Security Compliance at Cloudflare

Cloudflare believes trust is fundamental to helping build a better Internet. One way Cloudflare is helping our customers earn their users’ trust is through industry standard security compliance certifications and regulations.
Security compliance certifications are reports created by independent, third-party auditors that validate and document a company’s commitment to security. These external auditors will conduct a rigorous review of a company’s technical environment and evaluate whether or not there are thorough controls - or safeguards - in place to protect the security, confidentiality, and availability of information stored and processed in the environment. SOC 2 was established by the American Institute of CPAs and is important to many of our U.S. companies, as it is a standardized set of requirements a company must meet in order to comply. Additionally, PCI and ISO 27001 are international standards. Cloudflare cares about achieving certifications because our adherence to these standards creates confidence to customers across the globe that we are committed to security. So, the Security team has been hard at work obtaining these meaningful compliance certifications.
Since the beginning of this year, we have been renewing our PCI DSS certification in February, achieving SOC 2 Type 1 compliance in March, obtaining Continue reading
A free Argo Tunnel for your next project
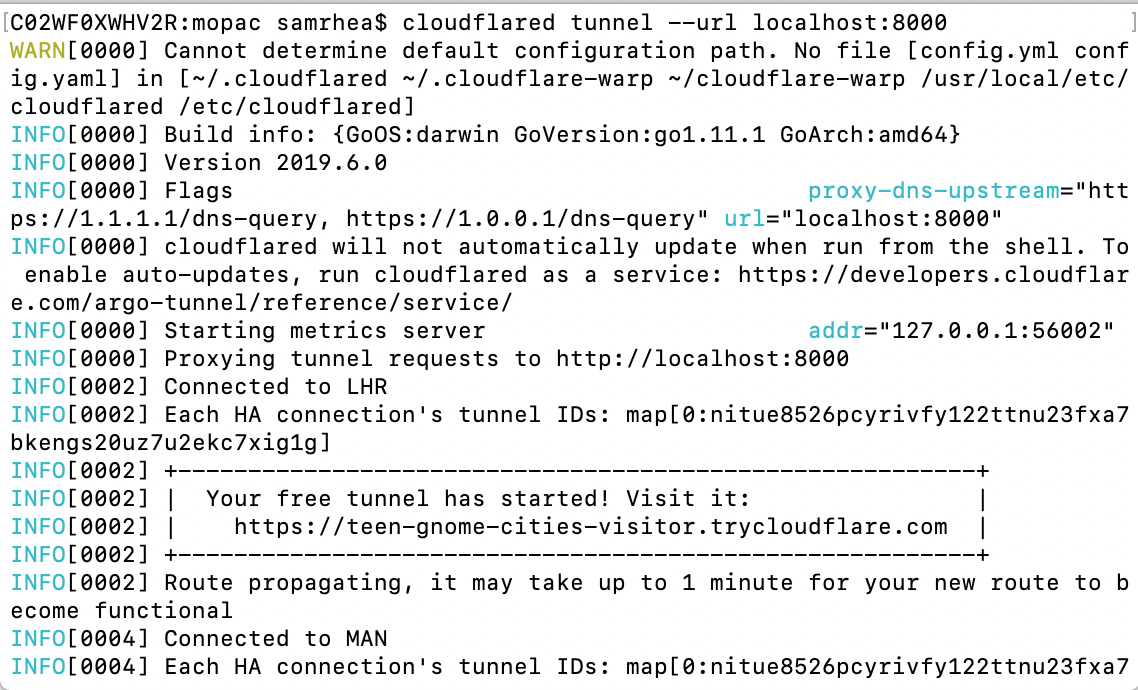
Argo Tunnel lets you expose a server to the Internet without opening any ports. The service runs a lightweight process on your server that creates outbound tunnels to the Cloudflare network. Instead of managing DNS, network, and firewall complexity, Argo Tunnel helps administrators serve traffic from their origin through Cloudflare with a single command.
We built Argo Tunnel to remove the burden of securing and connecting servers to the Internet. This new model makes it easier to run a service in multi-cloud and hybrid deployments by replacing manual and error-prone work with a process that adds intelligence to the last-mile between Cloudflare and your origins or clusters. However, the service was previously only available to users with Cloudflare accounts. We want to make Argo Tunnel more accessible for any project.
Starting today, any user, even those without a Cloudflare account, can try this new method of connecting their server to the Internet. Argo Tunnel can now be used in a free model that will create a new URL, known only to you, that will proxy traffic to your server. We’re excited to make connecting a server to the Internet more accessible for everyone.
What is Argo Tunnel?
Argo Tunnel replaces Continue reading
Censorship vs. the memes
- you can't yell fire in a crowded movie theater
- but this speech is harmful
- Karl Popper's Paradox of Tolerance
- censorship/free-speech don't apply to private organizations
- Twitter blocks and free speech
In other words, how can it be used to justify the thing you are trying to censor and yet be an invalid justification for Continue reading
Protecting Project Galileo websites from HTTP attacks
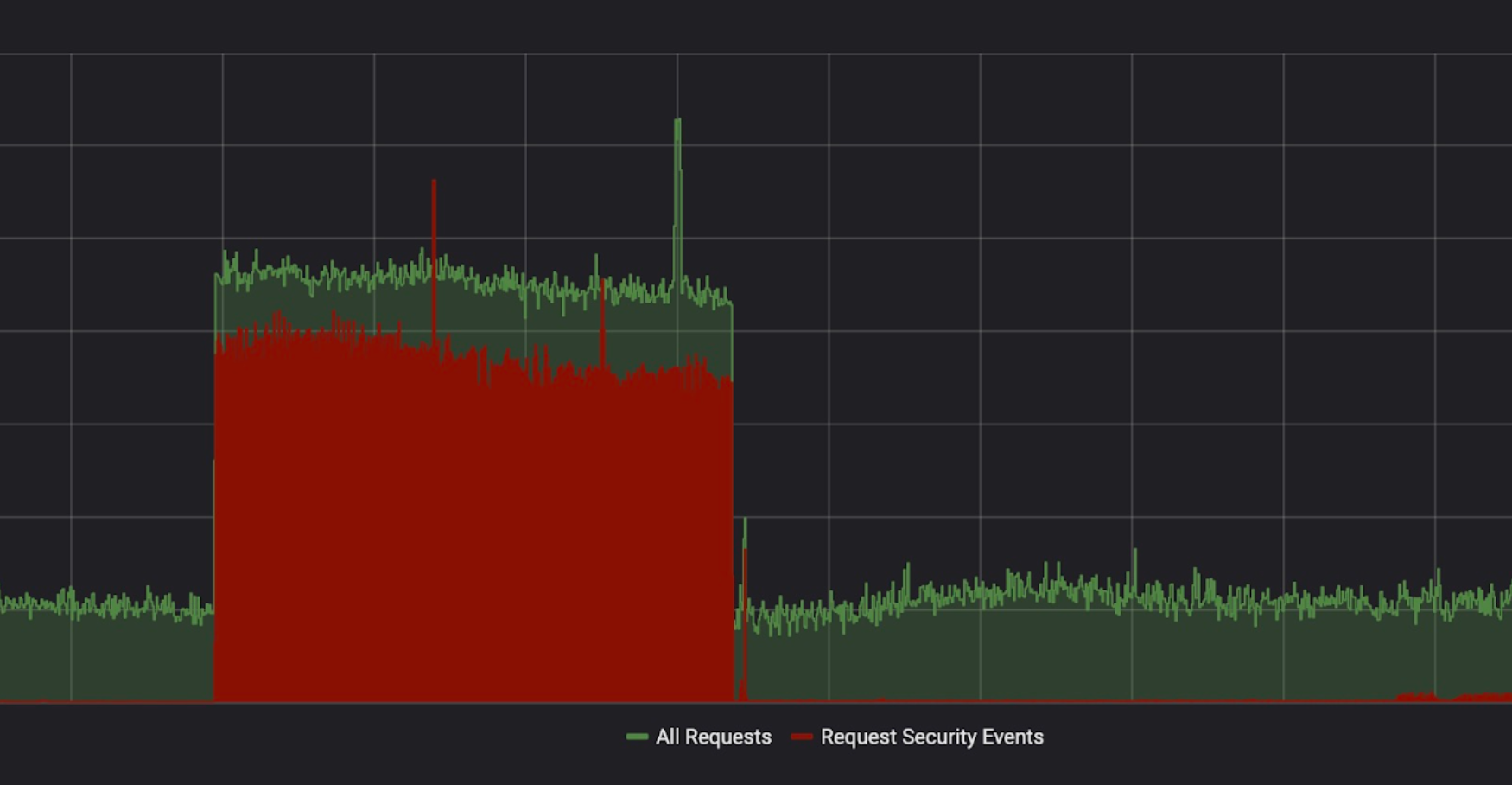
Yesterday, we celebrated the fifth anniversary of Project Galileo. More than 550 websites are part of this program, and they have something in common: each and every one of them has been subject to attacks in the last month. In this blog post, we will look at the security events we observed between the 23 April 2019 and 23 May 2019.
Project Galileo sites are protected by the Cloudflare Firewall and Advanced DDoS Protection which contain a number of features that can be used to detect and mitigate different types of attack and suspicious traffic. The following table shows how each of these features contributed to the protection of sites on Project Galileo.
|
Firewall Feature |
Requests Mitigated |
Distinct originating IPs |
Sites Affected (approx.) |
|
78.7M |
396.5K |
~ 30 |
|
|
41.7M |
1.8M |
~ 520 |
|
|
24.0M |
386.9K |
~ 200 |
|
|
9.4M |
32.2K |
~ 500 |
|
|
4.5M |
163.8K |
~ 200 |
|
|
2.3M |
1.3K |
~ 15 |
|
|
2.0M |
686.7K |
~ 40 |
|
|
1.6M |
360 |
1 |
|
|
623.5K |
6.6K |
~ 15 |
|
|
9.7K |
2.8K |
Home on the Palo Alto Networks Cyber Range

You’ve probably heard many horror stories by now about the crazy interviews that companies in Silicon Valley put you though. Sure, some of the questions are downright silly. How would I know how to weigh the moon? But the most insidious are the ones designed to look like skills tests. You may have to spend an hour optimizing a bubble sort or writing some crazy code that honestly won’t have much impact on the outcome of what you’ll be doing for the company.
Practical skills tests have always been the joy and the bane of people the world over. Many disciplines require you to have a practical examination before you can be certified. Doctors are one. The Cisco CCIE is probably the most well-known in IT. But what is the test really quizzing you on? Most people will admit that the CCIE is an imperfect representation of a network at best. It’s a test designed to get people to think about networks in different ways. But what about other disciplines? What about the ones where time is even more of the essence than it was in CCIE lab?
Red Team Go!
I was at Palo Alto Networks Ignite19 this past Continue reading
Technology’s Promise – Highlights from DEF CON China 1.0

DEF CON is one of the largest and oldest security conferences in the world. Last year, it launched a beta event in China in hopes of bringing the local security communities closer together. This year, the organizer made things official by introducing DEF CON China 1.0 with a promise to build a forum for China where everyone can gather, connect, and grow together.
Themed "Technology's Promise", DEF CON China kicked off on 5/30 in Beijing and attracted participants of all ages. Watching young participants test, play and tinker with new technologies with such curiosity and excitement absolutely warmed our hearts!
It was a pleasure to participate in DEF CON China 1.0 this year and connect with local communities. Great synergy as we exchanged ideas and learnings on cybersecurity topics. Did I mention we also spoiled ourselves with the warm hospitality, wonderful food, live music, and amazing crowd while in Beijing.
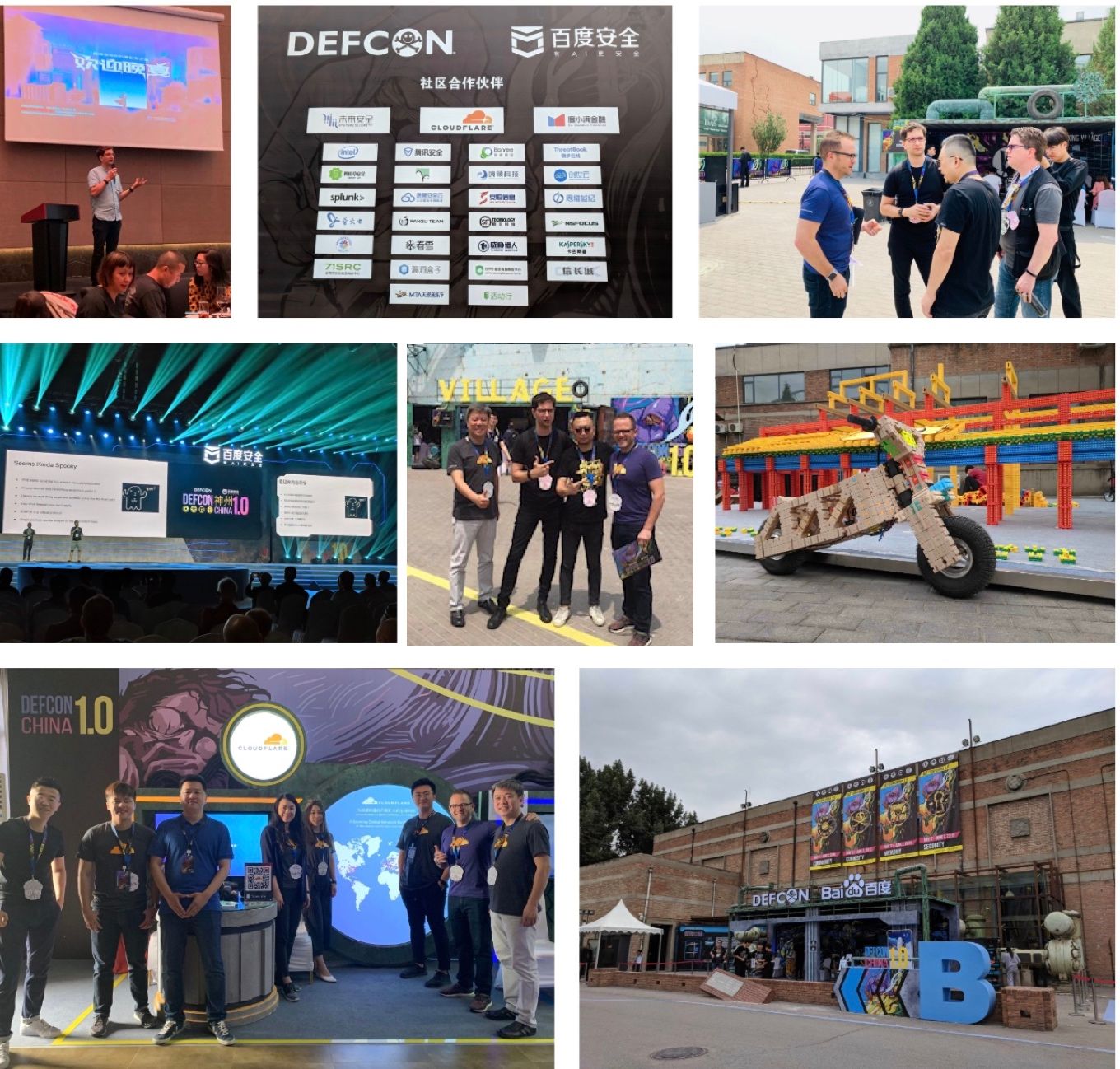
Meet our youngest and cutest attendee today at BugZee village. Meet 8 year old "Joy" from Beijing who did phenomenal soldering. Amazing crowd at Continue reading
Some Raspberry Pi compatible computers
I noticed this spreadsheet over at r/raspberry_pi reddit. I thought I'd write up some additional notes.https://docs.google.com/spreadsheets/d/1jWMaK-26EEAKMhmp6SLhjScWW2WKH4eKD-93hjpmm_s/edit#gid=0
Consider the Upboard, an x86 computer in the Raspberry Pi form factor for $99. When you include storage, power supplies, heatsinks, cases, and so on, it's actually pretty competitive. It's not ARM, so many things built for the Raspberry Pi won't necessarily work. But on the other hand, most of the software built for the Raspberry Pi was originally developed for x86 anyway, so sometimes it'll work better.
Consider the quasi-RPi boards that support the same GPIO headers, but in a form factor that's not the same as a RPi. A good example would be the ODroid-N2. These aren't listed in the above spreadsheet, but there's a tone of them. There's only two Nano Pi's listed in the spreadsheet having the same form factor as the RPi, but there's around 20 different actual boards with all sorts of different form factors and capabilities.
Consider the heatsink, which can make a big difference in the performance and stability of the board. You can put a small heatsink on any board, but you really need larger heatsinks and possibly fans. Some boards, Continue reading
Your threat model is wrong
Several subjects have come up with the past week that all come down to the same thing: your threat model is wrong. Instead of addressing the the threat that exists, you've morphed the threat into something else that you'd rather deal with, or which is easier to understand.Phishing
An example is this question that misunderstands the threat of "phishing":
Should failing multiple phishing tests be grounds for firing? I ran into a guy at a recent conference, said his employer fired people for repeatedly falling for (simulated) phishing attacks. I talked to experts, who weren't wild about this disincentive. https://t.co/eRYPZ9qkzB pic.twitter.com/Q1aqCmkrWL— briankrebs (@briankrebs) May 29, 2019
Recently, my university sent me an email for mandatory Title IX training, not digitally signed, with an external link to the training, that requested my university login Continue reading
Stopping SharePoint’s CVE-2019-0604
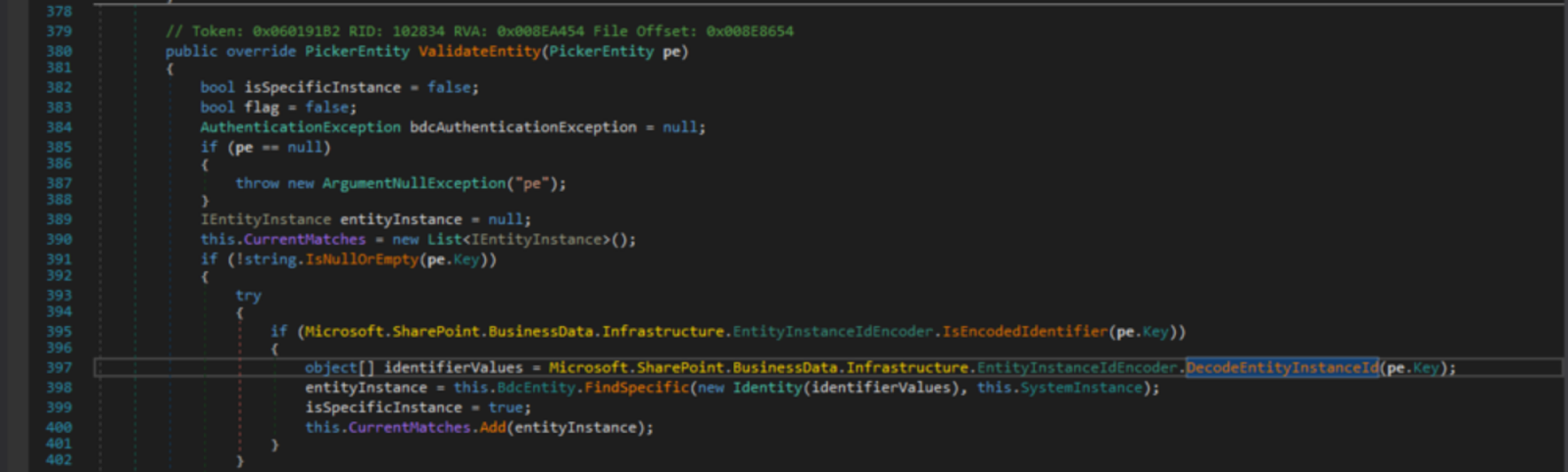
On Saturday, 11th May 2019, we got the news of a critical web vulnerability being actively exploited in the wild by advanced persistent threats (APTs), affecting Microsoft’s SharePoint server (versions 2010 through 2019).
This was CVE-2019-0604, a Remote Code Execution vulnerability in Microsoft SharePoint Servers which was not previously known to be exploitable via the web.
Several cyber security centres including the Canadian Centre for Cyber Security and Saudi Arabia’s National Center put out alerts for this threat, indicating it was being exploited to download and execute malicious code which would in turn take complete control of servers.
The affected software versions:
- Microsoft SharePoint Foundation 2010 Service Pack 2
- Microsoft SharePoint Foundation 2013 Service Pack 1
- Microsoft SharePoint Server 2010 Service Pack 2
- Microsoft SharePoint Server 2013 Service Pack 1
- Microsoft SharePoint Enterprise Server 2016
- Microsoft SharePoint Server 2019
Introduction
The vulnerability was initially given a critical CVSS v3 rating of 8.8 on the Zero Day Initiative advisory (however the advisory states authentication is required). This would imply only an insider threat, someone who has authorisation within SharePoint, such as an employee, on the local network could exploit the vulnerability.
We discovered that was not always Continue reading
Almost One Million Vulnerable to BlueKeep Vuln (CVE-2019-0708)
Microsoft announced a vulnerability in it's "Remote Desktop" product that can lead to robust, wormable exploits. I scanned the Internet to assess the danger. I find nearly 1-million devices on the public Internet that are vulnerable to the bug. That means when the worm hits, it'll likely compromise those million devices. This will likely lead to an event as damaging as WannaCry and notPetya from 2017 -- potentially worse, as hackers have since honed their skills exploiting these things for ransomware and other nastiness.CheriABI: enforcing valid pointer provenance and minimizing pointer privilege in the POSIX C run-time environment
CheriABI: enforcing valid pointer provenance and minimizing pointer privilege in the POSIX C run-time environment Davis et al., ASPLOS’19
Last week we saw the benefits of rethinking memory and pointer models at the hardware level when it came to object storage and compression (Zippads). CHERI also rethinks the way that pointers and memory work, but the goal here is memory protection. The scope of the work stands out as particularly impressive:
We have adapted a complete C, C++, and assembly-language software stack, including the open source FreeBSD OS (nearly 800 UNIX programs and more than 200 libraries including OpenSSH, OpenSSL, and bsnmpd) and PostgreSQL database, to employ ubiquitous capability-based pointer and virtual-address protection.
The protections are hardware implemented and cannot be forged in software. The process model, user-kernel interactions, dynamic linking, and memory management concerns are all in scope, and the protection spans the OS/DBMS boundary.
The basic question here is whether it is practical to support a large-scale C-language software stack with strong pointer-based protection… with only modest changes to existing C code-bases and with reasonable performance cost. We answer this question affirmatively.
That ‘reasonable’ performance cost is a 6.8% slowdown, significantly better than e. Continue reading
A lesson in journalism vs. cybersecurity
A recent NYTimes article blaming the NSA for a ransomware attack on Baltimore is typical bad journalism. It's an op-ed masquerading as a news article. It cites many to support the conclusion the NSA is to be blamed, but only a single quote, from the NSA director, from the opposing side. Yet many experts oppose this conclusion, such as @dave_maynor, @beauwoods, @daveaitel, @riskybusiness, @shpantzer, @todb, @hrbrmstr , ... It's not as if these people are hard to find, it's that the story's authors didn't look.The main reason experts disagree is that the NSA's Eternalblue isn't actually responsible for most ransomware infections. It's almost never used to start the initial infection -- that's almost always phishing or website vulns. Once inside, it's almost never used to spread laterally -- that's almost always done with windows networking and stolen credentials. Yes, ransomware increasingly includes Eternalblue as part of their arsenal of attacks, but this doesn't mean Eternalblue is responsible for ransomware.
The NYTimes story takes extraordinary effort to jump around this fact, deliberately misleading the reader to conflate one with the other. A good example is this paragraph:
GDPR and Privacy
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3.0 License
http://creativecommons.org/licenses/by/3.0/
Increasing Entropy with Crypto4A

Have you ever thought about the increasing disorder in your life? Sure, it may seem like things are constantly getting crazier every time you turn around, but did you know that entropy is always increasing in the universe? It’s a Law of Thermodynamics!
The idea that organized systems want to fall into disorder isn’t too strange when you think about it. Maintaining order takes a lot of effort and disorder is pretty easy to accomplish by just giving up. Anyone with a teenager knows that the amount of disorder that can be accomplished in a bedroom is pretty impressive.
One place where we don’t actually see a lot of disorder is in the computing realm. Computers are based on the idea that there is order and rationality in everything that we do. This is so prevalent that finding a way to be random is actually pretty hard. Computer programmers have tried a number of ways to come up with random number generators that take a variety of inputs into the formula and come up with something that looks sufficiently random. For most people just wanting the system to guess a number between 1 and 100 it’s not too bad. But Continue reading
Insider Threats and Facebook’s Poor Password Management

Storing passwords in clear text is a bonanza for insider threats. Who knows what they got ?
The post Insider Threats and Facebook’s Poor Password Management appeared first on EtherealMind.
The Internet Society’s African Chapters Join the African Union and Other Partners to Discuss IoT Security, Privacy, and Digital ID in Africa

In collaboration with the Africa Union Commission (AUC), the Africa Telecommunication Union (ATU), and Omidyar Network, from 8-11 April 2019 the Africa Regional Bureau successfully gathered in Addis Ababa, Ethiopia 103 participants comprising Internet Society Chapter leaders, African Regional economic bodies, privacy experts, regulators, and data protection agencies to a two-day workshop on IoT Security, Privacy, and Digital ID followed by the 2019 African Chapters Advocacy Meeting.
The first day of the workshop focused on IoT opportunities and security considerations. It explored the IoT landscape in Africa and shared active deployments and chapter-led projects. The day also discussed IoT security and privacy considerations with emphasis on frameworks that could be implemented to ensure the security and safety of IoT devices. A dedicated session on aligning policy and IoT security needs shared the experience of the Senegal multistakeholder IoT security process and motivated member states to initiate a similar process in their countries.
The second day focused on localizing the AUC and Internet Society Personal Data Protection Guidelines. Our partners AUC, Omidyar Network, Mozilla Foundation, and UNECA unpacked issues related to digital identity, personal data protection and privacy in the region. The meeting explored the nature of policies in place to Continue reading
10 Years of Auditing Online Trust – What’s Changed?

Last week we released the 10th Online Trust Audit & Honor Roll, which is a comprehensive evaluation of an organization’s consumer protection, data security, and privacy practices. If you want to learn more about this year’s results, please join us for our webinar on Wednesday, 24 April, at 1PM EDT / 5PM UTC. Today, though, we thought it would be interesting to see how the Audit and results have evolved over time. Here are some quick highlights over the years:
- 2005 – The Online Trust Alliance issued “scorecards” tracking adoption of email authentication (SPF) in Fortune 500 companies.
- 2008 – Added DKIM tracking to the scorecards, and extended the sectors to include the US federal government, banks, and Internet retailers.
- 2009 – Shifted from scorecard to “Audit” because criteria were expanded to include Extended Validation (EV) certificates and elements of site security (e.g., website malware).
- 2010 – Introduced the Honor Roll concept, highlighting organizations following best practices. Only 8% made the Honor Roll.
- 2012 – Expanded criteria to include DMARC, Qualys SSL Labs website assessment, and scoring of privacy statements and trackers. Shifted overall sector focus to consumer-facing organizations, so dropped the Fortune 500 and added Continue reading
Programming languages infosec professionals should learn
Code is an essential skill of the infosec professional, but there are so many languages to choose from. What language should you learn? As a heavy coder, I thought I'd answer that question, or at least give some perspective.The tl;dr is JavaScript. Whatever other language you learn, you'll also need to learn JavaScript. It's the language of browsers, Word macros, JSON, NodeJS server side, scripting on the command-line, and Electron apps. You'll also need to a bit of bash and/or PowerShell scripting skills, or SQL for queries. Other languages are important as well, Python is very popular for example. Actively avoid C++ and PHP as they are obsolete.
Also tl;dr: whatever language you decide to learn, also learn how to use an IDE with visual debugging, rather than just a text editor. That problems means Visual Code from Microsoft.
Let's talk in general terms. Here are some types of languages.
- Unavoidable. As mentioned above, familiarity with JavaScript, bash/Powershell, and SQL are unavoidable. If you are avoiding them, you are doing something wrong.
- Small scripts. You need to learn at least one language for writing quick-and-dirty command-line scripts to automate tasks or process data. As a tool using animal, this Continue reading
Was it a Chinese spy or confused tourist?
Politico has an article from a former spy analyzing whether the "spy" they caught at Mar-a-lago (Trump's Florida vacation spot) was actually a "spy". I thought I'd add to it from a technical perspective about her malware, USB drives, phones, cash, and so on.The part that has gotten the most press is that she had a USB drive with evil malware. We've belittled the Secret Service agents who infected themselves, and we've used this as the most important reason to suspect she was a spy.
But it's nonsense.
It could be something significant, but we can't know that based on the details that have been reported. What the Secret Service reported was that it "started installing software". That's a symptom of a USB device installing drivers, not malware. Common USB devices, such as WiFi adapters, Bluetooth adapters, microSD readers, and 2FA keys look identical to flash drives, and when inserted into a computer, cause Windows to install drivers.
Visual "installing files" is not a symptom of malware. When malware does its job right, there are no symptoms. It installs invisibly in the background. Thats the entire point of malware, that you don't know it's there. It's not to say Continue reading