VMware Warns That 3 Hurdles Prevent Mass Kubernetes Adoption
 In order for Kubernetes to infiltrate more than 100,000 organizations, the ecosystem needs to tackle business cases, management, and training.
In order for Kubernetes to infiltrate more than 100,000 organizations, the ecosystem needs to tackle business cases, management, and training.
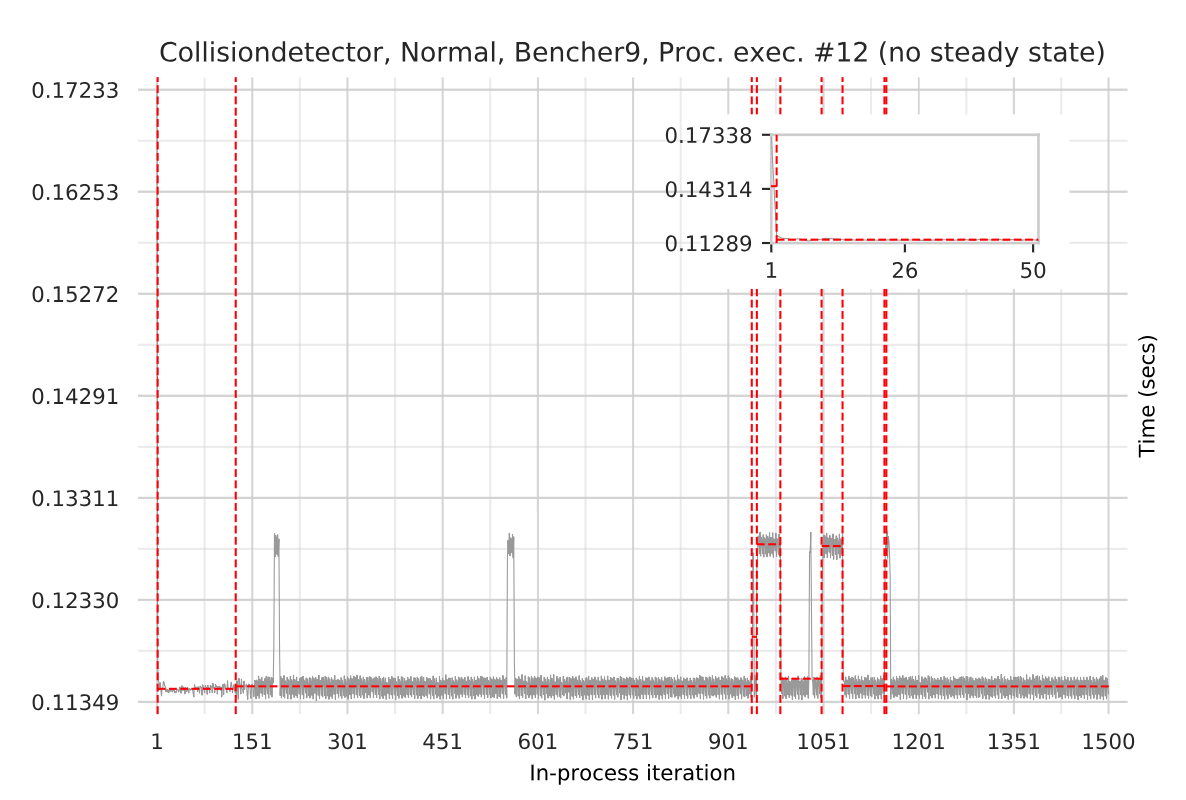
More consistent LuaJIT performance
This is a guest post by Laurence Tratt, who is a programmer and Reader in Software Development in the Department of Informatics at King's College London where he leads the Software Development Team. He is also an EPSRC Fellow.
A year ago I wrote about a project that Cloudflare were funding at King's College London to help improve LuaJIT. Our twelve months is now up. How did we do?
The first thing that happened is that I was lucky to employ a LuaJIT expert, Thomas Fransham, to work on the project. His deep knowledge about LuaJIT was crucial to getting things up and running – 12 months might sound like a long time, but it soon whizzes by!
The second thing that happened was that we realised that the current state of Lua benchmarking was not good enough for anyone to reliably tell if they'd improved LuaJIT performance or not. Different Lua implementations had different benchmark suites, mostly on the small side, and not easily compared. Although it wasn't part of our original plan, we thus put a lot of effort into creating a larger benchmark suite. This sounds like a trivial job, but it isn't. Many programs make Continue reading
Video: Top 10 Misconceptions About 5G For Beginners

Breaks down the reality and practical considerations so that you can decode whether someone in marketing wrote those hypetastic 5G articles that you see everywhere.
The post Video: Top 10 Misconceptions About 5G For Beginners appeared first on EtherealMind.
Verizon Writes Down Oath by $4.8 Billion

And now they dream of selling SDWAN to Enterprises ? LOL
The post Verizon Writes Down Oath by $4.8 Billion appeared first on EtherealMind.
Navigating with Wireshark
Tony Fortunato takes you on a quick Wireshark navigational exercise. In the video, he provides examples and discusses filters and other topics to get you started.
Response: Google’s CEO thinks Android users know how much their phones are tracking them – TechCrunch

I think thats a bare faced lie. And google knows it.
The post Response: Google’s CEO thinks Android users know how much their phones are tracking them – TechCrunch appeared first on EtherealMind.
Configuring Cisco Flexible NetFlow and Juniper j-Flow v8
The post Configuring Cisco Flexible NetFlow and Juniper j-Flow v8 appeared first on Noction.
Can I Replace a Commercial Load Balancer with HAProxy?
A networking engineer attending the Building Next-Generation Data Centers online course sent me this question:
My client will migrate their data center, so they’re not interested in upgrading existing $vendor load balancers. Would HAProxy be a good alternative?
As you might be facing a similar challenge, here’s what I told him:
Read more ...The Case of the Missing LDP Neighbor
R1 and R2 are cabled up twice to each other via their gig0/0/1 interfaces and their gig0/0/7 interfaces. Each connection is in its own subnet, and each interface configured for OSPF and MPLS. But while we have 2 OSPF neighbors between them… we only have 1 LDP neighbor.

R1#show mpls int
Interface IP Tunnel BGP Static Operational
Gi0/0/1 Yes (ldp) No No No Yes
Gi0/0/7 Yes (ldp) No No No Yes
R1#
So as you can see from the output of show mpls interface, gig0/0/1 and gig0/0/7 are both configured for MPLS LDP. Why then if we look below do we see only 1 MPLS LDP neighbor between them?
What is the problem? Actually… in this situation there isn’t a problem. This is actually expected behavior.
R1#sh mpls ldp neighbor
Peer LDP Ident: 10.100.100.2:0; Local LDP Ident 10.100.100.1:0
TCP connection: 10.100.100.2.22592 - 10.100.100.1.646
State: Oper; Msgs sent/rcvd: 184/184; Downstream
Up time: 02:32:11
LDP discovery sources:
GigabitEthernet0/0/1, Src IP addr: 10.1.1.2
GigabitEthernet0/0/7, Src IP addr: 10.1.7.2
Addresses bound to peer LDP Ident:
Continue reading
OAuth Auth Server through Workers
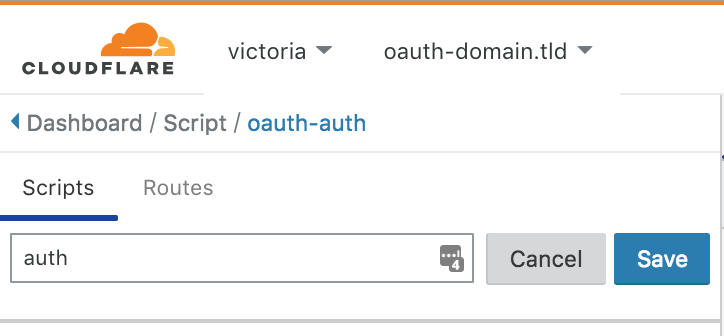
Let’s pretend I own a service and I want to grant other services access to my service on behalf of my users. The familiar OAuth 2.0 is the industry standard used by the likes of Google sign in, Facebook, etc. to communicate safely without inconveniencing users.
Implementing an OAuth Authentication server is conceptually simple but a pain in practice. We can leverage the power of Cloudflare Worker to simplify the implementation, reduce latency, and segregate our service logic from the authentication layer.
For those unfamiliar with OAuth, I highly recommend reading a more in depth article.
The steps of the OAuth 2.0 workflow are as follows:
- The consumer service redirects the user to a callback URL that was setup by the auth server. At this callback URL, the auth server asks the user to sign in and accept the consumer permissions requests.
- The auth server redirects the user to the consumer service with a code.
- The consumer service asks to exchange this code for an access token. The consumer service validates their identity by including their client secret in the callback URL.
- The auth server gives the consumer the access token.
- The consumer service can now use Continue reading
Pivot3 Adds Encryption, Key Management to HCI Stack
 Adding these policy-based security capabilities to the Pivot3 Intelligence Engine enables customers to integrate data encryption and key management into the same workflow for managing applications and storage.
Adding these policy-based security capabilities to the Pivot3 Intelligence Engine enables customers to integrate data encryption and key management into the same workflow for managing applications and storage.