Cairo, Egypt: CloudFlare’s 74th Data Center

It’s been a big year of expansion for CloudFlare’s global network as we added new data centers across six continents, and we’re certainly not done. Today we announce the launch of our newest data center in Cairo, Egypt and a partnership with Telecom Egypt. This marks our third data center in Africa, after Johannesburg and Mombasa, and our 74th data center globally.
Faster performance across Egypt
For many years, CloudFlare has been trusted by Egyptian websites to be protected from attacks.
Over half of the 20 most popular websites in Egypt already use CloudFlare to be safe, and are now seeing a 2x improvement in performance.
Reduced latency to Egypt's largest network, Telecom Egypt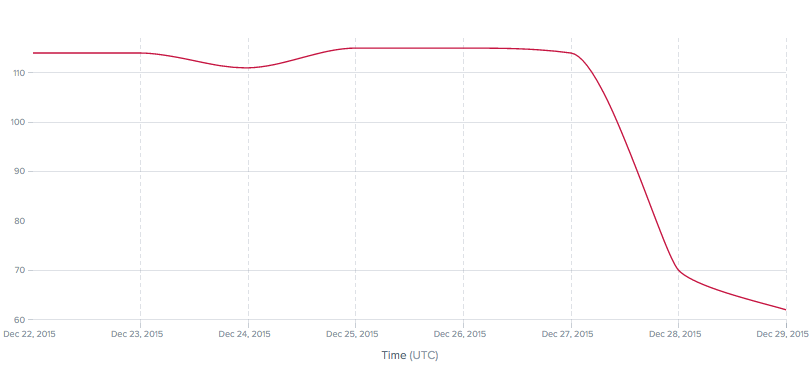
Local Deployments
Just like in Egypt, we partner with ISPs globally by deploying caches directly into their facilities. These points of presence help major networks improve the performance of millions of websites, reduce their costs and capacity used in accessing our customers' content, and provide a direct local interconnect with critical Internet infrastructure. If you are a carrier or Internet service provider in Egypt, elsewhere in Africa or anywhere around the world that would like to request a CloudFlare cache deployment, please reach out to Continue reading
 HPE will have to share the NFV glory but says it's not out of Telefónica's plans.
HPE will have to share the NFV glory but says it's not out of Telefónica's plans. Read the full Q&A and watch the video for the SDxCentral NV Report Webinar sponsored by Avaya where experts elaborate on why network virtualization and SDN should reach further than the data center.
Read the full Q&A and watch the video for the SDxCentral NV Report Webinar sponsored by Avaya where experts elaborate on why network virtualization and SDN should reach further than the data center. Register today for the SDxCentral and Pluribus Networks Network Virtualization Report webinar where you'll learn the true value of analytics and insights in the data center.
Register today for the SDxCentral and Pluribus Networks Network Virtualization Report webinar where you'll learn the true value of analytics and insights in the data center. Only a few years old, NFV passed some milestones in 2015.
Only a few years old, NFV passed some milestones in 2015. It's been a year of learning about new products, new markets... and giraffes.
It's been a year of learning about new products, new markets... and giraffes.