Faizullabhoy
Escape from VMs with Image2Docker by Elton Stoneman and Jeff Nickoloff
What Have Namespaces Done for You Lately? by Liz Rice
Watch the top rated sessions from #dockercon cc @brendangregg @abbyfuller @lizrice @diogomonica
Click To Tweet
The post DockerCon 2017: The Top Rated Sessions appeared first on Docker Blog.
“Fast and Furious 8: Fate of the Furious”
So "Fast and Furious 8" opened this weekend to world-wide box office totals of $500,000,000. I thought I'd write up some notes on the "hacking" in it. The tl;dr version is this: yes, while the hacking is a bit far fetched, it's actually more realistic than the car chase scenes, such as winning a race with the engine on fire while in reverse.[SPOILERS]
Car hacking
The most innovative cyber-thing in the movie is the car hacking. In one scene, the hacker takes control of the cars in a parking structure, and makes them rain on to the street. In another scene, the hacker takes control away from drivers, with some jumping out of their moving cars in fear.
How real is this?
Well, today, few cars have a mechanical link between the computer and the steering wheel. No amount of hacking will fix the fact that this component is missing.
With that said, most new cars have features that make hacking possible. I'm not sure, but I'd guess more than half of new cars have internet connections (via the mobile phone network), cameras (for backing up, but also looking forward for lane departure warnings), braking (for emergencies), and acceleration.
Continue reading
Twistlock Closes $17M Funding Round for Container Security
 IBM security veteran Brendan Hannigan joined the Twistlock board.
IBM security veteran Brendan Hannigan joined the Twistlock board.
AES-CBC is going the way of the dodo
A little over a year ago, Nick Sullivan talked about the beginning of the end for AES-CBC cipher suites, following a plethora of attacks on this cipher mode.
Today we can safely confirm that this prediction is coming true, as for the first time ever the share of AES-CBC cipher suites on Cloudflare’s edge network dropped below that of ChaCha20-Poly1305 suites, and is fast approaching the 10% mark.
Over the course of the last six months, AES-CBC shed more than 33% of its “market” share, dropping from 20% to just 13.4%.
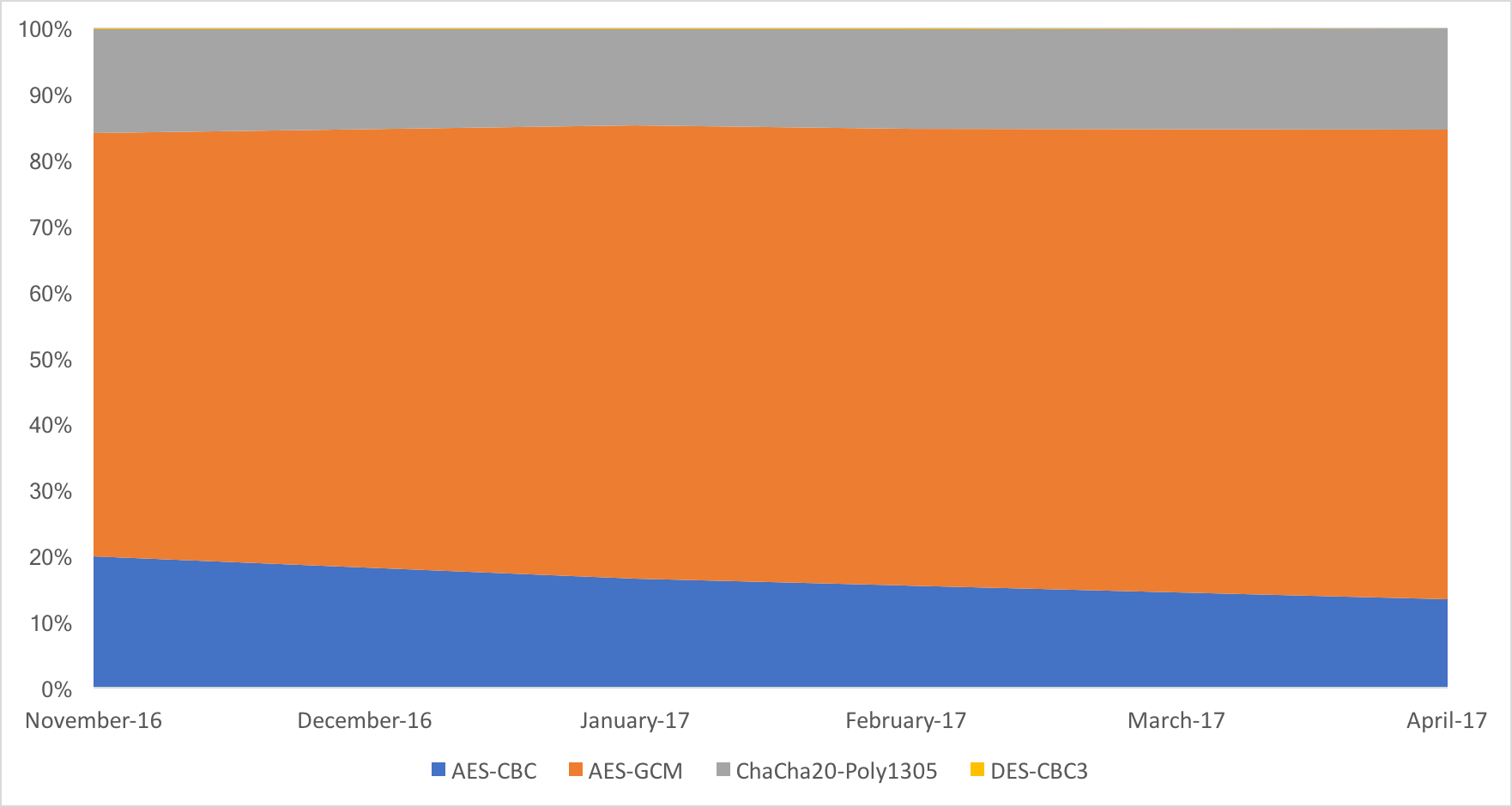
All of that share, went to AES-GCM, that currently encrypts over 71.2% of all connections. ChaCha20-Poly1305 is stable, with 15.3% of all connections opting for that cipher. Surprisingly 3DES is still around, with 0.1% of the connections.
The internal AES-CBC cipher suite breakdown as follows:
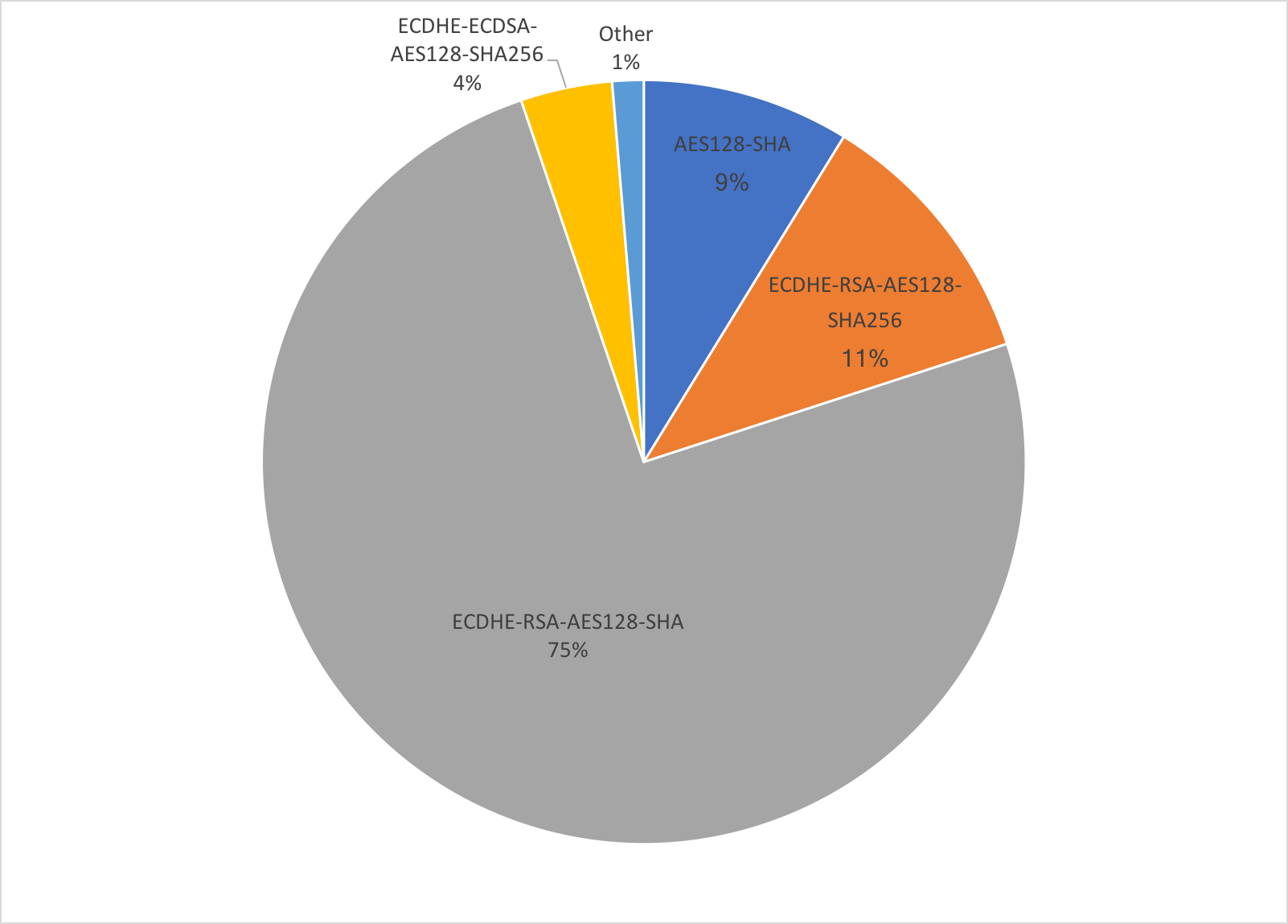
The majority of AES-CBC connections use ECDHE-RSA or RSA key exchange, and not ECDHE-ECDSA, which implies that we mostly deal with older clients.
RSA is also dying
In other good new, the use of ECDSA surpassed that of RSA at the beginning of the year. Currently more than 60% of all connections use Continue reading
HyTrust Helps Feds Meet Cloud Security Mandate
 It's a 'Swiss Army Knife' for federal cloud security compliance.
It's a 'Swiss Army Knife' for federal cloud security compliance.
ICSA Labs Certifies NSX Micro-segmentation Capabilities
VMware NSX has achieved ICSA labs Corporate Firewall Certification.
With the release of NSX for vSphere® 6.3, VMware has not only introduced several key security features such as Application Rule Manager and Endpoint Monitoring, which provide deep visibility into the application, and enable a rapid zero-trust deployment, but has also achieved Corporate Firewall Certification in independent testing performed by ICSA labs, a leading third-party testing and certification body and independent division of Verizon.
VMware NSX for vSphere 6.3 has been tested against an industry-accepted standard to which a consortium of firewall vendors, end users and ICSA labs contributed, and met all the requirements in the Baseline and Corporate module of the ICSA Module Firewall Certification Criteria version 4.2.
NSX is the only true micro-segmentation platform to achieve ICSA Firewall certification — with the NSX Distributed Firewall providing kernel-based, distributed stateful firewalling, and the Edge Services Gateway providing services such as North-South firewalling, NAT, DHCP, VPN, load balancing and high availability. VMware NSX provides security controls aligned to the application and enables a Zero-Trust model, independent of network topology.
The ICSA Firewall Certification criteria focus on several key firewall aspects, including stateful services, logging and persistence. ICSA also validates Continue reading
Observable Networks Detects Changes in AWS Lambda Functions
 Serverless functions are becoming mainstream.
Serverless functions are becoming mainstream.
Can Container Security Surpass That of Virtual Machines?
 Containers certainly face security threats that virtual machines do not.
Containers certainly face security threats that virtual machines do not.
Announcing LinuxKit: A Toolkit for building Secure, Lean and Portable Linux Subsystems

Last year, one of the most common requests we heard from our users was to bring a Docker-native experience to their platforms. These platforms were many and varied: from cloud platforms such as AWS, Azure, Google Cloud, to server platforms such as Windows Server, desktop platforms that their developers used such as OSX and Windows 10, to mainframes and IoT platforms – the list went on.
We started working on support for these platforms, and we initially shipped Docker for Mac and Docker for Windows, followed by Docker for AWS and Docker for Azure. Most recently, we announced the beta of Docker for GCP. The customizations we applied to make Docker native for each platform have furthered the adoption of the Docker editions.
One of the issues we encountered was that for many of these platforms, the users wanted Linuxcontainer support but the platform itself did not ship with Linux included. Mac OS and Windows are two obvious examples, but cloud platforms do not ship with a standard Linux either. So it made sense for us to bundle Linux into the Docker platform to run in these places.
What we needed to bundle was a secure, lean and portable Linux Continue reading
Introducing Moby Project: a new open-source project to advance the software containerization movement

Since Docker democratized software containers four years ago, a whole ecosystem grew around containerization and in this compressed time period it has gone through two distinct phases of growth. In each of these two phases, the model for producing container systems evolved to adapt to the size and needs of the user community as well as the project and the growing contributor ecosystem.
The Moby Project is a new open-source project to advance the software containerization movement and help the ecosystem take containers mainstream. It provides a library of components, a framework for assembling them into custom container-based systems and a place for all container enthusiasts to experiment and exchange ideas.
Let’s review how we got where we are today. In 2013-2014 pioneers started to use containers and collaborate in a monolithic open source codebase, Docker and few other projects, to help tools mature.

Then in 2015-2016, containers were massively adopted in production for cloud-native applications. In this phase, the user community grew to support tens of thousands of deployments that were backed by hundreds of ecosystem projects and thousands of contributors. It is during this phase, that Docker evolved its production model to an open component based approach. In Continue reading


