Network-based policies in Cloudflare Gateway
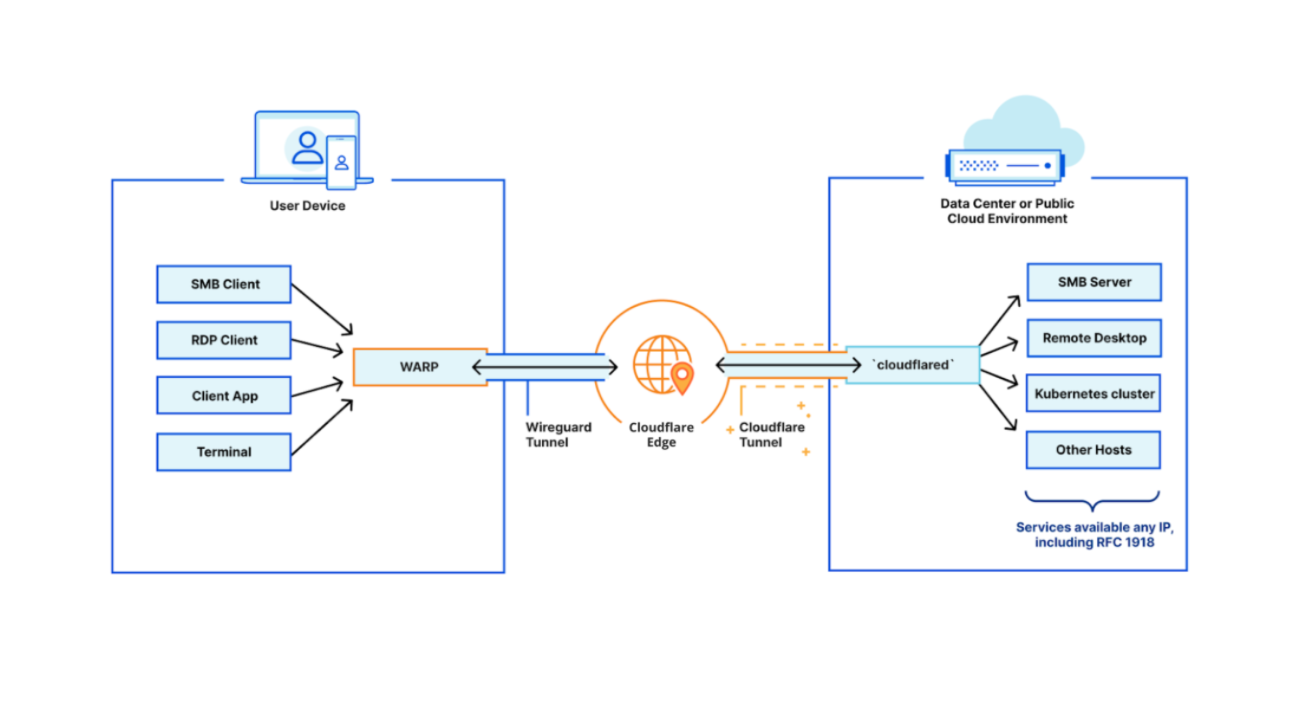
Over the past year, Cloudflare Gateway has grown from a DNS filtering solution to a Secure Web Gateway. That growth has allowed customers to protect their organizations with fine-grained identity-based HTTP policies and malware protection wherever their users are. But what about other Internet-bound, non-HTTP traffic that users generate every day — like SSH?
Today we’re excited to announce the ability for administrators to configure network-based policies in Cloudflare Gateway. Like DNS and HTTP policy enforcement, organizations can use network selectors like IP address and port to control access to any network origin.
Because Cloudflare for Teams integrates with your identity provider, it also gives you the ability to create identity-based network policies. This means you can now control access to non-HTTP resources on a per-user basis regardless of where they are or what device they’re accessing that resource from.
A major goal for Cloudflare One is to expand the number of on-ramps to Cloudflare — just send your traffic to our edge however you wish and we’ll make sure it gets to the destination as quickly and securely as possible. We released Magic WAN and Magic Firewall to let administrators replace MPLS connections, define routing decisions, and apply packet-based Continue reading
Illusory Correlation and Security
Fear sells. Fear of missing out, fear of being an imposter, fear of crime, fear of injury, fear of sickness … we can all think of times when people we know (or worse, a people in the throes of madness of crowds) have made really bad decisions because they were afraid of something. Bruce Schneier has documented this a number of times. For instance: “it’s smart politics to exaggerate terrorist threats” and “fear makes people deferential, docile, and distrustful, and both politicians and marketers have learned to take advantage of this.” Here is a paper comparing the risk of death in a bathtub to death because of a terrorist attack—bathtubs win.
But while fear sells, the desire to appear unafraid also sells—and it conditions people’s behavior much more than we might think. For instance, we often say of surveillance “if you have done nothing wrong, you have nothing to hide”—a bit of meaningless bravado. What does this latter attitude—“I don’t have anything to worry about”—cause in terms of security?
Several attempts at researching this phenomenon have come to the same conclusion: average users will often intentionally not use things they see someone they perceive as paranoid using. Continue reading
QUIC Version 1 is live on Cloudflare
On May 27 2021, the Internet Engineering Task Force published RFC 9000 - the standardarized version of the QUIC transport protocol. The QUIC Working Group declared themselves done by issuing a Last Call 7 months ago. The i's have been dotted and the t's crossed, RFC 8999 - RFC 9002 are a suite of documents that capture years of engineering design and testing of QUIC. This marks a big occasion.
And today, one day later, we’ve made the standardized version of QUIC available to Cloudflare customers.
Transport protocols have a history of being hard to deploy on the Internet. QUIC overcomes this challenge by basing itself on top of UDP. Compared to TCP, QUIC has security by default, protecting almost all bytes from prying eyes or "helpful" middleboxes that can end up making things worse. It has designed-in features that speed up connection handshakes and mitigate the performance perils that can strike on networks that suffer loss or delays. It is pluggable, providing clear standardised extensions point that will allow smooth, iterative development and deployment of new features or performance enhancements for years to come.
The killer feature of QUIC, however, is that it is deployable in reality. We are Continue reading
How to Protect Azure VMware Solution Resources with Azure Application Gateway
Azure VMware Solution (AVS) is a VMware validated private cloud solution managed and maintained by Azure. It runs on dedicated bare-metal Azure infrastructure. AVS allows customers to manage and secure applications across VMware environments and Microsoft Azure with a consistent operating framework. It supports workload migration, VM deployment, and Azure service consumption.
As AVS private cloud runs on an isolated Azure environment, it is not accessible from Azure or the Internet by default. Users can use either ExpressRoute Global Reach (i.e., from on-prem) or a jump box (i.e., on an Azure VNet) to access AVS private cloud. This means AVS workload VMs are confined within AVS private cloud and not accessible from the Internet.
But what if customers want to make AVS Private Cloud resources, such as web servers, accessible from the Internet? In that case, Public IP needs to be deployed. There are couple of ways to do this: (1) Azure Application Gateway, and (2) Destination NAT or DNAT using Azure WAN Hub and Firewall. Azure Application Gateway is Continue reading
Learn from industry experts at the Kubernetes Security and Observability Summit—next week!
The Kubernetes Security and Observability Summit is only 1 week away! The industry’s first and only conference solely focused on Kubernetes security and observability will be taking place online June 3, 2021.
During the Summit, DevOps, SREs, platform architects, and security teams will enjoy the chance to network with industry experts and explore trends, strategies, and technologies for securing, observing and troubleshooting cloud-native applications.
What does security and observability mean in a cloud-native context? What challenges should Kubernetes practitioners anticipate and what opportunities should they investigate? Join us to explore these types of questions and gain valuable insight you’ll be able to take back to your teams.
Speakers & sessions
Tigera’s President & CEO, Ratan Tipirneni, will kick off the Summit with an opening keynote address. Two additional keynotes from Graeme Hay of Morgan Stanley and Keith Neilson of Discover Financial Services will follow. Attendees will then have the opportunity to attend breakout sessions organized into three tracks:
- Stories from the real world
- Best practices
- Under the hood
During these sessions, experts from industry-leading companies like Amazon, Box, Citi, EY, Mirantis, Morgan Stanley, PayPal, Salesforce, and of course, Tigera, will share real-world stories, best practices, and technical concepts related to Continue reading
Cloudflare’s SOC as a Service
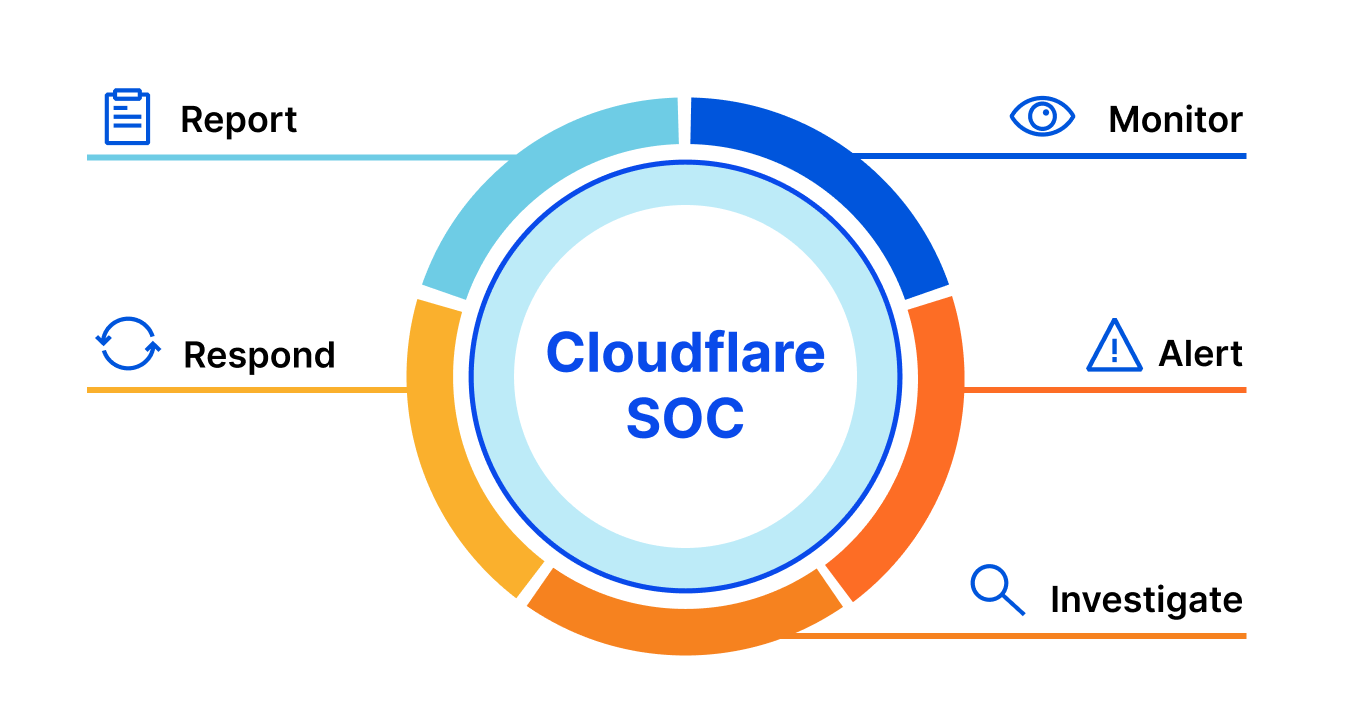
When Cloudflare started, sophisticated online security was beyond the reach of all but the largest organizations. If your pockets were deep enough, you could buy the necessary services — and the support that was required to operate them — to keep your online operations secure, fast, and reliable. For everyone else? You were out of luck.
We wanted to change that: to help build a better Internet. To build a set of services that weren’t just technically sophisticated, but easy to use. Accessible. Affordable. Part of this meant that we were always looking to build and equip our customers with all the tools they needed in order to do this for themselves.
Of course, a lot has changed since we started. The Internet has only increased in importance, fast becoming the most important channel for many businesses. Cybersecurity threats have only become more prevalent — and more sophisticated. And the products that Cloudflare offers to keep you safe on the Internet have attracted some of the largest and most recognizable organizations in the world.
Ask some of these larger organizations about cybersecurity, and they’ll tell you a few things: first, they love our products. But, second, that when something happens Continue reading
Data Center Threats: Turning Remote Access into Money
Data centers are an appealing target for cybercriminals. Even though they may be more difficult to compromise than the home computer of a kid playing Fortnite or the laptop of a sales representative connecting to a random wireless network, they can bring very large rewards: databases with millions of records containing financial and personal information, substantial computational resources that can be used to mine cryptocurrencies, and access to key assets that can be held for ransom.
In this blog post, we analyze the main pathways that cybercriminals leverage to gain access to data centers, how they take advantage of that access, and what security administrators can do to reduce and manage the associated risks.
Getting into the Data Center
The obvious first goal of an attacker is to gain access to the targeted data center. This can be achieved in several ways — including social engineering [1], physical access [2], and occasionally by deer [3]— but anecdotal evidence suggests that the two main avenues are remote exploitation (also known as remote-to-local attacks [4]), and stolen credentials [5].
Remote-to-local Attacks
In a remote-to-local attack, an attacker targets a remotely accessible service provided by one of the workloads running in the data Continue reading
Why you don’t want to miss the upcoming Kubernetes Security and Observability Summit
The inaugural Kubernetes Security and Observability Summit will be a free, live, online experience full of Kubernetes-related security and observability content. On June 3, 2021, industry experts will gather under one virtual roof to discuss trends, strategies, and technologies for Kubernetes security and observability, to help you understand and navigate today’s pressing issues in the world of cloud-native applications.
Why attend?
The Summit is a great opportunity to:
- Network with the industry’s best security, DevOps, and site reliability engineer (SRE) teams for cloud-native platforms
- Learn how to secure, observe, and troubleshoot Kubernetes environments
- Explore real-world Kubernetes security and observability use cases presented by experts from industry-leading companies like Amazon, Box, Citi, EY, Mirantis, Morgan Stanley, PayPal, Salesforce, and of course, Tigera
Who should attend?
SREs, platform architects, and DevOps and security teams will all find value in attending the Summit.
- DevOps teams and SREs – Learn how to include security and observability in your CI/CD to enable security, observability, and troubleshooting
- Platform architects – Learn architecture patterns and best practices to secure and troubleshoot cloud-native applications
- Security teams – Learn how to holistically secure your cloud-native applications following today’s best practices
Speakers & sessions
An opening keynote address from Continue reading
VMware Wins 2021 Global InfoSec Award as Market Leader in Firewall
Today at RSA Conference 2021, we’re excited to announce that VMware is a winner of the CyberDefense Magazine 2021 Global InfoSec Award as Market Leader in Firewall. One of VMware’s core beliefs is that we need structural and architectural changes to how organizations approach security. This means taking a fresh look at how we approach issues such as internal data center security. This is exactly what led us to deliver the VMware NSX Service-defined Firewall.
The NSX Service-defined Firewall is one of the foundations of VMware Security. This solution is a unique distributed, scale-out internal firewall that protects all east-west traffic across all workloads without network changes. This radically simplifies the security deployment model. It includes a distributed firewall, advanced threat protection, and network traffic analytics. With the VMware NSX Service-defined Firewall, security teams can protect their organizations from cyberattacks that make it past the traditional network perimeter and attempt to move laterally. Its key differentiating capabilities include:
- Distributed, granular enforcement: The NSX Service-defined Firewall provides distributed and granular enforcement of security policies to deliver protection down to the workload level, eliminating the need for network changes.
- Scalability and throughput: Because it is distributed, the Service-defined Firewall is elastic, Continue reading
Humanity wastes about 500 years per day on CAPTCHAs. It’s time to end this madness


Select all the buses. Click on bikes. Does this photo have traffic lights? As ridiculous as these questions are, you’re almost guaranteed to have seen one recently. They are a way for online services to separate humans from bots, and they’re called CAPTCHAs. CAPTCHAs strengthen the security of online services. But while they do that, there’s a very real cost associated with them.
Based on our data, it takes a user on average 32 seconds to complete a CAPTCHA challenge. There are 4.6 billion global Internet users. We assume a typical Internet user sees approximately one CAPTCHA every 10 days.
This very simple back of the envelope math equates to somewhere in the order of 500 human years wasted every single day — just for us to prove our humanity.
Today, we are launching an experiment to end this madness. We want to get rid of CAPTCHAs completely. The idea is rather simple: a real human should be able to touch or look at their device to prove they are human, without revealing their identity. We want you to be able to prove that you are human without revealing which human you are! You may ask if this is Continue reading
Security Director Cloud Is Juniper’s SASE Vision Board
Juniper's newly announced Security Director Cloud lays a policy foundation for an eventual SASE offering. Juniper hopes to keep customers from going to competitors' offerings as it realizes its own SASE vision.
The post Security Director Cloud Is Juniper’s SASE Vision Board appeared first on Packet Pushers.
The Hedge 82: Jared Smith and Route Poisoning
Intentionally poisoning BGP routes in the Default-Free Zone (DFZ) would always be a bad thing, right? Actually, this is a fairly common method to steer traffic flows away from and through specific autonomous systems. How does this work, how common is it, and who does this? Jared Smith joins us on this episode of the Hedge to discuss the technique, and his research into how frequently it is used.
Response: The Instagram ads Facebook won’t show you
 Facebook is corporate IT security risk.
Facebook is corporate IT security risk.
VMware Debuts A SASE Distributed Work Conglomeration Called Anywhere Workspace
VMware has announced the Anywhere Workspace. Designed to help control access to premises and cloud apps, and enforce security policies regardless of where an employee may be working, Anywhere Workspace is an assemblage of several existing products in VMware’s portfolio: endpoint management for laptops and smartphones, access control, endpoint security, and cloud-based security services. The […]
The post VMware Debuts A SASE Distributed Work Conglomeration Called Anywhere Workspace appeared first on Packet Pushers.
Anatomy of how you get pwned
Today, somebody had a problem: they kept seeing a popup on their screen, and obvious scam trying to sell them McAfee anti-virus. Where was this coming from?
In this blogpost, I follow this rabbit hole on down. It starts with "search engine optimization" links and leads to an entire industry of tricks, scams, exploiting popups, trying to infect your machine with viruses, and stealing emails or credit card numbers.
Evidence of the attack first appeared with occasional popups like the following. The popup isn't part of any webpage.
This is obviously a trick. But from where? How did it "get on the machine"?
There's lots of possible answers. But the most obvious answer (to most people), that your machine is infected with a virus, is likely wrong. Viruses are generally silent, doing evil things in the background. When you see something like this, you aren't infected ... yet.
Instead, things popping with warnings is almost entirely due to evil websites. But that's confusing, since this popup doesn't appear within a web page. It's off to one side of the screen, nowhere near the web browser.
Moreover, we spent some time diagnosing this. We restarted the webbrowser in "troubleshooting mode" with all Continue reading
If you haven’t found the tradeoffs …
One of the big movements in the networking world is disaggregation—splitting the control plane and other applications that make the network “go” from the hardware and the network operating system. This is, in fact, one of the movements I’ve been arguing in favor of for many years—and I’m not about to change my perspective on the topic. There are many different arguments in favor of breaking the software from the hardware. The arguments for splitting hardware from software and componentizing software are so strong that much of the 5G transition also involves the open RAN, which is a disaggregated stack for edge radio networks.
If you’ve been following my work for any amount of time, you know what comes next: If you haven’t found the tradeoffs, you haven’t looked hard enough.
This article on hardening Linux (you should go read it, I’ll wait ’til you get back) exposes some of the complexities and tradeoffs involved in disaggregation in the area of security. Some further thoughts on hardening Linux here, as well. Two points.
First, disaggregation has serious advantages, but disaggregation is also hard work. With a commercial implementation you wouldn’t necessarily think about these kinds of supply chain issues. Continue reading
Ethics: University of Minnesota’s hostile patches
The University of Minnesota (UMN) got into trouble this week for doing a study where they have submitted deliberately vulnerable patches into open-source projects, in order to test whether hostile actors can do this to hack things. After a UMN researcher submitted a crappy patch to the Linux Kernel, kernel maintainers decided to rip out all recent UMN patches.
Both things can be true:
- Their study was an important contribution to the field of cybersecurity.
- Their study was unethical.
Cloudflare obtains new ISO/IEC 27701:2019 privacy certification and what that means for you
This post is also available in French and German.
Cloudflare is one of the first organisations in our industry to have achieved ISO/IEC 27701:2019 certification, and the first web performance & security company to be certified to the new ISO privacy standard as both a data processor and controller.
Providing transparency into our privacy practices has always been a priority for us. We think it is important that we do more than talk about our commitment to privacy — we are continually looking for ways to demonstrate that commitment. For example, after we launched the Internet's fastest, privacy-first public DNS resolver, 1.1.1.1, we didn’t just publish our commitments to our public resolver users, we engaged an independent firm to make sure we were meeting our commitments, and we blogged about it, publishing their report.

Following in that tradition, today we’re excited to announce that Cloudflare has been certified to a new international privacy standard for protecting and managing the processing of personal data — ISO/IEC 27701:2019. The standard is designed such that the requirements organizations must meet to become certified are very closely aligned to the requirements in the EU’s General Data Protection Regulation (“GDPR”). So Continue reading
DDoS attack trends for 2021 Q1


Last week was Developer Week at Cloudflare. During that week, our teams released a bunch of cool new products, including a bunch of improvements to Workers. And it's not just our customers that love deploying apps with Workers, but also our engineering teams. Workers is also what powers our Internet traffic and attack trends on Cloudflare Radar. Today, along with this deep-dive analysis blog, we’re excited to announce the new Radar DDoS Report page, our first fully automated data notebook built on top of Jupyter, Clickhouse, and Workers.
Last month, we introduced our autonomous edge DDoS (Distributed Denial of Service) protection system and explained how it is able to drop attacks at wire speed without impacting performance. It runs in our networks’ edge, analyzes traffic asynchronously to avoid impacting performance, and pushes mitigation rules in-line immediately once attacks are detected. All of this is done autonomously, i.e., without requiring centralized consensus.
Today, we’d like to share the latest DDoS insights and trends that are based on attacks that our system mitigated during the first quarter of 2021. When we analyze attacks, we calculate the “DDoS activity” rate, which is the percent of attack traffic out of Continue reading
