VMware Raises Forecast, But Can It Be the ‘Glue of the Hybrid Cloud?’
 VMware’s full fiscal year outlook puts total revenue at almost $8 billion, about a 10 percent jump.
VMware’s full fiscal year outlook puts total revenue at almost $8 billion, about a 10 percent jump.
Physical SD-WAN Appliances Aren’t Going Anywhere
 However, they do range in function depending on how “thick” or “thin” vendors want these to be.
However, they do range in function depending on how “thick” or “thin” vendors want these to be.
The Ironic – And Fleeting – Volatility In NVM Storage
There is no question any longer that flash memory has found its place – in fact, many places – in the datacenter, even though the debate is still raging about when or if solid state memory will eventually replace disk drives in all datacenters of the world.
Sometime between tomorrow and never is a good guess.
Flash is still a hot commodity, so much so that the slower-than-expected transition to 3D NAND has caused a shortage in supply that is driving up the price of enterprise-grade flash – unfortunately at the same time that memory makers are having trouble cranking …
The Ironic – And Fleeting – Volatility In NVM Storage was written by Timothy Prickett Morgan at The Next Platform.
When Agility Outweighs Cost for Big Cloud Operations
If anything has become clear over the last several years of watching infrastructure and application trends among SaaS-businesses, it is that nothing is as simple as it seems. Even relatively straightforward services, like transactional email processing, have some hidden layers of complexity, which tends to equal cost.
For most businesses providing web-based services, the solution for complexity was found by offloading infrastructure concerns to the public cloud. This provided geographic availability, pricing flexibility, and development agility, but not all web companies went the cloud route out of the gate. Consider SendGrid, which pushes out over 30 billion emails per month. …
When Agility Outweighs Cost for Big Cloud Operations was written by Nicole Hemsoth at The Next Platform.
Worth Reading: The Coco Block Chain
The post Worth Reading: The Coco Block Chain appeared first on rule 11 reader.
AWS Debuts AI-Powered Cloud Security, Announces 2 Big Customer Wins
 AWS’ cloud services and infrastructure give enterprises ‘superpowers.’
AWS’ cloud services and infrastructure give enterprises ‘superpowers.’
Amdocs Monitors ‘Pretty Much Everything’ in ONAP
 ONAP counts 1,000 participants in less than a year.
ONAP counts 1,000 participants in less than a year.
Huawei X-Haul Uses Cloud to Support 5G and Network Slicing
 The X-Haul platform is targeted at backhaul and fronthaul needs.
The X-Haul platform is targeted at backhaul and fronthaul needs.
Performance Portability on the Road to Exascale
The software ecosystem in high performance computing is set to be more complex with the leaps in capability coming with next generation exascale systems. Among several challenges is making sure that applications retain their performance as they scale to higher core counts and accelerator-rich systems.
Software development and performance profiling company, Allinea, which has been around for almost two decades in HPC, was recently acquired by ARM to add to the company’s software ecosystem story. We talked with one of the early employees of Allinea, VP of Product Development, Mark O’Connor about what has come before—and what the software performance …
Performance Portability on the Road to Exascale was written by Nicole Hemsoth at The Next Platform.
Brazil needs to involve all stakeholders in Internet governance
Last week the Brazilian government, through the Ministry of Science, Technology, Innovation and Communication, launched an open consultation as part of a process for reviewing the current structure and mission of the Brazilian Internet Steering Committee, the CGI.Br.
[Note: Portuguese version of this post included below.]
An evaluation and review of a Governance mechanism is natural and something that should not call the attention of anybody. The particularity here is that the announcement was unexpected, showing that the criteria to be used, the objectives of the review, and the process itself were not done in a multistakeholder manner.
Thoughts on Grey Failures
In this video I work through some thoughts around grey failures—a big thanks to Ivan for discussing this with me, which was very helpful. The paper mentioned in the video can be found here.
The post Thoughts on Grey Failures appeared first on rule 11 reader.
Oracle Database Platform Runs on Bare Metal Cloud Infrastructure
 Other public cloud providers are ‘like Southwest Airlines.’ Oracle says it’s a private jet.
Other public cloud providers are ‘like Southwest Airlines.’ Oracle says it’s a private jet.
Why Morningstar Moved to the Cloud: 97% Cost Reduction
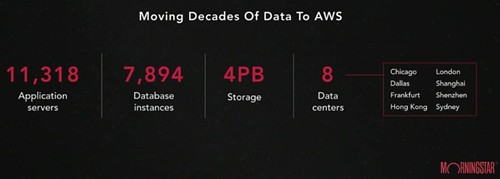
Enterprises won't move to the cloud. If they do, it's tantamount to admitting your IT group sucks. That has been the common wisdom. Morningstar, an investment research provider, is moving to the cloud and they're about as enterprisey as it gets. And they don't strike me as incompetent, it just seems they don't want to worry about all the low level IT stuff anymore.
Mitch Shue, Morningstar's CTO, gave a short talk at AWS Summit Series 2017 on their move to AWS. It's not full of nitty gritty technical details. That's not the interesting part. The talk is more about their motivations, the process they used to make the move, and some of the results they've experienced. While that's more interesting, we've heard a lot of it before.
What I found most interesting was the idea of Morningstar as a canary test. If Morningstar succeeds, the damn might bust and we'll see a lot more adoption of the cloud by stodgy mainstream enterprises. It's a copy cat world. That sort of precedent gives other CTOs the cover they need to make the same decision.
The most important idea in the whole talk: the cost savings of moving to Continue reading