There’s Application Virtualization and There’s Docker
In what appears to be a recurring theme (which I promise I’ll move off of soon), I’m going to spend some time talking about what Docker isn’t – Docker is not application virtualization. I spent a good amount of time … ContinuedI’m Leaving You
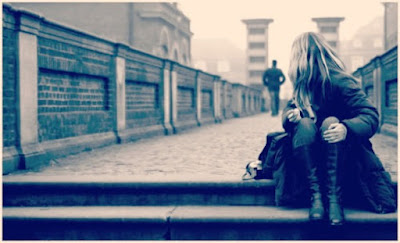
No. It’s not you.
It’s me. It’s always been me.
I remember the first time we met. It was early 2000.
I was young and just graduated from Mechanical Engineering.
I didn’t have any job.
I was desperate. That’s when I met you.
It was like love at first sight.
I spent sleepless nights just to know you.
And more and more I spent time with you, more and more I love you.
I spent time with several others, but my mind and heart were always be with you.
I knew I have to get to you, at any cost.
Even if I had to sacrifice.
Even if I had to leave my home in Dubai.
Even if I had to leave all my friends behind.
Finally in 2006 we were officially together.
I remember it was November, in Singapore.
I couldn’t describe how happy I was.
I traveled many countries in Asia Pacific for you.
I never asked questions. I was a very happy man.
And you invited me several times to visit your home in California.
I was living my dream.
You asked me to move back to Dubai with you in 2008.
A request that I didn’t Continue reading
Shortest Path Bridging (SPB) and Avaya Fabric on Software Gone Wild
A few months ago I met a number of great engineers from Avaya and they explained to me how they creatively use Shortest Path Bridging (SPB) to create layer-2, layer-3, L2VPN, L3VPN and even IP Multicast fabrics – it was clearly time for another deep dive into SPB.
It took me a while to meet again with Roger Lapuh, but finally we started exploring the intricacies of SPB, and even compared it to MPLS for engineers more familiar with MPLS/VPN. Interested? Listen to Episode 54 of Software Gone Wild.