DH-1024 in Bitcoin terms
The ASIC power in the current Bitcoin network could do all the necessary precomputations for a Diffie-Hellman 1024 bit pair with 154 minutes worth of work. Or, the precomputation effort is roughly equal to 15 bitcoin blocks, at the current rate.(Update: I did some math wrong, it's 154 minutes not 23 minutes)
Another way of comparing is by using the website "keylength.com", which places the equivalent effort of cracking 1024 DH with 72 to 80 bits of symmetric crypto. At the current Bitcoin rate, 72 bits of crypto comes out to 15 bitcoin blocks, Continue reading
Global Impacts of Recent Leaks

Recent routing leaks remind us why monitoring Internet routing and performance is important and requires effective tools. Routing leaks are the ‘benign cousin’ of the malicious BGP route hijack. They happen accidentally, but the result is the same: traffic to affected prefixes is redirected, lost, or intercepted. And if they happen to you, your online business and brand suffers.
In this blog, we look at examples of a full-table peer leak, an origination leak, and a small peer leak and what happens to traffic when these incidents occur. As we will see, some events can go on for years, undetected and hence, unremediated, but extremely impactful never the less. As you read this blog, keep the following questions in mind. Would you know if the events described here were happening to you? Would you know how to identify the culprit if you did?
iTel/Peer1 routing leak
Starting on 10 October at 10:54 UTC, iTel (AS16696) leaked a full routing table (555,010 routes) to Peer 1 (AS13768). Normally, iTel exports 49 routes to Peer 1; however, over the course of several minutes, it leaked 436,776 routes from Hurricane Electric (AS6939) and 229,537 Continue reading
Cybereason Locks Up a $59 Million Round
 Cybersecurity firm partners with SoftBank for joint offering in Japan
Cybersecurity firm partners with SoftBank for joint offering in Japan
Security Release: Docker 1.8.3 and 1.6.2-CS7
As part of our ongoing security efforts, a vulnerability was discovered that affects the way content is stored and retrieved within the Docker Engine. Today we are releasing a security update that addresses this issue in accordance with our coordinated … ContinuedInfosec is good people
A10 DemoFriday Q&A + Video: Delivering Advanced Security & Application Policies with Cisco ACI & Thunder ADC
 The A10 and Cisco teams answer advanced security questions following their presentation on the Thunder ADC and Cisco ACI.
The A10 and Cisco teams answer advanced security questions following their presentation on the Thunder ADC and Cisco ACI.
Control Plane Protection in Cisco IOS
How does Internet work - We know what is networking
CoPP – Control Plane Protection or better Control Plain Policing is the only option to make some sort of flood protection or QoS for traffic going to control plane. In the router normal operation the most important traffic is control plain traffic. Control plane traffic is traffic originated on router itself by protocol services running on it and destined to other router device on the network. In order to run properly, routers need to speak with each other. They speak with each other by rules defined in protocols and protocols are run in shape of router services. Examples for this
SSL Certificate signed by own CA
There are a lot of “how-to” on the Internet explaining the setup procedure. This is mainly a copy / paste example for those in a hurry :)
How to setup your own CA
Cisco Strikes a Blow Against Ransomware
 A $60M Angler Exploit Kit operation gets cut in half.
A $60M Angler Exploit Kit operation gets cut in half.
Arista Takes a Macro Approach to Physical & Virtual Network Security
 It's like microsegmentation, only more 'macro.'
It's like microsegmentation, only more 'macro.'
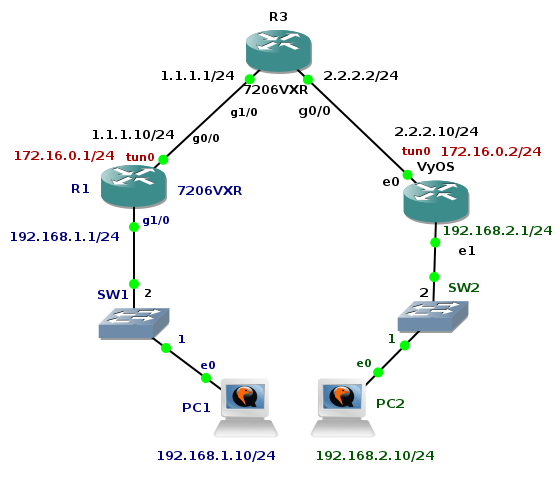
GRE over IPSec Tunnel Between Cisco and VyOS
The previous tutorial shown GRE tunnel configuration between Cisco router and Linux Core. The big advantage of GRE protocol is that it encapsulates L3 and higher protocols inside the GRE tunnel so routing updates and other multicast traffic can be successfully transferred over the tunnel. The main drawback of GRE protocol is the lack of built-in security. Data are transferred in plain-text over the tunnel and peers are not authenticated (no confidentiality). Tunneled traffic can be changed by attacker (no integrity checking of IP packets). For this reason GRE tunnel is very often used in conjunction with IPSec. Typically, GRE tunnel is encapsulated inside the IPSec tunnel and this model is called GRE over IPSec.
The tutorial shows configuration of OSPF routing protocol, GRE and IPSec tunnel on Cisco 7206 VXR router and appliance running VyOS network OS. Devices are running inside GNS3 lab an they are emulated by Dynamips (Cisco) and Qemu (VyOS).
Picture 1 - Topology
Note: VyOS installation is described here. You can easily build your own VyOS Qemu appliance using the Expect and Bash script shared in the article.
1. R3 Configuration
R3(config)# interface gigabitEthernet 1/0
R3(config-if)# ip address 1.1.1.1 255.255.255.0
R3(config-if)# no shutdown
R3(config-if)# interface gigabitEthernet 0/0
R3(config-if)# ip Continue reading
PCI Compliance in OpenStack Private Clouds With SDN
 Laying the foundation for better security moving forward.
Laying the foundation for better security moving forward.
Security Startup Illumio Joins the Docker Parade
 Illumio's ASP aims to cover all environments — which of course must include Docker containers.
Illumio's ASP aims to cover all environments — which of course must include Docker containers.
Jeb Bush is a cyber-weenie
Jeb Bush, one of them many 2016 presidential candidates, has numerous positions on "cyber" issues. They are all pretty silly, demonstrating that not only he but also his advisors profoundly misunderstand the issues.For example, his recent position opposing "NetNeutrality" regulations says this:
these rules prohibit one group of companies (ISPs) from charging another group of companies (content companies) the full cost for using their servicesUh, no, that's how Democrats frame the debate. ISPs charging content providers is actually a very bad thing. That we Republicans oppose NetNeutrality is not based on the belief that "charging content companies" is a good thing.
Instead, NetNeutrality is about technical issues like congestion and routing. Congestion is an inherent property of the Internet. NetNeutrality shifts the blame for congestion onto the ISPs. NetNeutrality means the 90% of Comcast subscribers who do not use Netflix must subsidize the 10% who are.
Or at least, that's one of the many ways Republicans would phrase the debate. More simply, all Republicans oppose NetNeutrality simply because it's over-regulation. My point is that Jeb Bush doesn't realized he's been sucked into the Democrat framing, and that what he says is garbage.
A better example is Jeb's position Continue reading
New Release of Cisco ACI Eases Layer 4-7 Integration
 The new release of Cisco Application Centric Infrastructure (ACI) includes innovations to ease Layer 4-7 network services integration.
The new release of Cisco Application Centric Infrastructure (ACI) includes innovations to ease Layer 4-7 network services integration.
Prez: Candidate synchronization
So last week I gave $10 to all the presidential campaigns, in order to watch their antics. One thing that's weird is that they often appear to act in unison, as if they are either copying each other, or are all playing from the same secret playbook.The candidates must report their donations every quarter, according to FEC (Federal Elections Commission) rules. The next deadline is September 30th. Three days before that deadline, half the candidates sent out email asking for donations to meet this "critical" deadline. They don't say why it's critical, but only that's is some sort of critical deadline that must be met, which we can only do so with your help. The real reason why, of course, is that this information will become public, implicitly ranking the amount of support each candidate has.
Four days before this deadline, I didn't get donation pleas mentioning it. Three days before, half the candidates mentioned it. It's as if one candidate sees such an email blast, realizes it's a great idea, and send's out a similar email blast of their own.
Two days before the deadline, three of the candidates sent out animated GIFs counting down to the deadline. Continue reading
Datadog Hunts Down Those Rogue Servers
 Using clustering algorithms, Datadog can spy cloud servers that aren't performing optimally.
Using clustering algorithms, Datadog can spy cloud servers that aren't performing optimally.
Phantom Cyber Raises $6.5M To Automate Security
 Someone needs to unify all those enterprise security tools, the startup reckons.
Someone needs to unify all those enterprise security tools, the startup reckons.
Juniper Unite Cloud-Enabled Enterprise Promises Agility & Security For Anytime, Anywhere Use
 As the reliance on the cloud continues to grow, Juniper finds a solution to bring agility, security, and faster services to enterprises: the Juniper Unite Cloud-Enabled Enterprise architecture.
As the reliance on the cloud continues to grow, Juniper finds a solution to bring agility, security, and faster services to enterprises: the Juniper Unite Cloud-Enabled Enterprise architecture.
How Encryption of Network Traffic Works?
How does Internet work - We know what is networking
I recently started studying again, this time as an attempt of deep-diving into some security concepts for one of my PhD courses. It’s interesting how, as much as you try to escape from it, mathematics will sooner or later catch you somewhere and you will need to learn a bit more of it. At least that happened to me… In this process I realised that if you go beyond simple security theory and network device configuration all other stuff is pure mathematics. The reason behind my unplanned course in mathematics is explained through the rest of this text. It will