Palo Alto Networks Pays $173M for Cloud Security Startup RedLock
 Palo Alto Networks plans to combine technologies from RedLock and Evident, another recent acquisition, into one product that provides cloud security analytics, advanced threat detection, continuous security, and compliance monitoring.
Palo Alto Networks plans to combine technologies from RedLock and Evident, another recent acquisition, into one product that provides cloud security analytics, advanced threat detection, continuous security, and compliance monitoring.
Cisco’s David Ulevitch Leaves to Join a VC Firm
 David Ulevitch, who was once in charge of Cisco’s security business, is leaving to become a general partner at Andreesson Horowitz.
David Ulevitch, who was once in charge of Cisco’s security business, is leaving to become a general partner at Andreesson Horowitz.
Cloudflare Access: Sharing our single-sign on plugin for Atlassian
Here at Cloudflare, we rely on a set of productivity tools built by Atlassian, including Jira and Confluence. We secure them with Cloudflare Access. In the past, when our team members wanted to reach those applications, they first logged in with our identity provider credentials to pass Access. They then broke out a second set of credentials, specific to Atlassian tools, to reach Jira. The flow is inconvenient on a desktop and downright painful on a mobile device.
While Access can determine who should be able to reach an application, the product alone cannot decide what the user should be able to do once they arrive at the destination. The application sets those specific permissions, typically by requiring another set of user credentials. The extra step slows down and frustrates end users. Access saves time by replacing a cumbersome VPN login. However, we wanted to also solve the SSO problem for our team.
We created a plugin, specific to Atlassian, that could take identity data from the token generated by Access and map it to a user account. Our team members log in with our identity provider to pass Access, and then Access could set their user permissions in Jira Continue reading
Cohesity Targets Service Providers With Multi-Tenant Platform
 The software-defined platform runs on top of Cohesity, Cisco, HPE, or Dell EMC hyperconverged secondary storage appliances.
The software-defined platform runs on top of Cohesity, Cisco, HPE, or Dell EMC hyperconverged secondary storage appliances.
Putting the M in MANO
 In the rush to capitalize on NFV many operators have focused purely on the NFV orchestration, but as they move from trials to production, one key piece is missing — management.
In the rush to capitalize on NFV many operators have focused purely on the NFV orchestration, but as they move from trials to production, one key piece is missing — management.
AWS ABCs – Can I Firewall My Compute Instances?
In a previous post, I reviewed what a public subnet and Internet Gateway (IGW) are and that they allowed outbound and inbound connectivity to instances (ie, virtual machines) running in the AWS cloud.
If you’re the least bit security conscious, your reaction might be, “No way! I can’t have my instances sitting right on the Internet without any protection”.
Fear not, reader. This post will explain the mechanisms that the Amazon Virtual Private Cloud (VPC) affords you to protect your instances.
Security Groups
In a nutshell: security groups (SGs) define what traffic is allowed to reach an instance.
“Security group” is a bit of a weird name for what is essentially a firewall that sits in front of an instance, however if you think about it in terms of all servers at a particular tier in an N-tier application (eg, all the web servers) or all the servers that have a common function (eg, all PostgreSQL servers) and how each group would have its own security requirements when it comes to allowed ports, protocols, and IP addresses, then it makes a bit more sense: the security rules appropriate for a group of servers are all put together within Continue reading
The Facebook Breach: Some Lessons for the Internet
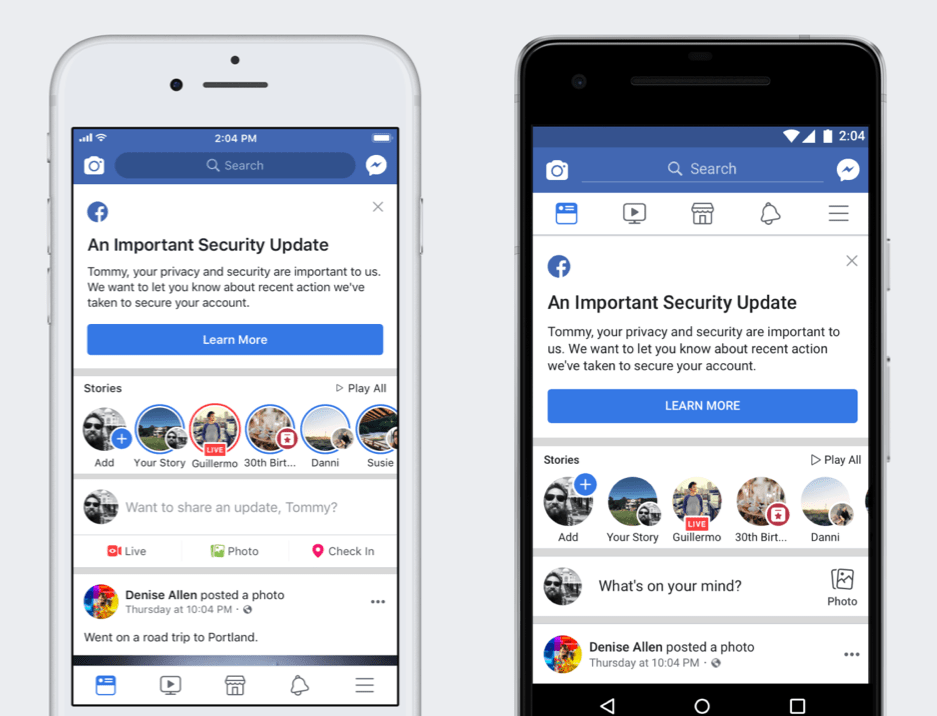
Last week Facebook found itself at the heart of a security breach that put at risk the personal information of millions of users of the social network.
On September 28, news broke that an attacker exploited a technical vulnerability in Facebook’s code that would allow them to log into about 50 million people’s accounts.
While Facebook was quick to address the exploit and fix it, they say they don’t know if anyone’s accounts actually were breached.
This breach follows the Cambridge Analytica scandal earlier this year that resulted in the serious mishandling of the data of millions of people who use Facebook.
Both of these events illustrate that we cannot be complacent about data security. Companies that hold personal and sensitive data need to be extra vigilant about protecting their users’ data.
Yet even the most vigilant are also vulnerable. Even a single security bug can affect millions of users, as we can see.
There are a few things we can learn from this that applies to the other security conversations: Doing security well is notoriously hard, and persistent attackers will find bugs to exploit, in this case a combination of three apparently unrelated ones on the Facebook platform.
This Continue reading
Mini pwning with GL-iNet AR150
Seven years ago, before the $35 Raspberry Pi, hackers used commercial WiFi routers for their projects. They'd replace the stock firmware with Linux. The $22 TP-Link WR703N was extremely popular for these projects, being half the price and half the size of the Raspberry Pi.Unfortunately, these devices had extraordinarily limited memory (16-megabytes) and even more limited storage (4-megabyte). That's megabytes -- the typical size of an SD card in an RPi is a thousand times larger.
I'm interested in that device for the simple reason that it has a big-endian CPU.
All these IoT-style devices these days run ARM and MIPS processors, with a smattering of others like x86, PowerPC, ARC, and AVR32. ARM and MIPS CPUs can run in either mode, big-endian or little-endian. Linux can be compiled for either mode. Little-endian is by far the most popular mode, because of Intel's popularity. Code developed on little-endian computers sometimes has subtle bugs when recompiled for big-endian, so it's best just to maintain the same byte-order as Intel. On the other hand, popular file-formats and crypto-algorithms use big-endian, so there's some efficiency to be gained with going with that choice.
I'd like to have a big-endian computer around to Continue reading
Birthday Week Wrap-Up: Every day is launch day at Cloudflare
Our customers are accustomed to us launching new services, features, and functionality at a feverish pace, but recently, we’ve been especially active. This week we celebrated our 8th Birthday Week by announcing new offerings that benefit our customers and the global Internet community. Our mission is to help build a better Internet, and we’re convinced that launching new capabilities that benefit not only our customers, but also the broader Internet overall, is the best way to fulfill our mission.
Helping build a better Internet, one launch at a time
As an organization, we could choose to celebrate Cloudflare’s birthday in lots of different ways (a press release, a company party, or fun gifts for all our employees). But at Cloudflare, we have a unique birthday tradition: we roll up our sleeves and give our customers and the Internet community a new capability (i.e. a gift) every day of our birthday week.
Some of this past week’s launches have been entirely new offerings, like providing key-value storage across Cloudflare’s global cloud network with Cloudflare Workers KV. Other birthday week launches help improve the overall Internet ecosystem: the Bandwidth Alliance reduces data transfer charges from major cloud hosts and Cloudflare Registrar Continue reading
Barefoot Preps for 5G and IoT With Its Tofino Chip and the P4 Language
 Paired with the P4 programming language, Barefoot’s Tofino chip gives users the freedom to design what the chip can do.
Paired with the P4 programming language, Barefoot’s Tofino chip gives users the freedom to design what the chip can do.
Alphabet’s Chronicle Launches VirusTotal Enterprise With 100x Faster Malware Search
 VirusTotal also has new capabilities to help companies’ threat intelligence teams better analyze massive amounts of data.
VirusTotal also has new capabilities to help companies’ threat intelligence teams better analyze massive amounts of data.
Security Best Practices for Cloud-Native and Hybrid Cloud Organizations
 Both cloud-native and traditional organizations must implement a security practice that offers automation, abstraction, flexibility, visibility, and is application-aware.
Both cloud-native and traditional organizations must implement a security practice that offers automation, abstraction, flexibility, visibility, and is application-aware.
Buyer’s Guide: Modern Web-Scale Backup and Recovery
 The Buyer’s Guide to Modern Backup is the definitive resource to help you make the right choice for your next data protection solution. Download the buyer's guide today.
The Buyer’s Guide to Modern Backup is the definitive resource to help you make the right choice for your next data protection solution. Download the buyer's guide today.
CNCF, Eclipse Foundation Push Kubernetes to the Edge
 The Kubernetes IoT Edge Working Group is looking to see how far it can push the centralized Kubernetes platform out into the distributed edge and IoT ecosystem.
The Kubernetes IoT Edge Working Group is looking to see how far it can push the centralized Kubernetes platform out into the distributed edge and IoT ecosystem.
The QUICening
Six o’clock already, I was just in the middle of a dream, now I’m up, awake, looking at my Twitter stream. As I do that the Twitter app is making multiple API calls over HTTPS to Twitter’s servers somewhere on the Internet.
Those HTTPS connections are running over TCP via my home WiFi and broadband connection. All’s well inside the house, the WiFi connection is interference free thanks to my eero system, the broadband connection is stable and so there’s no packet loss, and my broadband provider’s connection to Twitter’s servers is also loss free.

Those are the perfect conditions for HTTPS running over TCP. Not a packet dropped, not a bit of jitter, no congestion. It’s even the perfect conditions for HTTP/2 where multiple streams of requests and responses are being sent from my phone to websites and APIs as I boot my morning. Unlike HTTP/1.1, HTTP/2 is able to use a single TCP connection for multiple, simultaneously in flight requests. That has a significant speed advantage over the old way (one request after another per TCP connection) when conditions are good.
But I have to catch an early train, got to be to work by nine, so Continue reading
BGP Security: A Gentle Reminder that Networking is Business
At NANOG on the Road (NotR) in September of 2018, I participated in a panel on BGP security—specifically the deployment of Route Origin Authentication (ROA), with some hints and overtones of path validation by carrying signatures in BGP updates (BGPsec). This is an area I have been working in for… 20 years? … at this point, so I have seen the argument develop across these years many times, and in many ways. What always strikes me about this discussion, whenever and wherever it is aired, is the clash between business realities and the desire for “someone to do something about routing security in the DFZ, already!” What also strikes me about these conversations it the number of times very fundamental concepts end up being explained to folks who are “new to the problem.”
- BGP security is a business problem first, and a technology problem second
- Signed information is only useful insofar as it is maintained
- The cost of deployment must be lower than the return on that cost
- Local policy will always override global policy—as it should
- The fear of losing business is a stronger motivator than gaining new business
Part of the problem here is Continue reading
Encrypt it or lose it: how encrypted SNI works


Today we announced support for encrypted SNI, an extension to the TLS 1.3 protocol that improves privacy of Internet users by preventing on-path observers, including ISPs, coffee shop owners and firewalls, from intercepting the TLS Server Name Indication (SNI) extension and using it to determine which websites users are visiting.
Encrypted SNI, together with other Internet security features already offered by Cloudflare for free, will make it harder to censor content and track users on the Internet. Read on to learn how it works.
SNWhy?
The TLS Server Name Indication (SNI) extension, originally standardized back in 2003, lets servers host multiple TLS-enabled websites on the same set of IP addresses, by requiring clients to specify which site they want to connect to during the initial TLS handshake. Without SNI the server wouldn’t know, for example, which certificate to serve to the client, or which configuration to apply to the connection.
The client adds the SNI extension containing the hostname of the site it’s connecting to to the ClientHello message. It sends the ClientHello to the server during the TLS handshake. Unfortunately the ClientHello message is sent unencrypted, due to the fact that client and server don’t share Continue reading
Encrypting SNI: Fixing One of the Core Internet Bugs
Cloudflare launched on September 27, 2010. Since then, we've considered September 27th our birthday. This Thursday we'll be turning 8 years old.
Ever since our first birthday, we've used the occasion to launch new products or services. Over the years we came to the conclusion that the right thing to do to celebrate our birthday wasn't so much about launching products that we could make money from but instead to do things that were gifts back to our users and the Internet in general. My cofounder Michelle wrote about this tradition in a great blog post yesterday.
Personally, one of my proudest moments at Cloudflare came on our birthday in 2014 when we made HTTPS support free for all our users. At the time, people called us crazy — literally and repeatedly. Frankly, internally we had significant debates about whether we were crazy since encryption was the primary reason why people upgraded from a free account to a paid account.
But it was the right thing to do. The fact that encryption wasn't built into the web from the beginning was, in our mind, a bug. Today, almost exactly four years later, the web is nearly 80% encrypted thanks to Continue reading
Cloudflare Turns 8 — here’s what we mean by a “better Internet”

I have always loved birthdays. It is a chance to get together with loved ones, a chance to have fun and a chance to reflect on anything you want to keep doing or change in the upcoming year. At Cloudflare, we’ve embraced celebrating our birthday as well.
This week, Cloudflare turns 8 years old. It feels like just yesterday that Matthew, Lee, Matthieu, Ian, Sri, Chris, Damon and I stepped on stage at Techcrunch Disrupt to launch Cloudflare to the world. Since then, we have celebrated our birthday every year by giving a gift back to our customers and the Internet. This year, we plan to celebrate each day with a new product benefiting our community. Or in other words, it is a weeklong birthday celebration. Like I said, I love birthdays!

The Cloudflare team when we launched the service at Techcrunch Disrupt during September 27 to 29, 2010 – Matthieu, Chris, Sri, Ian, Lee, Matthew, Michelle and Damon.
While I can’t share exactly what we’re releasing every day — after all who doesn’t like a surprise? — I wanted to share some thoughts on how we decide what to release birthday week.
Our mission at Cloudflare is to help Continue reading
Cyber Threat Alliance Reports 459% Spike in Cryptomining Malware
 “If you’ve got mining happening on your network, you probably have other bad stuff happening on your network, and it’s probably much worse than mining,” said CTA’s Neil Jenkins.
“If you’ve got mining happening on your network, you probably have other bad stuff happening on your network, and it’s probably much worse than mining,” said CTA’s Neil Jenkins.