An MNO’s Guide to Buying a 5G-Ready Next-Generation Firewall
In the new era of 5G, mobile network operators have the opportunity to move up the value chain and...
Cloudflare IPO Targets a $483M Haul, $3.5B Valuation
The vendor claims it competes against companies like Amazon, Cisco, and Oracle. It also directly...
Thread on the OSI model is a lie
Thread on network input parsers
Cisco Patches Critical Bug in REST API Container
Cisco issued a patch for a critical bug in its IOS XE operating system that could allow a remote...
Announcing the General Availability of API Tokens
APIs at Cloudflare
Today we are announcing the general availability of API Tokens - a scalable and more secure way to interact with the Cloudflare API. As part of making a better internet, Cloudflare strives to simplify manageability of a customer’s presence at the edge. Part of the way we do this is by ensuring that all of our products and services are configurable by API. Customers ranging from partners to enterprises to developers want to automate management of Cloudflare. Sometimes that is done via our API directly, and other times it is done via open source software we help maintain like our Terraform provider or Cloudflare-Go library. It is critical that customers who are automating management of Cloudflare can keep their Cloudflare services as secure as possible.
Least Privilege and Why it Matters
Securing software systems is hard. Limiting what a piece of software can do is a good defense to prevent mistakes or malicious actions from having greater impact than they could. The principle of least privilege helps guide how much access a given system should have to perform actions. Originally formulated by Jerome Saltzer, “Every program and every privileged user of the system should operate using Continue reading
IBM, Orange Top UK’s SDN Market, Says ISG Report
IBM and Orange Business Services top the list of U.K. SDN vendors, according to an ISG report that...
OnX Adds Cisco SD-WAN to Its Managed Service Portfolio
Toronto-based cloud services provider OnX Canada is now offering Cisco's SD-WAN as a managed...
How Will Open Source Deal With Success?
“Part of winning is that with great power comes great responsibility,” noted Red Hat CTO Chris...
Check Point Expands CloudGuard to SD-WAN Security
Check Point expanded its CloudGuard portfolio with the launch of two new security suites aimed at...
VMware Adds Load Balancer, Analytics Engine to NSX
VMware rolled out updates to its NSX networking platform including a new analytics engine and load...
Rackspace Targets Hybrid-Cloud Adoption With New Services
Rackspace rolled out five new enhancements to its hybrid cloud portfolio aimed at helping customers...
Mellanox Reveals SmartNICs With 200 Gb/s Connectivity
Mellanox today introduced a pair of SmartNICs for data center servers and storage systems at...
IBM Drives Quantum-Safe Cryptography Into Its Public Cloud
IBM predicts that due to the rate of progress in quantum computing data protected by current...
VMware Buys Carbon Black for $2.1B and Pivotal for $2.7B
VMware said it will buy Pivotal in a deal valued at $2.7 billion and security company Carbon Black...
Supercharging Firewall Events for Self-Serve
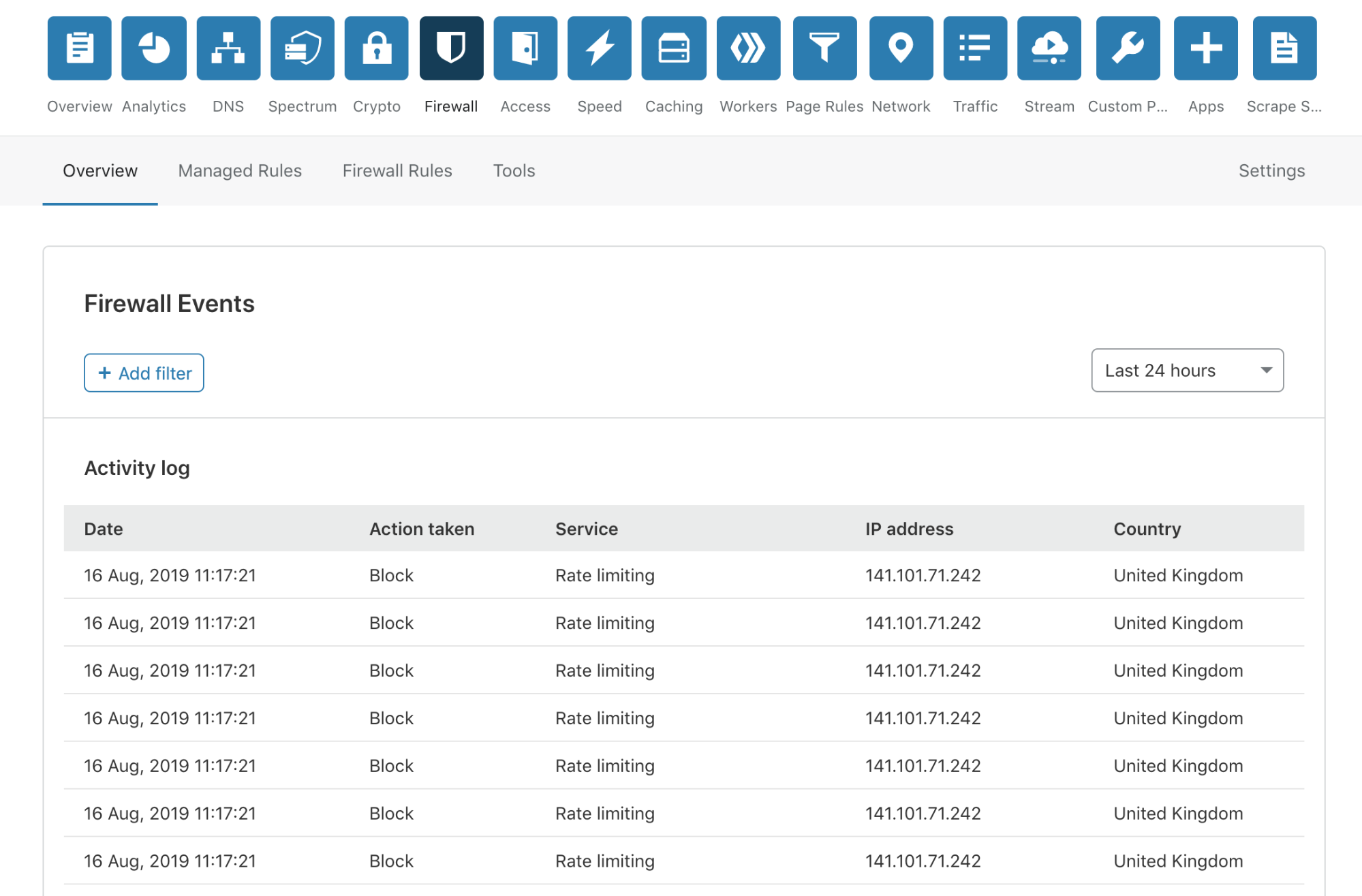
Today, I’m very pleased to announce the release of a completely overhauled version of our Firewall Event log to our Free, Pro and Business customers. This new Firewall Events log is now available in your Dashboard, and you are not required to do anything to receive this new capability.
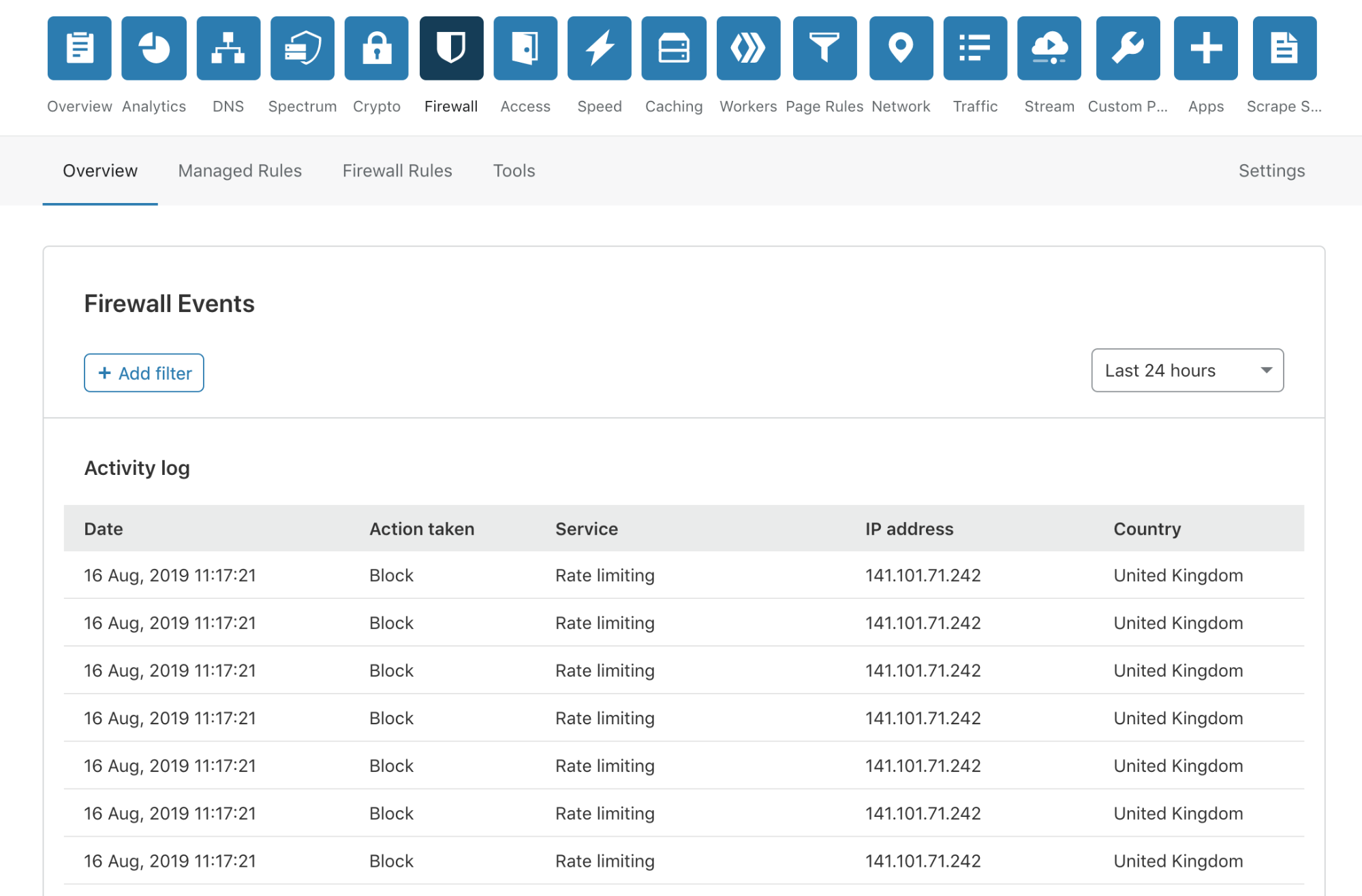
No more modals!
We have done away with those pesky modals, providing a much smoother user experience. To review more detailed information about an event, you simply click anywhere on the event list row.
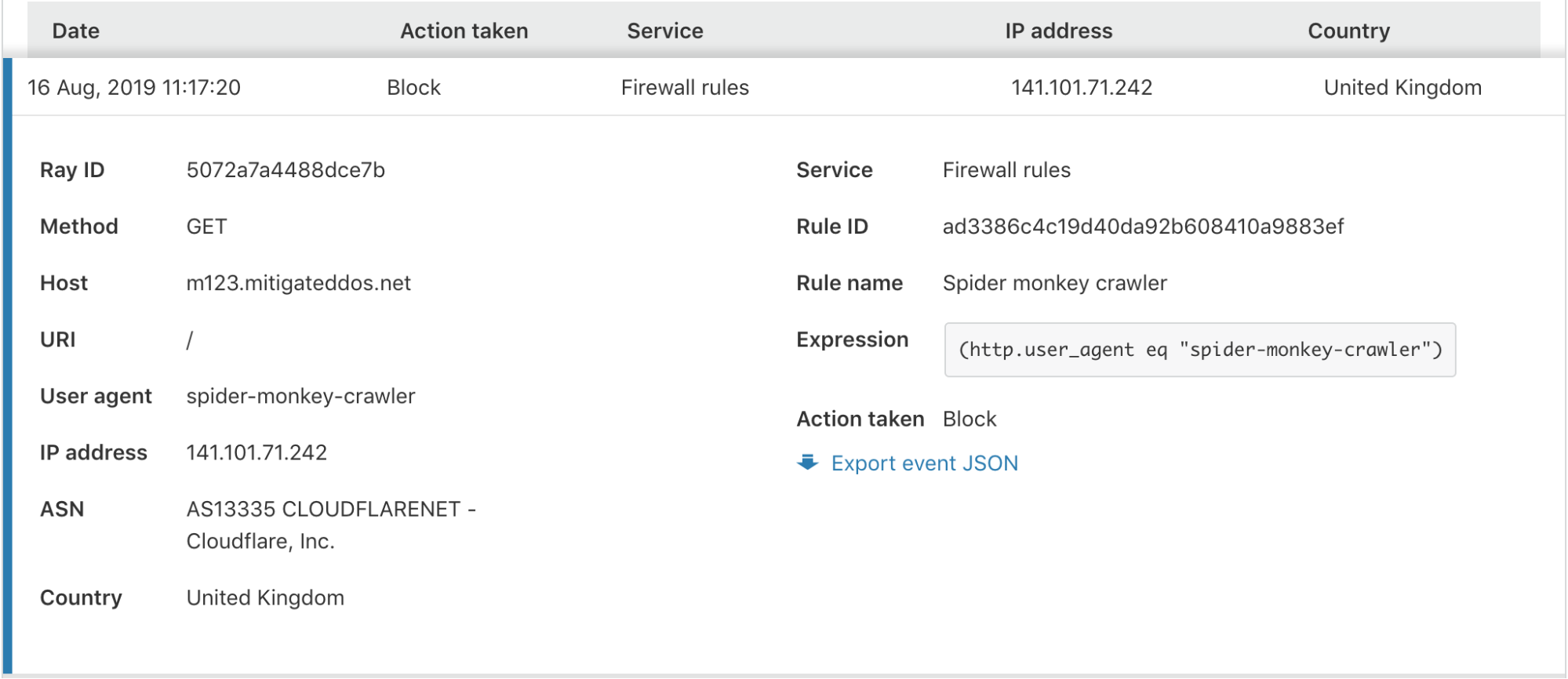
In the expanded view, you are provided with all the information you may need to identify or diagnose issues with your Firewall or find more details about a potential threat to your application.
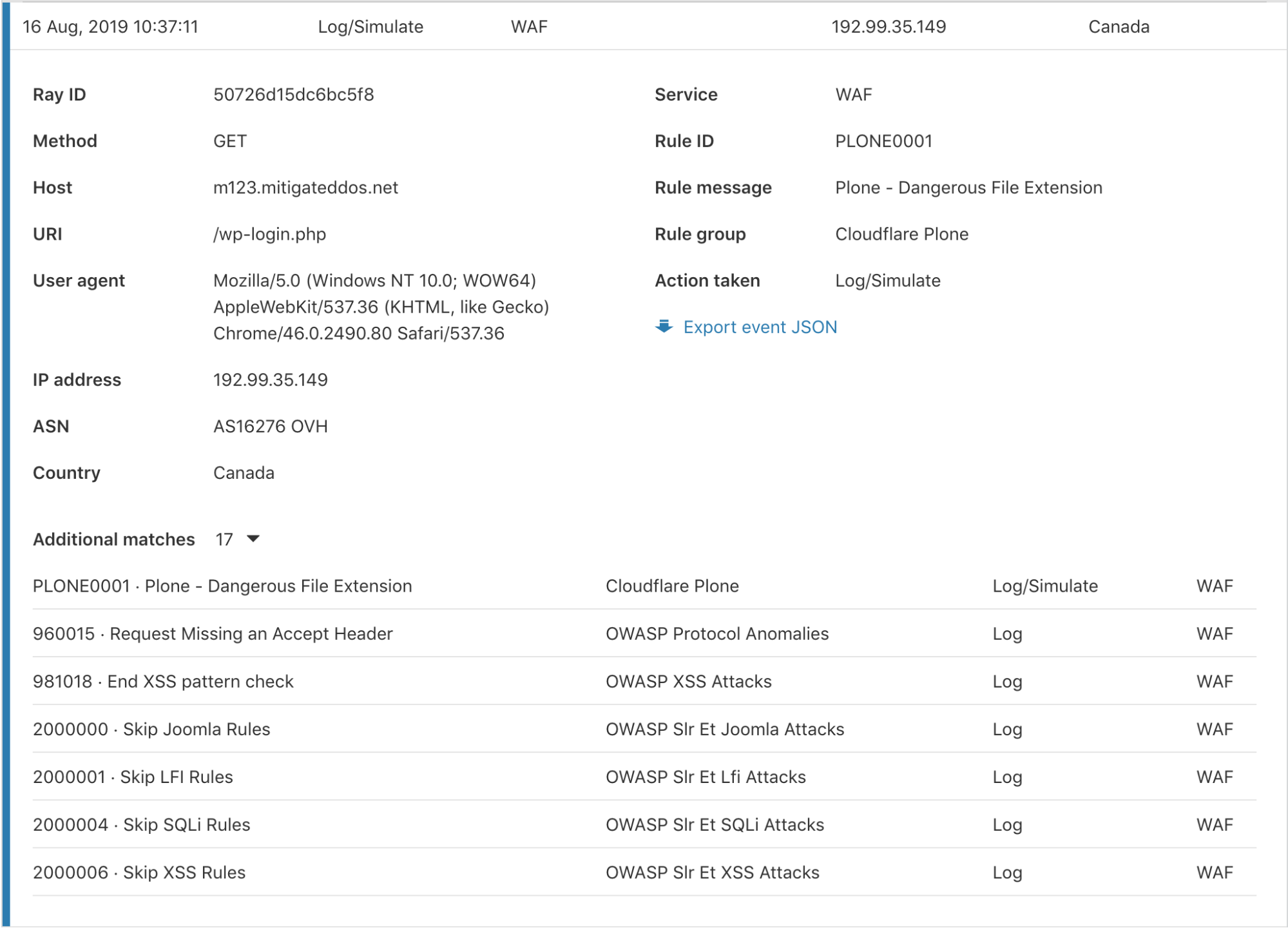
Additional matches per event
Cloudflare has several Firewall features to give customers granular control of their security. With this control comes some complexity when debugging why a request was stopped by the Firewall. To help clarify what happened, we have provided an “Additional matches” count at the bottom for events triggered by multiple services or rules for the same request. Clicking the number expands a list showing each rule and service along with the corresponding action.
Search for any field within a Firewall Event
Can a Composable Hypervisor Re-Imagine Virtualization?
“Virtualization is changing and what people need from virtualization is changing,” said Intel's...
VMware Buying Spree Continues With Intrinsic
VMware bought Intrinsic, an application security startup, in its fifth acquisition in three months,...
Microsoft, Intel, and Red Hat Back Confidential Computing
The Linux Foundation’s Confidential Computing Consortium is a who’s who of cloud providers,...