A Deeper Dive Into Public DNS Resolver Quad9
There are plenty of public DNS resolvers. The best known was Google Public DNS i.e. 8.8.8.8 and 8.8.4.4 for IPv4 and 2001:4860:4860::8888 and 2001:4860:4860::8844 for IPv6. But there are a few other options available now, each with different policies and technical features.
Two new Public DNS resolvers were recently launched. Quad9 (launched Nov 2017) and 1dot1dot1dot1 (launched Apr 2018). We have already covered 1.1.1.1 in detail in a recent blog. So let’s talk about Quad9 (9.9.9.9).
The Global Cyber Alliance (GCA), an organization founded by a partnership of law enforcement (New York County District Attorney and City of London Police) and research (Center for Internet Security – CIS) organizations focused on combating systemic cyber risk in real, measurable ways, partnered with IBM and Packet Clearing House (PCH) to launch a Global Public Recursive DNS Resolver Service. Quad9 protects users from accessing known malicious websites, leveraging threat intelligence from multiple industry leaders; it currently blocks up to two million threats per day.
A handy little infographic on the Quad9 website helps show how it works. Essentially, you set up Quad 9 as your Continue reading
Oblix: an efficient oblivious search index
Oblix: an efficient oblivious search index Mishra et al., IEEE Security & Privacy 2018
Unfortunately, many known schemes that enable search queries on encrypted data achieve efficiency at the expense of security, as they reveal access patterns to the encrypted data. In this paper we present
Oblix, a search index for encrypted data that is oblivious (provably hides access patterns) is dynamic (supports inserts and deletes), and has good efficiency.
There’s a lot to this paper! Starting with a recap of existing work on Path ORAM (Oblivious RAM) and Oblivious Data Structures (ODS), Mishra introduce an extension for an Oblivious Sorted Multimap (OSM) (such that you can look up a key and find a set of associated values, handy for building indexes!). Then because their design runs a client-proxy process inside an enclave at the server, and enclaves still leak some information, they also design “doubly-oblivious” versions of all of the above that hide the client access patterns in addition to those at the server process. It’s all topped off with an implementation in Rust (nice to see Rust being used for systems research), and an evaluation with three prime use cases: private contact discovery in Signal, Continue reading
ThetaRay Scores $30 Million Series B for AI-Powered Security
 The startup’s customers include banks and industrial firms. Its latest funding round brings its total to $60.5 million.
The startup’s customers include banks and industrial firms. Its latest funding round brings its total to $60.5 million.
Tracking DNSSEC: See the Deployment Maps
Did you know the Internet Society Deploy360 Programme provides a weekly view into global DNSSEC deployment? Each Monday, we generate new maps and send them to a public DNSSEC-Maps mailing list. We also update the DNSSEC Deployment Maps page periodically, usually in advance of ICANN meetings.
DNS Security Extensions — commonly known as DNSSEC — allow us to have more confidence in our online activities at work, home, and school. DNSSEC acts like tamper-proof packaging for domain name data, helping to ensure that you are communicating with the correct website or service. However, DNSSEC must be deployed at each step in the lookup from the root zone to the final domain name. Signing the root zone, generic Top Level Domains (gTLDs) and country code Top Level Domains (ccTLDs) is vital to this overall process. These maps help show what progress the Internet technical community is making toward the overall goal of full DNSSEC deployment.
These maps are a bit different from other DNSSEC statistics sites in that they contain both factual, observed information and also information based on news reports, presentations, and other collected data. For more information about how we track the deployment status of TLDs, please read our page Continue reading
EnclaveDB: a secure database using SGX
EnclaveDB: A secure database using SGX Priebe et al., IEEE Security & Privacy 2018
This is a really interesting paper (if you’re into this kind of thing I guess!) bringing together the security properties of Intel’s SGX enclaves with the Hekaton SQL Server database engine. The result is a secure database environment with impressive runtime performance. (In the read-mostly TATP benchmarks, overheads are down around 15%, which is amazing for this level of encryption and security). The paper does a great job showing us all of the things that needed to be considered to make EnclaveDB work so well in this environment.
One of my favourite takeaways is that we don’t always have to think of performance and security as trade-offs:
In this paper, we show that the principles behind the design of a high performance database engine are aligned with security. Specifically, in-memory tables and indexes are ideal data structures for securely hosting and querying sensitive data in enclaves.
Motivation and threat model
We host databases in all sorts of untrusted environments, potentially with unknown database administrators, server administrators, OS and hypervisors. How can we guarantee data security and integrity in such a world? Or even how Continue reading
Grand Pwning Unit: Accelerating microarchitectural attacks with the GPU
Grand Pwning Unit: Accelerating microarchitectural attacks with the GPU Frigo et al., IEEE Security & Privacy
The general awareness of microarchitectural attacks is greatly increased since meltdown and spectre earlier this year. A lot of time and energy has been spent in defending against such attacks, with a threat model that assumes attacks originate from the CPU. Frigo et al. open up an entirely new can of worms – modern SoCs contain a variety of special purpose accelerator units, chief among which is the GPU. GPUs are everywhere these days.
Unfortunately, the inclusion of these special-purpose units in the processor today appears to be guided by a basic security model that mainly governs access control, while entirely ignoring the threat of more advanced microarchitectural attacks.
I’m sure you know where this is heading…
It turns out the accelerators can also be used to “accelerate” microarchitectural attacks. Once more we find ourselves in a situation with widespread vulnerabilities. The demonstration target in the paper is a mobile phone running on the ARM platform, with all known defences, including any applicable advanced research defences, employed. Using WebGL from JavaScript, Frigo et al. show how to go from e.g. an advert Continue reading
CenturyLink Security Log Monitoring Increases Visibility Across Hybrid Networks
 Security Log Monitoring is a SaaS-based log collection and security information and event management (SIEM) platform built on open source and proprietary tools.
Security Log Monitoring is a SaaS-based log collection and security information and event management (SIEM) platform built on open source and proprietary tools.
The Week in Internet News: WiFi Gets a New Security Standard
A more secure Wi-Fi: The Wi-Fi Alliance has released the new WPA2 standard for WiFi that’s designed to mitigate several long-standing security problems. Among the fixes: The new standard mandates stronger WiFi passwords, Wired.com reports. The new standard also will include 192-bit encryption. The alliance also published the new WiFi Easy Connect protocol, designed for IoT devices that have limited or no display, says SlashGear.
Wait for us, says email: The Electronic Frontier Foundation, one of the organizations behind the HTTPS-encryption initiative Let’s Encrypt, has launched an email server encryption project called STARTTLS Everywhere. The project is designed to help admins run more secure email servers, Engadget reports.
AI targets fraud: Insurers are increasingly turning to artificial intelligence technologies to root out fraud, Fast Company says. AI can help pick out inconsistencies and unusual patterns to identify “sophisticated rings of fraudsters rigging auto accidents” and people exaggerating the worth of their damaged property.
AI also examines eruptions: Scientists at the Earth-Life Science Institute in Tokyo are using AI to help predict the types of eruptions coming from volcanos, says Phys.org. By examining tiny particles of volcanic ash, the AI is predicting the types of eruptions coming from Continue reading
The rise of the citizen developer: assessing the security impact of online app generators
The rise of the citizen developer: assessing the security impact of online app generators Oltrogge et al., IEEE Security & Privacy 2018
“Low code”, “no code”, “citizen developers”, call it what you will, there’s been a big rise in platforms that seek to make it easy to develop applications for non-export developers. Today’s paper choice studies the online application generator (OAG) market for Android applications. When what used to be a web site (with many successful web site templating and building options around) is often in many cases now also or instead a mobile app, so it makes sense that the same kind of templating and building approach should exist there too. For a brief period at the end of last year, Apple flirted with banning such apps from their app store, before back-tracking just a couple of weeks after the initial announcement. After reading today’s paper I can’t help but feel that perhaps they were on to something. Not that templated apps are bad per se, but when the generated apps contain widespread vulnerabilities and privacy issues, then that is bad.
With the increasing use of OAGs the duty of generating secure code shifts away from the Continue reading
Security Company Tenable Files for IPO
 An IPO could value value Tenable between $1.5 billion and $2 billion, according to anonymous sources.
An IPO could value value Tenable between $1.5 billion and $2 billion, according to anonymous sources.
Security Startup Preempt Closes $17.5M Series B, Scores ClearSky, Blackstone, and Intel Funding
 The company’s platform “preempts” threats (hence the name) based on identity, behavior, and risk. One of its new investors — Blackstone — started as a customer.
The company’s platform “preempts” threats (hence the name) based on identity, behavior, and risk. One of its new investors — Blackstone — started as a customer.
Delivering a Serverless API in 10 minutes using Workers
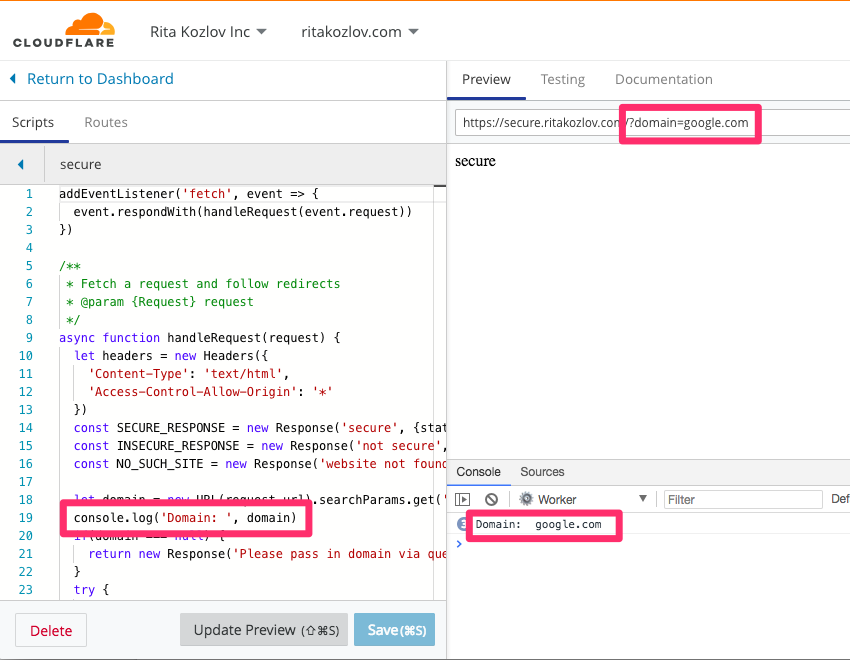
In preparation for Chrome’s Not Secure flag, which will update the indicator to show Not Secure when a site is not accessed over https, we wanted people to be able to test whether their site would pass. If you read our previous blog post about the existing misconceptions around using https, and preparing your site, you may have noticed a small fiddle, allowing you to test which sites will be deemed “Secure”. In preparation for the blog post itself, one of our PMs approached me asking for help making this fiddle come to life. It was a simple ask: we need an endpoint which runs logic to see if a given domain will automatically redirect to https.
The logic and requirements turned out to be very simple:
Make a serverless API endpoint
Input: domain (e.g. example.com)
Output: “secure” / “not secure”
Logic:
if http://example.com redirects to https://example.com
Return “secure”
Else
Return “not secure”
One additional requirement here was that we needed to follow redirects all the way; sites often redirect to http://www.example.com first, and only then redirect to https. That is an additional line of code I was prepared to handle.
I’ve done some Continue reading
Jask Raises $25M Series B Funding for Autonomous Security Platform
 This brings its total to $39 million. Kleiner Perkins led the funding round with participation from Battery Ventures, Dell Technologies Capital, TenEleven Ventures, and Vertical Venture Partners.
This brings its total to $39 million. Kleiner Perkins led the funding round with participation from Battery Ventures, Dell Technologies Capital, TenEleven Ventures, and Vertical Venture Partners.
NSX Cloud Blog Series Part 2: A Consistent Security Posture Across Your Hybrid Cloud
We now dig deeper into the cloud security use-case. As more and more companies embrace cloud, the cloud IT teams are tasked with the responsibility of ensuring that these cloud deployments are secure. Cloud inherently brings in new environments, and these cloud security teams are now faced with ensuring Enterprise security policy consistency across these multiple disparate cloud environments.
VMware NSX Cloud addresses these challenges, offering a common security and micro-segmentation platform across the on-premises and cloud environment. Together with NSX Data Center, it provides a single pane of glass to provision and manages consistent security controls not only for cross-cloud communication but also within each cloud.
Let’s start with VISIBILITY. You can’t protect what you can’t see. As a cloud infrastructure/security team, you may have to manage 1 AWS cloud account (subscription in Azure) and 1 AWS VPC (VNET in Azure) … or you may be managing 500+ accounts/subscriptions, each having multiple VPCs / VNETs. As cloud deployments bring automation and higher levels of agility, the cloud footprint that you would be responsible for can quickly become large and constantly evolve. How do you ensure that this dynamic environment is secure?
Focused on this specific Continue reading
T-25 days until Chrome starts flagging HTTP sites as “Not Secure”
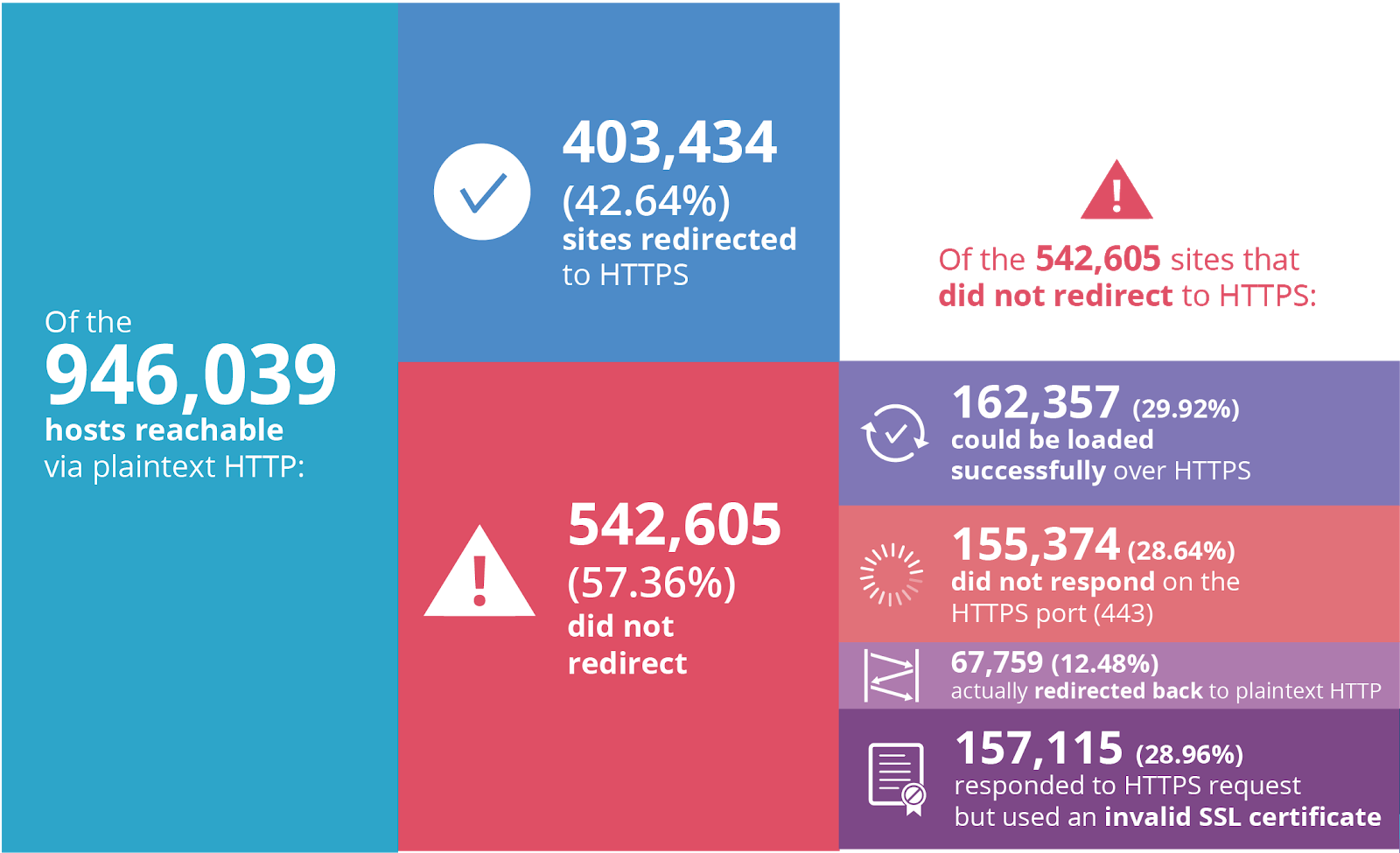
Less than one month from today, on July 23, Google will start prominently labeling any site loaded in Chrome without HTTPS as "Not Secure".
When we wrote about Google’s plans back in February, the percent of sites loaded over HTTPS clocked in at 69.7%. Just one year prior to that only 52.5% of sites were loaded using SSL/TLS—the encryption protocol behind HTTPS—so tremendous progress has been made.
Unfortunately, quite a few Continue reading
Lessons from nPetya one year later
This is the one year anniversary of NotPetya. It was probably the most expensive single hacker attack in history (so far), with FedEx estimating it cost them $300 million. Shipping giant Maersk and drug giant Merck suffered losses on a similar scale. Many are discussing lessons we should learn from this, but they are the wrong lessons.An example is this quote in a recent article:
"One year on from NotPetya, it seems lessons still haven't been learned. A lack of regular patching of outdated systems because of the issues of downtime and disruption to organisations was the path through which both NotPetya and WannaCry spread, and this fundamental problem remains."This is an attractive claim. It describes the problem in terms of people being "weak" and that the solution is to be "strong". If only organizations where strong enough, willing to deal with downtime and disruption, then problems like this wouldn't happen.
But this is wrong, at least in the case of NotPetya.
NotPetya's spread was initiated through the Ukraining company MeDoc, which provided tax accounting software. It had an auto-update process for keeping its software up-to-date. This was subverted in order to deliver the initial NotPetya Continue reading
John Chambers’ VC Firm Backs Security Startup Balbix’s $20M Series B
 Cavium, Nutanix, and Equinix are all customers using the security company’s predictive breach-risk platform.
Cavium, Nutanix, and Equinix are all customers using the security company’s predictive breach-risk platform.
Secure coding practices in Java: challenges and vulnerabilities
Secure coding practices in Java: challenges and vulnerabilities Meng et al., ICSE’18
TL;DR : don’t trust everything you read on Stack Overflow.
Meng et al. conduct a study of Stack Overflow posts relating to secure coding practices in Java to find out the hot topics, what people struggle with, and whether or not the accepted answers are actually following security best practices.
We conducted an empirical study on Stack Overflow posts, aiming to understand developer’s concerns on Java secure coding, their programming obstacles, and insecure coding practices. We observed a wide adoption of the authentication and authorization features provided by Spring Security — a third-party framework designed to secure enterprise applications…
Well, how could I resist reading that! (Some readers may know that I was for many years the CTO of SpringSource). Spring Security does come in for some flak in this paper for the high volume of questions that are asked relating to it. There’s no calibration though for underlying popularity. One of the reasons there are a lot of questions, I posit, is that there are an awful lot of users of Spring Security. Spring Boot applications will use Spring Security, and Spring Boot has been growing Continue reading
Pulse Secure Elevates vADC Assets to Google Cloud
 The vADC uses central management tools to accelerate service deployment and increase security, scalability, and resiliency of applications as enterprises migrate to the cloud.
The vADC uses central management tools to accelerate service deployment and increase security, scalability, and resiliency of applications as enterprises migrate to the cloud.