Cloud Foundry Project Eirini Inches the Group Closer to Kubernetes
 The Project Eirini work also calls into question the future of Cloud Foundry's Diego container...
The Project Eirini work also calls into question the future of Cloud Foundry's Diego container...
NetApp’s Ingo Fuchs on the Hybrid Cloud’s Best-of-Breed Approach
 In this interview, Ingo Fuchs—Chief Technologist for Cloud and DevOps at NetApp—discusses the...
In this interview, Ingo Fuchs—Chief Technologist for Cloud and DevOps at NetApp—discusses the...
Day Two Cloud 006: Dealing With The Unknown Unknowns Of Building Cloud Applications
Today's Day Two Cloud podcast looks at how one developer dealt with surprises and unexpected issues that arose as his company built CMS application on Azure, including storage problems, user identity quirks, and more.Day Two Cloud 006: Dealing With The Unknown Unknowns Of Building Cloud Applications
Today's Day Two Cloud podcast looks at how one developer dealt with surprises and unexpected issues that arose as his company built CMS application on Azure, including storage problems, user identity quirks, and more.
The post Day Two Cloud 006: Dealing With The Unknown Unknowns Of Building Cloud Applications appeared first on Packet Pushers.
CNCF Remains Focused as Cloud Native Interest Soars
 Dan Kohn, executive director of CNCF, said the group this year is targeting the broader telecom...
Dan Kohn, executive director of CNCF, said the group this year is targeting the broader telecom...
Episode 48 – BGP Peering In The Real World
Internet BGP Peering relationships are a complicated mix of competing and complimentary motivations. In this Network Collective Community Roundtable we dive in to the world of public BGP peering to discuss how it works in the real world and when it might make sense for your organization to consider getting involved as well.
We would like to thank Cumulus Networks for sponsoring this episode of Network Collective. Cumulus Networks makes networking software for the open, modern data center. It’s the only open networking software that allows you to affordably build and efficiently operate your network like the worlds largest data center operators. Cumulus Networks wants you to build something epic. Whether you’re scaling your data center network or designing the next “big thing,” you have your sights set on building something that matters. To do that, you’ll need to use the absolute best resources. If you would like to learn more about how Cumulus Networks can help you build something epic, you should check out https://cumulusnetworks.com/epic
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3. Continue reading
Enabling the Next Generation of Community Network Builders: A Report on CNXAPAC 2018 and CN Champs
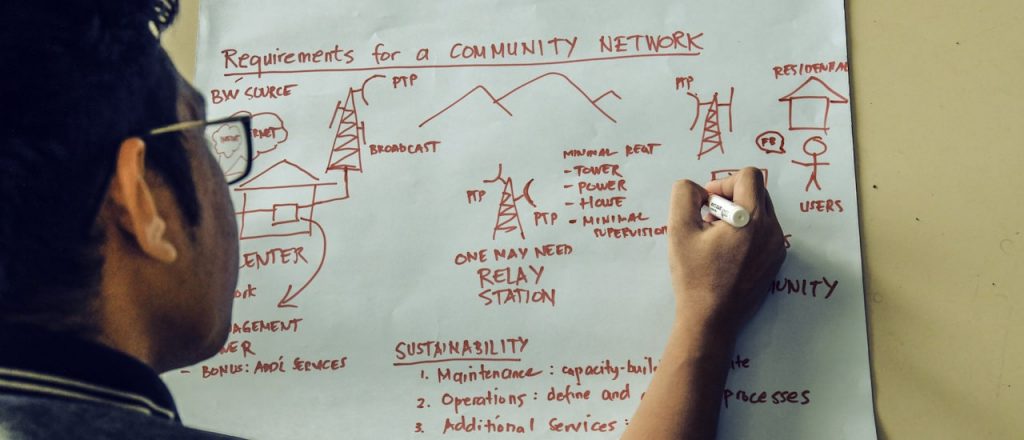
In October 2018, together with our partner Digital Empowerment Foundation (DEF), we organized the 2nd edition of CNXAPAC (Community Network eXchange Asia-Pacific) with a focus on how two sets of community operators – community radio network operators and community (Internet) network operators – could explore synergies in the work they do.
The event was kindly hosted by UNESCO at their Delhi office, and brought together over 50 participants from around the world to exchange knowledge and best practices, and see how the Internet can improve the lives of underserved and unserved communities.
In many parts of the world, community radio stations play an important role in providing information to the public – particularly in rural communities. The community radio community have expertise in setting up radio communications, as well as creating content relevant to their local communities. This presents a wonderful opportunity for this community to add Internet services to their repertoire, and 12 community radio operators from around India were brought to CNXAPAC to learn about Internet community networks, and how these could be deployed in their local communities.
The Internet Society Asia-Pacific Bureau has been working on community networks since 2010 as part of its Wireless for Continue reading
Aqua Secures $62M Funding Round, Bringing Total to Over $100M
 “Any technology that shows early signs of enterprise adoption in the cloud native space will be...
“Any technology that shows early signs of enterprise adoption in the cloud native space will be...
Don’t Sugarcoat the Challenges You Have
Last year I got into somewhat-heated discussion with a few engineers who followed the advice to run IBGP EVPN address family on top of an EBGP underlay.
My main argument was simple: this is not how BGP was designed and how it’s commonly used, and twisting it this way requires schizophrenic BGP routing process which introduces unnecessary complexity (even though it looks simple in Junos configuration) and might confuse people who have to run the network after the brilliant designer is gone.
Read more ...MemVerge Raises $24.5M for Intel Optane-Based Infrastructure Software
 The software, when applied to Intel's persistent memory hardware, improves the performance and...
The software, when applied to Intel's persistent memory hardware, improves the performance and...
Cumulus content roundup: March
Did you feel like you missed any of our great blogs or podcasts this month? We had a lot of great ones to choose from in our March content roundup and on top of that, we had a lot of great industry articles and videos we shared that you can easily access below too! Spend a minute or two, or maybe even sixty to digest it all and increase your overall knowledge. Happy trails!
From Cumulus Networks:
Cumulus Networks is excited to announce being the first to power Facebook’s next generation, open modular platform, Minipack: With this news being announced at the recent OCP Summit 2019, we provided this helpful blog with links to everything you need to know about the announcement including data sheets etc.
Kernel of Truth season 2 episode 3: Storage solutions: Ask & you shall receive! A question asking “what are middle-tier customers doing for storage” came across our path & we thought hey, let’s tap a couple of experts to answer this one. Listen as David Iles from Mellanox Technologies discusses this with our own Peter Lumbis & host Brian O’Sullivan here.
The multicloud we need, but not the one we deserve: How can you take advantage of multi-cloud deployments without completely ditching Continue reading
CTIA: US on Pace to Lead 5G
 By freeing up more spectrum during the next five years, the U.S. wireless industry could add $391...
By freeing up more spectrum during the next five years, the U.S. wireless industry could add $391...




