How Network Automation Increases Security
This blog post was initially sent to subscribers of my SDN and Network Automation mailing list. Subscribe here.
After publishing the Manual Work Is a Bug blog post, I got this feedback from Michele Chubirka explaining why automating changes in your network also increases network security:
Read more ...1 Thing You Can Do To Make Your Internet Safer And Faster


On April 1st, 2018, we announced 1.1.1.1, the fastest public DNS resolver in the world ???. Today, we are launching the 1.1.1.1 mobile app to make it incredibly easy to use 1.1.1.1 on your phone.
TL;DR
Any time you are on a public internet connection people can see what sites you visit. Even worse, your Internet Service Provider is very possibly selling all of your browsing history to the highest bidder. We have a tool called 1.1.1.1 which makes it easy to get a faster, more private, Internet experience, but it’s historically been too complex for many people to use, particularly on mobile devices. Today, we’re launching an app you (and everyone you know) can use to use 1.1.1.1 every time your mobile phone connects to the Internet. It’s a free, it’s easy, download it now.
Fastest Public Resolver
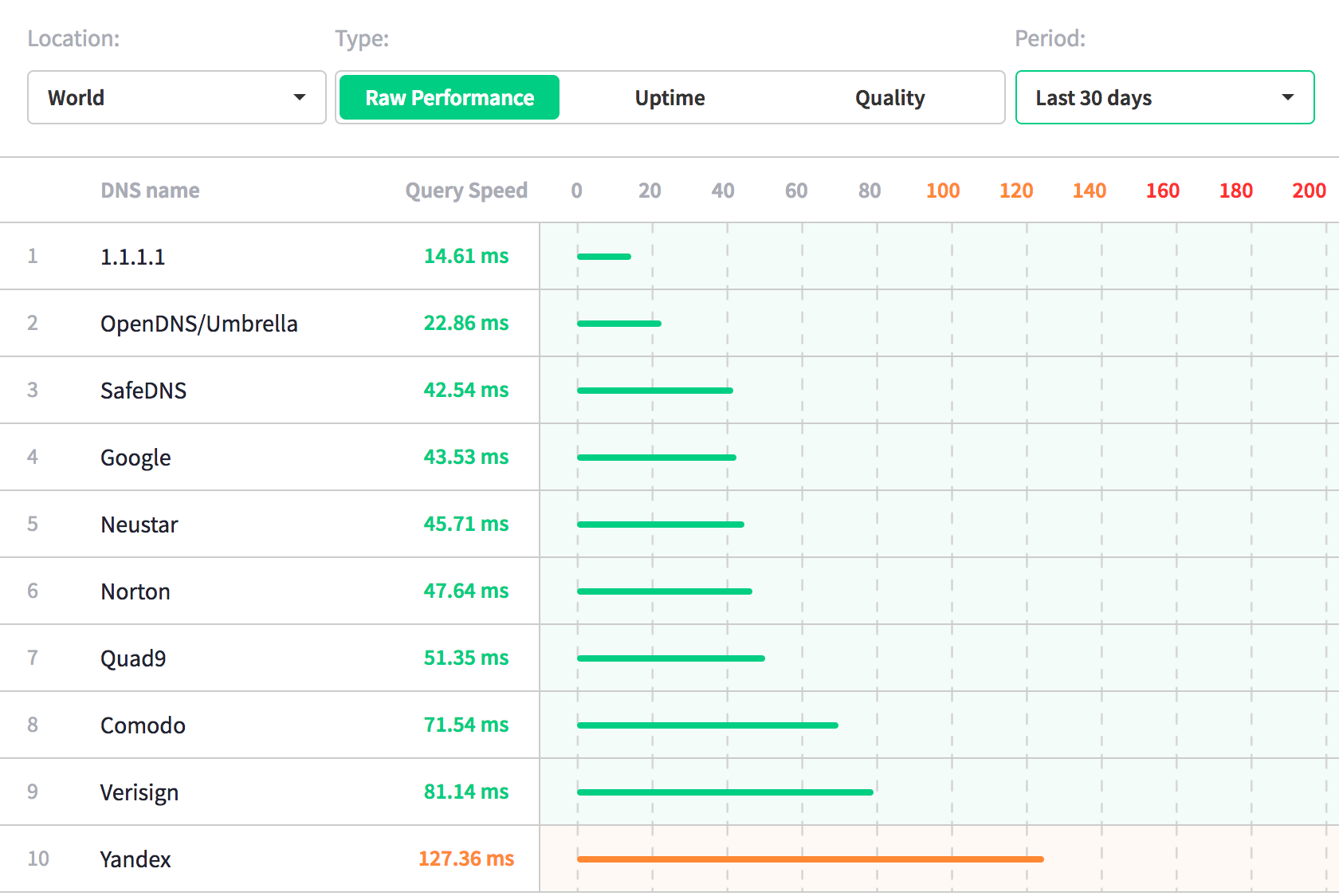
We launched 1.1.1.1 on April 1st. Frankly, we’ve been blown away by how many people actually made the switch. Changing your network settings is not easy, but if our traffic amount is any indication, many of you made the effort. Continue reading
Global Cybersecurity and the Internet Conundrum

Today marks the 100th anniversary of the armistice that ended the first World War. The 1918 ceasefire re-introduced a fragile peace that had collapsed when the world failed to defend common rules and international cooperation. International security and stability are as important now as they were a century ago.
That’s why French President Emmanuel Macron and leaders from around the world are about to gather in Paris for the first Paris Peace Forum. The forum will attempt to pave a way forward for a world that is shifting and changing faster than most of us can keep up with. That change and shift, and the speed of it is enabled by the Internet.
That is why the Internet Society is participating in the Forum.
I will be in Paris to speak on a panel about creating peace in cyberspace. Cybersecurity concerns across the world are real and justified and need to be addressed. We believe that the collaborative approach that helped to drive the growth of the Internet and allows it to thrive is essential for establishing cybersecurity.
The essence of a collaborative approach is that it allows stakeholders to create a shared vision for security.
The Shared Vision
At the Continue reading
BGP best path selection
The complexity and the efficiency of BGP reside in the concept of route “attributes” and the way the protocol juggles them to determine the best path. This is a quick guide (refresh of an old article), still very actual for those dealing with BGP design. I hope the following Cisco BGP best path selection diagram will be of […]Weekly Wrap Podcast: Cisco Lays Off Hundreds of Employees
 SDxCentral Weekly Wrap for Nov. 9, 2018: Cisco axes jobs; Verizon CEO Vestberg makes bold moves with restructuring; and more.
SDxCentral Weekly Wrap for Nov. 9, 2018: Cisco axes jobs; Verizon CEO Vestberg makes bold moves with restructuring; and more.
NetApp: HCI Means Hybrid Cloud, Not Hyperconverged
 What’s in a name? NetApp says its HCI is really hybrid cloud infrastructure (not hyperconverged), but it sounds more like composable.
What’s in a name? NetApp says its HCI is really hybrid cloud infrastructure (not hyperconverged), but it sounds more like composable.
Xilinx, Under a New CEO, Mulls Acquisition of Mellanox
 Xilinx is renown for its field programmable gate array (FPGA), which the company's founder invented. A purchase of Mellanox could give it additional products to sell into the data center.
Xilinx is renown for its field programmable gate array (FPGA), which the company's founder invented. A purchase of Mellanox could give it additional products to sell into the data center.
Alibaba Group Leans Into Cloud Computing Business
 Alibaba Group’s CEO said that cloud computing will be its “main business” in the future — following closely in Amazon’s footsteps.
Alibaba Group’s CEO said that cloud computing will be its “main business” in the future — following closely in Amazon’s footsteps.
Cable Companies Eye Dish’s Greenfield 5G Network
 Dish says it is building a neutral-host 5G network that customers can rent space on to deliver different types of services.
Dish says it is building a neutral-host 5G network that customers can rent space on to deliver different types of services.
SDxCentral’s Weekly Roundup — November 9, 2018
 Docker containerizes Windows Server 2008; Rumors fly that Thoma Bravo will buy Symantec; CommScope buys Arris.
Docker containerizes Windows Server 2008; Rumors fly that Thoma Bravo will buy Symantec; CommScope buys Arris.
Cisco, Huawei Among Alef Mobitech Edge Platform Test Partners
 The software-based platform is focused on mobility network functions needed to interconnect any edge application without any upgrades to the underlying network or origin cloud.
The software-based platform is focused on mobility network functions needed to interconnect any edge application without any upgrades to the underlying network or origin cloud.
Weekly Show 415: Gluware’s Brownfield Automation For Big Pharma (Sponsored)
Gluware sponsors today's Weekly Show podcast and brings along a Big Pharma customer to talk about network automation in a brownfield production network. We dive into making network automation work in real life.
The post Weekly Show 415: Gluware’s Brownfield Automation For Big Pharma (Sponsored) appeared first on Packet Pushers.
