4 tips for tough conversations with your employees
No one likes when difficult situations at work, but when these issues do arise, it's important that your focus remains on establishing a productive conversation where everyone feels heard."When difficult conversations do arise -- such as discussions about low performance, inconsistent results, frustrated clients -- a leader can confidently assess the current situation against previously defined expectations and a focus on identifying and closing the gap," says Anthony Abbatiello, global lead, Deloitte Leadership business.When you approach tough conversations with professionalism and leadership, they can ultimately help guide the employee in their career by helping them figure out what their strengths and weaknesses are. However, it can still be just as difficult to deliver bad news at work as it is to receive it, but there are a few steps you can take to help make those tough moments at work easier on everyone.To read this article in full or to leave a comment, please click here
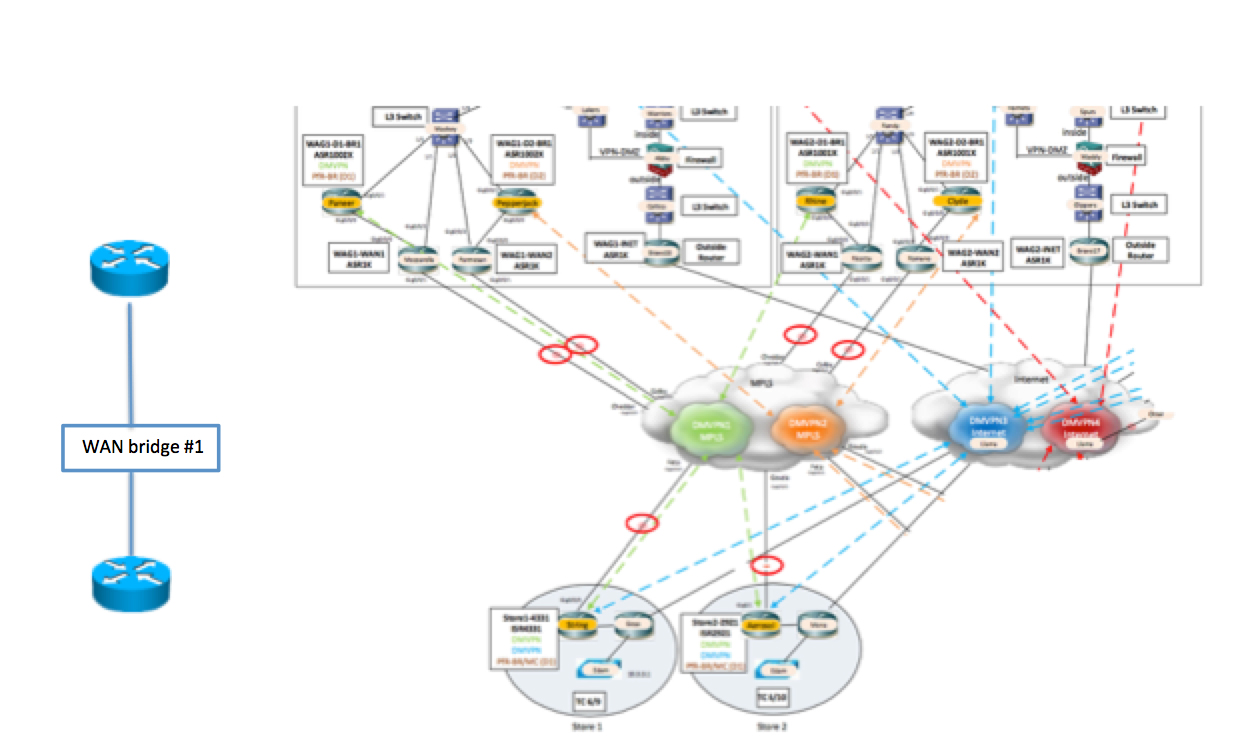
 Determine which apps are most suitable to run on the cloud.
Determine which apps are most suitable to run on the cloud.

 I use WAN Bridge – its simple and free.
I use WAN Bridge – its simple and free.