3 Bad Habits NetOps Should Avoid
Don't make these mistakes when adopting DevOps for production network automation and orchestration.
Don't make these mistakes when adopting DevOps for production network automation and orchestration.
All-flash system enables fast, cost-effective production for entertainment and media company.
This is the sixth article from the series of the articles discussing the configuration of an entire enterprise network. The article explains the configuration of the edge router vIOS-EDGE-I and configuration of ISP routers. Now let's say few words about the router vIOS-EDGE-I. The router is Cisco IOSv Qemu appliance, version 15.6(2)T. It has assigned 512MB RAM by GNS3. The router connects all three parts of the company network to the Internet. These parts are the the campus network, data center and DMZ.

Picture 1 - Company Connection to the Internet via vIOS-EDGE-I
The company has assigned the prefix 195.1.1.0/24. Devices located in DMZ have assigned the prefix 195.1.1.128/25. The prefix 195.1.1.0/25 is assigned for devices hidden behind NAT. NAT is configured on vIOS-EDGE-I router, translating campus and data center subnets to the subnet 195.1.1.128/25. The router is connected to the upstream providers via their Ethernet ports Gi0/1 and Gi0/3. This is a single multi homed topology when a company is connected to two upstream providers with a single edge router. The entire prefix 195.1.1.0/24 is advertised to the both ISPs via BGP routing protocol. Continue reading
This is the sixth article from the series of the articles discussing the configuration of an entire enterprise network. The article explains the configuration of the edge router vIOS-EDGE-I and configuration of ISP routers. Now let's say few words about the router vIOS-EDGE-I. The router is Cisco IOSv Qemu appliance, version 15.6(2)T. It has assigned 512MB RAM by GNS3. The router connects all three parts of the company network to the Internet. These parts are the the campus network, data center and DMZ.
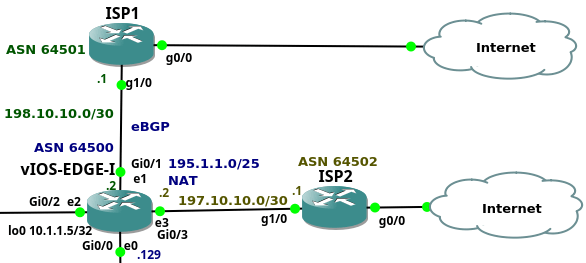
Picture 1 - Company Connection to the Internet via vIOS-EDGE-I
The company has assigned the prefix 195.1.1.0/24. Devices located in DMZ have assigned the prefix 195.1.1.128/25. The prefix 195.1.1.0/25 is assigned for devices hidden behind NAT. NAT is configured on vIOS-EDGE-I router, translating campus and data center subnets to the subnet 195.1.1.128/25. The router is connected to the upstream providers via their Ethernet ports Gi0/1 and Gi0/3. This is a single multi homed topology when a company is connected to two upstream providers with a single edge router. The entire prefix 195.1.1.0/24 is advertised to the both ISPs via BGP routing protocol. Continue reading
Although it’s almost three months till the start of the Building Next-Generation Data Center online course, we already have most of the guest speakers. Today I’d like to introduce the first two (although they need no introduction).
You might have heard about Russ White. He was known as Mr. CCDE when that program started and recently focused more on data centers, open networking and whitebox switching. He’s also an authority on good network design and architecture, network complexity, and tradeoffs you have to make when designing a network.
Read more ...Researcher Olexandr Isayev wasn’t just impressed to see an AI framework best the top player of a game so complex it was considered impossible for an algorithm to track. He was inspired.
“The analogy of the complexity of chemistry, the number of possible molecule we don’t know about, is roughly the same order of complexity of Go, the University of North Carolina computational biology and chemistry expert explained.
“Instead of playing with checkers on a board, we envisioned a neural network that could play the game of generating molecules—one that did not rely on human intuition for this initial but …
How AlphaGo Sparked a New Approach to De Novo Drug Design was written by Nicole Hemsoth at The Next Platform.
Tune into our live CCNA Kickoff session to get advice from a seasoned professional on what to expect during the CCNA Certification exam, and how to pass the first time.

When: February 1st at 10 am PST/ 1 pm EST
Estimated Length: 3 hours
Instructor: Keith Bogart CCIE #4923
Cost: FREE
Who Should Watch:
This webinar is for anyone and everyone! Since this webinar is geared towards those who are just starting out on their journey towards CCNA certification, no prior knowledge is needed in order to participate, just an interest in earning your CCNA.
What We’ll Discuss:
We will cover common trouble areas that most people experience when getting started with their CCNA certification, such as how to approach making a study schedule and strategies for not becoming overwhelmed by the sheer quantity of topics to be learned. We will also discuss the testing experience and the CCNA Certification test format. Topics include: Deciding whether to take one test or two to get your CCNA, What to expect when you walk into the testing center, which topics to study and how in depth, and what study tools can be useful. Last, Keith will talk about his own experience taking Continue reading
Even though graph analytics has not disappeared, especially in the select areas where this is the only efficient way to handle large-scale pattern matching and analysis, the attention has been largely silenced by the new wave machine learning and deep learning applications.
Before this newest hype cycle displaced its “big data” predecessor, there was a small explosion of new hardware and software approaches to tackling graphs at scale—from system-level offerings from companies like Cray with their Eureka appliance (which is now available as software on its standard server platforms) to unique hardware startups (ThinCI, for example) and graph …
Putting Graph Analytics Back on the Board was written by Nicole Hemsoth at The Next Platform.
 Ulf Ewaldsson, who played a key role in developing the company’s 5G vision, will leave the executive team.
Ulf Ewaldsson, who played a key role in developing the company’s 5G vision, will leave the executive team.
 The company integrated two acquisitions during the quarter.
The company integrated two acquisitions during the quarter.
Customers understand the need for micro-segmentation and benefits it provides to enhance the security posture within their datacenter. However, one of the challenges for a Security admin is how to define micro-segmentation policies for applications owned and managed by application teams. This is even more challenging especially when you have tens or hundreds of unique applications in your data center, all of which use different port and protocols and resources across the cluster. The traditional manual perimeter firewall policy modeling may not be ideal and may not be able to scale for the micro-segmentation of your applications as it would be error-prone, complex and time consuming.
NSX addresses the how & where to start micro-segmentation challenge by providing the built-in tool called Application Rule Manager (ARM), to automate the application profiling and the onboarding of applications with micro-segmentation policies. NSX ARM has been part of NSX, since the NSX 6.3.0 release but here we will talk about Application Rule Manager (ARM) enhancement, Recommendation Engine, introduced as part of NSX 6.4.0 release. This enhancement allows you to do Rapid Micro-segmentation to your data center application by recommending “ready to consume” workload grouping & firewall policy rules.